Stuxnet a famous malware to sabotage Iran’s nuclear program. From technical of view, malware change the shape of computers in the world convert to a cyber weapon. Who’s the team take responsibility? For sure that is not you and me.
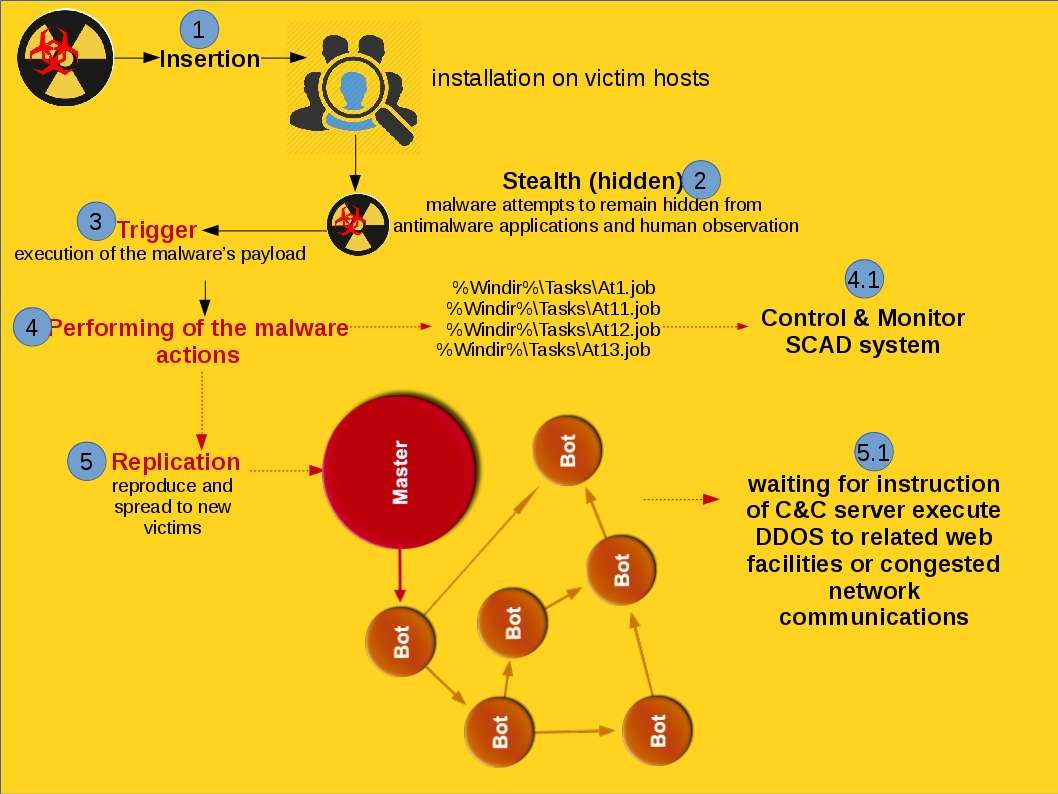
Stunext attack scenario:
Heard that malware activities in South Korea run serious recently. Headline news were told the military defense of south Korea was hacked. Regarding to the articles the goal of such malware attack focus South Korean nuclear facility. We don’t have related information and not going to predict who is the attacker of this incident. But malware focus nuclear power facilities not only occurs today. Stuxnet, Duqu, and Flame are categories hardcore type malware. The hardcore type malware usually achieve the following actions.
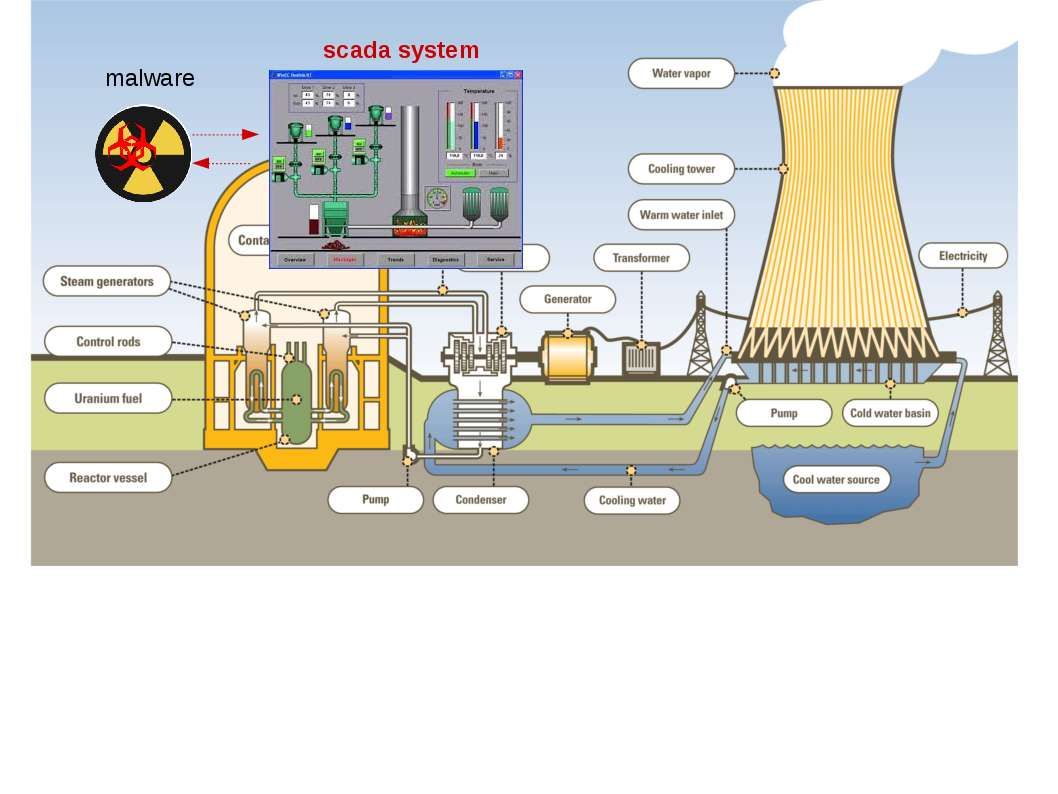
Do you think SCADA system is the culprit of attack on nuclear power system?
What is SCADA?
SCADA is an acronym for Supervisory Control And Data Acquisition, which is a computer system for gathering and analyzing real-time data.
Where is SCADA used?
SCADA systems are used to automate complex industrial processes where human control is impractical. The SCADA systems benefits to control and monitor processes. Thereby it used in large applications such as monitoring and controlling a nuclear power plant.
SCADA application:
WinCC (Siemens Simatic HMI WinCC v7.3 (x86/x64)) provides all the functionality of SCADA for Windows for all industries.
Historical incident record:
June 2010 – Stuxnet relies on MS zero day implant malware granted control and monitor functions in SCADA system.
Malware attack triggered by Microsoft Zero day (MS08-067, MS10-046 & MS10-061)
Malware relies on vulnerability (CVE-2010-2772) and execute privileges escalation on database of WinCC MSSQL server. As a result hacker allow to view information on SCADA system.
Oct 2011 – Duqu executables share injection code with the Stuxnet worm. The Duqu design was based on the same source code as Stuxnet. The similarity of features shown as below:
- Duqu use XOR based encryption for strings (key: 0xAE1979DD)
- Decrypted DLLs are directly injected into system processes instead of dropped to disk.
- Rootkit to hide its activities
May 2012 – Flame malware targeted cyber espionage in Middle Eastern countries.
The researchers say that Flame may be part of a parallel project created by contractors who were hired by the same nation-state team that was behind Stuxnet and its sister malware, DuQu.
The number and geographical location of Flame infections detected by Kaspersky Lab on customer machines.
- Iran = 189
- Israel Palestine = 98
- Sudan = 32
- Syria = 30
- Lebanon = 18
- Sudi Arabia = 10
- Egypt = 5
Apr 2016 – Virus:Win32/Ramnit.A, German nuclear plant infected with computer virus. As Reuters reports, viruses with names like “W32.Ramnit” and “Conficker” where found in a computer system that deals with data visualization.
The virusesWin32/Ramnit.A is a file infector with IRCBot functionality which infects .exe, and .HTML/HTM files, and opens a back door that compromises your computer.
- File MD5: 0x5CC31D49CAFC508238259616583332A2
- File SHA-1: 0xC775A22B4B150989F57AB129591F4DA328F52B7C
Aug 2016 – Virus:Win32/Ramnit.A (checksum changed)
- File MD5: 0x25C1DE8838ADBC0DCFF61E6B44458CF4
- File SHA-1: 0xDF6B04BA2103B2EB43B51EBDFB705A37BE5F28A9
1st Oct 2016 – Headline News: Rep. Kim Jin-pyo, a lawmaker of the main opposition Minjoo Party of Korea, told Yonhap News Agency in a telephone interview that the hacking targeted the “vaccine routing server” installed at the cyber command.
Interim summary:
SCADA systems are used to automate complex industrial processes where human control is impractical. The SCADA systems benefits to control and monitor processes. Thereby it used in large applications such as monitoring and controlling a nuclear power plant. WinCC (Siemens Simatic HMI WinCC v7.3 (x86/x64)) provides all the functionality of SCADA for Windows for all industries. Since zero-day vulnerability found each week especially Miscrosoft products. Do you think SCADA system is the culprit of attack on nuclear power system?
The project development of Nuclear power budget huge amount of money and covered with disaster recovery plan. Do you think current disaster recovery plan will cover up Zero day attack on SCADA system? What do you think?
Spot on with this write-up, I actually think this website wants far more consideration. I抣l in all probability be again to learn much more, thanks for that info.
It抯 hard to seek out educated folks on this topic, however you sound like you recognize what you抮e speaking about! Thanks
A lot of thanks for all of your hard work on this web page. Ellie delights in getting into investigation and it’s obvious why. My partner and i learn all about the powerful mode you produce great ideas via this web blog and as well welcome contribution from people on this matter so my simple princess has been discovering a lot of things. Take pleasure in the rest of the year. You’re performing a powerful job.
I抦 impressed, I must say. Really hardly ever do I encounter a blog that抯 both educative and entertaining, and let me inform you, you may have hit the nail on the head. Your thought is outstanding; the problem is something that not enough persons are speaking intelligently about. I’m very completely happy that I stumbled across this in my seek for something relating to this.
Spot on with this write-up, I truly think this web site wants way more consideration. I抣l probably be once more to read way more, thanks for that info.
This really answered my problem, thank you!
Youre so cool! I dont suppose Ive read anything like this before. So nice to seek out any person with some original thoughts on this subject. realy thank you for starting this up. this web site is something that is wanted on the internet, somebody with a little bit originality. useful job for bringing something new to the web!
Thank you so much for providing individuals with such a brilliant possiblity to check tips from this site. It can be so terrific and stuffed with fun for me and my office fellow workers to search your website at the least 3 times in one week to read the latest issues you have. And indeed, I am just certainly impressed for the great hints served by you. Certain 3 facts in this posting are rather the most suitable we’ve ever had.
Your house is valueble for me. Thanks!?
WONDERFUL Post.thanks for share..more wait .. ?
you have an awesome weblog right here! would you prefer to make some invite posts on my weblog?
WONDERFUL Post.thanks for share..extra wait .. ?
Needed to draft you this very small word to thank you very much as before regarding the unique strategies you have featured here. This is simply incredibly generous of you to offer openly just what a few people could possibly have made available for an ebook to help make some profit for themselves, especially seeing that you could possibly have tried it in case you decided. These guidelines likewise acted to become good way to be sure that most people have a similar dream similar to my very own to learn great deal more concerning this condition. I think there are many more pleasurable moments ahead for individuals who view your blog post.
Needed to draft you a very little observation to say thanks as before for your personal striking principles you have shown on this website. It’s quite seriously open-handed of you to make unreservedly exactly what many of us would have supplied for an electronic book in making some dough for their own end, principally given that you might well have tried it if you ever desired. The guidelines in addition worked as the great way to understand that someone else have a similar eagerness similar to my personal own to understand a great deal more on the subject of this matter. I believe there are a lot more pleasurable moments in the future for people who go through your website.
you may have an excellent blog here! would you prefer to make some invite posts on my blog?
Oh my goodness! an incredible article dude. Thanks Nevertheless I am experiencing concern with ur rss . Don抰 know why Unable to subscribe to it. Is there anybody getting equivalent rss drawback? Anybody who knows kindly respond. Thnkx
After study a couple of of the blog posts on your website now, and I actually like your means of blogging. I bookmarked it to my bookmark website checklist and shall be checking again soon. Pls try my site as effectively and let me know what you think.
I抎 should check with you here. Which is not one thing I normally do! I take pleasure in studying a post that will make individuals think. Additionally, thanks for permitting me to remark!
My spouse and i ended up being absolutely fulfilled Chris could finish off his researching out of the ideas he grabbed using your site. It is now and again perplexing to just find yourself giving away guidelines which the others may have been trying to sell. And we also figure out we’ve got the blog owner to appreciate because of that. The main explanations you’ve made, the simple web site navigation, the relationships you can give support to foster – it is all spectacular, and it’s really assisting our son and us feel that the subject is exciting, and that’s unbelievably mandatory. Many thanks for the whole thing!
When I initially commented I clicked the -Notify me when new comments are added- checkbox and now each time a comment is added I get 4 emails with the same comment. Is there any way you possibly can take away me from that service? Thanks!
Spot on with this write-up, I actually suppose this web site wants way more consideration. I抣l most likely be again to read far more, thanks for that info.
I must show appreciation to the writer just for rescuing me from such a scenario. Right after exploring through the world-wide-web and seeing views which are not pleasant, I believed my entire life was well over. Living without the strategies to the difficulties you’ve resolved through your main short post is a crucial case, as well as those that might have in a negative way damaged my entire career if I had not encountered your web blog. Your primary competence and kindness in maneuvering a lot of stuff was important. I’m not sure what I would have done if I had not encountered such a stuff like this. I am able to at this moment relish my future. Thanks very much for this professional and sensible help. I won’t be reluctant to refer your blog to anyone who desires direction on this topic.
An interesting dialogue is worth comment. I believe that it is best to write extra on this matter, it might not be a taboo subject however generally individuals are not sufficient to talk on such topics. To the next. Cheers
You made some first rate points there. I regarded on the web for the problem and found most people will go together with along with your website.
WONDERFUL Post.thanks for share..extra wait .. ?
Can I simply say what a relief to search out somebody who actually knows what theyre talking about on the internet. You definitely know methods to bring a difficulty to gentle and make it important. Extra folks must learn this and understand this side of the story. I cant believe youre no more in style because you undoubtedly have the gift.
Aw, this was a very nice post. In thought I would like to put in writing like this moreover ?taking time and precise effort to make a very good article?however what can I say?I procrastinate alot and not at all seem to get something done.
My husband and i got cheerful Chris managed to deal with his studies via the precious recommendations he received out of the web pages. It is now and again perplexing just to choose to be releasing information which other people could have been selling. And we also remember we now have you to thank because of that. The type of explanations you have made, the straightforward website menu, the friendships your site aid to promote – it is many sensational, and it’s really assisting our son and us believe that the issue is amusing, and that is tremendously serious. Thank you for all!
you’ve got an amazing weblog right here! would you prefer to make some invite posts on my weblog?
