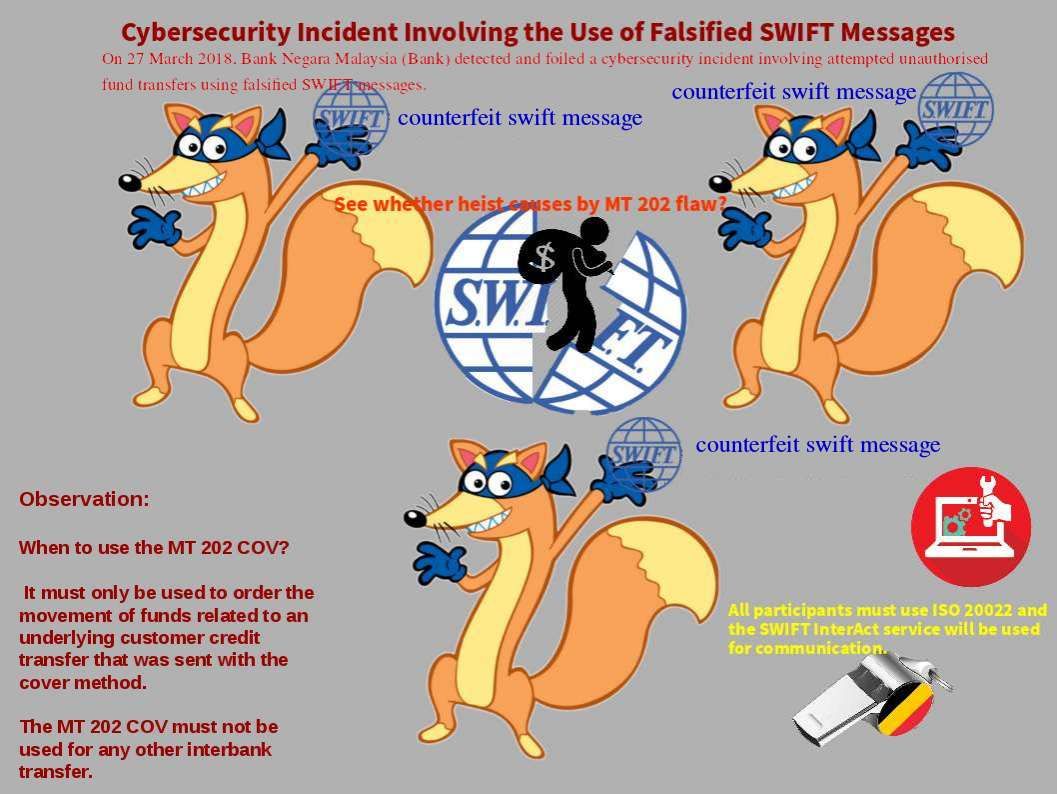
Easter holiday make me lazy. Seen cyber incident alert posted by my friend Enoch yesterday. However I just ignore until awaken this evening. The details of this incident was that the crooks use falsified SWIFT Messages try to achieve their goal. The news told that they haven’t successful. As far as I remember, on February this year City Union Bank in India victim of cyber hack through SWIFT system. My speculation is that it is the flaw of MT202. A fundamental design limitation on original MT 202 message. Perhaps MT 202 COV doing the compensated control. But the MT 202 COV must not be used for any other interbank transfer. However MT 202 still valid and not end of life yet. A hints input of technical concerns shown on attach picture see whether this is root causes of this incident.
MT 202 design weakness lure financial crime
i. Suspicious activity monitoring on the underlying originator and beneficiary in the message would not be performed.
ii. The originating bank could be in a jurisdiction with different sanction watch lists and the technical capabilities of each bank’s sanction screening program could vary.
Below url is the press release (Cybersecurity Incident Involving the Use of Falsified SWIFT Messages)
http://www.bnm.gov.my/index.php?ch=en_press&pg=en_press&ac=4651
Reference: