Preface
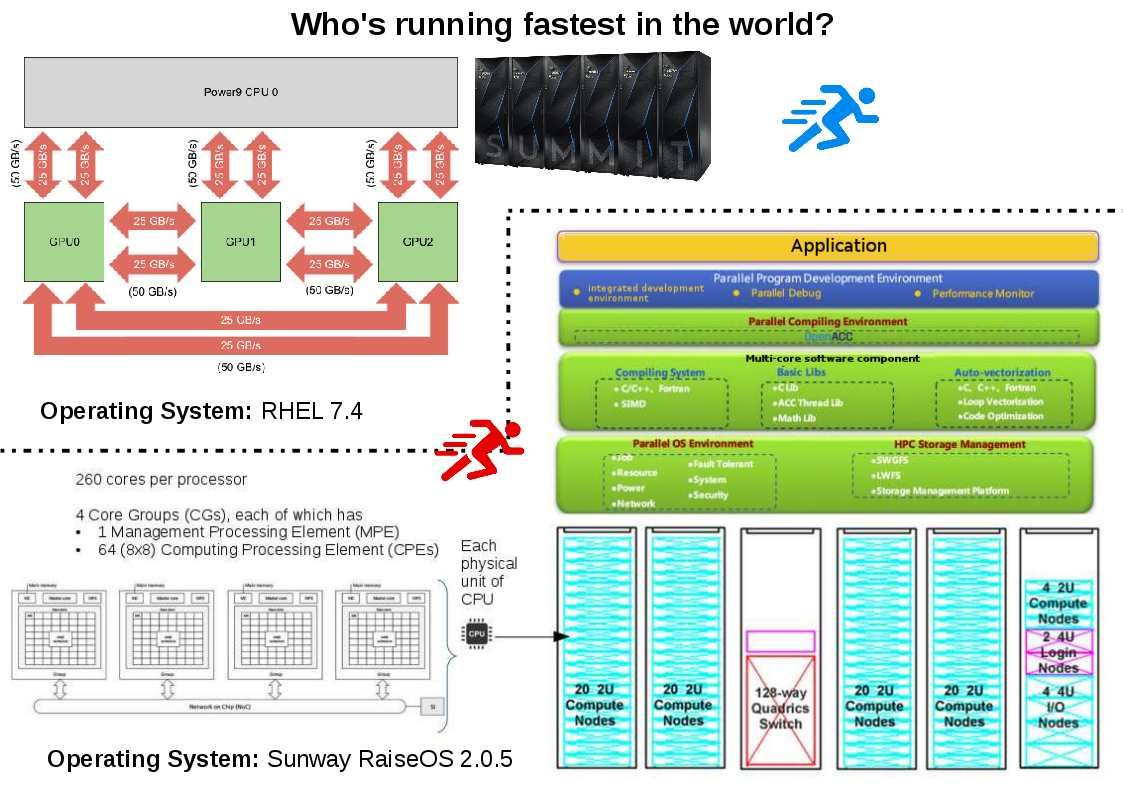
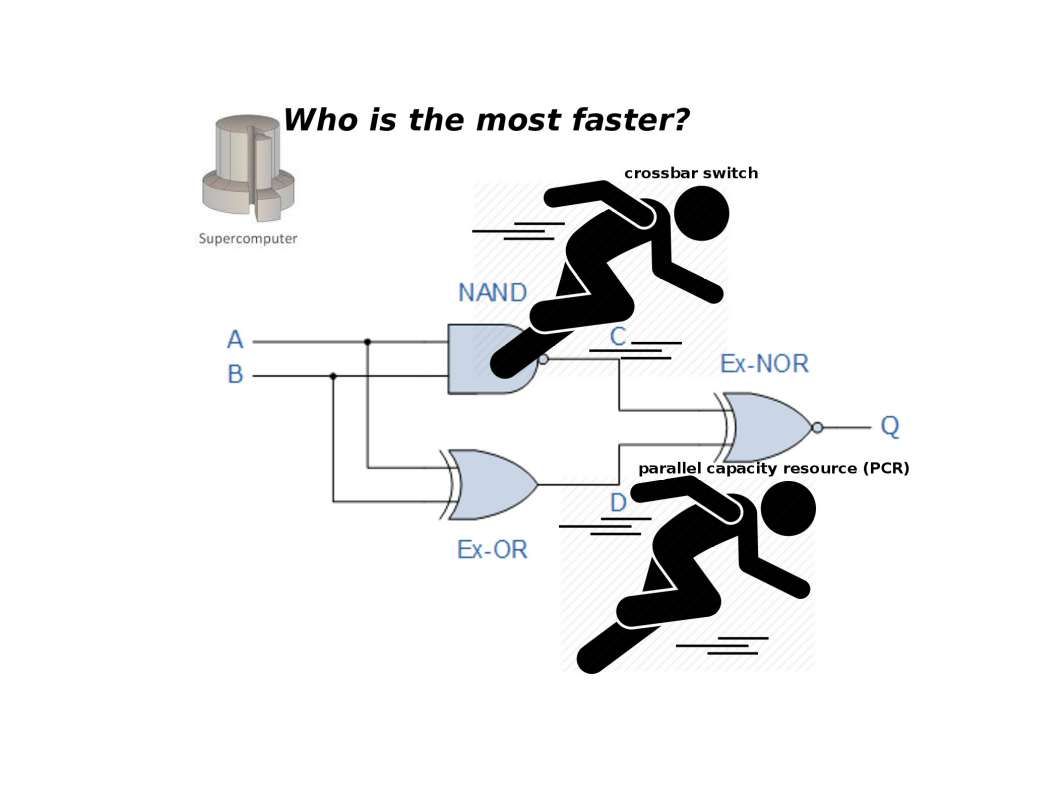
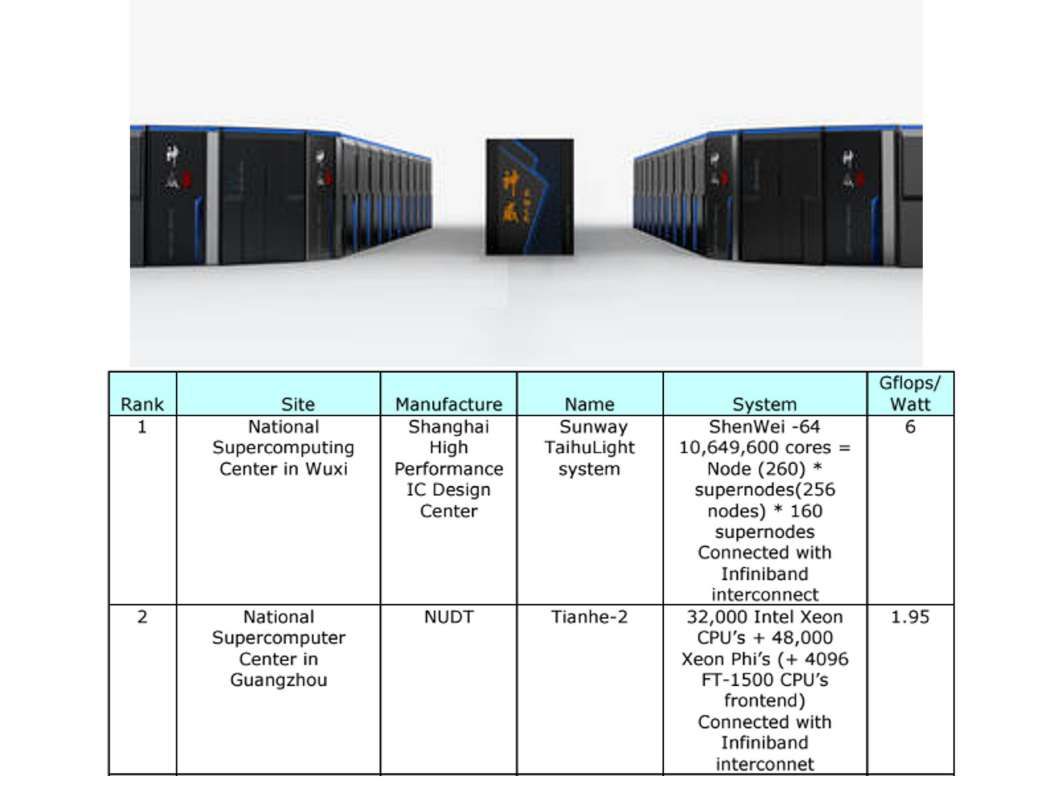
China won 1st of the TOP500 list of the world’s top supercomputers on June 2016. Can we say PCR is the mainstream? Or still keep crossbar switch deployment?
Who’s ready to break a record today?