An attention-grabbing dialogue is worth comment. I think that it’s best to write more on this topic, it might not be a taboo subject however generally persons are not sufficient to talk on such topics. To the next. Cheers
That is the best weblog for anybody who desires to find out about this topic. You understand so much its virtually laborious to argue with you (not that I really would want匟aHa). You definitely put a brand new spin on a topic thats been written about for years. Nice stuff, simply great!
There may be noticeably a bundle to find out about this. I assume you made sure good points in features also.
I really wanted to compose a word so as to say thanks to you for all of the fabulous pointers you are sharing here. My rather long internet investigation has now been compensated with reliable insight to go over with my family members. I would mention that most of us readers actually are unquestionably endowed to exist in a fabulous community with so many brilliant people with very beneficial principles. I feel truly grateful to have encountered your entire webpages and look forward to tons of more entertaining moments reading here. Thank you once again for a lot of things.
I’m typically to running a blog and i actually appreciate your content. The article has actually peaks my interest. I’m going to bookmark your web site and preserve checking for brand new information.
After examine a number of of the weblog posts on your website now, and I really like your means of blogging. I bookmarked it to my bookmark website listing and will probably be checking again soon. Pls try my web page as well and let me know what you think.
very good publish, i actually love this website, keep on it
This is the correct blog for anybody who desires to find out about this topic. You notice so much its virtually laborious to argue with you (not that I really would want匟aHa). You undoubtedly put a brand new spin on a subject thats been written about for years. Nice stuff, simply great!
I must express my appreciation to this writer just for rescuing me from such a problem. Right after surfing through the world-wide-web and coming across suggestions which are not powerful, I assumed my life was gone. Living minus the strategies to the issues you have sorted out through your entire guideline is a serious case, and those which could have badly affected my career if I had not encountered your website. Your knowledge and kindness in handling the whole thing was tremendous. I’m not sure what I would’ve done if I hadn’t discovered such a step like this. I am able to now relish my future. Thank you so much for the skilled and sensible guide. I will not hesitate to endorse the sites to anybody who ought to have support about this subject matter.
I as well as my pals ended up looking at the nice strategies found on your web page and all of the sudden got a horrible feeling I had not expressed respect to the website owner for those techniques. Most of the guys appeared to be absolutely thrilled to learn them and have now very much been making the most of those things. Appreciate your truly being quite thoughtful and for making a choice on this form of perfect useful guides most people are really wanting to understand about. Our sincere apologies for not saying thanks to you sooner.
I happen to be commenting to make you be aware of of the really good discovery my princess found reading through your web page. She realized a wide variety of issues, not to mention what it is like to possess a marvelous teaching mindset to let many others without problems know just exactly chosen hard to do subject matter. You actually did more than her desires. Thanks for providing such practical, healthy, informative as well as fun tips about the topic to Emily.
Thanks so much for giving everyone a very pleasant possiblity to discover important secrets from here. It is usually very fantastic and as well , packed with fun for me and my office friends to visit your website a minimum of 3 times per week to study the latest secrets you have. And of course, I am just at all times happy with the breathtaking solutions served by you. Selected 4 facts in this post are basically the most beneficial we have all ever had.
I and also my pals were studying the excellent tactics located on the blog while immediately I got an awful suspicion I never expressed respect to the site owner for those secrets. My people are already certainly glad to read all of them and already have pretty much been having fun with these things. Thanks for actually being indeed kind as well as for having these kinds of superior tips most people are really eager to understand about. Our honest regret for not expressing gratitude to earlier.
I have to show some appreciation to this writer for rescuing me from this particular setting. Because of exploring through the internet and finding strategies which were not beneficial, I thought my entire life was gone. Existing without the solutions to the problems you’ve sorted out all through your good report is a serious case, as well as those that could have badly damaged my career if I had not noticed your site. Your talents and kindness in playing with every aspect was precious. I’m not sure what I would’ve done if I had not come across such a step like this. I’m able to at this point look forward to my future. Thank you very much for the impressive and sensible guide. I won’t be reluctant to suggest the blog to any individual who ought to have guidance about this issue.
My wife and i were very joyous that Albert could carry out his inquiry while using the ideas he got from your very own web site. It’s not at all simplistic to simply be making a gift of techniques many people might have been selling. And we also grasp we now have you to appreciate for this. The type of explanations you’ve made, the simple website navigation, the relationships your site aid to instill – it’s many extraordinary, and it’s aiding our son and our family feel that this issue is awesome, which is wonderfully pressing. Thank you for all!
My spouse and i got quite lucky when Peter managed to do his reports using the ideas he received through your web site. It is now and again perplexing to just choose to be making a gift of tips and tricks other people could have been selling. So we consider we’ve got the blog owner to thank because of that. Most of the illustrations you made, the easy website menu, the friendships you will make it easier to instill – it is most fabulous, and it is aiding our son in addition to the family imagine that that subject matter is exciting, which is exceedingly mandatory. Thank you for all!
I’m just commenting to make you understand what a fabulous experience my friend’s daughter obtained reading through your web site. She came to understand too many pieces, which included how it is like to possess a great teaching style to make a number of people with ease completely grasp selected very confusing matters. You actually surpassed her expected results. Many thanks for rendering those effective, safe, informative not to mention cool tips on this topic to Emily.
Thanks for all your valuable effort on this site. My mom delights in managing investigation and it’s easy to see why. All of us know all concerning the dynamic mode you convey very important guidelines through the blog and therefore increase contribution from other ones on that point so my child is undoubtedly being taught a great deal. Enjoy the rest of the new year. You are always performing a wonderful job.
I must show thanks to the writer for rescuing me from this trouble. Just after searching throughout the world-wide-web and meeting tips which are not pleasant, I assumed my life was done. Existing devoid of the solutions to the difficulties you have fixed as a result of the review is a serious case, as well as the ones which may have negatively damaged my entire career if I hadn’t discovered the blog. Your actual talents and kindness in handling every part was priceless. I don’t know what I would’ve done if I hadn’t encountered such a step like this. I’m able to at this moment look ahead to my future. Thanks a lot so much for the reliable and effective help. I will not think twice to recommend your site to anyone who needs and wants counselling on this matter.
A lot of thanks for your entire effort on this blog. My niece delights in working on internet research and it’s really easy to see why. My partner and i know all relating to the lively means you make practical strategies on your website and as well as encourage participation from other ones on the article plus our favorite girl is being taught so much. Take pleasure in the remaining portion of the new year. You are always performing a first class job.
I would like to point out my love for your kind-heartedness for men who actually need help on in this concept. Your personal commitment to passing the solution along was exceedingly invaluable and have in every case enabled most people just like me to get to their dreams. Your new informative facts can mean a whole lot to me and especially to my colleagues. With thanks; from all of us.
Thanks a lot for giving everyone an extraordinarily memorable chance to check tips from this website. It is usually very brilliant plus jam-packed with a good time for me and my office co-workers to search the blog at least thrice per week to learn the newest guidance you have. And of course, I am also always pleased concerning the remarkable ideas served by you. Certain 1 points in this posting are ultimately the most suitable we’ve had.
I’m also commenting to make you understand what a outstanding encounter my friend’s girl gained using your webblog. She learned numerous things, including what it is like to possess an excellent teaching spirit to get many more with no trouble fully grasp some tortuous subject matter. You actually exceeded my expected results. Thank you for offering these informative, dependable, revealing and also cool thoughts on your topic to Evelyn.
Thank you a lot for giving everyone an extraordinarily pleasant opportunity to read articles and blog posts from this blog. It is often so cool and jam-packed with a good time for me personally and my office friends to search your blog particularly three times in one week to study the latest tips you will have. Of course, I’m also at all times astounded concerning the good principles you serve. Certain 1 facts in this article are completely the simplest we have had.
I must express thanks to the writer for rescuing me from this situation. After scouting through the world wide web and seeing recommendations which were not beneficial, I thought my entire life was over. Living without the solutions to the difficulties you have resolved by way of your good blog post is a crucial case, as well as the ones which may have adversely damaged my career if I hadn’t noticed your web page. The understanding and kindness in taking care of all the things was helpful. I’m not sure what I would’ve done if I had not encountered such a point like this. I can at this moment look forward to my future. Thank you so much for the professional and effective guide. I will not be reluctant to endorse your web sites to any individual who would need guidance on this matter.
I’m just commenting to let you understand what a beneficial experience my wife’s child undergone going through your web site. She figured out such a lot of things, not to mention how it is like to have a marvelous giving character to let the rest completely master specific grueling topics. You truly exceeded our own expected results. Thanks for offering such insightful, dependable, edifying and easy tips on the topic to Tanya.
I as well as my guys appeared to be reading through the great helpful hints from the website then instantly developed a terrible feeling I had not expressed respect to you for those secrets. Most of the women became consequently stimulated to read them and already have without a doubt been taking advantage of these things. Thank you for actually being simply accommodating and also for utilizing these kinds of impressive useful guides millions of individuals are really eager to learn about. My personal honest apologies for not expressing appreciation to sooner.
I needed to send you this little bit of remark to be able to give many thanks over again over the spectacular tactics you have shared on this page. It’s so extremely generous with you to give easily all that a lot of folks might have supplied as an electronic book to get some cash for their own end, primarily since you might have tried it in the event you decided. The points also served to be a fantastic way to recognize that some people have a similar zeal much like my own to understand very much more with reference to this issue. I am certain there are some more fun moments in the future for folks who read your blog post.
I would like to convey my appreciation for your kind-heartedness for folks who need help on this one area of interest. Your personal dedication to passing the message across has been extraordinarily invaluable and have truly helped guys just like me to reach their aims. Your new important publication means a whole lot a person like me and further more to my office colleagues. Thanks a lot; from each one of us.
Thanks for your whole efforts on this site. Gloria enjoys conducting research and it is easy to see why. A lot of people learn all of the lively method you render vital thoughts on this web site and even increase contribution from some other people on this concept while our favorite princess is without a doubt becoming educated a whole lot. Take pleasure in the remaining portion of the year. You have been conducting a first class job.
Thank you so much for providing individuals with a very spectacular chance to read in detail from this site. It really is so superb plus stuffed with amusement for me and my office fellow workers to visit your blog no less than thrice in 7 days to find out the fresh guidance you have. Of course, I’m always impressed for the gorgeous pointers served by you. Some 2 tips on this page are unquestionably the most suitable we have had.
I’m also commenting to let you understand what a fabulous discovery my wife’s girl enjoyed studying your web page. She came to understand so many pieces, with the inclusion of what it’s like to have an ideal giving mindset to have the others just comprehend several advanced subject matter. You undoubtedly did more than our expectations. I appreciate you for distributing the good, trustworthy, informative and easy tips on your topic to Evelyn.
Needed to send you this very small note to help say thank you over again considering the pretty guidelines you’ve shown in this article. It was so pretty generous with you to offer easily what a lot of folks could have supplied for an ebook to help make some cash for their own end, and in particular now that you could have done it if you wanted. These advice additionally worked as a fantastic way to realize that other individuals have similar interest just as my very own to understand good deal more on the topic of this issue. I think there are some more pleasurable sessions ahead for people who check out your site.
I am just writing to make you know of the outstanding encounter my princess had viewing your web site. She came to understand plenty of issues, including what it is like to have an amazing coaching spirit to have most people easily learn several complicated things. You really exceeded my expectations. I appreciate you for providing these good, healthy, informative and in addition easy thoughts on the topic to Jane.
My spouse and i got quite peaceful that Jordan managed to complete his investigations through the entire ideas he was given in your weblog. It is now and again perplexing just to happen to be releasing techniques which usually many others could have been making money from. And we grasp we have you to appreciate because of that. The main illustrations you made, the straightforward website navigation, the friendships you aid to instill – it’s many excellent, and it is making our son and us know that that topic is interesting, which is certainly extraordinarily pressing. Thanks for the whole thing!
Experts say the ATP punishment too light 3 weeks cannot solve, gaussian psychological problems
I definitely wanted to compose a simple message to be able to express gratitude to you for the pleasant tricks you are posting at this website. My incredibly long internet lookup has at the end of the day been honored with good facts and strategies to share with my family members. I would say that many of us visitors are very endowed to live in a fantastic site with very many lovely people with very helpful opinions. I feel very much happy to have seen the website page and look forward to so many more excellent moments reading here. Thanks a lot once more for everything.
I together with my friends appeared to be digesting the excellent thoughts on your web site and suddenly developed a terrible feeling I had not expressed respect to the site owner for those tips. Those ladies were definitely absolutely joyful to read all of them and now have surely been taking advantage of those things. Appreciation for getting well accommodating and for obtaining this sort of nice tips millions of individuals are really needing to discover. Our own sincere regret for not expressing gratitude to you earlier.
I precisely needed to appreciate you once again. I’m not certain what I would have used without the entire aspects provided by you over this concern. It had been the scary scenario in my circumstances, nevertheless considering your expert avenue you resolved the issue made me to weep for delight. Extremely thankful for the service and thus have high hopes you are aware of a great job your are undertaking educating some other people thru your web blog. I’m certain you have never got to know all of us.
Thank you so much for giving everyone an extraordinarily memorable possiblity to read from this website. It is always so good plus full of fun for me and my office fellow workers to visit the blog at the very least 3 times per week to learn the new tips you have. And lastly, we’re certainly fulfilled concerning the dazzling solutions you serve. Selected 3 areas on this page are definitely the very best I have ever had.
I would like to get across my gratitude for your kindness supporting men and women who really need assistance with the study. Your special commitment to getting the solution all over has been exceptionally important and have continuously made guys like me to attain their goals. The important report entails much to me and substantially more to my office colleagues. Thank you; from everyone of us.
Thank you so much for giving everyone remarkably pleasant opportunity to read from this blog. It’s usually very nice plus packed with a great time for me personally and my office friends to visit your blog at the very least three times a week to find out the latest guides you will have. And of course, I am at all times motivated concerning the spectacular creative concepts you serve. Some two tips in this posting are rather the most beneficial we have ever had.
Thanks for each of your hard work on this web page. Debby delights in doing investigations and it is easy to see why. All of us notice all concerning the powerful manner you make effective items on this web blog and as well as strongly encourage participation from people on this matter plus my simple princess is truly becoming educated a lot. Have fun with the remaining portion of the new year. Your performing a fantastic job.
I’m also writing to let you know what a excellent discovery my friend’s princess enjoyed reading through your site. She learned such a lot of things, which include what it’s like to possess a marvelous coaching spirit to get the others with no trouble fully understand a number of tricky issues. You actually surpassed my expectations. Thank you for distributing such helpful, dependable, revealing and also unique tips on this topic to Jane.
I have to express thanks to you just for rescuing me from this incident. As a result of researching throughout the world-wide-web and coming across things that were not pleasant, I believed my life was gone. Existing without the presence of approaches to the issues you have resolved by means of your good site is a serious case, and the ones that would have in a wrong way affected my entire career if I had not noticed your web site. Your main competence and kindness in dealing with all areas was valuable. I don’t know what I would have done if I hadn’t discovered such a step like this. It’s possible to at this moment look forward to my future. Thanks so much for this high quality and result oriented help. I will not be reluctant to refer your web sites to anybody who ought to have care on this issue.
I simply wanted to send a brief comment so as to say thanks to you for those superb facts you are writing at this site. My long internet lookup has at the end of the day been recognized with beneficial knowledge to write about with my classmates and friends. I would tell you that many of us website visitors are extremely lucky to be in a fantastic community with so many awesome people with insightful advice. I feel rather happy to have discovered your entire web pages and look forward to tons of more fun minutes reading here. Thank you again for everything.
