Prefect: Headlines new – Critical VxWorks flaws expose millions of devices to hacking.
What is VxWorks? The VxWorks RTOS comprises the core capabilities of the wind microkernel(not monolithic) along with advanced networking support, powerful file system and I/O management, and C++ and other standard run-time support.
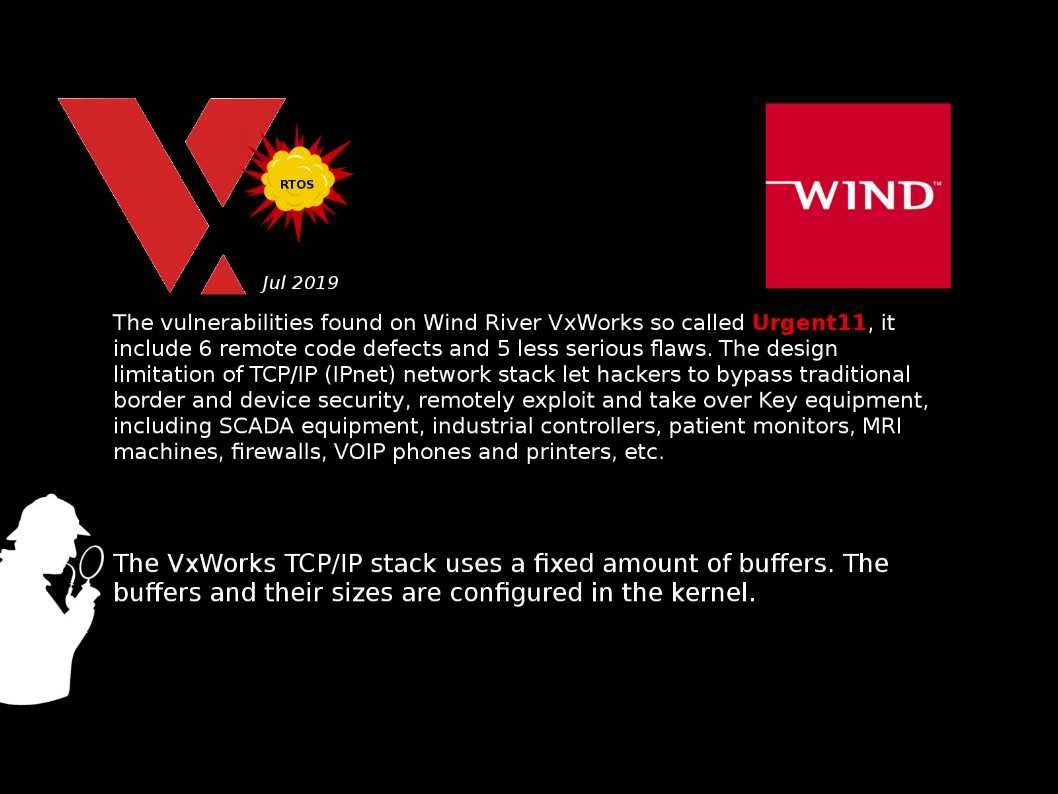
Vulnerability details: The vulnerabilities found on Wind River VxWorks so called Urgent11, it include 6 remote code defects and 5 less serious flaws. The design limitation of TCP/IP (IPnet) network stack let hackers to bypass traditional border and device security, remotely exploit and take over Key equipment, including SCADA equipment, industrial controllers, patient monitors, MRI machines, firewalls, VOIP phones and printers, etc.
Vendor response – Please refer to url: https://www.windriver.com/security/announcements/tcp-ip-network-stack-ipnet-urgent11/
Reference:
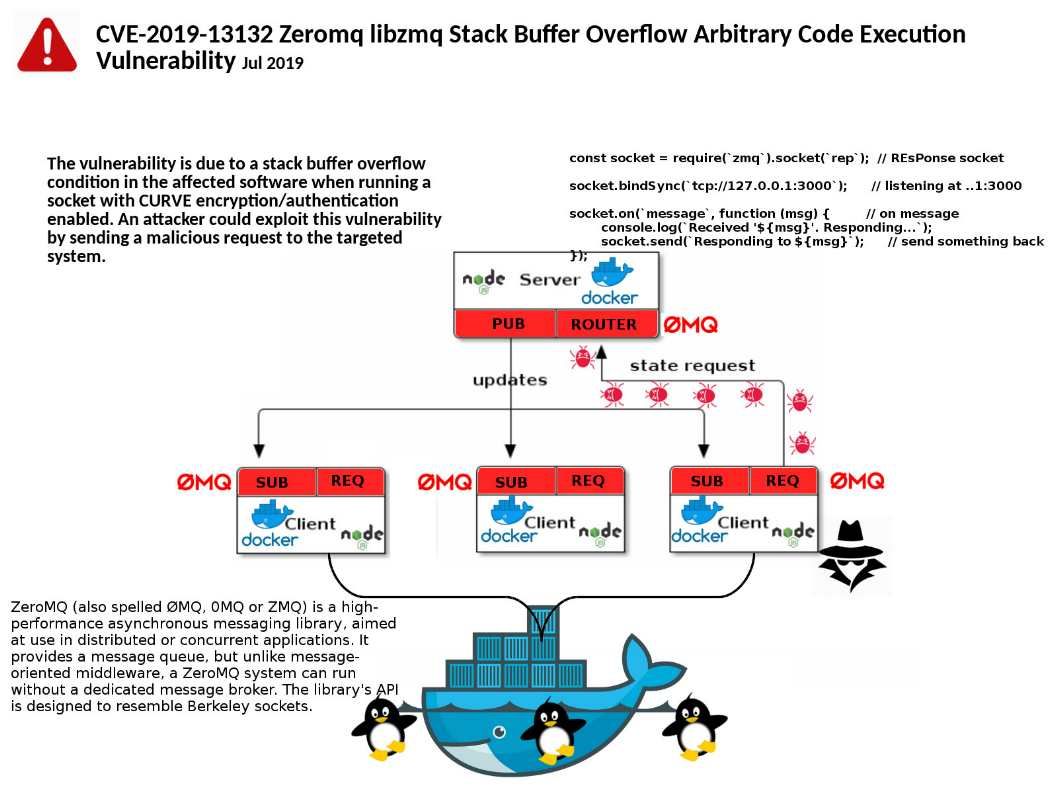
The stack is the temporary memory where variables are stored while a function is executing. The memory will be cleaned up automatically when job done.
The heap is memory that the programmer can use for the application in non automatic way. Programmer might build a mechanism to free up memory after use.