Preface: The blockchain technology can ensure the security and integrity of data. By combining AI and blockchain, it is possible to create more powerful systems.
Background: When taking about Blockchain, we simply will think about ctyptocurrecy. As a matter of fact, Blockchain technology influenced far-reaching in the world of science and technology.
Oracles provide a way for the decentralized Web3 ecosystem to access existing data sources, legacy systems, and advanced computations. Decentralized oracle networks (DONs) enable the creation of hybrid smart contracts, where on-chain code and off-chain infrastructure are combined to support advanced decentralized applications (dApps) that react to real-world events and interoperate with traditional systems.
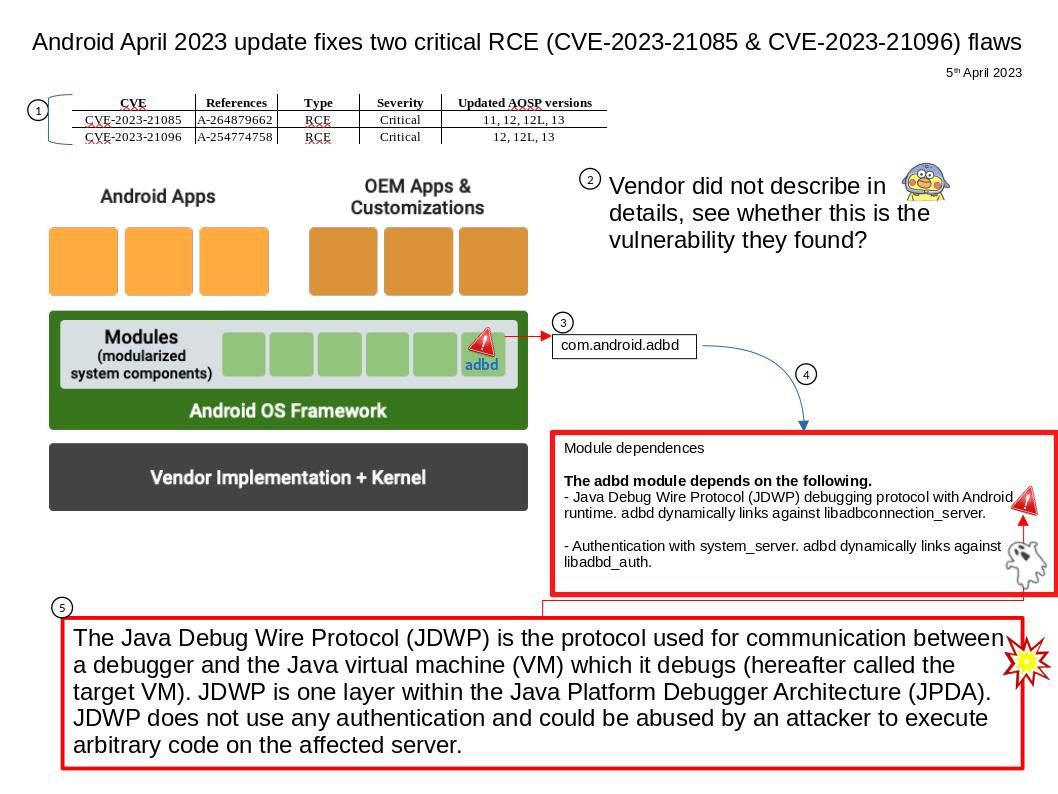
A pre-release announcement of Oracle will be published on the Thursday preceding each Critical Patch Update release. On 18th April 2023, the Pre-Release Announcement said that Critical Patch Update contains 7 new security patches for Oracle Blockchain Platform. 5 of these vulnerabilities may be remotely exploitable without authentication, i.e., may be exploited over a network without requiring user credentials. Before we wait for the official details to be released, let’s take a quick look at the Oracle Blockchain Platform. For details, please refer to attached diagram.
Official announcement: For detail of Oracle Critical Patch Update Pre-Release Announcement – April 2023, please refer to official url for reference – https://www.oracle.com/security-alerts/cpuapr2023.html
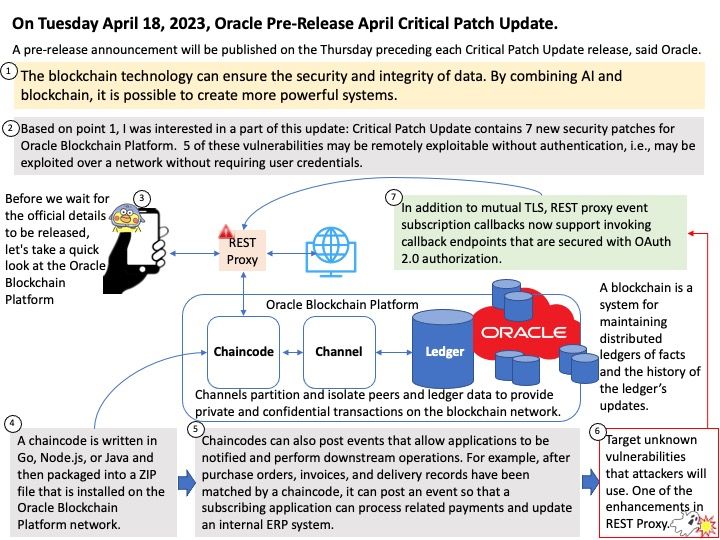
Remark: So far, security expert was concerns how below broadcast protocol may be used for malicious behavior as a botnet command and control (C2) channel. Be my guest, see below for details whether you will think more ideas.
Reference: Atomic transactions work at the application level. Typically you do not need to change existing chaincode logic to support atomic transactions. Because one or more additional arguments are added by the atomic transactions framework, make sure that any existing chaincode does not perform strict checks on the number of arguments passed in the chaincode method. Atomic transactions are supported by the following REST API endpoint:
- restproxy/api/v2/atomicTransactions