I would like to show my passion for your kind-heartedness supporting persons who have the need for help with this concept. Your real commitment to getting the message all over appeared to be quite important and have continuously empowered most people like me to achieve their endeavors. Your own invaluable instruction entails much a person like me and even further to my office workers. Many thanks; from all of us.
I am only writing to make you understand of the cool experience my wife’s child developed using your blog. She mastered so many issues, most notably how it is like to possess a marvelous helping mindset to have a number of people very easily thoroughly grasp a number of tortuous subject areas. You truly surpassed her expected results. I appreciate you for displaying the insightful, healthy, educational and unique tips about this topic to Emily.
There are definitely a variety of particulars like that to take into consideration. That is a nice level to carry up. I offer the ideas above as normal inspiration but clearly there are questions like the one you deliver up the place a very powerful thing might be working in sincere good faith. I don?t know if greatest practices have emerged around issues like that, however I am positive that your job is clearly recognized as a good game. Both girls and boys really feel the impact of only a moment抯 pleasure, for the remainder of their lives.
I must get across my affection for your generosity giving support to people that really want help with this important area. Your real commitment to passing the solution throughout turned out to be really helpful and has continuously empowered guys just like me to achieve their pursuits. Your new invaluable facts implies this much to me and even further to my office colleagues. With thanks; from everyone of us.
I just wanted to write a small note to appreciate you for those awesome ways you are posting here. My long internet investigation has now been compensated with beneficial know-how to exchange with my best friends. I ‘d state that that most of us readers actually are quite blessed to live in a decent community with many awesome professionals with insightful methods. I feel quite grateful to have used the website and look forward to plenty of more enjoyable moments reading here. Thank you once again for everything.
WONDERFUL Post.thanks for share..extra wait .. ?
I wanted to send you the bit of observation in order to say thank you as before with the incredible basics you have discussed in this case. It’s so unbelievably generous with you to supply openly all many people would’ve offered for sale for an e-book to make some dough on their own, most notably considering the fact that you might well have tried it in the event you considered necessary. The solutions likewise worked to provide a easy way to comprehend other individuals have the identical desire like mine to figure out more and more with regards to this issue. I know there are a lot more fun opportunities in the future for individuals who browse through your site.
Thanks a lot for giving everyone a very marvellous opportunity to discover important secrets from this website. It is always very cool and as well , stuffed with a lot of fun for me and my office peers to visit your website the equivalent of 3 times weekly to find out the new guides you have got. And indeed, we’re usually pleased concerning the great opinions served by you. Certain 3 facts in this posting are in fact the best I have had.
I wish to show some appreciation to this writer for bailing me out of this particular condition. Because of surfing throughout the online world and seeing ways which are not pleasant, I assumed my entire life was well over. Living devoid of the solutions to the issues you have resolved by means of the review is a crucial case, as well as the ones that might have negatively damaged my entire career if I hadn’t noticed your blog post. Your primary know-how and kindness in dealing with all things was tremendous. I don’t know what I would have done if I had not come across such a step like this. It’s possible to now look forward to my future. Thanks so much for your specialized and amazing help. I won’t be reluctant to recommend your blog to anybody who needs to have tips on this subject matter.
Aw, this was a very nice post. In thought I wish to put in writing like this additionally ?taking time and precise effort to make an excellent article?however what can I say?I procrastinate alot and in no way seem to get something done.
Thanks so much for giving everyone a very terrific possiblity to check tips from here. It is often very useful and as well , stuffed with a lot of fun for me and my office mates to visit your site more than thrice in one week to see the latest stuff you have got. Of course, I’m also certainly impressed with your gorgeous pointers served by you. Some 3 points in this posting are surely the very best we have had.
I definitely wanted to send a quick message so as to express gratitude to you for some of the precious advice you are placing here. My incredibly long internet investigation has now been rewarded with reasonable know-how to share with my two friends. I ‘d suppose that most of us site visitors are quite lucky to be in a notable network with so many lovely people with great principles. I feel somewhat blessed to have used your website page and look forward to so many more awesome minutes reading here. Thanks a lot again for a lot of things.
I really wanted to construct a note to appreciate you for these wonderful instructions you are showing here. My time intensive internet look up has at the end of the day been honored with reasonable facts and techniques to go over with my family and friends. I would say that most of us site visitors are extremely endowed to live in a fabulous community with many awesome individuals with good hints. I feel quite fortunate to have used your entire weblog and look forward to really more fabulous times reading here. Thanks a lot again for everything.
I just wanted to make a quick comment to thank you for all the pleasant ways you are writing at this site. My long internet investigation has at the end been honored with beneficial strategies to go over with my great friends. I ‘d tell you that most of us visitors actually are very endowed to live in a decent website with so many outstanding individuals with very beneficial tips and hints. I feel somewhat grateful to have come across your entire webpages and look forward to so many more pleasurable moments reading here. Thanks a lot once again for everything.
I really wanted to write down a quick note to appreciate you for those lovely tips you are giving at this website. My time consuming internet look up has finally been honored with professional details to talk about with my good friends. I would admit that we site visitors actually are quite fortunate to exist in a fantastic network with many awesome professionals with very beneficial hints. I feel very much lucky to have discovered your entire site and look forward to tons of more amazing times reading here. Thanks once again for all the details.
here we go!
Very interesting information!Perfect just what I was searching for! “I have great faith in fools — self confidence my friends call it.” by Edgar Allan Poe.
I just want to tell you that I am just new to blogs and truly enjoyed this website. Probably I’m planning to bookmark your website . You absolutely come with really good articles and reviews. Thanks a bunch for sharing your blog.
hi!,I like your writing very much! percentage we communicate more about your article on AOL? I require a specialist on this area to unravel my problem. May be that is you! Taking a look forward to peer you.
Pretty nice post. I just stumbled upon your weblog and wanted to say that I’ve really enjoyed browsing your blog posts. In any case I’ll be subscribing to your feed and I hope you write again soon!
Attractive section of content. I just stumbled upon your web site and in accession capital to assert that I acquire actually enjoyed account your blog posts. Any way I will be subscribing to your feeds and even I achievement you access consistently fast.
Good day very nice website!! Guy .. Excellent .. Superb .. I will bookmark your site and take the feeds additionally¡KI’m happy to find so many helpful info here within the post, we want work out more strategies in this regard, thank you for sharing. . . . . .
I just could not leave your site before suggesting that I extremely loved the usual info an individual provide to your visitors? Is going to be again often in order to check out new posts
wonderful issues altogether, you just gained a logo new reader. What may you suggest in regards to your submit that you simply made a few days ago? Any certain?
I am really impressed with your writing skills and also with the layout on your weblog. Is this a paid theme or did you modify it yourself? Anyway keep up the nice quality writing, it is rare to see a nice blog like this one these days..
I have been examinating out many of your stories and i can claim pretty good stuff. I will surely bookmark your blog.
Good blog! I truly love how it is easy on my eyes and the data are well written. I’m wondering how I might be notified whenever a new post has been made. I have subscribed to your feed which must do the trick! Have a great day!
Attractive section of content. I just stumbled upon your site and in accession capital to assert that I get in fact enjoyed account your blog posts. Anyway I’ll be subscribing to your feeds and even I achievement you access consistently quickly.
Good website! I really love how it is simple on my eyes and the data are well written. I am wondering how I could be notified whenever a new post has been made. I’ve subscribed to your RSS feed which must do the trick! Have a great day!
Thanks for sharing superb informations. Your website is very cool. I am impressed by the details that you¡¦ve on this website. It reveals how nicely you understand this subject. Bookmarked this web page, will come back for extra articles. You, my pal, ROCK! I found simply the info I already searched everywhere and just couldn’t come across. What a perfect web site.
Thank you, I’ve just been looking for information approximately this topic for a long time and yours is the greatest I’ve discovered so far. But, what concerning the bottom line? Are you certain about the supply?
Wow! This can be one particular of the most beneficial blogs We have ever arrive across on this subject. Basically Wonderful. I’m also a specialist in this topic so I can understand your hard work.
I do consider all of the ideas you have presented to your post. They’re really convincing and will definitely work. Nonetheless, the posts are very quick for novices. May you please extend them a bit from subsequent time? Thank you for the post.
I don’t even know how I ended up here, but I thought this post was great. I don’t know who you are but certainly you are going to a famous blogger if you aren’t already 😉 Cheers!
Great write-up, I am normal visitor of one¡¦s web site, maintain up the nice operate, and It’s going to be a regular visitor for a lengthy time.
It¡¦s really a great and useful piece of info. I am happy that you just shared this useful info with us. Please keep us up to date like this. Thanks for sharing.
Well I truly enjoyed reading it. This article provided by you is very useful for proper planning.
fantastic post, very informative. I wonder why the other experts of this sector don’t understand this. You should continue your writing. I’m confident, you’ve a great readers’ base already!
I simply could not depart your site prior to suggesting that I really loved the standard information an individual provide for your visitors? Is going to be back ceaselessly in order to investigate cross-check new posts
Helpful information. Lucky me I discovered your web site accidentally, and I am stunned why this coincidence did not took place earlier! I bookmarked it.
What i don’t realize is in fact how you’re now not really much more smartly-appreciated than you might be now. You are very intelligent. You recognize therefore significantly with regards to this matter, produced me individually imagine it from so many varied angles. Its like men and women don’t seem to be fascinated except it¡¦s something to accomplish with Woman gaga! Your individual stuffs great. Always handle it up!
Normally I do not learn post on blogs, but I wish to say that this write-up very pressured me to check out and do it! Your writing style has been amazed me. Thank you, quite nice article.
You are a very intelligent person!
Its like you read my mind! You seem to know a lot about this, like you wrote the book in it or something. I think that you could do with some pics to drive the message home a little bit, but other than that, this is great blog. An excellent read. I will certainly be back.
Good ¡V I should certainly pronounce, impressed with your web site. I had no trouble navigating through all tabs as well as related info ended up being truly easy to do to access. I recently found what I hoped for before you know it at all. Quite unusual. Is likely to appreciate it for those who add forums or anything, web site theme . a tones way for your client to communicate. Nice task..
I am really impressed with your writing skills as well as with the layout on your weblog. Is this a paid theme or did you customize it yourself? Anyway keep up the excellent quality writing, it is rare to see a nice blog like this one these days..
You could definitely see your expertise in the paintings you write. The sector hopes for more passionate writers like you who are not afraid to say how they believe. All the time follow your heart.
Its like you read my mind! You appear to know so much about this, like you wrote the book in it or something. I think that you could do with some pics to drive the message home a bit, but other than that, this is fantastic blog. A great read. I will definitely be back.
certainly like your website but you have to test the spelling on quite a few of your posts. A number of them are rife with spelling issues and I in finding it very bothersome to tell the reality however I¡¦ll certainly come back again.
You made a few good points there. I did a search on the issue and found a good number of persons will have the same opinion with your blog.
Thank you a lot for giving everyone an extremely terrific possiblity to read critical reviews from this web site. It really is so pleasurable and also jam-packed with a great time for me and my office co-workers to search the blog at the least 3 times per week to find out the newest things you will have. Of course, I’m actually fulfilled considering the gorgeous secrets you serve. Selected two points in this article are completely the most beneficial I’ve had.
I have been exploring for a little for any high-quality articles or blog posts on this kind of space . Exploring in Yahoo I at last stumbled upon this site. Reading this information So i¡¦m happy to convey that I have a very excellent uncanny feeling I discovered just what I needed. I so much indubitably will make sure to don¡¦t disregard this site and provides it a look on a continuing basis.
Excellent post. I was checking constantly this blog and I am impressed! Very useful info specifically the last part 🙂 I care for such information much. I was looking for this particular information for a very long time. Thank you and good luck.
I’m very happy to read this. This is the type of manual that needs to be given and not the accidental misinformation that’s at the other blogs. Appreciate your sharing this greatest doc.
Very nice article and right to the point. I don’t know if this is actually the best place to ask but do you folks have any thoughts on where to employ some professional writers? Thanks in advance 🙂
I was recommended this web site by my cousin. I am not sure whether this post is written by him as nobody else know such detailed about my trouble. You are wonderful! Thanks!
Excellent website. A lot of helpful info here. I¡¦m sending it to a few pals ans also sharing in delicious. And naturally, thank you on your effort!
This is really interesting, You are a very skilled blogger. I’ve joined your feed and look forward to seeking more of your fantastic post. Also, I have shared your site in my social networks!
Good site! I really love how it is easy on my eyes and the data are well written. I am wondering how I might be notified whenever a new post has been made. I have subscribed to your feed which must do the trick! Have a nice day!
Generally I do not learn post on blogs, however I wish to say that this write-up very pressured me to take a look at and do it! Your writing style has been surprised me. Thank you, quite great post.
Wow! Thank you! I continually wanted to write on my site something like that. Can I implement a portion of your post to my blog?
Wonderful website. A lot of helpful information here. I am sending it to a few pals ans additionally sharing in delicious. And of course, thank you on your sweat!
Useful information. Fortunate me I found your site by accident, and I am surprised why this accident did not took place in advance! I bookmarked it.
Hello. remarkable job. I did not anticipate this. This is a fantastic story. Thanks!
Thanks for the sensible critique. Me and my neighbor were just preparing to do a little research on this. We got a grab a book from our area library but I think I learned more clear from this post. I am very glad to see such wonderful information being shared freely out there.
I have been checking out many of your stories and it’s pretty nice stuff. I will make sure to bookmark your site.
I was just searching for this info for some time. After 6 hours of continuous Googleing, at last I got it in your website. I wonder what is the lack of Google strategy that don’t rank this type of informative websites in top of the list. Generally the top websites are full of garbage.
Awsome article and straight to the point. I don’t know if this is truly the best place to ask but do you people have any ideea where to employ some professional writers? Thank you 🙂
Wow! This can be one particular of the most beneficial blogs We’ve ever arrive across on this subject. Actually Magnificent. I am also an expert in this topic so I can understand your hard work.
I cling on to listening to the reports lecture about getting free online grant applications so I have been looking around for the most excellent site to get one. Could you tell me please, where could i find some?
It¡¦s really a nice and useful piece of info. I am happy that you simply shared this useful information with us. Please stay us up to date like this. Thank you for sharing.
Hello my loved one! I wish to say that this article is amazing, nice written and come with approximately all vital infos. I would like to peer extra posts like this .
Heya i am for the first time here. I found this board and I find It really useful & it helped me out much. I hope to give something back and aid others like you aided me.
Hey There. I found your blog using msn. This is an extremely well written article. I’ll make sure to bookmark it and return to read more of your useful info. Thanks for the post. I will definitely return.
certainly like your web site however you need to check the spelling on several of your posts. A number of them are rife with spelling issues and I in finding it very troublesome to tell the truth then again I¡¦ll definitely come back again.
Great website! I am loving it!! Will be back later to read some more. I am taking your feeds also
Hi, i think that i saw you visited my website thus i came to “return the favor”.I am trying to find things to improve my web site!I suppose its ok to use some of your ideas!!
you’re in reality a excellent webmaster. The website loading velocity is amazing. It seems that you’re doing any unique trick. Furthermore, The contents are masterwork. you have done a excellent process in this matter!
