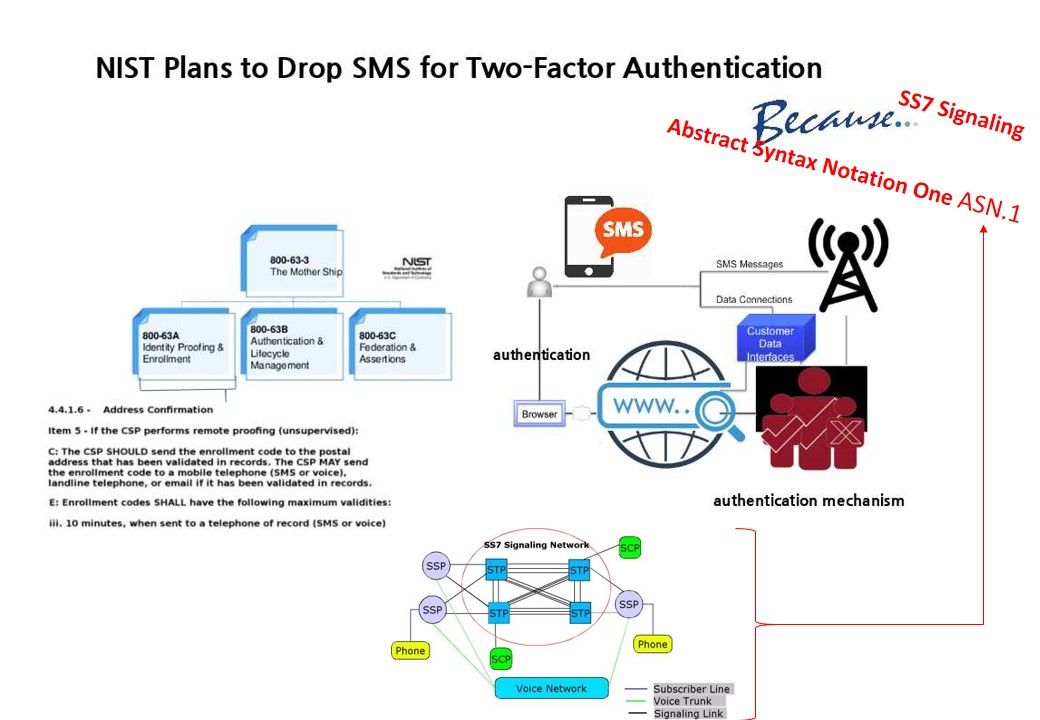
As of today, we are enjoying the security protection of 2 factor authentication with SMS-based one-time passwords (OTP). This protection mechanism was distributed widely. For instance, online banking, Visa,Master credit card online payment system and mobile application payment system. However NIST plan to retire SMS base 2 factor authentication. This decision has similar a open topic for public discussion in related industry since end of 2016. Some of the people queries of the technical standpoint of this decision.
Background – NIST-800-63-3 equivalent a bible for CSO (chief security officer) in the world. Even though you business not focusing US market. The documentation structure of NIST SP 800-63A is the subset of 800-63-3. This subset of guidelines was specify address digital identity guidelines. Item 4.4.1.6 indicate the address confirmation including SMS. (below hyperlink for official document download).
https://nvlpubs.nist.gov/nistpubs/SpecialPublications/NIST.SP.800-63a.pdf
Reference: Two-factor authentication uses two different factors of below namely, “something you have” (e.g. mobile phones), “something you are” (e.g. fingerprints) or “something you know” (e.g. password), to authenticate a user identity.
SMS messages system design limitation (see below):
- SIM swap is a type of phishing fraud that poses a serious threat to mobile phone user. As a result, all calls and texts to the victim’s number are routed to the fraudster’s phone, including one-time passwords
- SMS Messages Can Be Intercepted in Many Ways (problem in SS7)
- ASN.1 design flaw
Should you have interest of item 2 and 3? Please refer below:
SS7 flaw make two factor authentication insecure – Reveal the veil