Preface
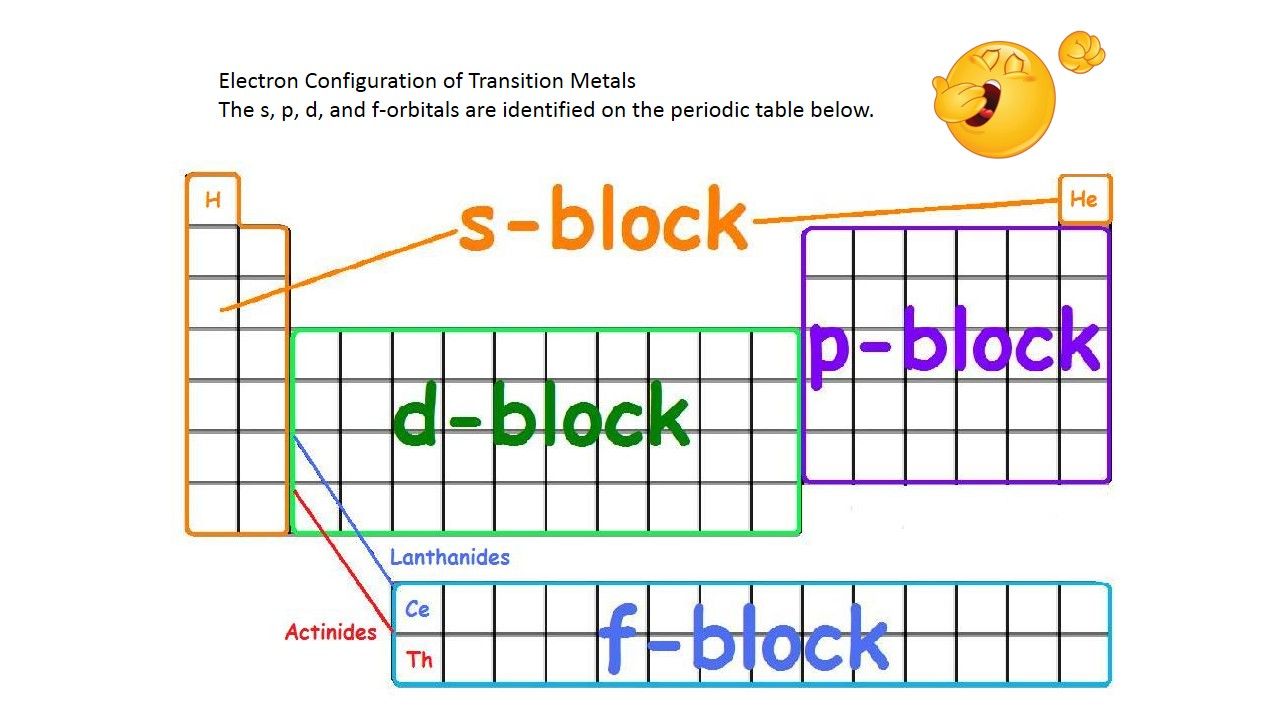
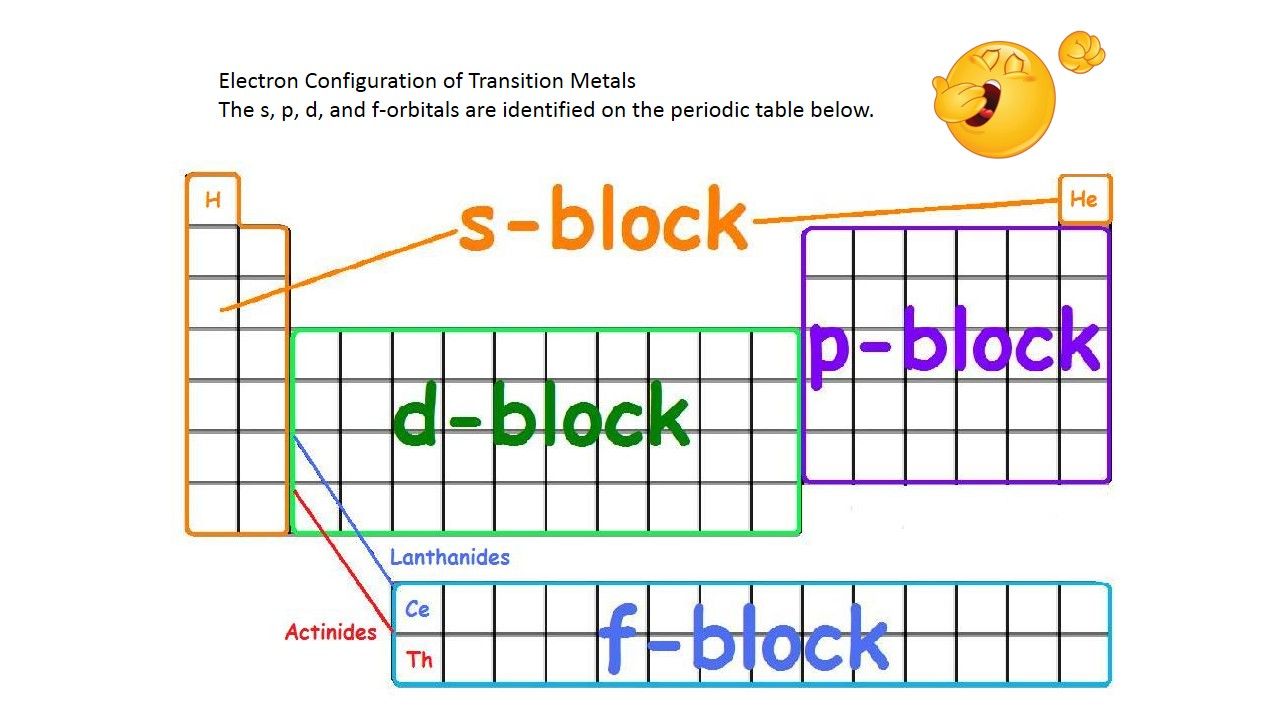
Blockchain technology is the hottest topic last few years. Actually a similar of block technology already infiltrate into our world since genesis of the world. Do you still remember that in your student age attend chemistry lesson. A boring subject introduce the four principle orbitals (s, p, d, and f) which are filled according to the energy level and valence electrons of the element (see below for reference). They are the block chain fundamental concept.