I have been browsing online more than 3 hours as of late, yet I never discovered any attention-grabbing article like yours. It is lovely worth sufficient for me. In my view, if all website owners and bloggers made excellent content material as you probably did, the internet might be a lot more helpful than ever before.
Wow! This can be one particular of the most helpful blogs We have ever arrive across on this subject. Actually Great. I’m also an expert in this topic so I can understand your effort.
you are in point of fact a good webmaster. The website loading pace is amazing. It sort of feels that you’re doing any distinctive trick. Moreover, The contents are masterpiece. you have done a wonderful activity on this matter!
Hello there, I found your site by the use of Google while searching for a similar subject, your website came up, it appears great. I’ve bookmarked it in my google bookmarks.
I delight in, result in I discovered exactly what I was taking a look for. You’ve ended my 4 day lengthy hunt! God Bless you man. Have a great day. Bye
It happens to be convenient opportunity to prepare some options for the extended term. I’ve go through this blog entry and if I may, I desire to recommend you very few helpful pointers.
Hi folks here, just started to be receptive to your post through Search engines like google, and realized that it is pretty helpful. I will be grateful should you decide retain this post.
Absolutely alluring resources that you have mentioned, thank you for posting.
I was pretty pleased to uncover this site. I need to to thank you for your time due to this fantastic read!! I definitely enjoyed every part of it and I have you saved to fav to see new information in your site.
I just desire to reveal to you that I am new to blogging and clearly adored your page. Very likely I am likely to store your blog post . You seriously have fabulous article materials. Like it for swapping with us all of your website post
I merely desire to inform you you that I am new to putting up a blog and extremely cherished your page. Very possible I am inclined to save your blog post . You indeed have memorable article blog posts. Love it for sharing with us your main website report
I loved as much as you will receive carried out right here. The sketch is attractive, your authored subject matter stylish. nonetheless, you command get got an nervousness over that you wish be delivering the following. unwell unquestionably come more formerly again since exactly the same nearly very often inside case you shield this hike.
Hi, i think that i saw you visited my site so i came to “return the favor”.I’m trying to find things to improve my web site!I suppose its ok to use a few of your ideas!!
It is in point of fact a nice and helpful piece of information. I¡¦m happy that you shared this helpful information with us. Please stay us up to date like this. Thanks for sharing.
Hello my family member! I want to say that this post is amazing, great written and come with almost all important infos. I¡¦d like to look more posts like this .
Thank you for the auspicious writeup. It in fact was a amusement account it. Look advanced to far added agreeable from you! However, how could we communicate?
Wow, amazing weblog format! How lengthy have you been running a blog for? you make running a blog look easy. The overall glance of your site is fantastic, as neatly as the content!
I have been browsing online more than three hours these days, but I by no means discovered any interesting article like yours. It is pretty price enough for me. Personally, if all website owners and bloggers made good content as you did, the net will probably be much more helpful than ever before.
I’m not sure where you are getting your information, but good topic. I needs to spend some time learning more or understanding more. Thanks for fantastic information I was looking for this information for my mission.
After I originally commented I appear to have clicked on the -Notify me when new comments are added- checkbox and from now on each time a comment is added I recieve 4 emails with the same comment. Is there a means you can remove me from that service? Kudos!|
Fantastic goods from you, man. I have understand your stuff previous to and you’re just too fantastic. I actually like what you’ve acquired here, really like what you’re stating and the way in which you say it. You make it entertaining and you still care for to keep it sensible. I can’t wait to read much more from you. This is actually a great website.
Thanks so much for giving everyone an extraordinarily spectacular chance to discover important secrets from this website. It is always very beneficial plus stuffed with amusement for me personally and my office colleagues to visit your site on the least thrice every week to see the new issues you have got. And of course, we’re certainly impressed considering the very good points you give. Certain 2 points in this posting are certainly the finest we’ve had.
Awsome info and right to the point. I don’t know if this is in fact the best place to ask but do you folks have any ideea where to get some professional writers? Thanks 🙂
I’m not sure where you are getting your information, but good topic. I needs to spend some time learning more or understanding more. Thanks for excellent info I was looking for this information for my mission.
I loved as much as you’ll receive carried out right here. The sketch is tasteful, your authored material stylish. nonetheless, you command get got an edginess over that you wish be delivering the following. unwell unquestionably come more formerly again since exactly the same nearly very often inside case you shield this increase.
hi!,I love your writing so so much! percentage we communicate more approximately your article on AOL? I need an expert on this space to unravel my problem. Maybe that’s you! Having a look ahead to see you.
I will right away grab your rss feed as I can not to find your e-mail subscription hyperlink or newsletter service. Do you’ve any? Please permit me recognise in order that I could subscribe. Thanks.
Keep up the excellent work , I read few articles on this site and I believe that your web site is really interesting and holds bands of superb info .
I really appreciate this post. I’ve been looking all over for this! Thank goodness I found it on Bing. You have made my day! Thx again!
Wow! This could be one particular of the most beneficial blogs We have ever arrive across on this subject. Actually Fantastic. I am also a specialist in this topic so I can understand your hard work.
I was suggested this blog by my cousin. I am not sure whether this post is written by him as nobody else know such detailed about my trouble. You are incredible! Thanks!
Hello, you used to write fantastic, but the last few posts have been kinda boring¡K I miss your tremendous writings. Past few posts are just a bit out of track! come on!
You really make it appear really easy with your presentation but I find this matter to be actually one thing which I feel I’d never understand. It sort of feels too complex and very vast for me. I am taking a look forward to your next submit, I will attempt to get the cling of it!
I¡¦ve read some just right stuff here. Certainly value bookmarking for revisiting. I wonder how a lot effort you put to create one of these great informative web site.
Well I definitely enjoyed reading it. This information provided by you is very effective for good planning.
Good article and straight to the point. I don’t know if this is really the best place to ask but do you folks have any ideea where to hire some professional writers? Thanks 🙂
Thanks for sharing excellent informations. Your web site is very cool. I am impressed by the details that you have on this site. It reveals how nicely you understand this subject. Bookmarked this website page, will come back for more articles. You, my friend, ROCK! I found simply the info I already searched all over the place and just could not come across. What a great website.
I am not sure where you are getting your info, but good topic. I needs to spend some time learning much more or understanding more. Thanks for excellent information I was looking for this information for my mission.
You have brought up a very good details , thanks for the post.
I must convey my gratitude for your kind-heartedness for folks who really want guidance on this particular concern. Your real commitment to getting the message up and down appears to be unbelievably practical and has continually allowed regular people just like me to realize their targets. This interesting facts implies a great deal a person like me and extremely more to my fellow workers. Regards; from each one of us.
Bonjour ! hum… D’accord sans être d’accord avec vous sur certains sujet dans votre site !
Bonjour ! Tiens ca me rappelle un truc ce site !
Thank you for the auspicious writeup. It in fact was a amusement account it. Look advanced to more added agreeable from you! By the way, how can we communicate?
It¡¦s really a cool and helpful piece of information. I¡¦m happy that you just shared this useful info with us. Please keep us up to date like this. Thanks for sharing.
I and also my guys were found to be taking note of the best helpful hints from your web blog and so suddenly I had an awful suspicion I had not expressed respect to the site owner for those techniques. All the young men were as a consequence thrilled to read through all of them and now have absolutely been taking advantage of those things. We appreciate you getting so kind and for utilizing varieties of helpful resources most people are really eager to learn about. Our own honest regret for not saying thanks to earlier.
Great write-up, I¡¦m normal visitor of one¡¦s blog, maintain up the nice operate, and It is going to be a regular visitor for a long time.
Great post. I was checking constantly this blog and I am impressed! Extremely useful info specifically the last part 🙂 I care for such info a lot. I was looking for this particular information for a very long time. Thank you and good luck.
You have brought up a very superb details , thankyou for the post.
Simply a smiling visitant here to share the love (:, btw outstanding style and design .
you’re really a good webmaster. The web site loading speed is incredible. It seems that you’re doing any unique trick. Also, The contents are masterwork. you have done a fantastic job on this topic!
Some truly wonderful information, Gladiolus I found this. “It’s amazing what ordinary people can do if they set out without preconceived notions.” by Charles Franklin Kettering.
It¡¦s really a cool and useful piece of information. I¡¦m happy that you simply shared this helpful info with us. Please keep us informed like this. Thanks for sharing.
Heya i am for the first time here. I came across this board and I find It really useful & it helped me out a lot. I hope to give something back and help others like you aided me.
I was very pleased to uncover this page. I need to to thank you for ones time for this wonderful read!! I definitely appreciated every little bit of it and i also have you book-marked to look at new things on your site.
You really make it seem so easy with your presentation but I find this matter to be actually something that I think I would never understand. It seems too complex and extremely broad for me. I am looking forward for your next post, I will try to get the hang of it!
I like the valuable info you provide in your articles. I’ll bookmark your blog and check again here frequently. I’m quite certain I will learn many new stuff right here! Best of luck for the next!
wonderful points altogether, you simply received a new reader. What could you recommend about your submit that you made a few days ago? Any certain?
I am really impressed with your writing skills as well as with the layout on your weblog. Is this a paid theme or did you customize it yourself? Anyway keep up the excellent quality writing, it is rare to see a great blog like this one today..
It’s perfect time to make some plans for the future and it is time to be happy. I’ve read this post and if I could I desire to suggest you few interesting things or suggestions. Maybe you can write next articles referring to this article. I wish to read even more things about it!
What i do not understood is if truth be told how you are not really much more well-liked than you may be right now. You’re so intelligent. You already know thus significantly with regards to this matter, produced me personally believe it from so many varied angles. Its like women and men are not fascinated until it¡¦s one thing to do with Girl gaga! Your personal stuffs excellent. At all times deal with it up!
I just wanted to construct a small comment so as to say thanks to you for those remarkable guides you are showing at this site. My long internet lookup has finally been paid with professional facts and strategies to talk about with my close friends. I would admit that we visitors actually are rather endowed to dwell in a fantastic website with many marvellous professionals with great tips. I feel quite fortunate to have come across your weblog and look forward to plenty of more entertaining moments reading here. Thank you once again for all the details.
of course like your web site however you need to test the spelling on several of your posts. Several of them are rife with spelling problems and I find it very troublesome to tell the reality however I’ll surely come back again.
This is very interesting, You’re a very skilled blogger. I have joined your feed and look forward to seeking more of your magnificent post. Also, I’ve shared your site in my social networks!
I regard something truly special in this web site.
Good write-up, I am normal visitor of one¡¦s website, maintain up the nice operate, and It is going to be a regular visitor for a long time.
I’m not sure where you are getting your information, but good topic. I needs to spend some time learning much more or understanding more. Thanks for wonderful info I was looking for this information for my mission.
Heya i am for the first time here. I found this board and I find It really useful & it helped me out much. I hope to give something back and aid others like you aided me.
I just wish to inform you you that I am new to writing and really admired your page. Likely I am most likely to bookmark your blog post . You definitely have lovely article information. Love it for telling with us the best web document
I was pretty pleased to uncover this great site. I want to to thank you for ones time for this particularly wonderful read!! I definitely enjoyed every bit of it and i also have you bookmarked to see new information on your blog.
Keep working ,great job!
This is appropriate time to have some preparations for the long run. I have scan this piece of writing and if I may possibly, I want to suggest you number of important suggestions.
Well I truly enjoyed studying it. This post offered by you is very practical for proper planning.
Might be practically not possible to encounter well-advised individuals on this niche, however, you appear like you fully understand those things you’re raving about! Cheers
Absolute helpful details you’ll have stated, say thanks a lot for putting up.
Thank you for any other informative site. Where else could I get that type of information written in such a perfect manner? I’ve a project that I am simply now running on, and I have been on the glance out for such info.
Hello.This article was extremely motivating, particularly because I was looking for thoughts on this matter last week.
I have to express some thanks to this writer for bailing me out of this particular matter. Just after researching throughout the world wide web and meeting notions which are not productive, I assumed my life was done. Being alive without the answers to the difficulties you’ve sorted out through your write-up is a serious case, and ones which may have badly damaged my entire career if I had not encountered your website. That know-how and kindness in dealing with the whole lot was valuable. I’m not sure what I would’ve done if I had not come across such a point like this. I can also at this moment look ahead to my future. Thanks a lot so much for your impressive and amazing help. I won’t hesitate to propose your site to any individual who should receive guidelines about this issue.
I will immediately grab your rss as I can not find your email subscription hyperlink or e-newsletter service. Do you have any? Please let me know in order that I could subscribe. Thanks.
I appreciate, cause I discovered exactly what I used to be having a look for. You have ended my four day long hunt! God Bless you man. Have a nice day. Bye
Hello, i think that i saw you visited my blog thus i came to “return the favor”.I am attempting to find things to enhance my web site!I suppose its ok to use some of your ideas!!
As a Newbie, I am constantly exploring online for articles that can help me. Thank you
This is really interesting, You are a very skilled blogger. I have joined your rss feed and look forward to seeking more of your wonderful post. Also, I’ve shared your website in my social networks!
Where can I find blogging websites that deal with legal issues?
Bonjour ! Merci pour cette agréable moment passé sur votre site
Major thankies for the blog article.Really looking forward to read more. Really Cool.
I have been absent for a while, but now I remember why I used to love this web site. Thank you, I¡¦ll try and check back more frequently. How frequently you update your website?
Hello there, just became aware of your blog through Google, and found that it’s truly informative.
I’m gonna watch out for brussels. I’ll be grateful if you continue
this in future. Many people will be benefited from your writing.
Cheers!
It’s ideal occasion to prepare some desires for the foreseeable future. I’ve scan this posting and if I should, I want to propose you handful of worthwhile suggestions.
I’m extremely pleased to find this site. I want to to thank you for ones time due to this fantastic read!! I definitely appreciated every part of it and i also have you saved as a favorite to check out new information on your web site.
I simply hope to inform you you that I am new to blogging and completely loved your review. Very possible I am going to bookmark your blog post . You simply have fantastic article information. Truly Appreciate it for telling with us the best site webpage
I simply want to show you that I am new to wordpress blogging and thoroughly loved your write-up. Probably I am likely to store your blog post . You truly have magnificent article materials. Acknowledge it for expressing with us your internet site report
It is actually nearly close to impossible to encounter well-aware readers on this subject, still, you come across as like you know the things that you’re writing about! Regards
Remarkably enlightening resources you’ll have said, a big heads up for setting up.
It’s ideal time to make some desires for the upcoming. I have browsed this post and if I can possibly, I wish to suggest you a few insightful recommendation.
I’m excited to find this site. I want to to thank you for your time just for this wonderful read!! I definitely savored every little bit of it and i also have you book marked to check out new stuff on your site.
Just want to say what a great blog you got here!I’ve been around for quite a lot of time, but finally decided to show my appreciation of your work!
I merely want to inform you that I am new to wordpress blogging and genuinely enjoyed your website. Very possible I am most likely to store your blog post . You undoubtedly have stunning article content. Be Thankful For it for share-out with us your main web information
It’s actually practically impossible to see well-educated visitors on this area, even though you seem like you know whatever you’re indicating! Bless You
I’m also commenting to let you know of the perfect experience my friend’s child gained studying your web page. She discovered so many issues, which include what it is like to have an incredible helping nature to let other people effortlessly completely grasp a variety of tortuous issues. You undoubtedly surpassed people’s expectations. Thanks for producing these informative, trusted, informative and easy tips on that topic to Janet.
