Preface: IoT device similar a delivery arm of robotic concept. They are the python language heavy duty users.
Python language married with IoT devices – For IoT, there has been a variant of python called Micropython , that lets you program for IoT in Python. Additionally, developer can use Raspberry Pi to program your IoT applications in Python.
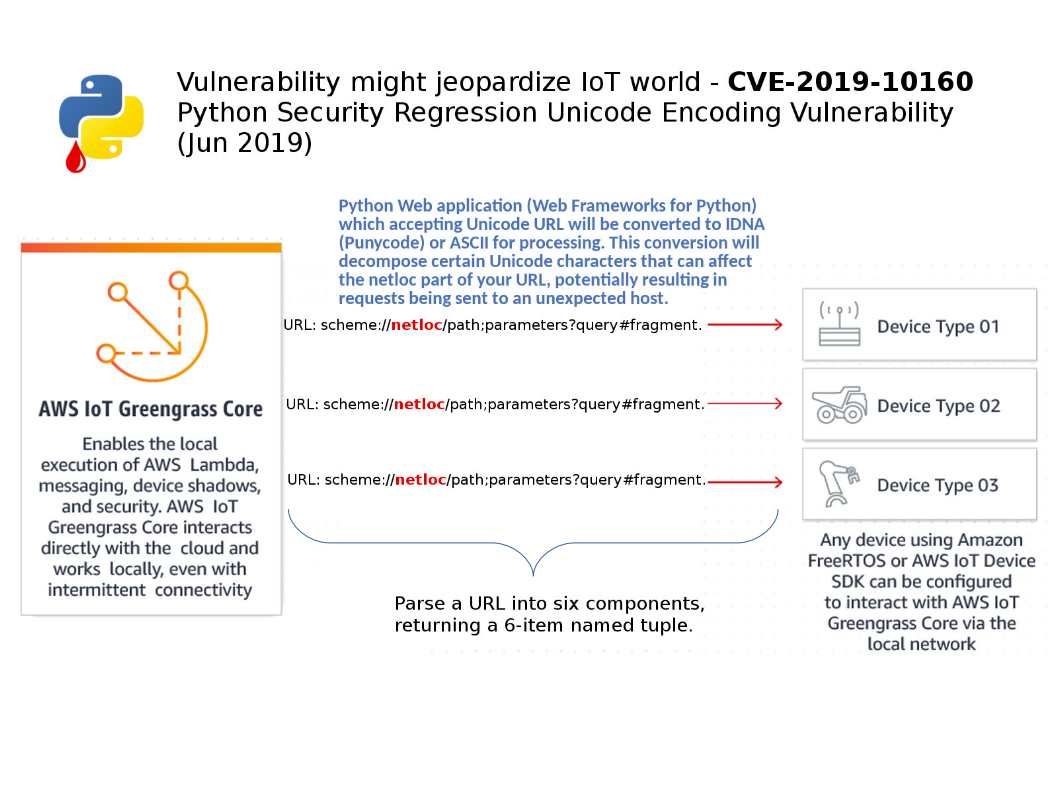
Vulnerability details: A vulnerability in the the urllib.parse.urlsplit and urllib.parse.urlparse components of Python could allow an unauthenticated, remote attacker to obtain sensitive information from a targeted system.
Synopsis: Python Web application (Web Frameworks for Python) which accepting Unicode URL will be converted to IDNA (Punycode) or ASCII for processing. This conversion will decompose certain Unicode characters that can affect the netloc part of your URL, potentially resulting in requests being sent to an unexpected host.
Remark: Parse a URL into six components, returning a 6-item named tuple. This corresponds to the general structure of a URL: scheme://netloc/path;parameters?query#fragment.
Remedy: Python has released a patch at the following link – https://github.com/python/cpython/commit/fd1771dbdd28709716bd531580c40ae5ed814468