Preface: AVEVA has reached agreement to acquire OSIsoft, a pioneer and global leader in real-time industrial operational data software and services.
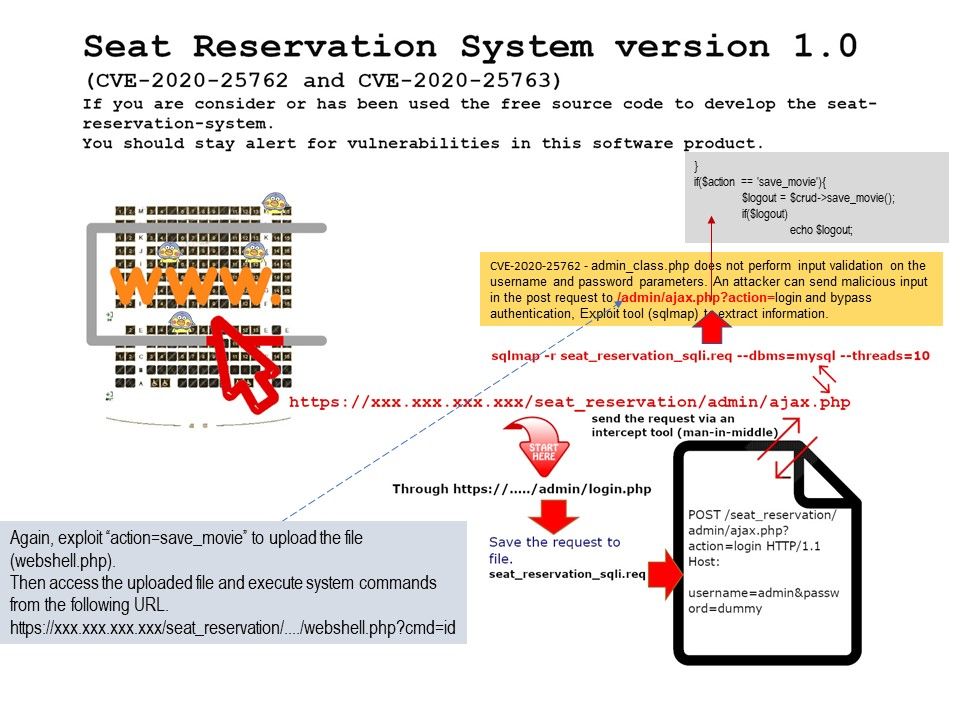
Background: Under normal circumstance, authorized user can navigate to the ASMX file through your browser. So, you can fill in the form with the parameters and post to the DB. If attacker finds the URL of this internet facing web portal, is there a way let hacker alter the database.
Reply: If someone else is in the same domain then he can copy the cookie in the referring page then exploit ASMX file to alter the DB.
Vulnerability details:
CVE-2020-13508 – Parameter AliasName in Alias.asmx is vulnerable to unauthenticated SQL injection attacks.
CVE-2020-13505 – Parameter psClass in ednareporting.asmx is vulnerable to unauthenticated SQL injection attacks.
CVE-2020-13503 – Parameter AttFilterName in ednareporting.asmx is vulnerable to unauthenticated SQL injection attacks.
CVE-2020-13501 – Parameter InstanceName in CHaD.asmx is vulnerable to unauthenticated SQL injection attacks.
CVE-2020-13500 – Parameter ClassName in CHaD.asmx is vulnerable to unauthenticated SQL injection attacks.
CVE-2020-13499 – Parameter InstancePath in CHaD.asmx is vulnerable to unauthenticated SQL injection attacks.
CVE-2020-13507 – Parameter OrigID in Alias.asmx is vulnerable to unauthenticated SQL injection attacks
Remark: Specially crafted SOAP web requests can cause SQL injections resulting in data compromise on above items.
Remedy: Waiting for official announcement.