The genesis did not mentioned in high profile until blockchain technology do the renovation!
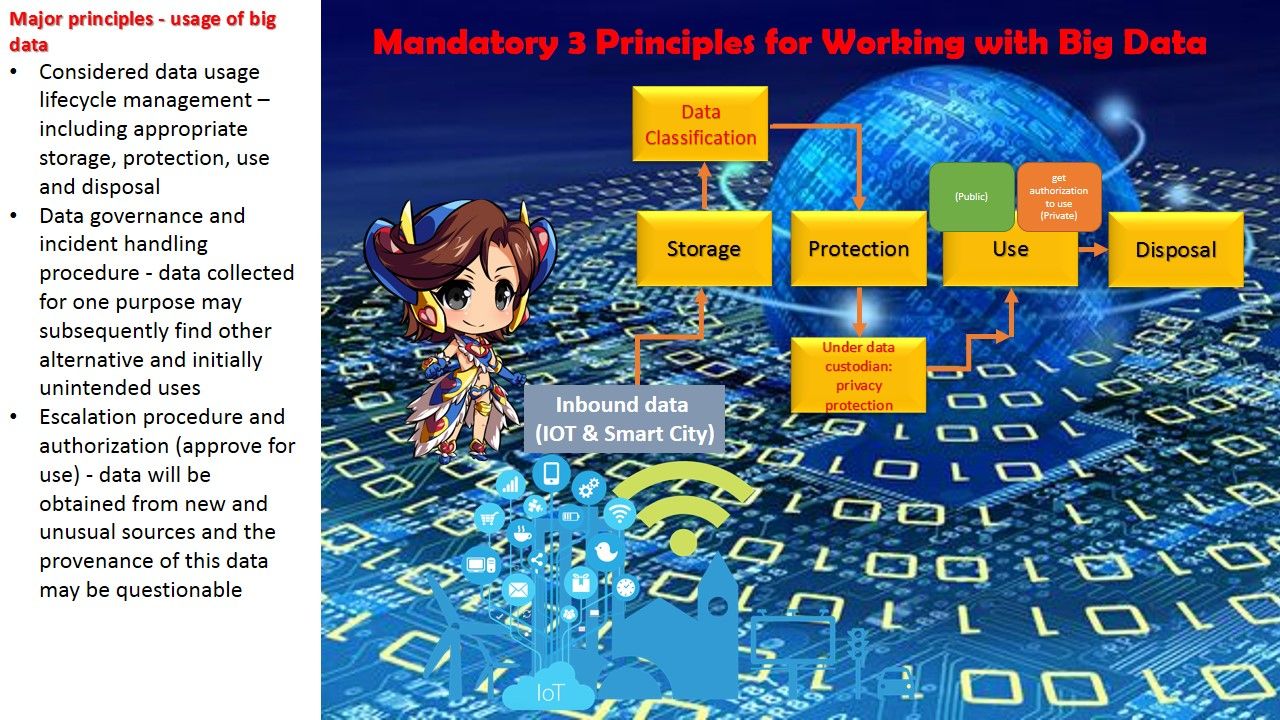
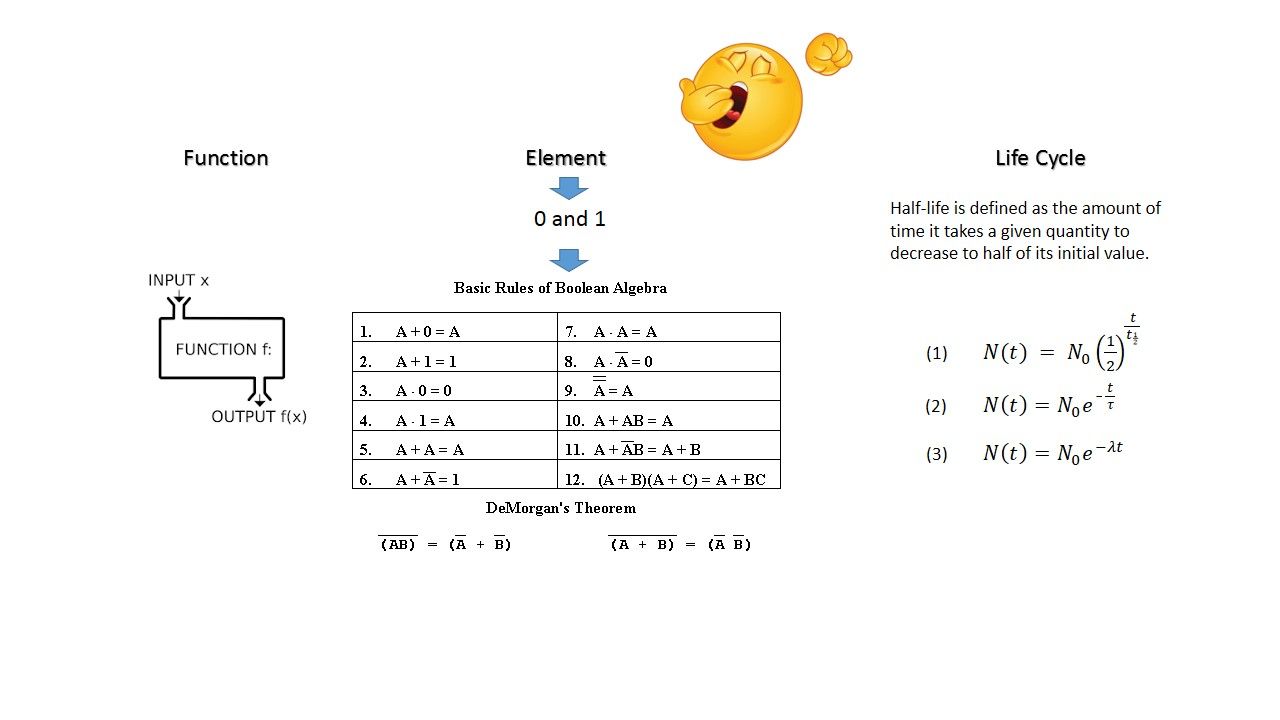
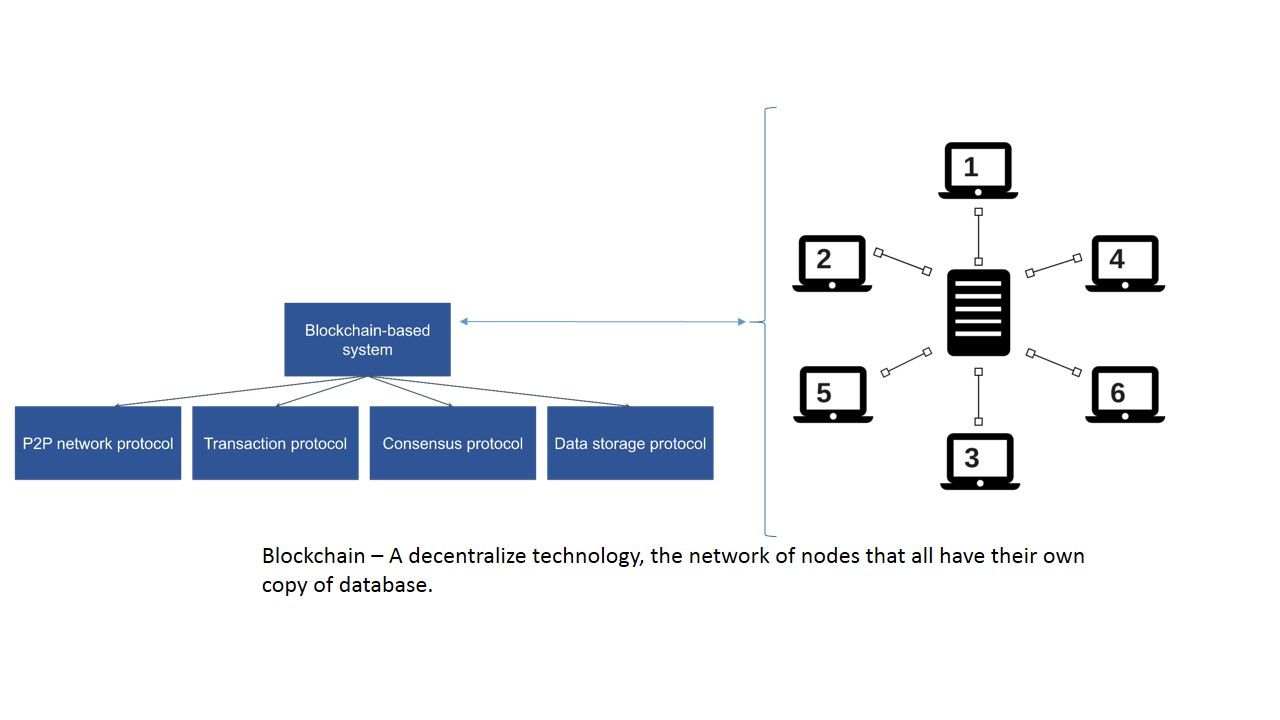
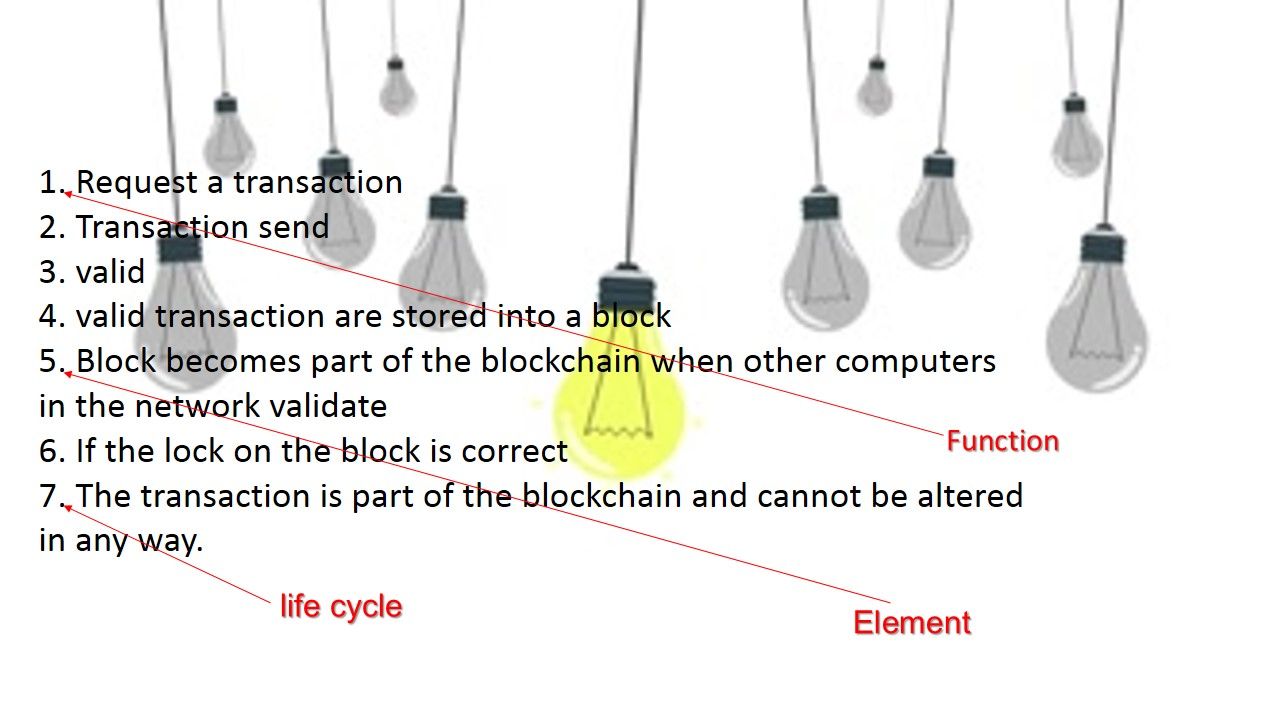
We are easy to find out the key elements of blockchain on internet. According to