I¡¦ll right away clutch your rss feed as I can not in finding your e-mail subscription hyperlink or e-newsletter service. Do you’ve any? Please permit me understand in order that I may just subscribe. Thanks.
I’m not sure where you’re getting your information, but great topic. I needs to spend some time learning more or understanding more. Thanks for great information I was looking for this information for my mission.
I wanted to compose you one bit of observation to help say thanks again considering the unique techniques you have featured in this article. It’s certainly pretty generous with you to grant easily just what most people might have sold as an electronic book to end up making some money for themselves, notably since you might have done it if you ever wanted. The guidelines as well acted like the easy way to know that other individuals have the same zeal similar to my very own to see more with regards to this problem. Certainly there are many more pleasurable periods ahead for many who scan your website.
I’m pretty pleased to discover this website. I want to to thank you for ones time for this particularly wonderful read!! I definitely really liked every little bit of it and I have you saved as a favorite to check out new things in your web site.
I just want to advise you that I am new to online blogging and clearly loved your write-up. Very likely I am going to remember your blog post . You undoubtedly have extraordinary article material. Truly Appreciate it for giving out with us your main internet webpage
I am just writing to make you know what a fine experience my wife’s princess enjoyed going through your webblog. She noticed lots of issues, which include what it’s like to have a very effective teaching spirit to let the rest effortlessly master certain multifaceted subject matter. You actually exceeded her expected results. I appreciate you for producing these useful, trustworthy, informative and even fun tips about the topic to Julie.
What i do not realize is actually how you’re now not actually much more neatly-preferred than you may be now. You are so intelligent. You know therefore significantly in relation to this subject, produced me individually consider it from numerous various angles. Its like men and women aren’t involved until it’s something to accomplish with Girl gaga! Your own stuffs great. Always maintain it up!|
I enjoy you because of your whole efforts on this blog. My mom enjoys carrying out investigations and it’s easy to see why. We all hear all relating to the dynamic form you make important secrets on the website and increase response from other individuals on the concern plus our favorite princess is being taught a whole lot. Take advantage of the remaining portion of the new year. Your conducting a tremendous job.
Hello, Neat post. There’s a problem together with your website in web explorer, may test this¡K IE still is the market chief and a good portion of other folks will leave out your great writing because of this problem.
fantastic post, very informative. I ponder why the opposite experts of this sector do not realize this. You must proceed your writing. I’m confident, you’ve a huge readers’ base already!
great put up, very informative. I’m wondering why the other specialists of this sector do not notice this. You must continue your writing. I’m confident, you’ve a huge readers’ base already!
I’m still learning from you, as I’m making my way to the top as well. I definitely enjoy reading everything that is written on your site.Keep the stories coming. I loved it!
You really make it seem really easy with your presentation however I find this topic to be actually something that I think I would never understand. It sort of feels too complicated and very huge for me. I am having a look forward on your next publish, I¡¦ll attempt to get the grasp of it!
I¡¦ll immediately grab your rss as I can’t to find your email subscription hyperlink or e-newsletter service. Do you’ve any? Kindly let me understand so that I may just subscribe. Thanks.
Thanks for another great post. Where else may anybody get that type of info in such an ideal way of writing? I have a presentation next week, and I’m at the search for such information.
Very informative blog.Thanks Again. Awesome.
I just wish to inform you that I am new to blog posting and incredibly loved your information. Very likely I am probably to bookmark your blog post . You definitely have wonderful article information. Truly Appreciate it for telling with us your current internet site information
I simply have to inform you that I am new to posting and absolutely adored your work. Likely I am inclined to bookmark your blog post . You absolutely have fabulous article content. Like it for swapping with us your main site report
I and my guys happened to be looking at the great tactics located on your website and so quickly came up with a horrible feeling I had not expressed respect to the blog owner for them. These boys were definitely passionate to study all of them and have in effect really been taking pleasure in those things. Many thanks for indeed being so considerate and then for selecting some fabulous issues most people are really eager to learn about. Our own sincere apologies for not expressing appreciation to you earlier.
Thanks so much for giving everyone remarkably pleasant possiblity to read from this website. It’s always so kind and also full of fun for me and my office friends to search your website not less than three times in 7 days to see the new things you will have. And lastly, we are at all times astounded with the outstanding suggestions you give. Selected 1 areas on this page are easily the simplest I’ve ever had.
Wow! This can be one particular of the most useful blogs We’ve ever arrive across on this subject. Actually Magnificent. I’m also a specialist in this topic therefore I can understand your effort.
I’m excited to uncover this website. I need to to thank you for your time due to this wonderful read!! I definitely really liked every little bit of it and i also have you saved as a favorite to check out new stuff on your blog.
you are really a excellent webmaster. The site loading speed is incredible. It sort of feels that you’re doing any distinctive trick. Furthermore, The contents are masterwork. you have performed a wonderful task in this topic!
Wonderful site. A lot of helpful information here. I¡¦m sending it to several friends ans also sharing in delicious. And naturally, thanks for your effort!
Awsome post and straight to the point. I don’t know if this is really the best place to ask but do you folks have any ideea where to hire some professional writers? Thanks in advance 🙂
Hello, you used to write magnificent, but the last few posts have been kinda boring¡K I miss your tremendous writings. Past several posts are just a bit out of track! come on!
I simply wished to thank you very much once more. I am not sure what I would have handled without those methods documented by you relating to such a concern. It truly was a real traumatic dilemma in my position, however , understanding this specialised fashion you processed the issue took me to weep for fulfillment. I am just grateful for this information and as well , expect you really know what a powerful job you happen to be getting into teaching the mediocre ones with the aid of your blog. Most likely you have never come across any of us.
Hi there, I found your site by way of Google at the same time as looking for a related topic, your website got here up, it appears to be like good. I have bookmarked it in my google bookmarks.
I’m really impressed with your writing skills and also with the layout on your blog. Is this a paid theme or did you customize it yourself? Anyway keep up the excellent quality writing, it is rare to see a great blog like this one nowadays..
Wow! Thank you! I always needed to write on my blog something like that. Can I include a portion of your post to my website?
Very efficiently written information. It will be helpful to anybody who utilizes it, including yours truly :). Keep doing what you are doing – can’r wait to read more posts.
Wow! This can be one particular of the most beneficial blogs We’ve ever arrive across on this subject. Actually Excellent. I am also an expert in this topic so I can understand your effort.
Its like you read my mind! You appear to know a lot about this, like you wrote the book in it or something. I think that you can do with a few pics to drive the message home a little bit, but instead of that, this is excellent blog. A fantastic read. I will definitely be back.
Great blog here! Also your web site loads up very fast! What web host are you using? Can I get your affiliate link to your host? I wish my website loaded up as fast as yours lol
obviously like your web site but you have to take a look at the spelling on quite a few of your posts. Several of them are rife with spelling problems and I in finding it very troublesome to inform the reality however I will surely come again again.
Hi there, I found your web site by means of Google whilst looking for a similar matter, your site got here up, it looks good. I have bookmarked it in my google bookmarks.
Great goods from you, man. I have understand your stuff previous to and you are just extremely fantastic. I actually like what you have acquired here, really like what you’re saying and the way in which you say it. You make it enjoyable and you still take care of to keep it sensible. I can’t wait to read far more from you. This is actually a tremendous website.
Thank you a lot for sharing this with all people you actually understand what you are talking approximately! Bookmarked. Please also consult with my web site =). We will have a link trade contract between us!
Perfectly written articles, Really enjoyed reading.
I was recommended this blog by my cousin. I am not sure whether this post is written by him as nobody else know such detailed about my difficulty. You’re wonderful! Thanks!
I simply could not leave your website prior to suggesting that I extremely loved the usual info a person supply for your visitors? Is gonna be back frequently in order to investigate cross-check new posts.
I reckon something really interesting about your site so I saved to fav.
You have remarked very interesting points ! ps decent web site . “It is better to be hated for who you are than to be loved for what you are not.” by Andre Gide.
My brother suggested I might like this website. He was entirely right. This post actually made my day. You can not imagine simply how much time I had spent for this information! Thanks!
I simply wanted to compose a brief word to be able to thank you for all the stunning tactics you are posting on this site. My considerable internet search has now been compensated with really good points to write about with my companions. I ‘d tell you that many of us visitors actually are rather endowed to exist in a very good place with so many marvellous individuals with good tricks. I feel rather grateful to have encountered your entire website and look forward to so many more enjoyable times reading here. Thank you once again for everything.
Somebody necessarily assist to make significantly articles I would state. That is the very first time I frequented your web page and to this point? I surprised with the analysis you made to make this particular post incredible. Magnificent process!
I was just looking for this information for a while. After six hours of continuous Googleing, finally I got it in your web site. I wonder what’s the lack of Google strategy that do not rank this type of informative websites in top of the list. Usually the top websites are full of garbage.
Very interesting points you have mentioned , appreciate it for putting up. “Death is Nature’s expert advice to get plenty of Life.” by Johann Wolfgang von Goethe.
I conceive you have noted some very interesting points , regards for the post.
I have recently started a website, the info you provide on this web site has helped me greatly. Thanks for all of your time & work. “There can be no real freedom without the freedom to fail.” by Erich Fromm.
Hi, Neat post. There’s a problem together with your web site in web explorer, could test this¡K IE still is the marketplace leader and a large component to other people will pass over your excellent writing due to this problem.
I’ve learn several good stuff here. Definitely worth bookmarking for revisiting. I wonder how so much attempt you put to create this type of magnificent informative website.
I was recommended this blog by my cousin. I’m not sure whether this post is written by him as no one else know such detailed about my difficulty. You are incredible! Thanks!
Normally I do not read post on blogs, but I would like to say that this write-up very pressured me to try and do it! Your writing taste has been amazed me. Thanks, very great article.
I really like your writing style, wonderful info , thankyou for posting : D.
I just wanted to write down a brief remark so as to thank you for some of the fabulous pointers you are sharing here. My incredibly long internet investigation has finally been recognized with incredibly good suggestions to go over with my family. I ‘d tell you that many of us readers are truly endowed to exist in a superb website with so many awesome individuals with insightful solutions. I feel very blessed to have seen the web site and look forward to plenty of more thrilling times reading here. Thanks once again for everything.
hi!,I like your writing very a lot! proportion we keep up a correspondence more approximately your article on AOL? I require a specialist on this house to unravel my problem. Maybe that’s you! Having a look ahead to look you.
Hello.This article was really remarkable, especially because I was browsing for thoughts on this issue last Thursday.
Nice blog here! Additionally your web site quite a bit up very fast! What web host are you the usage of? Can I am getting your associate hyperlink in your host? I wish my site loaded up as fast as yours lol
I have recently started a web site, the information you offer on this site has helped me greatly. Thank you for all of your time & work.
My wife and i were contented when Emmanuel managed to finish off his homework via the ideas he came across in your web pages. It is now and again perplexing to simply be offering key points which a number of people have been making money from. We remember we need the blog owner to appreciate because of that. The main explanations you’ve made, the straightforward website menu, the relationships you can help promote – it is many awesome, and it is letting our son and our family believe that the situation is entertaining, which is certainly unbelievably important. Thanks for the whole lot!
wonderful issues altogether, you simply gained a new reader. What would you recommend about your post that you just made some days in the past? Any positive?
I don’t even know how I ended up here, but I thought this post was good. I don’t know who you are but certainly you’re going to a famous blogger if you are not already 😉 Cheers!
When your
Some genuinely nice and useful information on this internet site, as well I conceive the style and design holds excellent features.
Hi my loved one! I want to say that this post is amazing, nice written and include approximately all important infos. I would like to see more posts like this .
Unquestionably believe that which you stated. Your favorite justification appeared to be on the internet the easiest thing to be aware of. I say to you, I certainly get annoyed while people think about worries that they just don’t know about. You managed to hit the nail upon the top as well as defined out the whole thing without having side effect , people can take a signal. Will probably be back to get more. Thanks
Magnificent beat ! I wish to apprentice while you amend your web site, how can i subscribe for a blog site? The account helped me a acceptable deal. I had been a little bit acquainted of this your broadcast offered bright clear idea
hey there and thank you for your information – I’ve certainly picked up something new from right here. I did however expertise some technical points using this web site, since I experienced to reload the website many times previous to I could get it to load properly. I had been wondering if your web hosting is OK? Not that I’m complaining, but sluggish loading instances times will sometimes affect your placement in google and could damage your high-quality score if advertising and marketing with Adwords. Well I’m adding this RSS to my e-mail and could look out for a lot more of your respective fascinating content. Ensure that you update this again soon..
I want to express my love for your kindness in support of visitors who really want help with this particular issue. Your special dedication to passing the message up and down turned out to be rather useful and have consistently allowed many people just like me to realize their pursuits. Your personal invaluable suggestions entails a lot to me and additionally to my office colleagues. Best wishes; from everyone of us.
Hello, you used to write excellent, but the last few posts have been kinda boring¡K I miss your great writings. Past few posts are just a little bit out of track! come on!
Hi there, just became alert to your blog through Google, and found that it is truly informative. I’m going to watch out for brussels. I’ll appreciate if you continue this in future. Numerous people will be benefited from your writing. Cheers!
Very efficiently written story. It will be beneficial to anybody who employess it, as well as me. Keep up the good work – looking forward to more posts.
Hello, you used to write wonderful, but the last several posts have been kinda boring¡K I miss your great writings. Past several posts are just a little bit out of track! come on!
You have brought up a very wonderful points , regards for the post.
Wow, superb blog layout! How long have you been blogging for? you made blogging look easy. The overall look of your web site is great, let alone the content!
I got what you intend, thanks for posting .Woh I am thankful to find this website through google. “Don’t be afraid of opposition. Remember, a kite rises against not with the wind.” by Hamilton Mabie.
I like this post, enjoyed this one regards for putting up. “The universe is not hostile, nor yet is it unfriendly. It is simply indifferent.” by John Andrew Holmes.
I just could not go away your website prior to suggesting that I really enjoyed the usual info an individual provide in your visitors? Is gonna be back often in order to check up on new posts.
Keep functioning ,impressive job!
My brother suggested I might like this website. He was totally right. This post truly made my day. You cann’t imagine simply how much time I had spent for this information! Thanks!
Definitely believe that which you said. Your favorite justification appeared to
be on the web the easiest thing to be aware of. I say to you, I definitely get irked while people think about worries
that they plainly don’t know about. You managed to hit the nail upon the top as
well as defined out the whole thing without having side-effects , people could take a signal.
Will probably be back to get more. Thanks
Heya i am for the first time here. I came across this board and I find It truly useful & it helped me out a lot. I hope to give something back and aid others like you helped me.
There is visibly a lot to realize about this. I consider you made certain nice points in features also.
I have read a few excellent stuff here. Definitely price bookmarking for revisiting. I wonder how so much attempt you set to create this kind of magnificent informative site.
Needed to create you the very little observation just to thank you very much again for your incredible pointers you have shown on this site. It has been so strangely generous with you to deliver unhampered what most people could possibly have offered as an e book to make some bucks for themselves, and in particular considering that you might have tried it if you desired. These tricks likewise acted to become a great way to be sure that the rest have the identical keenness similar to my personal own to grasp a lot more on the topic of this condition. I’m sure there are millions of more pleasant moments ahead for people who looked at your website.
