Preface: The vmalloc() function works in a similar fashion to kmalloc(), except it allocates memory that is only virtually contiguous and not necessarily physically contiguous.
Background: In the kernel, ION supports multiple clients, one for each driver that uses the ION functionality. A kernel driver calls the following function to obtain an ION client handle:
struct ion_client *ion_client_create(struct ion_device *dev, unsigned int heap_mask, const char *debug_name)
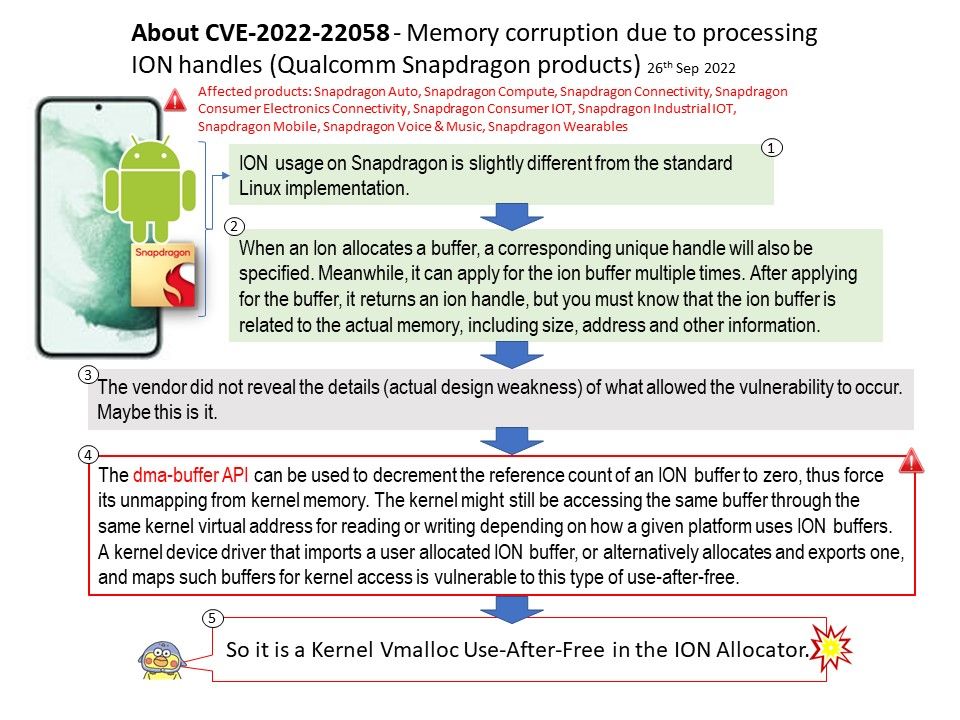
ION usage on Snapdragon is slightly different from the standard linux implementation.
Heaps are listed in the order they will be allocated. Do not swap the order unless you know what you are doing, said Qualcomm.
Vulnerability details: Memory corruption due to use after free issue in kernel while processing ION handles in Snapdragon Auto, Snapdragon Compute, Snapdragon Connectivity, Snapdragon Consumer Electronics Connectivity, Snapdragon Consumer IOT, Snapdragon Industrial IOT, Snapdragon Mobile, Snapdragon Voice & Music, Snapdragon Wearables.
Reference:
- A use-after-free vulnerability is an issue related to incorrect use of dynamic memory during program operation, according to MITRE.
- “Heap” memory, also known as “dynamic” memory, is an alternative to local stack memory. Local memory is quite automatic. Local variables are allocated automatically when a function is called, and they are deallocated automatically when the function exits.
Remedy: Waiting for vendor provide the solution.
.jpg)