my observation so far, the result might not similar. My observation summary are function, element and the lifetime (life cycle). See below details for reference (another boring diagram)
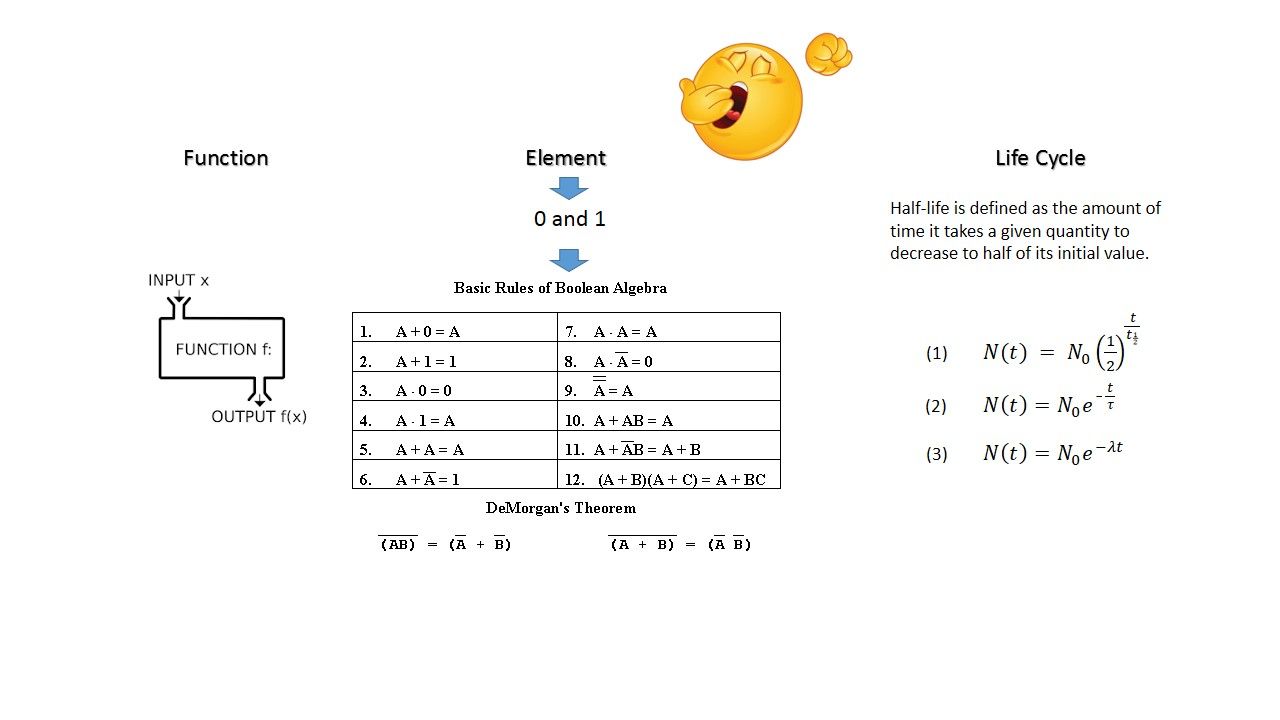
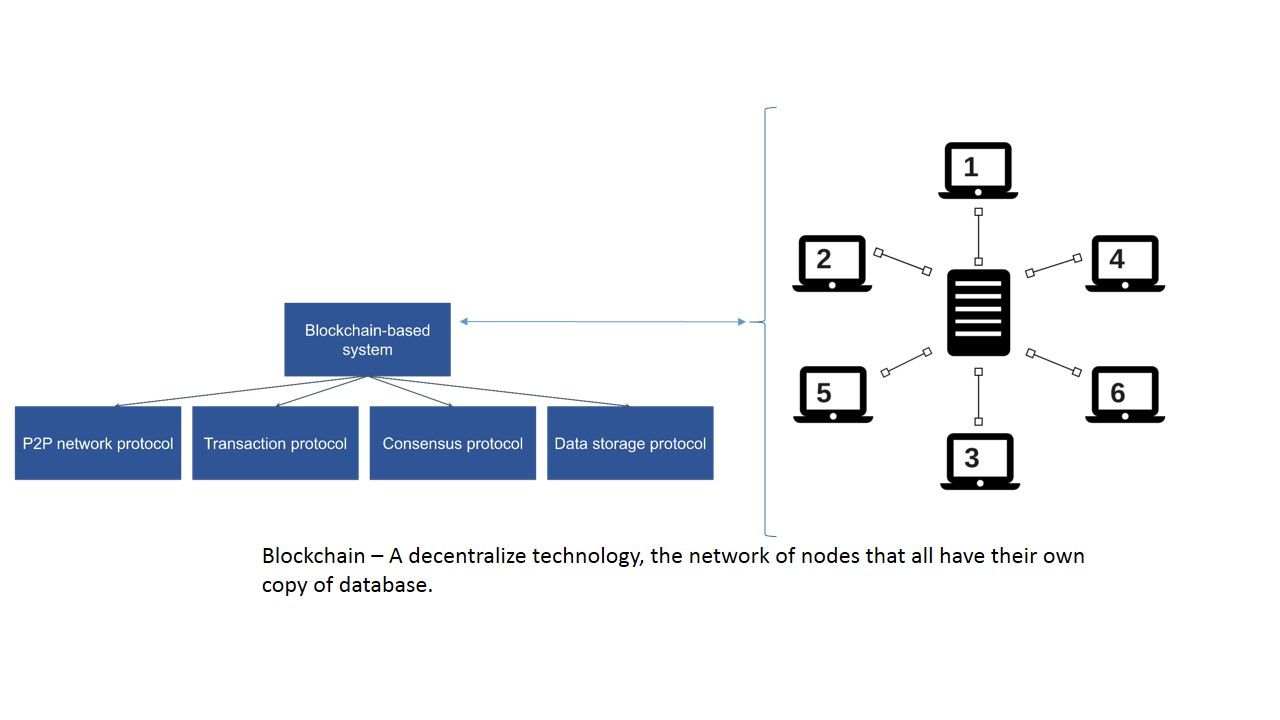
The blockchain technology reveal those three items of key element since Bitcoin currency concept found 90’s. Bitcoin was invented by an unknown person or group of people under the name Satoshi Nakamoto and released as open-source software in 2009. The first impression of blockchain to the world is crypto currency (Bitcoin) until ENIGMA found another new idea of concept and announced to public in 2017.
