Preface: Maybe people won’t use WPA because it’s not safe. However, WPA2 can also collect PSK through tools.
Technical details:
WPA and WPA2 offline attack technique are well known today. For instance, penetration test conduct the WiFi penetration test will relies on tool (Aircrack-NG). As a matter of fact, the attacker first obtains a man-in-the-middle (MitM) position between the victim and the real Wi-Fi network. However it does not enable the attacker to decrypt packets! One of the way use a password recovery tool work with “wordlist”. The mechanism is read line by line from a textfile (aka “dictionary” or “wordlist”) and try each line to find out the password.
Reference: The dictionary pass-phrase attack is one of the popular attacks on WPA2-PSK. Since PSK will be the main key to protect WLAN, the attacker will try to guess the pass-phrase used to generate PSK. This can be done by capturing the initial WPA2-PSK handshaking between a legitimate wireless client and the AP.
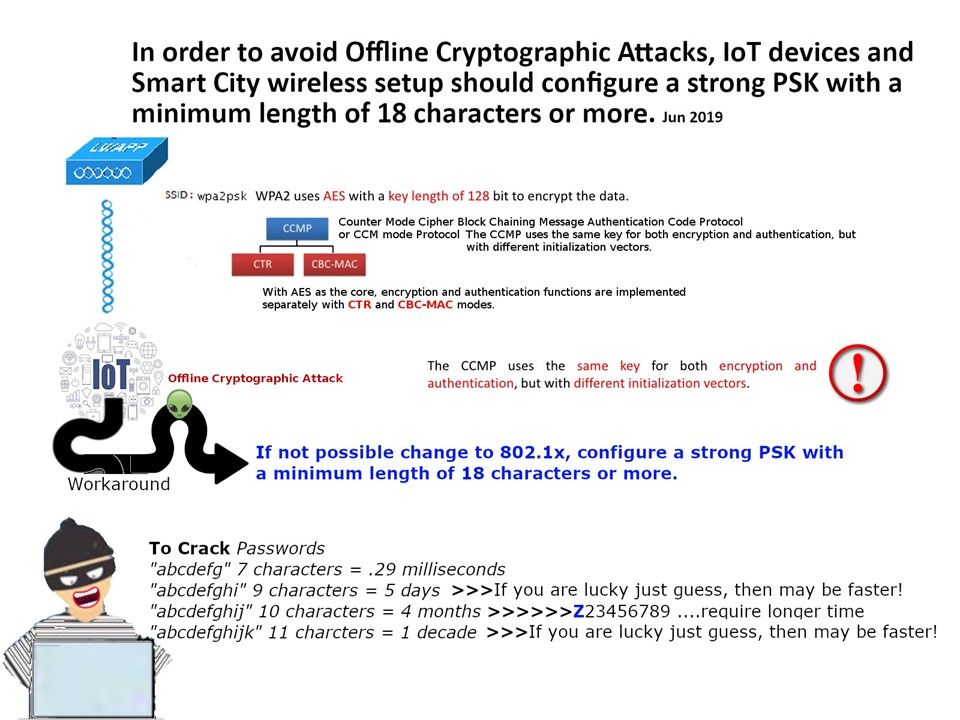
Remedy: Sounds like not difficult to crack. In our world, IoT devices do not use 802.1x for authentication. What can we do?
If not possible change to 802.1x, configure a strong PSK with a minimum length of 19 characters or more.