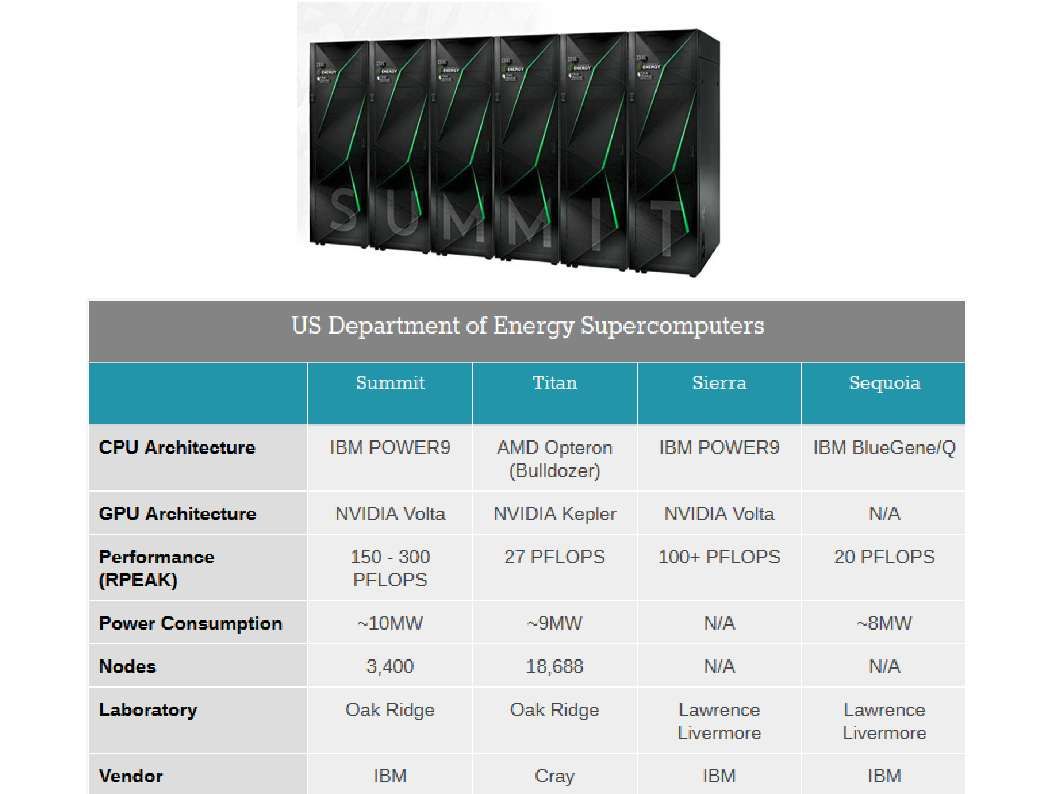
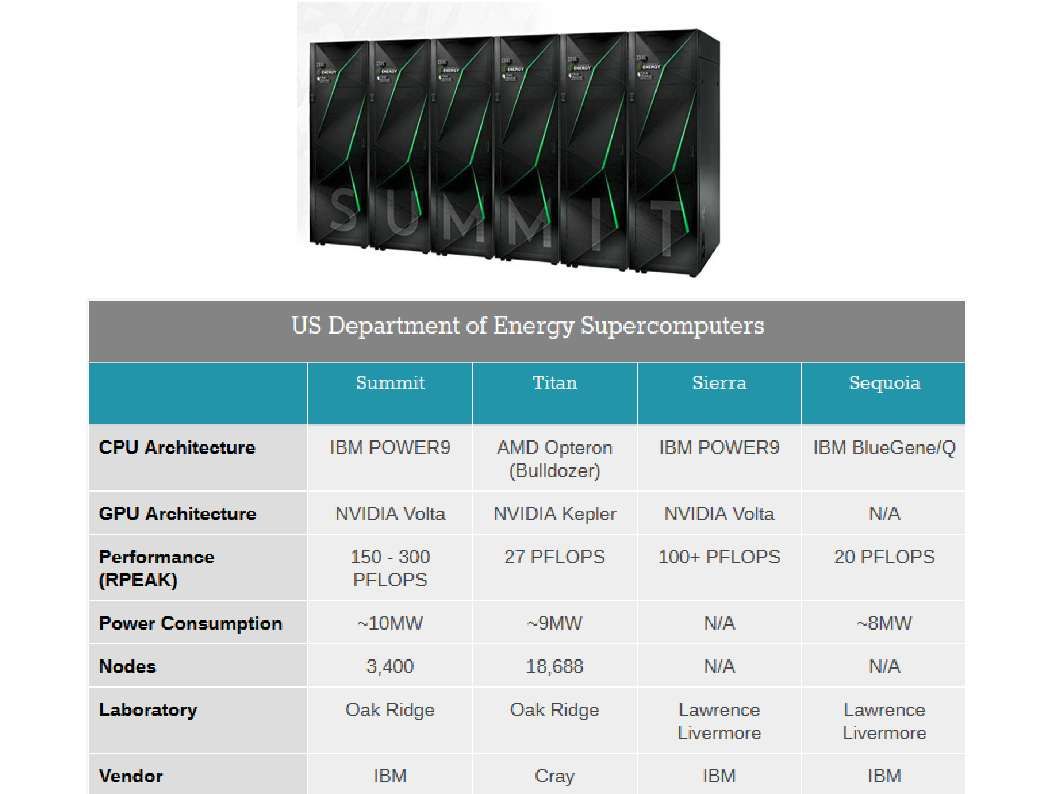
IBM announced on June 2018. SUMMIT’s do mathematical calculations at the rate of 200 quadrillion per second, or 200 petaflops.
The Sunway TaihuLight has a processing speed of 93 petaflops.