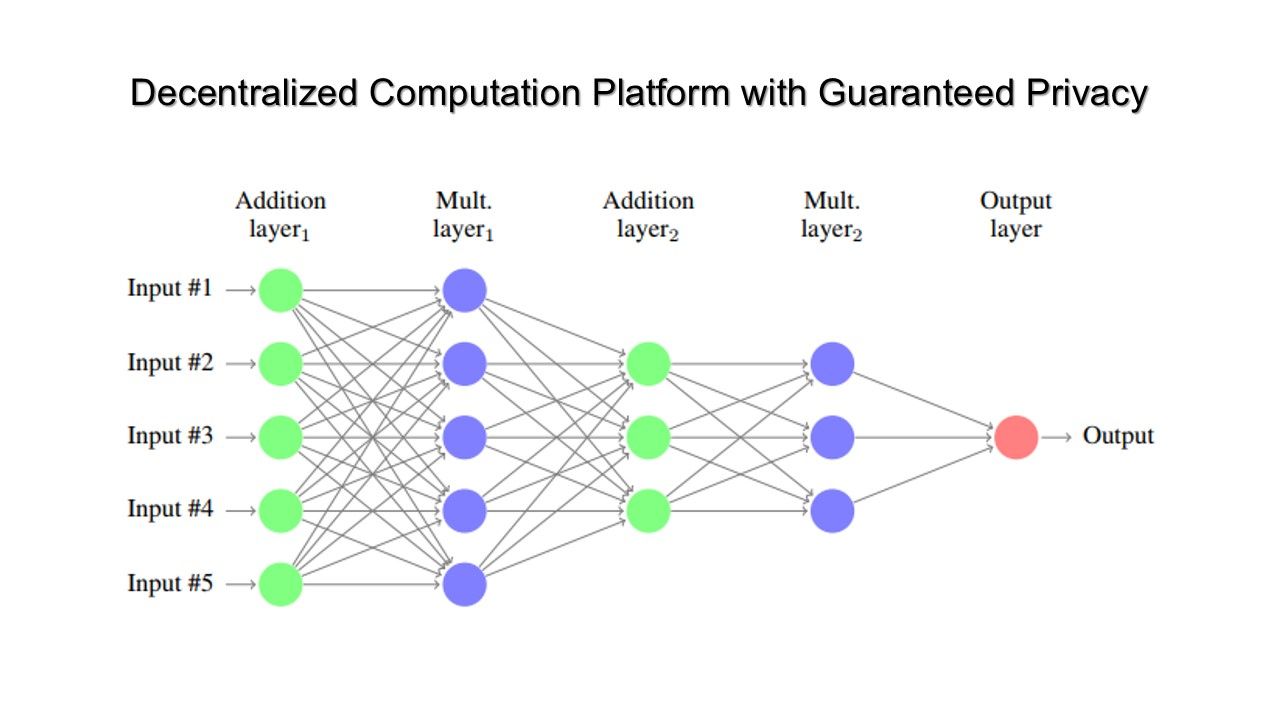
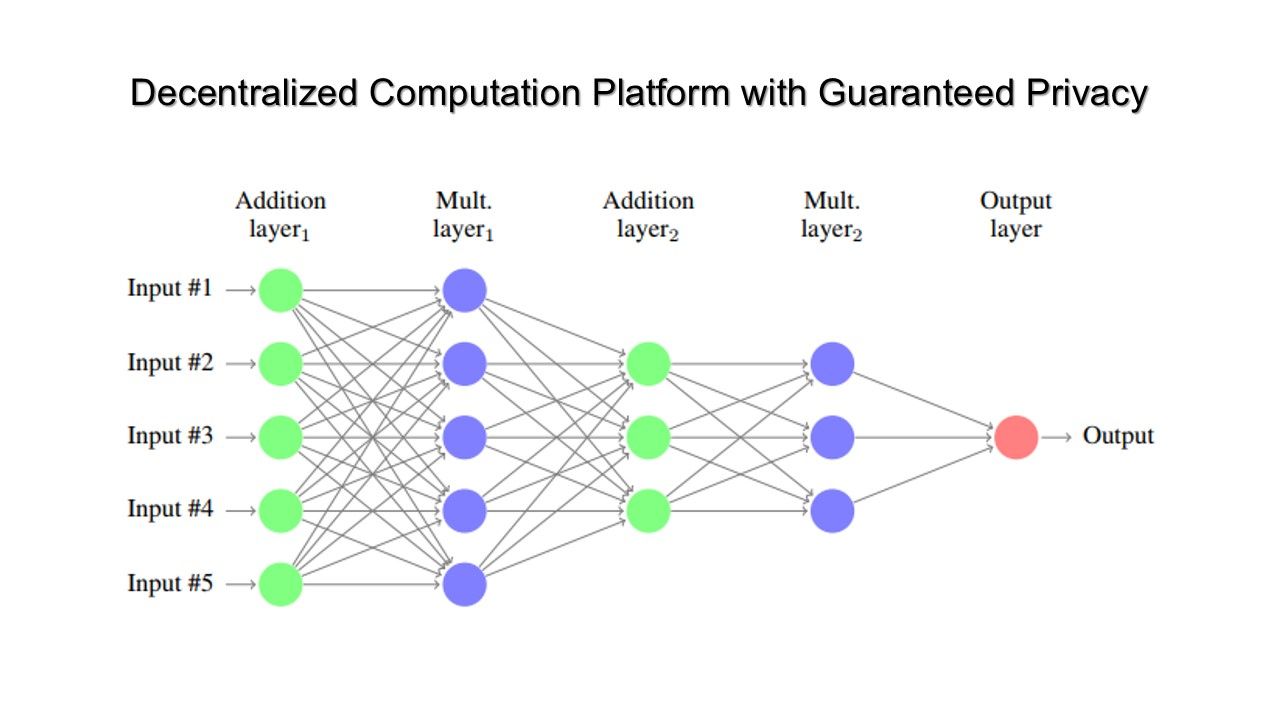
Modern world concerning data privacy blockchain can do it better
In reference to technical article (Decentralized Computation Platform with Guaranteed Privacy) written by Guy Zyskind, Oz Nathan and Alex ’Sandy’ Pentland. It shown that an advanced encryption scheme (secure multi-party computation) provides more advance benefits comparing with key encryption concept.

