Address space layout randomization (ASLR) is a computer security technique involved in preventing exploitation of memory corruption vulnerabilities. ASLR function like the last line of defense of the system against cyber attack. Recently, security expert comment that the software application developer might not following guideline issue by CPU vendor. The fact is that an error occur on their software application when apply ASLR or SGX ( Software Guard Extensions – Intel). As a result, the non compliance application products will be available in the cyber world.
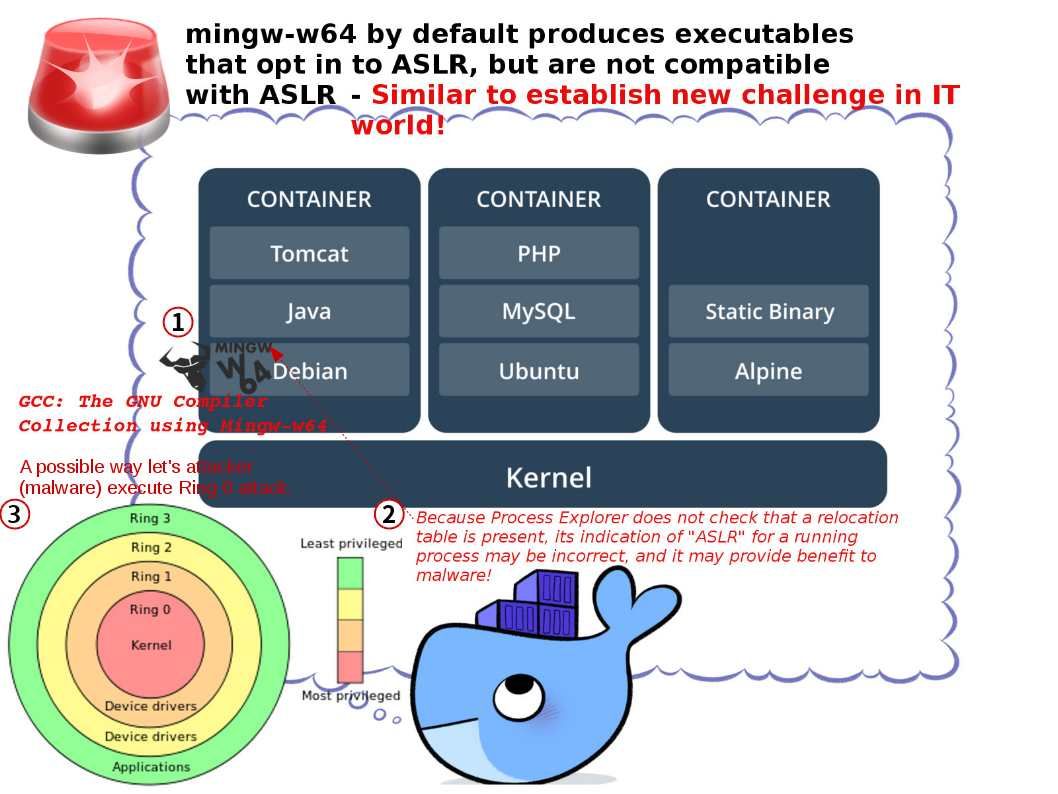
The actual scenario is that several tools that check for ASLR compatibility assume that the presence of the “Dynamic base” PE header is sufficient for ASLR compatibility. Because Process Explorer does not check that a relocation table is present, its indication of “ASLR” for a running process may be incorrect, and it may provides room for malware alive. I forseen that it may create the impact to the docker environment.
MinGW is an implementation of most of the GNU building utilities, like gcc and make on windows, while gcc is only the compiler. It looks that it has more Linux operating system includes in ASLR non compatible checklist announced by MinGW. The CPU vendor on the way to address the CPU design flaw (Meltdown and Spectre). It looks that a new form of challenge is going to join into the mistaken task force.
Should you have interest. Below hyperlink can provides the detail.
Vulnerability Note VU#307144 : mingw-w64 by default produces executables that opt in to ASLR, but are not compatible with ASLR