Valuable info. Lucky me I found your web site by accident, and I’m stunned why this coincidence didn’t took place earlier! I bookmarked it.
Wow! Thank you! I always needed to write on my site something like that. Can I include a fragment of your post to my site?
I like it whenever people come together and share views. Great website, keep it up!
Excellent post. I was checking constantly this
blog and I’m impressed! Very useful info particularly the last part
🙂 I care for such information much. I was seeking this
certain info for a long time. Thank you and best of luck.
You actually make it seem so easy with your presentation but I find this topic to be actually something that I think I would never understand. It seems too complex and very broad for me. I’m looking forward for your next post, I will try to get the hang of it!
Regards for helping out, great information. “Riches cover a multitude of woes.” by Menander.
Very interesting topic, appreciate it for posting.
Good – I should definitely pronounce, impressed with your website. I had no trouble navigating through all tabs and related info ended up being truly simple to do to access. I recently found what I hoped for before you know it in the least. Quite unusual. Is likely to appreciate it for those who add forums or anything, website theme . a tones way for your client to communicate. Excellent task.
Keep up the superb work , I read few articles on this website and I believe that your web blog is rattling interesting and holds circles of good information.
I was recommended this web site by my cousin. I’m not sure whether this post is written by him as nobody else know such detailed about my trouble. You’re wonderful! Thanks!
You made some good points there. I looked on the internet for the subject matter and found most guys will agree with your blog.
Well I truly liked studying it. This subject procured by you is very practical for good planning.
Wow, awesome blog layout! How long have you been blogging for? you made blogging look easy. The entire glance of your site is excellent, let alone the content!
I¡¦ve read some good stuff here. Definitely worth bookmarking for revisiting. I surprise how much attempt you set to make this sort of great informative site.
You actually make it seem so easy with your presentation however I to find this matter to be really one thing which I feel I would never understand. It kind of feels too complicated and very huge for me. I am looking forward for your subsequent post, I¡¦ll attempt to get the cling of it!
Thanks for any other informative site. The place else may I am getting that type of information written in such an ideal method? I’ve a challenge that I’m simply now operating on, and I’ve been at the look out for such info.
Excellent blog right here! Also your website lots up very fast! What host are you using? Can I am getting your affiliate link in your host? I desire my website loaded up as quickly as yours lol
Excellent website. A lot of helpful information here. I¡¦m sending it to several friends ans also sharing in delicious. And naturally, thank you to your sweat!
Wow! This can be one particular of the most helpful blogs We have ever arrive across on this subject. Actually Wonderful. I am also a specialist in this topic therefore I can understand your effort.
Hi, Neat post. There’s an issue along with your website in internet explorer, may check this… IE still is the marketplace chief and a big component to people will pass over your fantastic writing because of this problem.
I truly enjoy studying on this site, it contains superb content . “Something unpredictable but in the end it’s right, I hope you have the time of your life.” by Greenday.
Great write-up, I¡¦m regular visitor of one¡¦s web site, maintain up the excellent operate, and It’s going to be a regular visitor for a lengthy time.
Fantastic beat ! I wish to apprentice while you amend your site, how could i subscribe for a blog website? The account aided me a acceptable deal. I had been tiny bit acquainted of this your broadcast offered bright clear idea
You could certainly see your skills within the work you write. The world hopes for even more passionate writers like you who aren’t afraid to mention how they believe. All the time follow your heart.
Nice read, I just passed this onto a colleague who was doing a little research on that. And he actually bought me lunch since I found it for him smile Thus let me rephrase that: Thanks for lunch!
Heya i’m for the first time here. I came across this board and I find It really useful & it helped me out much. I hope to give something back and help others like you aided me.
Hiya, I’m really glad I’ve found this info. Nowadays bloggers publish only about gossips and internet and this is actually frustrating. A good blog with interesting content, that is what I need. Thanks for keeping this web site, I’ll be visiting it. Do you do newsletters? Cant find it.
Great website! I am loving it!! Will come back again. I am bookmarking your feeds also
Heya i am for the first time here. I found this board and I find It truly useful & it helped me out a lot. I hope to give something back and help others like you helped me.
I like the helpful information you provide in your articles. I’ll bookmark your weblog and check again here regularly. I’m quite certain I’ll learn many new stuff right here! Good luck for the next!
I’ve been browsing on-line more than three hours lately, but I never discovered any fascinating article like yours. It is pretty price sufficient for me. In my opinion, if all webmasters and bloggers made good content material as you probably did, the internet will be much more helpful than ever before.
I do not even know how I ended up here, but I thought this post was great. I do not know who you are but definitely you are going to a famous blogger if you aren’t already 😉 Cheers!
I’m so happy to read this. This is the type of manual that needs to be given and not the accidental misinformation that is at the other blogs. Appreciate your sharing this best doc.
I’m still learning from you, while I’m trying to achieve my goals. I certainly love reading all that is written on your blog.Keep the tips coming. I enjoyed it!
Useful info. Lucky me I found your web site accidentally, and I am surprised why this accident didn’t happened earlier! I bookmarked it.
Great post however I was wondering if you could write a litte more on this subject? I’d be very thankful if you could elaborate a little bit further. Thanks!
It is truly a great and useful piece of information. I’m glad that you just shared this useful information with us. Please keep us up to date like this. Thank you for sharing.
You could definitely see your skills in the work you write. The arena hopes for even more passionate writers such as you who aren’t afraid to mention how they believe. At all times go after your heart. “What power has law where only money rules.” by Gaius Petronius.
hey there and thank you for your info – I’ve definitely picked up anything new from right here. I did however expertise a few technical issues using this web site, since I experienced to reload the website many times previous to I could get it to load properly. I had been wondering if your hosting is OK? Not that I am complaining, but sluggish loading instances times will often affect your placement in google and could damage your quality score if advertising and marketing with Adwords. Anyway I am adding this RSS to my email and could look out for much more of your respective exciting content. Make sure you update this again very soon..
I have been surfing on-line greater than three hours today, but I never found any interesting article like yours. It is beautiful worth sufficient for me. In my opinion, if all website owners and bloggers made just right content material as you probably did, the web might be a lot more helpful than ever before.
I’ve been browsing online more than 3 hours lately, yet I by no means found any interesting article like yours. It’s lovely value sufficient for me. In my view, if all site owners and bloggers made just right content material as you probably did, the net will be much more useful than ever before. “Perfection of moral virtue does not wholly take away the passions, but regulates them.” by Saint Thomas Aquinas.
Just desire to say your article is as astonishing. The clearness in your post is simply nice and i could assume you are an expert on this subject. Fine with your permission allow me to grab your RSS feed to keep up to date with forthcoming post. Thanks a million and please keep up the enjoyable work.
Thanks for the good writeup. It in fact was a enjoyment account it. Look complex to more delivered agreeable from you! By the way, how can we keep up a correspondence?
I’m gone to tellinformsay toconvey my little brother, that he should also visitgo to seepay a visitpay a quick visit this blogweblogwebpagewebsiteweb site on regular basis to takegetobtain updated from latestnewestmost recentmost up-to-datehottest newsinformationreportsgossipnews update.
I’m extremely impressed with your writing skills as well as with the layout on your weblog. Is this a paid theme or did you modify it yourself? Either way keep up the excellent quality writing, it is rare to see a great blog like this one today..
Wow, amazing blog layout! How long have you been blogging for? you made blogging look easy. The overall look of your website is magnificent, let alone the content!
As a Newbie, I am continuously browsing online for articles that can benefit me. Thank you
wonderful put up, very informative. I wonder why the opposite specialists of this sector don’t understand this. You should continue your writing. I am confident, you’ve a huge readers’ base already!
Very nice post and straight to the point. I am not sure if this is really the best place to ask but do you folks have any thoughts on where to employ some professional writers? Thanks 🙂
I loved as much as you’ll receive carried out right here. The sketch is tasteful, your authored material stylish. nonetheless, you command get bought an edginess over that you wish be delivering the following. unwell unquestionably come more formerly again as exactly the same nearly a lot often inside case you shield this increase.
I simply wanted to thank you very much again. I do not know what I would’ve done without the entire creative concepts documented by you about this area of interest. It was before the frightening problem in my circumstances, however , taking a look at the very specialised technique you dealt with it forced me to jump with joy. I am just happy for your work and then trust you recognize what an amazing job you’re getting into training other individuals through a web site. Probably you’ve never got to know any of us.
Hello, i think that i saw you visited my website so i came to “return the favor”.I’m attempting to find things to enhance my web site!I suppose its ok to use a few of your ideas!!
I have not checked in here for some time since I thought it was getting boring, but the last several posts are good quality so I guess I¡¦ll add you back to my daily bloglist. You deserve it my friend 🙂
I really like your writing style, excellent information, thanks for posting :D. “Much unhappiness has come into the world because of bewilderment and things left unsaid.” by Feodor Mikhailovich Dostoyevsky.
Keep up the good work , I read few posts on this website and I think that your web site is really interesting and has circles of superb information.
Merely wanna input that you have a very nice site, I enjoy the layout it really stands out.
I lovereally like your blog.. very nice colors & theme. Did you createdesignmake this website yourself or did you hire someone to do it for you? Plz replyanswer backrespond as I’m looking to createdesignconstruct my own blog and would like to knowfind out where u got this from. thanksthanks a lotkudosappreciate itcheersthank youmany thanks
Great article. It is unfortunate that over the last 10 years, the travel industry has already been able to to deal with terrorism, SARS, tsunamis, flu virus, swine flu, and the first ever real global tough economy. Through it all the industry has proven to be robust, resilient and also dynamic, discovering new strategies to deal with trouble. There are continually fresh troubles and opportunity to which the sector must again adapt and act in response.
Hello, you used to write excellent, but the last few posts have been kinda boring¡K I miss your super writings. Past several posts are just a little out of track! come on!
There is evidently a bunch to realize about this. I consider you made some good points in features also.
I dugg some of you post as I thought they were handy invaluable
Magnificent goods from you, man. I have understand your stuff previous to and you’re just extremely magnificent. I actually like what you’ve acquired here, certainly like what you are stating and the way in which you say it. You make it enjoyable and you still care for to keep it smart. I can not wait to read far more from you. This is actually a wonderful website.
But wanna admit that this is extremely helpful, Thanks for taking your time to write this.
Fantastic beat ! I would like to apprentice while you amend your site, how can i subscribe for a blog website? The account aided me a acceptable deal. I had been tiny bit acquainted of this your broadcast offered bright clear concept
It¡¦s really a nice and helpful piece of information. I am happy that you just shared this useful info with us. Please stay us informed like this. Thanks for sharing.
I like this post, enjoyed this one thanks for posting. “‘I have done my best.’ That is about all the philosophy of living one needs.” by Lin Yutang.
Hi there, You have done an incredible job. I’ll definitely digg it and personally suggest to my friends. I’m sure they’ll be benefited from this site.
I like what you guys are up also. Such intelligent work and reporting! Keep up the superb works guys I have incorporated you guys to my blogroll. I think it’ll improve the value of my web site :).
I just wanted to write down a word so as to appreciate you for these remarkable facts you are sharing here. My long internet investigation has now been recognized with beneficial insight to talk about with my friends and family. I ‘d state that that most of us readers are unequivocally fortunate to live in a fine place with many brilliant individuals with great opinions. I feel extremely grateful to have seen your entire webpages and look forward to so many more fun moments reading here. Thanks a lot again for all the details.
great issues altogether, you just won a logo new reader. What would you recommend about your submit that you made a few days in the past? Any sure?
Well I sincerely enjoyed reading it. This tip offered by you is very helpful for proper planning.
Just want to say your article is as astonishing. The clearness in your post is just cool and i could assume you’re an expert on this subject. Fine with your permission let me to grab your RSS feed to keep updated with forthcoming post. Thanks a million and please keep up the rewarding work.
You made some clear points there. I looked on the internet for the subject matter and found most individuals will consent with your website.
You actually make it seem so easy with your presentation but I find this topic to be really something that I think I would never understand. It seems too complex and extremely broad for me. I’m looking forward for your next post, I’ll try to get the hang of it!
NowAt this timeAt this momentRight away I am goinggoing awayready to do my breakfast, afterlater thanoncewhenafterward having my breakfast coming againyet againover again to read moreadditionalfurtherother news.
I¡¦m no longer positive where you’re getting your information, but great topic. I needs to spend some time studying much more or working out more. Thanks for excellent info I was on the lookout for this info for my mission.
What’s Happening i am new to this, I stumbled upon this I have found It positively helpful and it has aided me out loads. I hope to contribute & help other users like its helped me. Good job.
Hello.This post was extremely motivating, especially since I was browsing for thoughts on this topic last Wednesday.
As soon as I found this site I went on reddit to share some of the love with them.
Fantastic web site. Lots of useful info here. I’m sending it to several buddies ans additionally sharing in delicious. And obviously, thank you to your sweat!
I have been surfing online more than 3 hours today, yet I never found any interesting article like yours. It’s pretty worth enough for me. Personally, if all web owners and bloggers made good content as you did, the internet will be a lot more useful than ever before.
good morning, notable blog on blubbery loss. similar helped.
You really make it appear really easy along with your presentation however I to find this matter to be really something that I believe I’d never understand. It sort of feels too complex and extremely vast for me. I’m taking a look ahead in your next put up, I¡¦ll attempt to get the cling of it!
I am not positive where you are getting your information, however good topic. I must spend some time studying much more or figuring out more. Thank you for wonderful information I used to be searching for this information for my mission.
Wow, incredible blog format! How lengthy have you been blogging for? you made blogging glance easy. The total look of your site is great, as smartly as the content material!
you are truly a just right webmaster. The website loading velocity is incredible. It sort of feels that you’re doing any distinctive trick. Also, The contents are masterwork. you’ve done a fantastic process on this subject!
Great blog here! Also your web site loads up very fast! What host are you using? Can I get your affiliate link to your host? I wish my site loaded up as quickly as yours lol
Nice blog here! Also your web site loads up very fast! What host are you using? Can I get your affiliate link to your host? I wish my site loaded up as fast as yours lol
naturally like your website however you have to check the spelling on several of your posts. A number of them are rife with spelling issues and I in finding it very bothersome to inform the truth then again I¡¦ll definitely come again again.
Heya i’m for the first time here. I found this board and I find It really useful & it helped me out much. I hope to give something back and help others like you aided me.
I am now not sure the place you are getting your info, but good topic. I must spend some time finding out more or understanding more. Thanks for magnificent info I was searching for this info for my mission.
I am continuously searching online for articles that can assist me. Thx!
I have to express my affection for your kindness in support of individuals that have the need for guidance on this important theme. Your real commitment to passing the solution all through came to be quite invaluable and has truly helped some individuals just like me to achieve their pursuits. Your entire useful tutorial can mean a lot a person like me and further more to my mates. With thanks; from all of us.
Great post. I was checking constantly this blog and I’m impressed! Very useful info specifically the last part 🙂 I care for such info much. I was looking for this particular info for a long time. Thank you and good luck.
I like this web blog so much, saved to bookmarks. “Nostalgia isn’t what it used to be.” by Peter De Vries.
You actually make it seem so easy with your presentation but I find this topic to be really something which I think I would never understand. It seems too complex and extremely broad for me. I’m looking forward for your next post, I’ll try to get the hang of it!
Dead written written content , thanks for selective information .