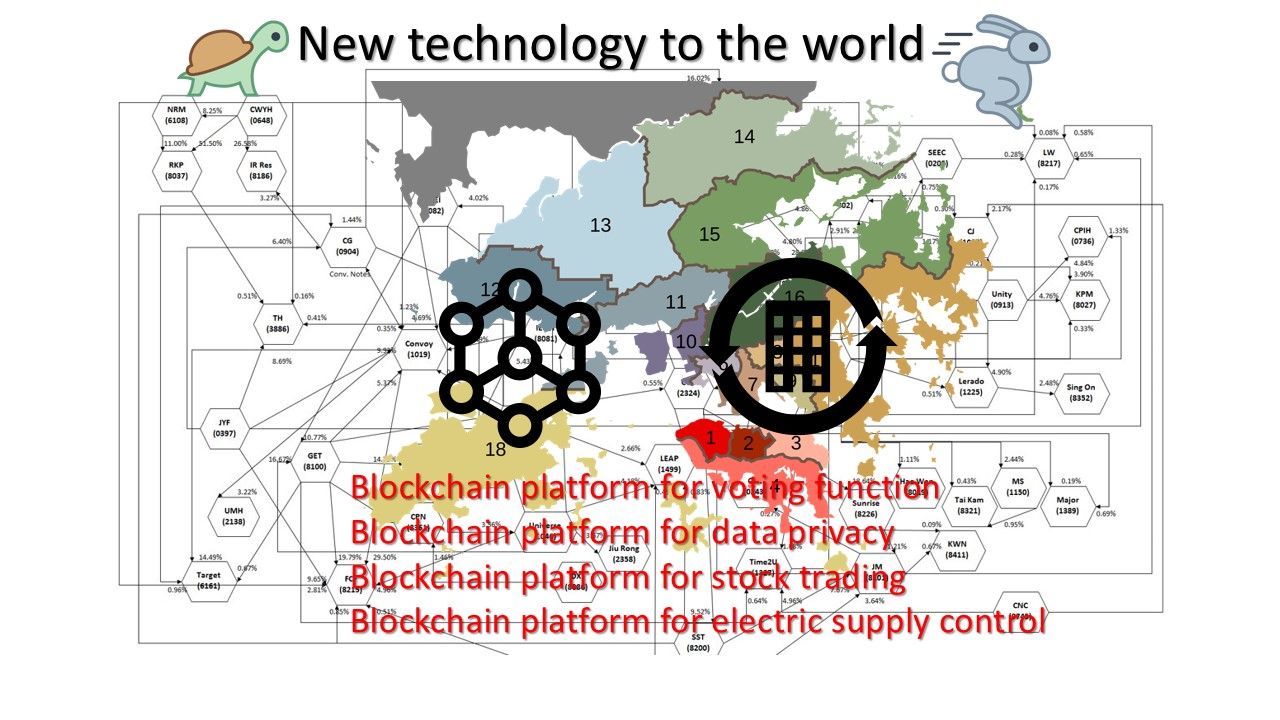
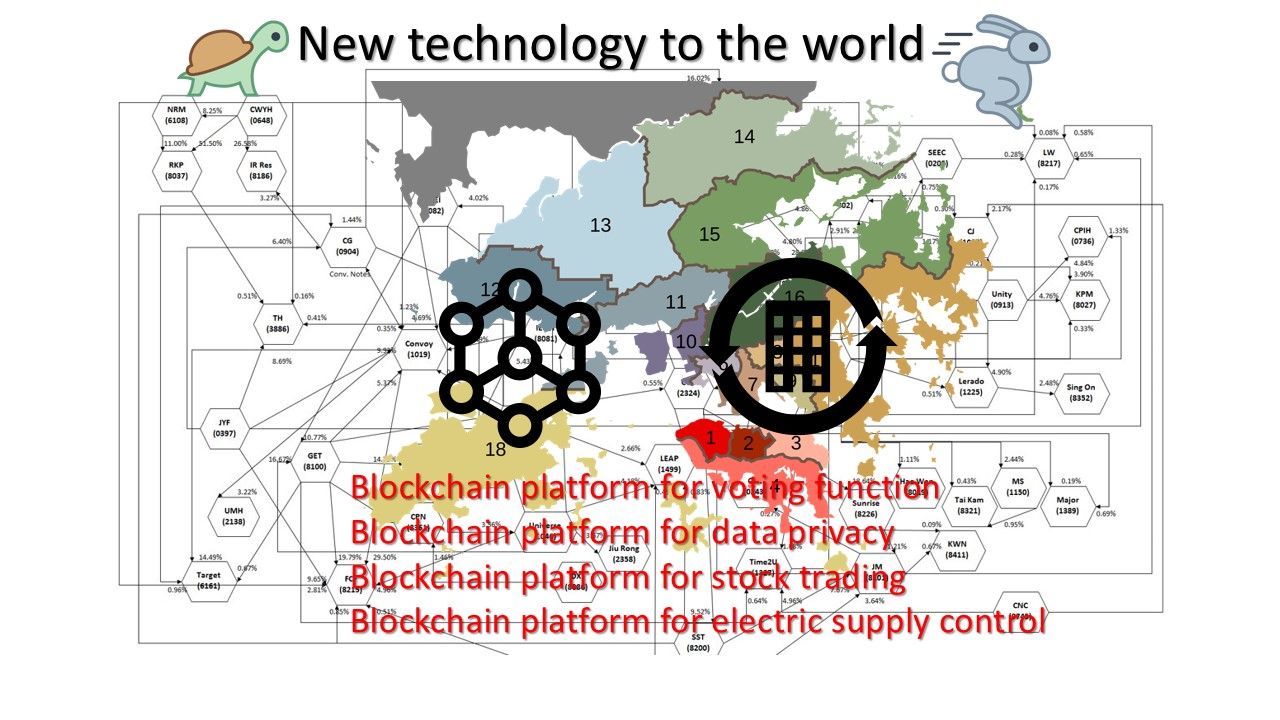
Blockchain technology shown his expandable feature to the world he is not limit to cryptocurrency.