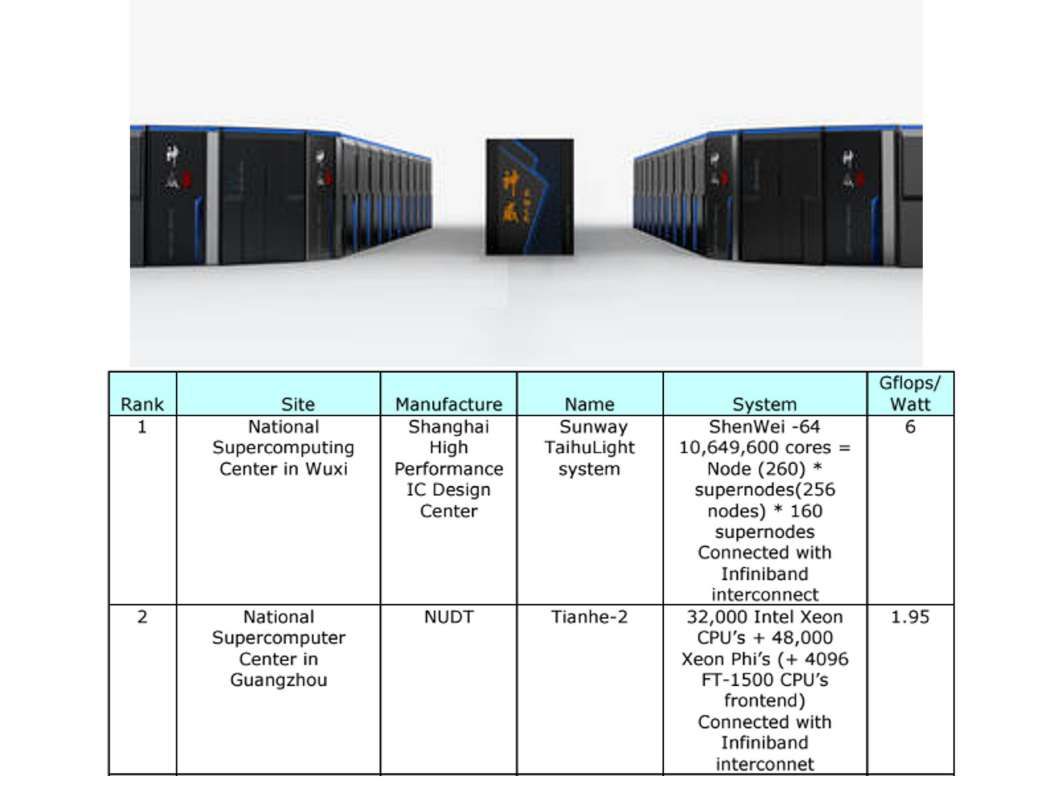
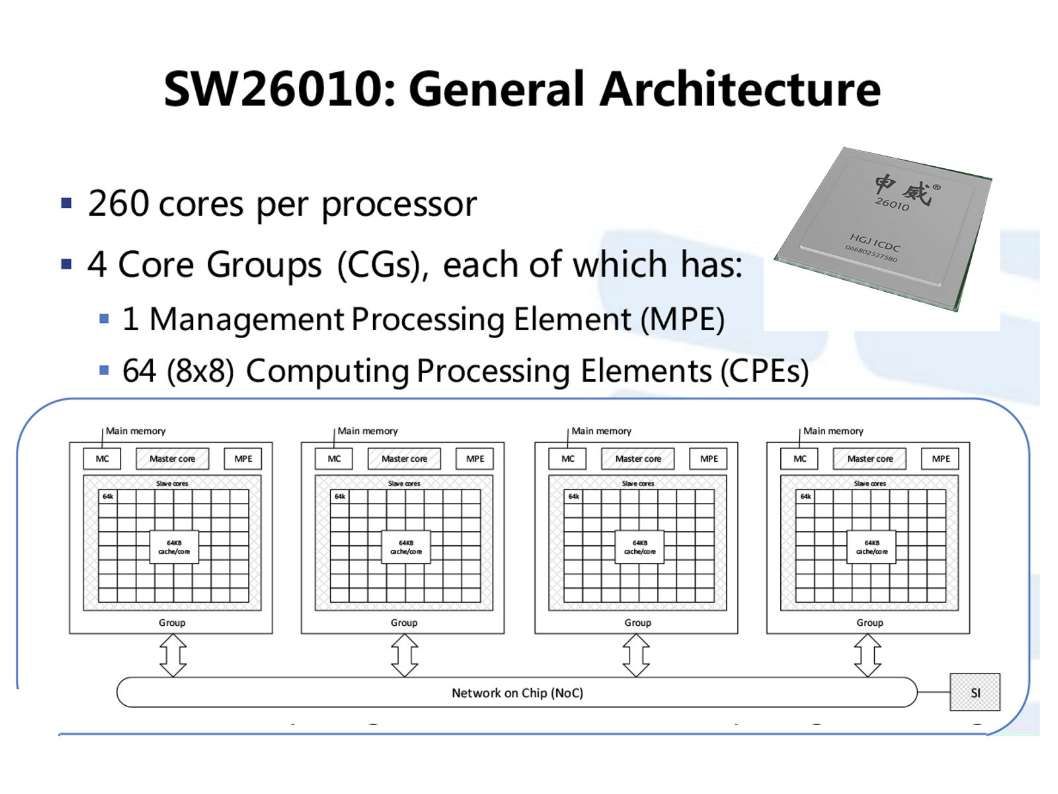
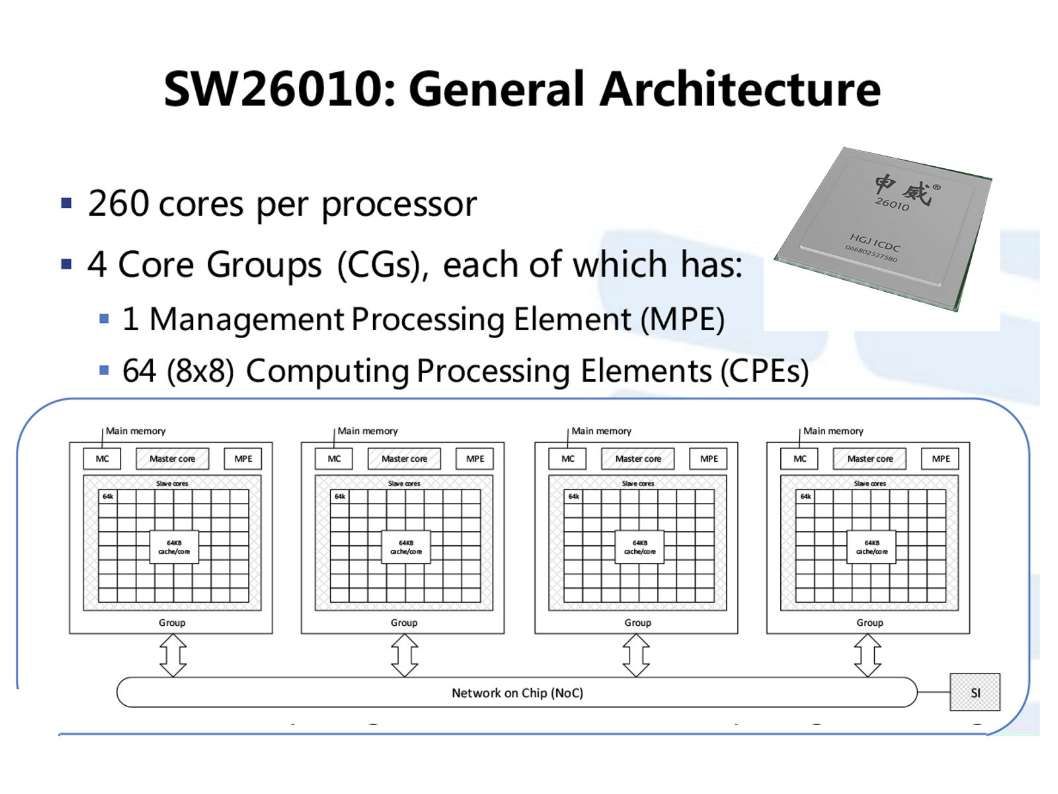
What are the key components of the Chinese supercomputer architecture?
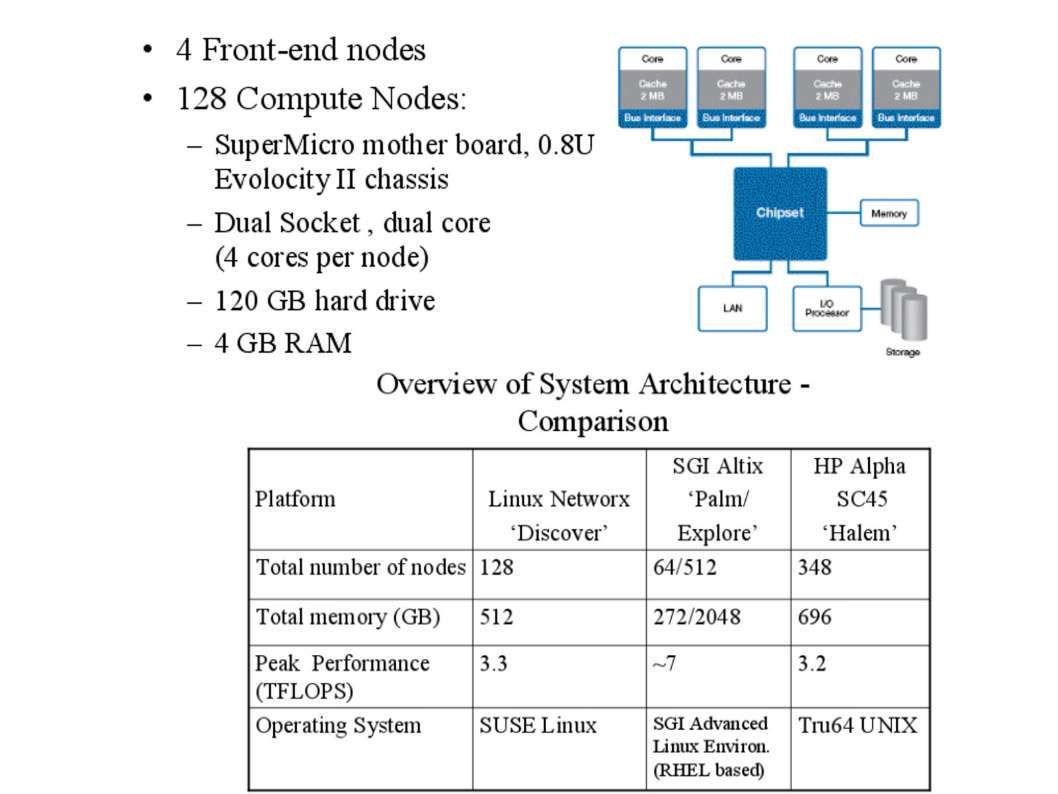
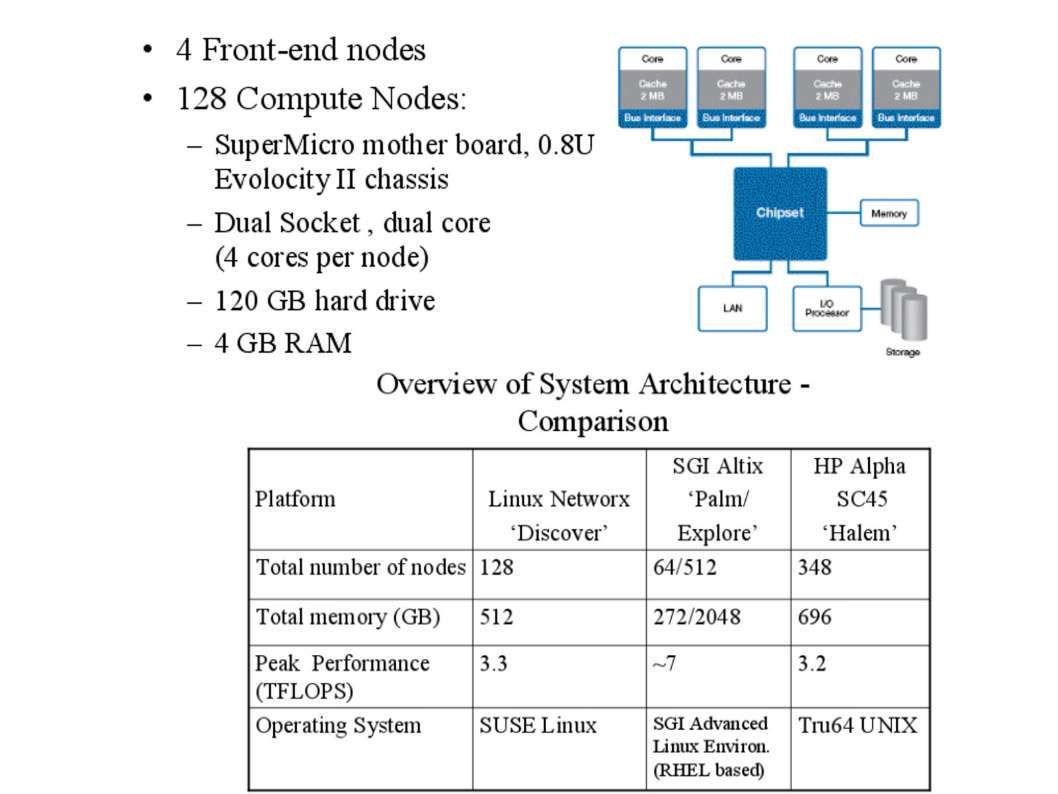
Do you remember the Parallel Capacity Resource (PCR) clusters? The mature technology found in 2002. The success of the PCR clusters was followed by the purchase of the Multiprogrammatic Capability Resource (MCR) cluster in July, 2002 from Linux NetworX (see below diagram). The PCR cluster debuted as the Top 500 Supercomputers list in November, 2002.
The Sunway TaihuLight uses a total of 40,960 Chinese-designed SW26010manycore 64-bit RISC processors based on the Sunway architecture.Each processor chip contains 256 processing cores, and an additional four auxiliary cores for system management (also RISC cores, just more fully featured) for a total of 10,649,600 CPU cores across the entire system.