Heya i am for the first time here. I came across this board and I find It truly useful & it helped me out a lot. I hope to give something back and help others like you helped me.
I am not sure where you are getting your info, but great topic. I needs to spend some time learning more or understanding more. Thanks for great information I was looking for this info for my mission.
I really appreciate this post. I have been looking all over for this! Thank goodness I found it on Bing. You’ve made my day! Thank you again!
Very good info can be found on blog . “Life without a friend is death without a witness.” by Eugene Benge.
Thank you for sharing excellent informations. Your site is so cool. I am impressed by the details that you have on this blog. It reveals how nicely you perceive this subject. Bookmarked this website page, will come back for more articles. You, my pal, ROCK! I found simply the info I already searched everywhere and simply could not come across. What an ideal web-site.
Bonjour ! Il n’y a pas de flux RSS ici ?
I think this is one of the most important info for me. And i’m glad reading your article. But should remark on some general things, The web site style is ideal, the articles is really nice : D. Good job, cheers
I’ve been surfing online more than three hours today, yet I never found any interesting article like yours. It is pretty worth enough for me. In my view, if all webmasters and bloggers made good content as you did, the net will be much more useful than ever before.
Whats Taking place i’m new to this, I stumbled upon this I have discovered It positively helpful and it has aided me out loads. I’m hoping to give a contribution & aid different users like its helped me. Good job.
I think other website proprietors should take this website as an model, very clean and excellent user friendly style and design, let alone the content. You are an expert in this topic!
I precisely had to thank you so much once again. I do not know the things I would’ve worked on without the type of tactics documented by you regarding such field. It truly was a very frustrating concern for me, however , looking at this well-written technique you managed it took me to cry over contentment. I’m just happy for the work as well as have high hopes you really know what a powerful job you happen to be getting into educating people today by way of your web site. Most likely you’ve never come across all of us.
Awsome article and right to the point. I am not sure if this is actually the best place to ask but do you folks have any ideea where to employ some professional writers? Thanks in advance 🙂
I will right away snatch your rss feed as I can’t in finding your email subscription hyperlink or newsletter service. Do you’ve any? Kindly let me recognize so that I may just subscribe. Thanks.
Hi there, I found your site by the use of Google while looking for a related topic, your website came up, it seems great. I have bookmarked it in my google bookmarks.
Your style is really unique compared to other folks I have read stuff from.
Thank you for posting when you have the opportunity, Guess I’ll
just bookmark this page.
Good site! I truly love how it is simple on my eyes and the data are well written. I’m wondering how I could be notified whenever a new post has been made. I’ve subscribed to your RSS feed which must do the trick! Have a nice day!
Useful info. Lucky me I discovered your site unintentionally, and I am stunned why this coincidence did not came about in advance! I bookmarked it.
Great post. I was checking continuously this blog and I’m impressed! Very helpful information particularly the last part 🙂 I care for such information a lot. I was seeking this certain information for a long time. Thank you and best of luck.
Bonjour ! tiens c’est sympa comme site
Thank you, I have recently been looking for info about this topic for a long time and yours is the greatest I have came upon till now. However, what concerning the conclusion? Are you positive concerning the supply?
Wow! This could be one particular of the most useful blogs We’ve ever arrive across on this subject. Basically Fantastic. I am also a specialist in this topic so I can understand your hard work.
Hi there, You’ve done an incredible job. I will definitely digg it and personally suggest to my friends. I am confident they will be benefited from this website.
Good web site! I really love how it is simple on my eyes and the data are well written. I’m wondering how I could be notified when a new post has been made. I have subscribed to your RSS which must do the trick! Have a nice day!
Hello There. I found your blog using msn. This is a really well written article. I’ll make sure to bookmark it and return to read more of your useful info. Thanks for the post. I will definitely comeback.
You completed several fine points there. I did a search on the topic and found mainly persons will consent with your blog.
I simply wished to say thanks once again. I do not know what I could possibly have undertaken without these opinions contributed by you relating to such a field. It became a terrifying situation in my view, nevertheless taking a look at the skilled style you managed that forced me to leap over delight. I’m just thankful for your advice and in addition pray you know what an amazing job you’re putting in training people thru your blog post. I’m certain you have never come across all of us.
My brother suggested I might like this blog. He was totally right. This post truly made my day. You can not imagine simply how much time I had spent for this info! Thanks!
I¡¦ve recently started a website, the information you offer on this site has helped me tremendously. Thank you for all of your time & work.
What i do not understood is in fact how you are no longer really much more well-liked than you might be now. You are so intelligent. You already know thus considerably in relation to this matter, made me for my part believe it from a lot of varied angles. Its like men and women aren’t fascinated unless it¡¦s something to accomplish with Lady gaga! Your personal stuffs outstanding. At all times maintain it up!
What i don’t understood is in reality how you’re not actually a lot more neatly-appreciated than you may be now. You’re very intelligent. You understand thus considerably relating to this topic, produced me individually consider it from a lot of varied angles. Its like women and men don’t seem to be fascinated unless it is something to do with Woman gaga! Your individual stuffs great. All the time care for it up!
Wow, fantastic blog structure! How long have you ever been blogging for? you make blogging look easy. The whole glance of your web site is excellent, as neatly as the content material!
Thanks for every other fantastic article. Where else may just anybody get that type of info in such a perfect method of writing? I have a presentation subsequent week, and I am on the look for such info.
Nice read, I just passed this onto a colleague who was doing some research on that. And he actually bought me lunch as I found it for him smile So let me rephrase that: Thanks for lunch!
Whats Taking place i am new to this, I stumbled upon this I’ve discovered It positively useful and it has aided me out loads. I hope to contribute & assist other customers like its aided me. Good job.
Excellent read, I just passed this onto a friend who was doing some research on that. And he just bought me lunch because I found it for him smile So let me rephrase that: Thank you for lunch! “Any man would be forsworn to gain a kingdom.” by Roger Zelazny.
Somebody essentially lend a hand to make seriously posts I might state.
This is the very first time I frequented your web page and so far?
I amazed with the research you made to create this particular publish incredible.
Great activity!
You have brought up a very superb points , thanks for the post.
If you wish for to improve your experience just keep visiting this site and be updated with the latest gossip posted here.
I do not even know how I ended up here, but I thought this post was good.
I don’t know who you are but certainly you are going to a famous blogger if you
are not already 😉 Cheers!
Definitely believe that which you stated. Your favorite reason appeared to be on the web the easiest thing to be aware of. I say to you, I definitely get annoyed while people consider worries that they plainly do not know about. You managed to hit the nail upon the top and also defined out the whole thing without having side-effects , people can take a signal. Will probably be back to get more. Thanks
You actually make it seem so easy with your presentation but I find this topic to be really something which I think I would never understand. It seems too complex and very broad for me. I’m looking forward for your next post, I’ll try to get the hang of it!
Great blog here! Also your site loads up fast! What web host are you using? Can I get your affiliate link to your host? I wish my web site loaded up as fast as yours lol
Very useful resources that you have mentioned, thank you for writing.
It’s practically extremely difficult to see well-informed visitors on this issue, nonetheless you seem like you fully grasp which you’re writing about! Thanks A Lot
You have brought up a very excellent details , regards for the post.
Great post. I was checking constantly this blog and I’m impressed! Very helpful information specifically the last part 🙂 I care for such information a lot. I was looking for this particular information for a long time. Thank you and good luck.
I gotta bookmark this website it seems invaluable handy
Why visitors still make use of to read news papers when in this technological globe everything is presented on web?
Unbelievably beneficial data you have mentioned, a big heads up for adding.
It certainly is practically unattainable to encounter well-advised men or women on this theme, nonetheless you appear like you realize the things you’re revealing! Appreciation
Can I use a different WordPress theme to a WordPress hosted blog?
I merely desire to show you that I am new to blog posting and genuinely liked your site. Likely I am probably to store your blog post . You really have superb article content. Appreciate it for swapping with us all of your url information
It certainly is practically impossible to find well-qualified people on this matter, then again you appear like you fully understand whatever you’re revealing! With Thanks
Major thanks for the post. Fantastic.
Greetings! Very helpful advice within this article! It’s the little changes that make the
largest changes. Thanks a lot for sharing!
Absolutely beneficial knowledge you have remarked, thanks a lot for posting.
I really like your writing style, wonderful info , regards for posting : D.
It is perfect time to make some plans for the future and it’s time to be happy. I have read this post and if I could I wish to suggest you some interesting things or tips. Maybe you could write next articles referring to this article. I desire to read even more things about it!
Hello.This article was extremely fascinating, especially because I was browsing for thoughts on this matter last Saturday.
you’re in point of fact a excellent webmaster. The website loading speed is amazing. It seems that you are doing any distinctive trick. Furthermore, The contents are masterwork. you’ve performed a fantastic activity in this topic!
It is actually near not possible to come across well-informed individual on this subject, nevertheless you look like you fully understand what you’re preaching about! Bless You
It can be mostly unattainable to see well-advised users on this theme, but you come across as like you fully grasp exactly what you’re preaching about! Many Thanks
It really is practically unthinkable to come across well-aware men or women on this issue, although you seem like you comprehend what you’re revealing! With Thanks
Definitely alluring specifics you’ll have remarked, thanks a lot for writing.
great points altogether, you just gained a new reader. What would you recommend about your post that you just made a few days ago? Any certain?
You have noted very interesting details! ps decent website.
Very interesting subject, thank you for putting up.
It is actually near close to impossible to come across well-aware women and men on this subject, fortunately you appear like you are familiar with exactly what you’re covering! Gratitude
I simply wish to tell you that I am new to wordpress blogging and very much admired your review. Quite possibly I am probably to bookmark your blog post . You truly have fantastic article material. Delight In it for swapping with us your own internet document
It can be near unattainable to see well-advised men and women on this matter, still, you appear like you comprehend what you’re writing about! Gratitude
Nice blog here! Also your web site loads up fast! What web host are you using? Can I get your affiliate link to your host? I wish my website loaded up as fast as yours lol
Highly intriguing knowledge that you have remarked, many thanks for publishing.
It appears like 1 of the guys could handle 1 skinny girl twerking but when the other came it was too much for him.
Incredibly intriguing highlights you’ll have remarked, thank you so much for publishing.
It’s actually mostly unattainable to find well-updated men and women on this niche, although you come across as like you realize the things you’re writing on! Thanks A Lot
Wow, superb blog layout! How long have you been blogging for? you made blogging look easy. The overall look of your site is excellent, as well as the content!
You are my inhalation , I possess few blogs and rarely run out from to brand.I believe this website has got some rattling good information for everyone. “Glory is fleeting, but obscurity is forever.” by Napoleon.
Wow! Thank you! I permanently wanted to write on my blog something like that. Can I include a fragment of your post to my blog?
Thanks , I have just been searching for info about this subject for a long time and yours is the greatest I’ve discovered so far. But, what in regards to the bottom line? Are you sure concerning the source?
As I site possessor I believe the content material here is rattling wonderful , appreciate it for your efforts. You should keep it up forever! Best of luck.
Someone essentially help to make critically posts I might state. This is the first time I frequented your web page and to this point? I surprised with the analysis you made to create this particular put up amazing. Excellent activity!
I precisely had to thank you very much all over again. I’m not certain the things I would’ve carried out without these pointers revealed by you directly on such situation. It seemed to be the terrifying issue in my position, but noticing a expert approach you dealt with it took me to jump for delight. Now i’m happier for your information and as well , expect you realize what a powerful job you have been getting into teaching many people using a blog. More than likely you haven’t encountered all of us.
Someone essentially lend a hand to make significantly articles I might state. That is the very first time I frequented your website page and thus far? I surprised with the research you made to make this actual publish extraordinary. Great task!
I merely wish to share it with you that I am new to posting and very much loved your post. Very likely I am probably to store your blog post . You undoubtedly have magnificent article materials. Acknowledge it for giving out with us your own web report
Tremendously entertaining data you’ll have remarked, say thanks a lot for adding.
You have mentioned very interesting details! ps nice web site.
Thanks for any other magnificent post. Where else could anyone get that type of info in such an ideal manner of writing? I’ve a presentation subsequent week, and I’m on the look for such info.
Generally I do not read article on blogs, but I would like to say that this write-up very forced me to check out and do it! Your writing style has been amazed me. Thank you, quite great article.
|Among spitting bars in her island accent, Nicki Minaj backs up her wagon on Busta Rhymes in his Twerk It” video.|Girls twerking turns me on as a lot
I simply couldn’t go away your site prior to suggesting that I really enjoyed the standard information a person supply in your visitors? Is gonna be back incessantly to check up on new posts
Generally I don’t learn post on blogs, however I would like to say that this write-up very forced me to try and do it! Your writing taste has been amazed me. Thanks, quite great post.
Keep working ,terrific job!
Thanks for any other magnificent post. The place else may anybody get that type of info in such a perfect manner of writing? I have a presentation next week, and I’m at the search for such information.
You completed several nice points there. I did a search on the issue and found the majority of people will consent with your blog.
What i do not understood is actually how you are now not actually much more smartly-liked than you may be now. You’re very intelligent. You realize thus significantly in the case of this subject, made me for my part believe it from numerous various angles. Its like men and women are not fascinated unless it is something to do with Woman gaga! Your personal stuffs excellent. Always maintain it up!
You really make it appear so easy together with your presentation however I in finding this matter to be actually one thing which I think I might by no means understand. It seems too complex and very vast for me. I’m looking ahead in your next put up, I will try to get the hold of it!
Heya i am for the first time here. I came across this board and I find It truly useful & it helped me out much. I hope to give something back and aid others like you helped me.
Nice post. I was checking continuously this blog and I’m impressed! Very helpful information particularly the last part 🙂 I care for such info much. I was looking for this particular info for a very long time. Thank you and best of luck.
My brother recommended I might like this blog. He was totally right. This post truly made my day. You cann’t imagine simply how much time I had spent for this info! Thanks!
I like the valuable info you provide in your articles. I’ll bookmark your blog and check again here frequently. I am quite certain I’ll learn a lot of new stuff right here! Good luck for the next!
We’re a group of volunteers and starting a brand new scheme in our community. Your web site provided us with valuable info to paintings on. You’ve performed a formidable task and our whole group will likely be grateful to you.
What i don’t realize is in reality how you’re no longer really a lot more well-liked than you might be now. You’re very intelligent. You already know thus considerably in the case of this subject, produced me in my opinion believe it from numerous numerous angles. Its like men and women are not fascinated except it¡¦s one thing to do with Girl gaga! Your personal stuffs great. Always take care of it up!
Its like you read my mind! You appear to know a lot about
this, like you wrote the book in it or something. I think that you can do
with some pics to drive the message home a bit, but instead of that, this is great blog.
A great read. I’ll certainly be back.
I have recently started a site, the information you provide on this web site has helped me greatly. Thanks for all of your time & work. “Never trust anybody who says ‘trust me.’ Except just this once, of course. – from Steel Beach” by John Varley.
I dugg some of you post as I cerebrated they were very useful very useful
Hi my family member! I wish to say that this post is awesome, great written and include almost all important infos. I’d like to peer extra posts like this.
Thank you for sharing superb informations. Your web site is so cool. I’m impressed by the details that you’ve on this website. It reveals how nicely you understand this subject. Bookmarked this website page, will come back for more articles. You, my friend, ROCK! I found simply the info I already searched all over the place and just couldn’t come across. What a great website.