Enigma technology pioneer to introduce the expandability on blockchain features (see below):
Data marketplace, secure backend, internal compartmentalization, N-Factor authentication, identity,IoT, distrubuted personal data stores, crypto bank, E-Voting and Bitcoin Wallet.
Feature highlight
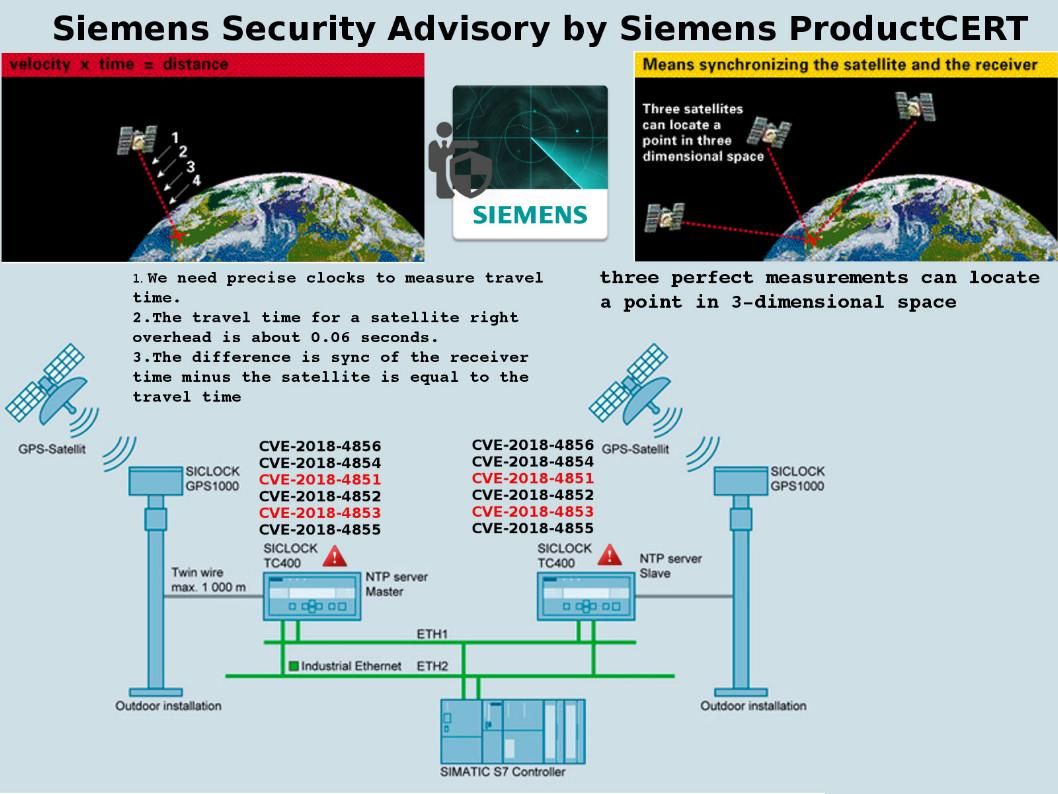
IoT: A fundamental weakness of IoT technology in regards to storage, manage and use (the highly sensitive) data collected by IoT devices in a decentralized area (trustless cloud). Blockchain technology is able to strengthen design weakness in data security area.
Transport layer security: We know traditional TLS (SSL) technology contained fundamental design weakness. Even though you are now using TLS 1.3, it is hard to guarantee the asymmetric cryptography will be encountered another vulnerability in future.