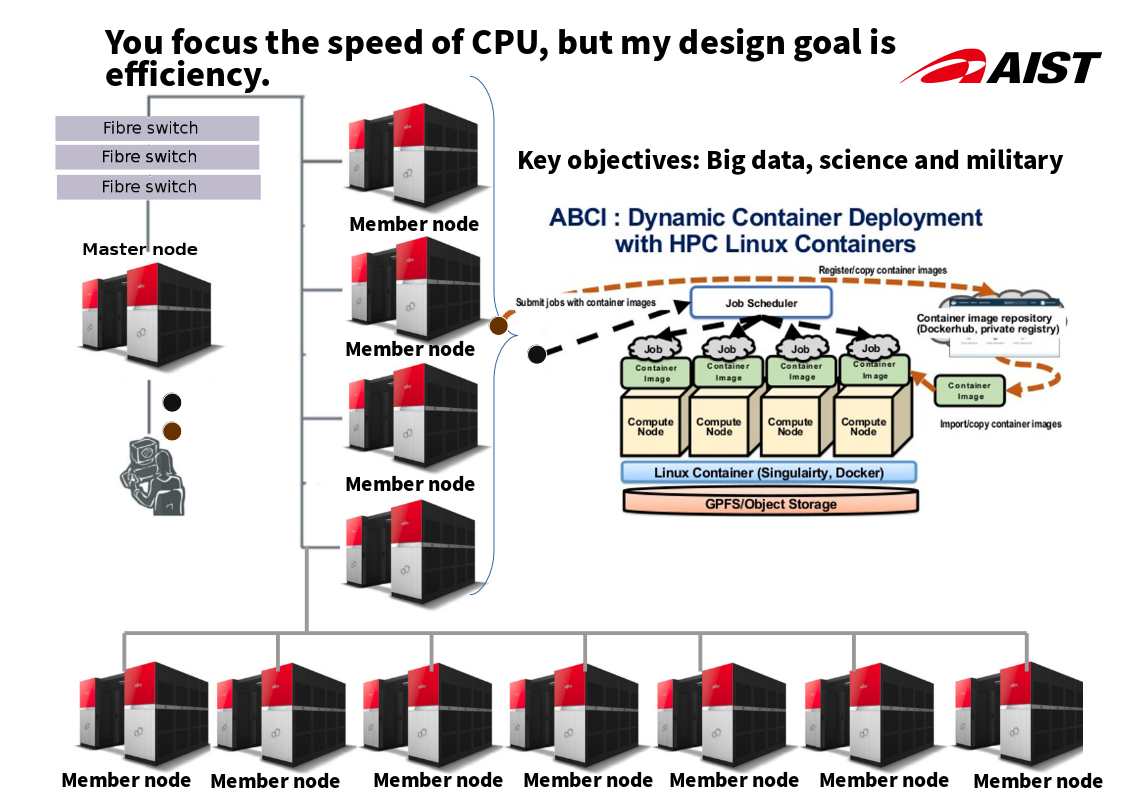
Parallel Capacity Resource (PCR) cluster architecture create the mystery power!
The differences between China supercomputer and traditional mainframe supercomputer.
I speculated that China supercomputer architecture established by Parallel Capacity Resources Cluster concept for system development. Some technical details as finger print to proof of concept. Detail is shown as below:
1. Sunway TaihuLight, with 10,649,600 computing cores comprising 40,960 nodes.
2. System OS not mentioned on technical report, however I believed that the OS kernel development on top of System V (Unix/Linux).
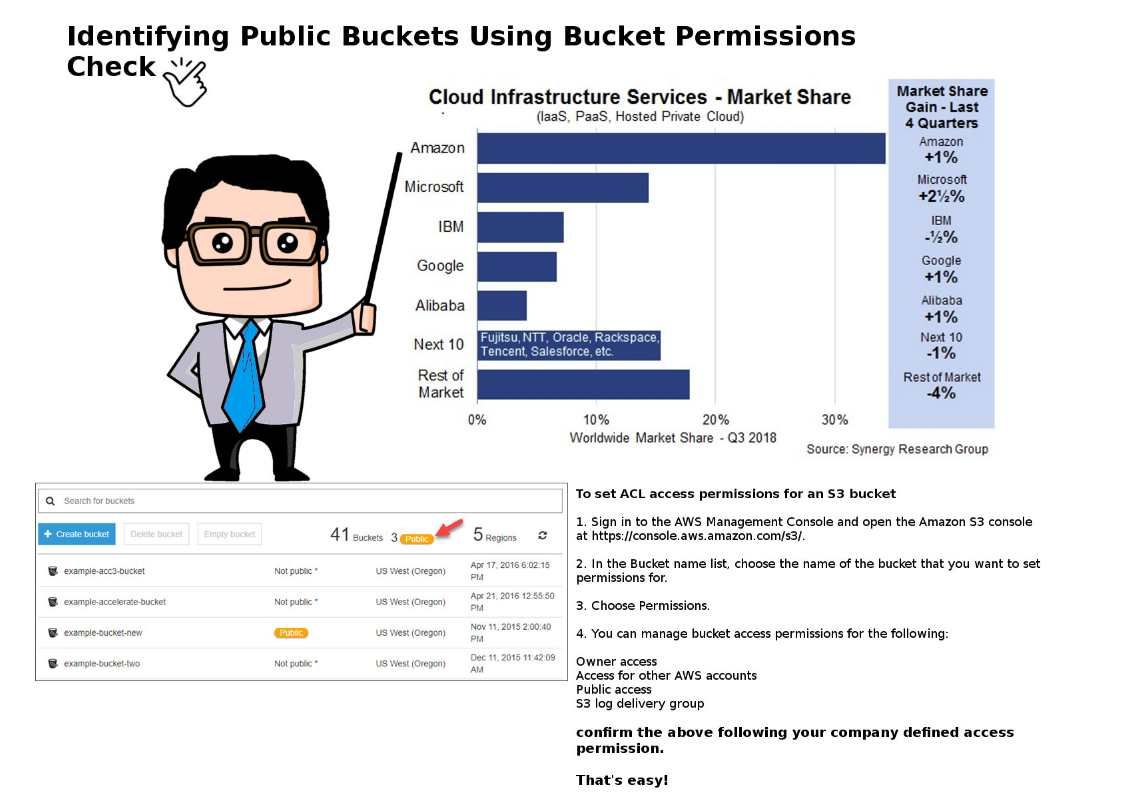
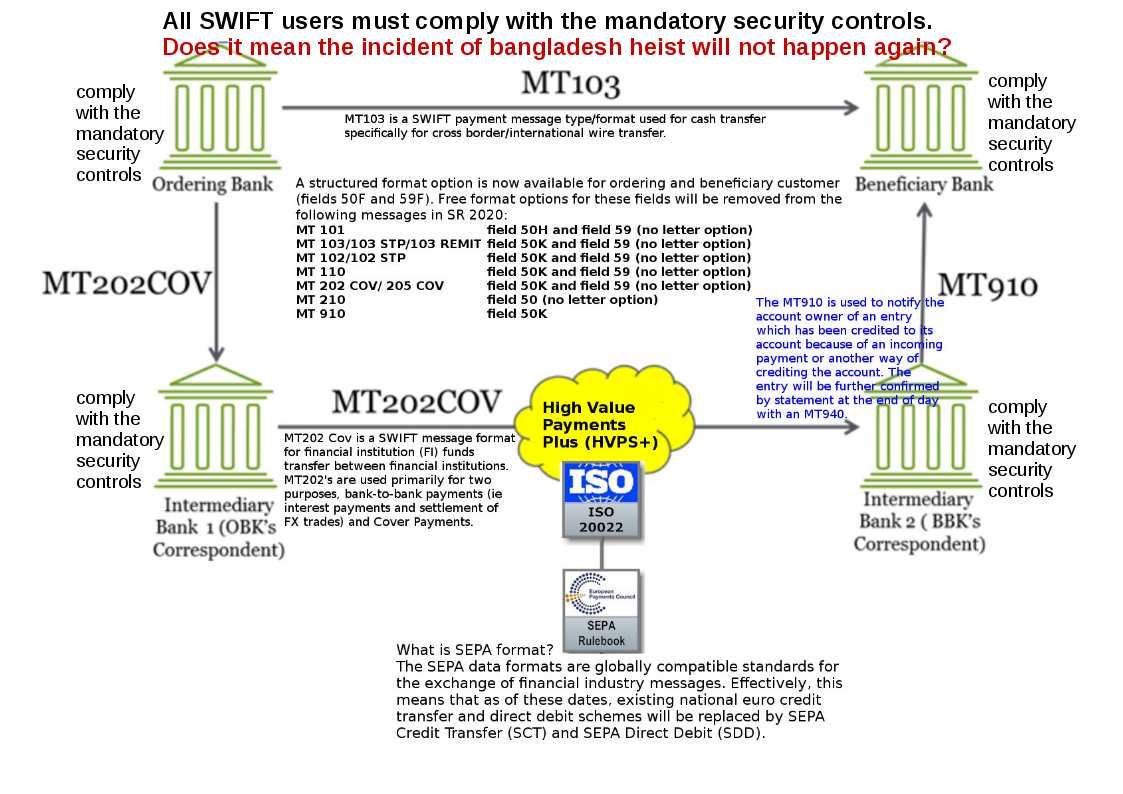
Cyber Security protection ( Linux NetworX versus IBM SUMMIT comparison)
IBM SUMMIT
Programming lanugage:
X10 is an open-source programming language being developed at IBM Research in collaboration with academic partners. The programming language designed specifically for parallel computing using the partitioned global address space (PGAS) model. A computation is divided among a set of places, each of which holds some data and hosts one or more activities that operate on those data. It has a constrained type system for object-oriented programming, a form of dependent types.
http://x10.sourceforge.net/documentation/languagespec/x10-latest.pdf
System Architecture:
