Preface: (2021-07-30) Reported to KDE and GNOME development teams – In response, patches for both kio and glib were implemented.
However, both projects rely mainly on udisks and use own code only as fallback.
Background: Ubuntu used to have Unity desktop in its default edition but it switched to GNOME desktop since version 17.10 release.
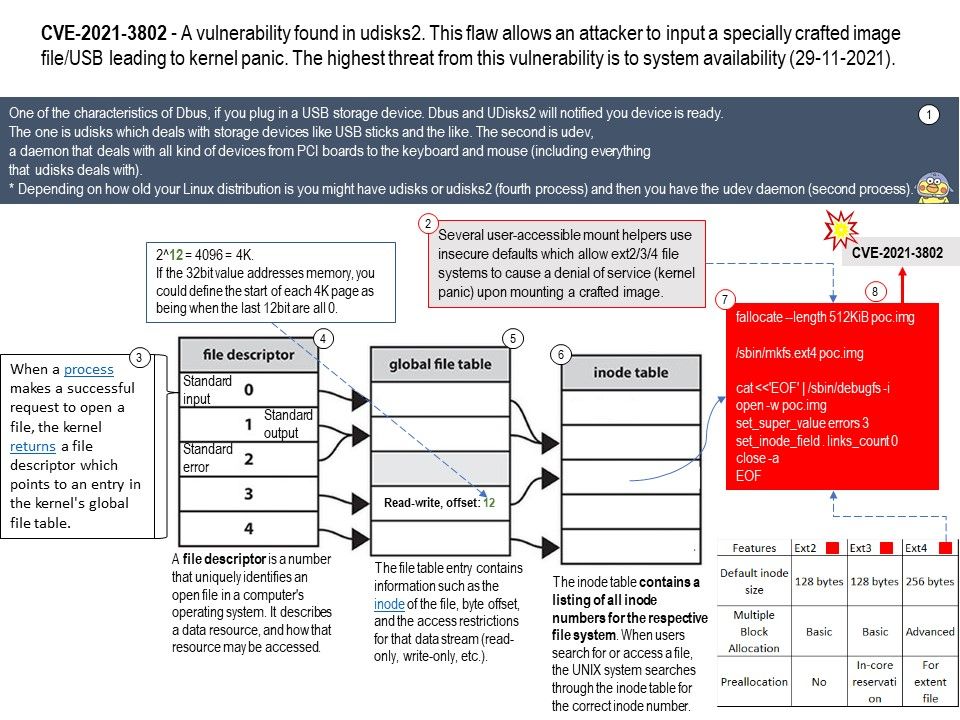
Ubuntu offers several desktop flavors and the KDE version is called Kubuntu. GNOME is the default desktop for Fedora and KDE is the default desktop for OpenSUSE. Depending on how old your Linux distribution is you might have udisks or udisks2 (fourth process) and then you have the udev daemon (second process).
One of the characteristics of Dbus, if you plug in a USB storage device. Dbus and UDisks2 will notified you device is ready.
Remark (a): udisks2 is used by KDE and GNOME nowadays at least (since years). udisks (1) is outdated/obsolete.
Remark (b): The one is udisks which deals with storage devices like USB sticks and the like. The second is udev, a daemon that deals with all kind of devices from PCI boards to the keyboard and mouse (including everything that udisks deals with).
Vulnerability details: Several user-accessible mount helpers use insecure defaults which allow ext2/3/4 file systems to cause a denial of service (kernel panic) upon mounting a crafted image.
Official announcement – https://bugzilla.redhat.com/show_bug.cgi?id=2003649
Udisks2 hides certain devices from the user by default. You can enter the following directory for review:
Fedora – /usr/lib/udev/rules[.]d/80-udisks2[.]rules
.jpg)
.jpg)