E-Voting: An data breach occurred last year (2016) on election of US president. Russian hackers targeted 21 US states’ election systems in last year’s presidential race. Blockchains are governed by a set of rules called the consensus protocol. These rules define which changes are allowed to be made to the database, who may make them, when they can be made. There are currently two main types of consensus protocol:
Proof of Work (PoW) and Proof of Stake (PoS)
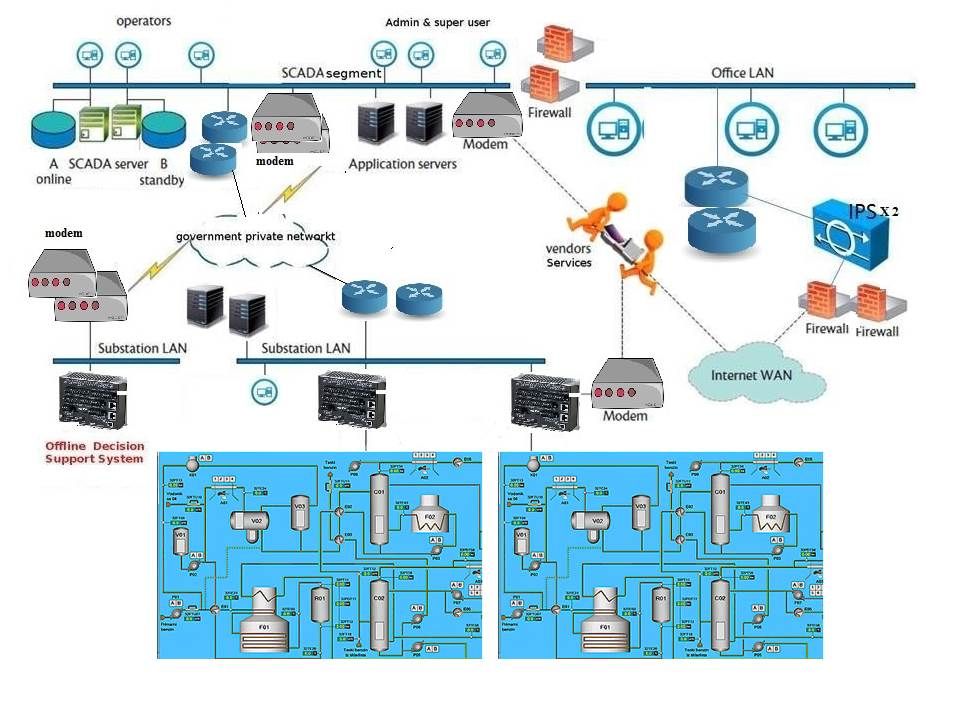
Build a multi-environment secure infrastructure avoid data breach
We noticed that banking industry have tough and demanding compliance requirements. Some sort of policy they are not able to outsource the hosting facilities to cloud computing environment. As a matter of fact, I totally agree with their auditors concerns of data ownership and governance of data. We heard a data breach on Amazon Simple Storage Service (S3) — Cloud Storage this year. However the on-going technology trend is going to do the system integration to cloud computing. It looks that the IT world no way to escape the cloud technology integrate to their IT infrastructure. Block chain technology itself embedded strong encryption feature which can replace traditional network transport and data protection mechanism. Even though hacker break through the public cloud computing farm, hacker not easy to decrypt the data.
How about ransomware attack?
Blockchain solutions are decentralized – a scenario may happen that ransomware encrypted the data belongs to specifics cyber victim. But another range of clients may not affected.
Who’s is ready to playing this game?
Let’s do a review on current cloud facilities located in APAC country. In the meantime AWS did not install their hosting in China and Hong Kong. But service (blockchain-as-a-service) is available,The nearest zone which have AWS hosting facility installed is Singapore. In such a way bring the advantage to Microsoft Azure cloud became a market leader in this area (see below reference).

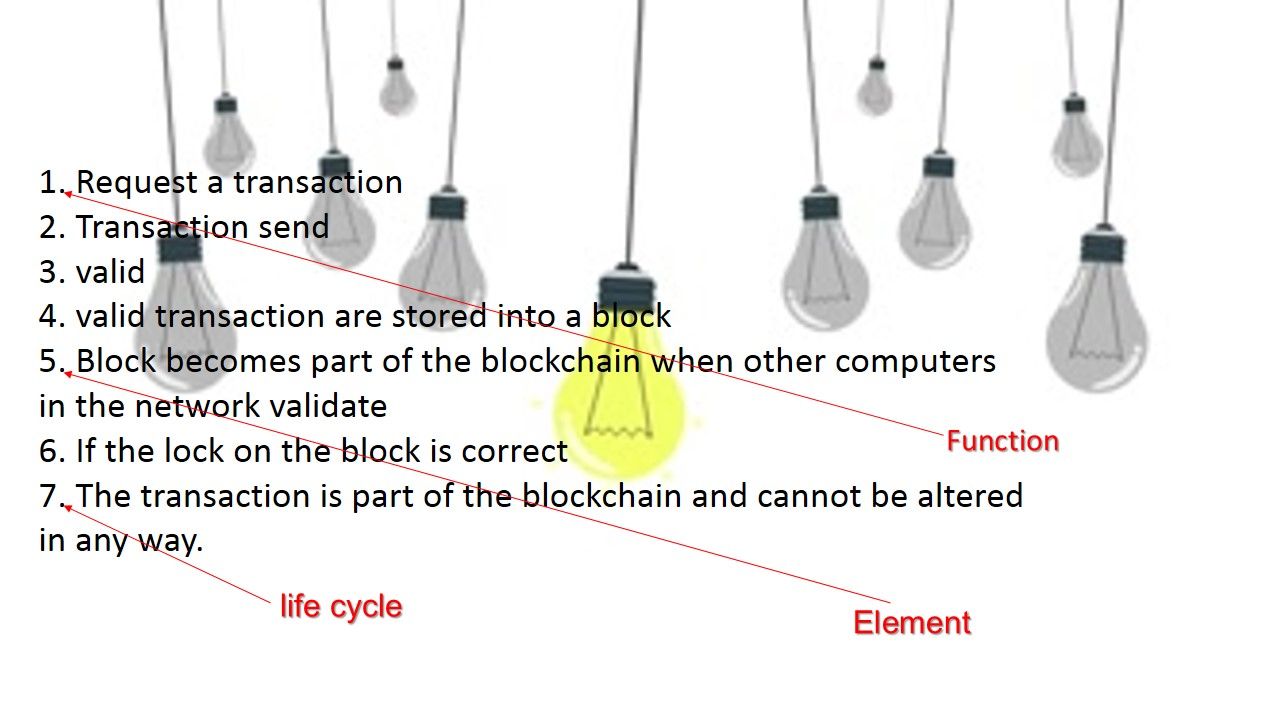
According to the blockchain key elements: function, element and life cycle. Blockchain can conduct like a theory apply to technology world without limitation.
Let take a closer look of blockchain processing sequence. The key elements are indicated on the diagram below.
Summary:
For those country who would like to implement the Smart City. Blockchain technology is the key project element which they cannot escape.
A Breakthrough for City Innovation driven by blockchain technology
- Single-sign-on facility provides every registered citizen with a free verified login with which they can securely connect and transact both locally and globally across both public and private services.
- A secure platform for innovation.
- Provides integrated solutions for local commerce across retailers, service providers, dining, and lodging internal system migrate to the cloud (blockchain-as-a-service).