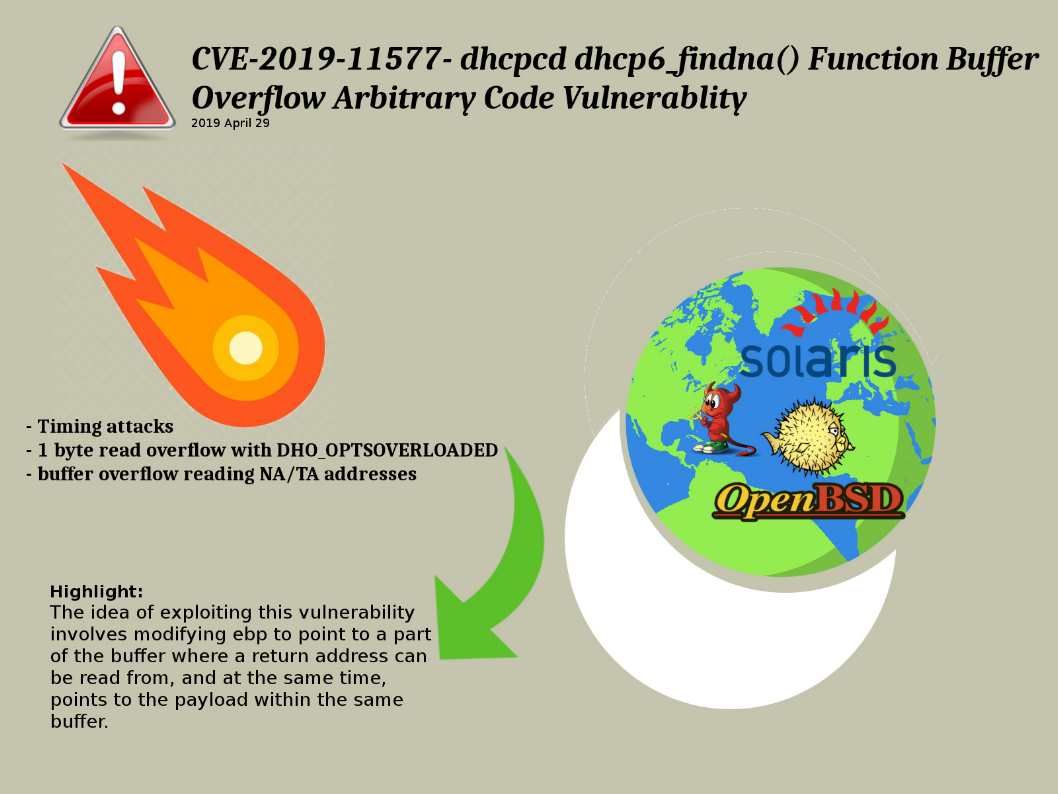
Preface: IT world can’t without DHCP function! It looks like public vehicle in our daily life.
Background: dhcpcd is a DHCP and DHCPv6 client. It is currently the most feature-rich open source DHCP client.
Vulnerabilities Details:
One of the vulnerabilities exists because the dhcp6_findna() function (src / dhcp6.c source code file) does not correctly handle reading specific addresses.
The idea of exploiting this vulnerability involves modifying ebp to point to a part of the buffer where a return address can be read from, and at the same time, points to the payload within the same buffer. We so called 1-byte buffer overflows.R
Remedy:
DHCPv6 – https://roy.marples.name/git/dhcpcd.git/commit/?id=8d11b33f6c60e2db257130fa383ba76b6018bcf6
DHCP – https://roy.marples.name/projects/dhcpcd