Preface: ChatGPT Memory uses the Redis vector database to store an embedded conversation history of past user-bot interactions.
The first interaction between the user and bot is critical to the user experience, said Microsoft.
There are 1482 Companies currently using OpenAI, it also include Adobe and Schneider Electric.
Background: ChatGPT, the full name of Chat Generation Pre-training Converter, is an artificial intelligence chat robot program developed by OpenAI, which will be launched in November 2022. The program uses large language models based on the GPT-3.5 and GPT-4 architectures and is trained with reinforcement learning.
OpenAI is a suite of artificial intelligence (AI) models designed for application developers. It enables users to create AI applications to understand natural-language semantics and generate natural text, translate natural language into programming code, create images from text captions, and classify images.
FastAPI is a Python web framework based on the Starlette microframework. With deep support for asyncio, FastAPI is indeed very fast.
FastAPI also distinguishes itself with features like automatic OpenAPI (OAS) documentation for your API, easy-to-use data validation tools, and more.
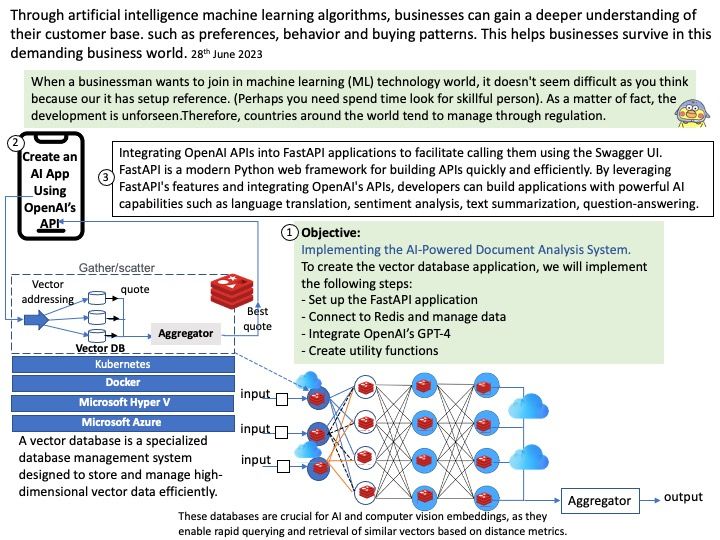
Integrating OpenAI APIs into FastAPI applications to facilitate calling them using the Swagger UI.
FastAPI is a modern Python web framework for building APIs quickly and efficiently. By leveraging FastAPI’s features and integrating OpenAI’s APIs,
developers can build applications with powerful AI capabilities such as language translation, sentiment analysis, text summarization, question-answering, and more.
How to install OpenAI in python
Step 1: Sign up for an OpenAI API key: You will visit the link to register for an account and if you already have an active account using Chat-Gpt 3, you can use the same account to sign in.
If you are a Linux user, have a good try.
How to Install OpenAI on Linux?
Step 2 : upgrade pip and install the openai library.
python3 -m pip install –upgrade pip
python3 -m pip install –upgrade openai
….
For details, please refer to the official link – https://openai.com/