Processor Security – When a partition is booted, the hypervisor initializes all of the hardware registers available to the partition to a known state. Later, when the partition is no longer running on a hardware thread, the hypervisor copies the current register contents to a save area associated with this specific logical processor. This copying of the registers is done for both dedicated and shared processor partitions. These virtualized registers are maintained in hypervisor memory (physical real memory) so that the memory cannot be altered.
Memory – The HPT (Hardware Page Table) is a mapping from the partitions address space to physical real addresses. Each partition that is created has its own HPT. Whenever a partition is running on a hardware thread, the hardware always uses the information from that partition’s HPT to translate the addressing. The HPT is part of the firmware memory usage on the server and since it is maintained only in real memory, only the PowerVM hypervisor can make changes to the HPT.
Linux NetworX and next generation
The specific cyber security did not mentioned since it priority to focusing the processing power. Should you have interest of the parallel capacity resource (PCR) computer architecture. Please refer below URL for referemce.
https://computing.llnl.gov/tutorials/linux_clusters/#Background
Reference:
The New York Times – Move Over, China: U.S. Is Again Home to World’s Speediest Supercomputer
https://www.nytimes.com/2018/06/08/technology/supercomputer-china-us.html?rref=collection%2Fsectioncollection%2Ftechnology
2016 Supercomputer magazine
2016 Supercomputer magazine