Hello there, You have done an incredible job. I’ll certainly digg it and personally recommend to my friends. I’m confident they’ll be benefited from this web site.
I have recently started a web site, the information you offer on this website has helped me tremendously. Thank you for all of your time & work. “Yield not to evils, but attack all the more boldly.” by Virgil.
hello!,I love your writing so so much! share we keep up a correspondence extra approximately your article on AOL? I need an expert on this space to resolve my problem. Maybe that is you! Looking ahead to look you.
Very interesting subject, thanks for posting.
Hello, you used to write great, but the last few posts have been kinda boring… I miss your tremendous writings. Past several posts are just a bit out of track! come on!
Good site! I really love how it is easy on my eyes and the data are well written. I’m wondering how I might be notified when a new post has been made. I have subscribed to your RSS feed which must do the trick! Have a great day!
Good day! I just would like to give a huge thumbs up for the great data you’ve gotten right here on this post. I can be coming back to your blog for more soon.
excellent issues altogether, you just received a brand new reader. What would you suggest in regards to your submit that you made a few days ago? Any certain?
I would like to thank you for the efforts you’ve put in writing this website. I’m hoping the same high-grade blog post from you in the upcoming also. Actually your creative writing abilities has inspired me to get my own blog now. Really the blogging is spreading its wings quickly. Your write up is a good example of it.
Magnificent beat ! I wish to apprentice while you amend your website, how can i subscribe for a blog site? The account helped me a acceptable deal. I had been tiny bit acquainted of this your broadcast offered bright clear concept
F*ckin’ amazing things here. I am very satisfied to peer your article. Thank you a lot and i’m taking a look ahead to touch you. Will you kindly drop me a e-mail?
This is very interesting, You are a very skilled blogger. I have joined your rss feed and look forward to seeking more of your wonderful post. Also, I have shared your website in my social networks!
I am really impressed with your writing skills as well as with the layout on your blog. Is this a paid theme or did you customize it yourself? Anyway keep up the excellent quality writing, it’s rare to see a nice blog like this one these days..
I am not sure where you are getting your information, but great topic. I needs to spend some time learning much more or understanding more. Thanks for excellent information I was looking for this information for my mission.
Hi my friend! I want to say that this post is amazing, nice written and include approximately all significant infos. I would like to see more posts like this .
Excellent beat ! I wish to apprentice while you amend your web site, how could i subscribe for a blog web site? The account aided me a acceptable deal. I had been tiny bit acquainted of this your broadcast provided bright clear idea
Very nice info and right to the point. I don’t know if this is really the best place to ask but do you folks have any thoughts on where to employ some professional writers? Thx 🙂
I have been reading out many of your stories and i must say clever stuff. I will make sure to bookmark your blog.
Hello.This article was really interesting, particularly because I was searching for thoughts on this topic last Thursday.
Hey very cool website!! Man .. Beautiful .. Amazing .. I’ll bookmark your site and take the feeds additionally…I’m glad to find numerous useful information here in the post, we want develop more techniques on this regard, thanks for sharing.
Thank you for sharing superb informations. Your website is so cool. I am impressed by the details that you’ve on this website. It reveals how nicely you perceive this subject. Bookmarked this web page, will come back for extra articles. You, my friend, ROCK! I found just the info I already searched all over the place and simply couldn’t come across. What an ideal web-site.
Pretty section of content. I just stumbled upon your site and in accession capital to assert that I acquire in fact enjoyed account your blog posts. Any way I will be subscribing to your feeds and even I achievement you access consistently fast.
excellent points altogether, you simply gained a new reader. What would you recommend about your post that you simply made a few days in the past? Any positive?
Hello there, I found your website by way of Google even as searching for a similar topic, your web site got here up, it seems to be good. I’ve bookmarked it in my google bookmarks.
Hi, Neat post. There is an issue along with your web site in internet explorer, might check this¡K IE still is the marketplace chief and a large component to other folks will omit your excellent writing because of this problem.
Valuable info. Fortunate me I discovered your site by chance, and I am shocked why this coincidence didn’t came about earlier! I bookmarked it.
Very efficiently written story. It will be supportive to everyone who usess it, as well as me. Keep doing what you are doing – looking forward to more posts.
Fantastic website. A lot of useful information here. I am sending it to several buddies ans additionally sharing in delicious. And certainly, thank you for your sweat!
I have been surfing online more than 3 hours today, yet I never found any interesting article like yours. It is pretty worth enough for me. In my view, if all website owners and bloggers made good content as you did, the web will be much more useful than ever before.
Its like you read my mind! You appear to know a lot about this, like you wrote the book in it or something. I think that you can do with some pics to drive the message home a little bit, but other than that, this is wonderful blog. An excellent read. I will definitely be back.
I conceive you have remarked some very interesting details , regards for the post.
I am extremely impressed with your writing skills and also with the layout on your blog. Is this a paid theme or did you customize it yourself? Anyway keep up the excellent quality writing, it is rare to see a nice blog like this one nowadays..
I’ve recently started a web site, the information you offer on this website has helped me greatly. Thank you for all of your time & work. “Quit worrying about your health. It’ll go away.” by Robert Orben.
Really fantastic information can be found on site . “Preach not to others what they should eat, but eat as becomes you, and be silent.” by Epictetus.
Thanks for the sensible critique. Me & my neighbor were just preparing to do some research on this. We got a grab a book from our area library but I think I learned more clear from this post. I am very glad to see such great information being shared freely out there.
You could certainly see your skills in the work you write. The world hopes for more passionate writers such as you who are not afraid to mention how they believe. Always follow your heart.
It¡¦s actually a cool and useful piece of information. I am satisfied that you simply shared this helpful info with us. Please stay us up to date like this. Thank you for sharing.
I wanted to write down a quick word in order to say thanks to you for all the magnificent instructions you are giving on this site. My time intensive internet investigation has now been rewarded with reputable points to talk about with my friends. I ‘d say that most of us readers are extremely lucky to be in a fabulous community with so many special individuals with useful guidelines. I feel somewhat lucky to have come across your entire web site and look forward to many more fun times reading here. Thank you once again for all the details.
It¡¦s really a nice and useful piece of info. I am glad that you simply shared this useful info with us. Please keep us up to date like this. Thanks for sharing.
I do accept as true with all of the ideas you’ve presented for your post. They are really convincing and can definitely work. Nonetheless, the posts are very brief for novices. May just you please lengthen them a bit from subsequent time? Thanks for the post.
Thanks for every other informative site. Where else may just I am getting that type of information written in such an ideal way? I have a mission that I am simply now operating on, and I’ve been at the glance out for such information.
Thanks , I’ve just been looking for info approximately this topic for a while and yours is the best I’ve found out till now. However, what concerning the conclusion? Are you positive in regards to the supply?
I am very happy to read this. This is the type of manual that needs to be given and not the accidental misinformation that is at the other blogs. Appreciate your sharing this best doc.
Hi, everything is going well here and ofcourse every one is sharing information, that’s in fact excellent, keep up writing.
Very nice post. I just stumbled upon your weblog and wanted to say that I’ve really enjoyed browsing your blog posts. After all I’ll be subscribing to your rss feed and I hope you write again soon!
I dugg some of you post as I cerebrated they were very helpful extremely helpful
I like this post, enjoyed this one appreciate it for putting up. “We seldom attribute common sense except to those who agree with us.” by La Rochefoucauld.
I like what you guys are up too. Such clever work and reporting! Carry on the superb works guys I have incorporated you guys to my blogroll. I think it’ll improve the value of my web site :).
It’s really a nice and helpful piece of info. I am satisfied that you shared this helpful info with us. Please keep us informed like this. Thank you for sharing.
I have to get across my passion for your kind-heartedness in support of all those that must have guidance on in this topic. Your special dedication to getting the solution all over became incredibly valuable and has regularly encouraged ladies just like me to reach their goals. Your entire important instruction indicates a whole lot to me and even further to my mates. With thanks; from all of us.
I’m still learning from you, as I’m improving myself. I certainly liked reading all that is posted on your site.Keep the aarticles coming. I loved it!
It is appropriate time to make some plans for the future and it is time to be happy. I’ve read this post and if I could I wish to suggest you some interesting things or advice. Perhaps you can write next articles referring to this article. I wish to read even more things about it!
Nice blog here! Also your site loads up fast! What host are you using? Can I get your affiliate link to your host? I wish my web site loaded up as fast as yours lol
Pretty section of content. I just stumbled upon your site and in accession capital to assert that I get in fact enjoyed account your blog posts. Any way I’ll be subscribing to your feeds and even I achievement you access consistently fast.
Valuable info. Lucky me I discovered your web site accidentally, and I’m shocked why this twist of fate didn’t came about in advance! I bookmarked it.
What i do not understood is in reality how you’re now not actually a lot more well-liked than you might be now. You are so intelligent. You already know thus considerably in relation to this topic, produced me in my opinion consider it from so many varied angles. Its like women and men are not involved unless it¡¦s one thing to do with Girl gaga! Your own stuffs excellent. At all times take care of it up!
I am continually invstigating online for ideas that can assist me. Thx!
Keep functioning ,remarkable job!
Hi there, I discovered your blog by way of Google even as looking for a comparable matter, your website got here up, it looks good. I have bookmarked it in my google bookmarks.
Great amazing issues here. I¡¦m very satisfied to look your post. Thank you a lot and i’m taking a look forward to touch you. Will you please drop me a mail?
I think this is among the most important information for me. And i’m glad reading your article. But want to remark on few general things, The website style is perfect, the articles is really excellent : D. Good job, cheers
I can’t believe how influential this post has been to me, it really grabbed us where it meant something.
I have shared this on my Facebook and just wanted to leave
a comment to thank you for the meaningful post.
Excellent website. A lot of helpful info here. I’m sending it to several pals ans also sharing in delicious. And of course, thank you to your effort!
Good blog! I truly love how it is easy on my eyes and the data are well written. I am wondering how I could be notified when a new post has been made. I’ve subscribed to your feed which must do the trick! Have a nice day!
Excellent weblog right here! Additionally your website loads up fast! What host are you using? Can I am getting your affiliate link in your host? I wish my website loaded up as quickly as yours lol
Thank you for the auspicious writeup. It in fact was a amusement account it. Look advanced to more added agreeable from you! By the way, how can we communicate?
Someone necessarily help to make seriously articles I might state. This is the first time I frequented your web page and up to now? I surprised with the analysis you made to create this particular put up incredible. Fantastic job!
I definitely wanted to send a simple message to express gratitude to you for the remarkable steps you are sharing at this site. My long internet search has at the end of the day been compensated with extremely good information to exchange with my co-workers. I ‘d state that that many of us visitors actually are definitely blessed to exist in a very good site with so many wonderful individuals with interesting advice. I feel somewhat blessed to have used the webpages and look forward to many more amazing moments reading here. Thanks a lot again for all the details.
You actually make it seem really easy together with your presentation however I in finding this matter to be really one thing which I think I would never understand. It sort of feels too complicated and very vast for me. I’m taking a look forward for your next submit, I will attempt to get the hold of it!
It is in reality a nice and useful piece of information. I am happy that you just shared this helpful info with us. Please stay us up to date like this. Thank you for sharing.
I do trust all the concepts you have presented in your post. They’re very convincing and can certainly work. Still, the posts are very brief for beginners. May just you please lengthen them a bit from subsequent time? Thanks for the post.
I am always invstigating online for posts that can help me. Thx!
hey there and thank you for your info – I have certainly picked up anything new from right here. I did however expertise some technical points using this website, since I experienced to reload the website a lot of times previous to I could get it to load correctly. I had been wondering if your web host is OK? Not that I am complaining, but slow loading instances times will often affect your placement in google and could damage your high-quality score if ads and marketing with Adwords. Anyway I’m adding this RSS to my email and can look out for much more of your respective fascinating content. Make sure you update this again soon..
Keep up the fantastic work , I read few posts on this web site and I conceive that your web site is very interesting and holds circles of fantastic info .
I was suggested this web site by my cousin. I’m not sure whether this post is written by him as nobody else know such detailed about my difficulty. You’re incredible! Thanks!
Of course, what a great blog and enlightening posts, I will bookmark your blog.Best Regards!
wonderful issues altogether, you simply gained a new reader. What could you recommend about your put up that you simply made a few days in the past? Any certain?
Very good blog post. Much obliged.
My brother suggested I might like this website. He was entirely right. This post actually made my day. You can not imagine simply how much time I had spent for this info! Thanks!
I’ve been surfing online more than 3 hours today, yet I never found any interesting article like yours. It’s pretty worth enough for me. Personally, if all webmasters and bloggers made good content as you did, the net will be a lot more useful than ever before.
fantastic points altogether, you just gained a logo new reader. What might you recommend about your publish that you made some days ago? Any positive?
Wow! This could be one particular of the most beneficial blogs We’ve ever arrive across on this subject. Basically Excellent. I am also a specialist in this topic so I can understand your effort.
its shocking you still believe in NASA Only person ignorant is None of NASA explanation is
You are my inhalation , I possess few blogs and very sporadically run out from to post .
You can certainly see your skills in the paintings you write. The arena hopes for even more passionate writers like you who are not afraid to mention how they believe. All the time go after your heart. “A simple fact that is hard to learn is that the time to save money is when you have some.” by Joe Moore.
I don’t even know how I ended up here, but I thought this post was great. I do not know who you are but certainly you are going to a famous blogger if you are not already 😉 Cheers!
Thanks for the sensible critique. Me & my neighbor were just preparing to do some research about this. We got a grab a book from our area library but I think I learned more from this post. I’m very glad to see such fantastic information being shared freely out there.
A person essentially help to make seriously articles I would state. This is the very first time I frequented your website page and thus far? I amazed with the research you made to create this particular publish extraordinary. Excellent job!
I am very happy to read this. This is the type of manual that needs to be given and not the random misinformation that’s at the other blogs. Appreciate your sharing this best doc.
I don’t even know how I ended up here, but I thought this post was good. I don’t know who you are but definitely you’re going to a famous blogger if you are not already 😉 Cheers!
I think this is one of the most significant info for me. And i am glad reading your article. But should remark on few general things, The website style is ideal, the articles is really nice : D. Good job, cheers
I’ve been surfing on-line greater than three hours as of late, but I never discovered any attention-grabbing article like yours. It is beautiful worth enough for me. Personally, if all web owners and bloggers made good content as you did, the web will probably be much more helpful than ever before.
I just couldn’t leave your site prior to suggesting that I extremely enjoyed the standard info a person provide on your visitors? Is going to be back regularly to check out new posts
I precisely needed to say thanks again. I’m not certain the things I would’ve tried in the absence of those strategies revealed by you regarding that question. It had been a alarming difficulty in my view, nevertheless seeing your skilled strategy you dealt with the issue forced me to leap over fulfillment. I’m just happy for your guidance as well as wish you know what a powerful job you are always undertaking training others through the use of your web page. More than likely you haven’t encountered any of us.
You are my aspiration , I possess few web logs and often run out from to brand.
I’m still learning from you, but I’m trying to reach my goals. I absolutely enjoy reading all that is written on your blog.Keep the posts coming. I liked it!
great points altogether, you just won a new reader. What might you suggest about your put up that you simply made some days ago? Any sure?
Hello There. I found your blog using msn. This is a really well written article. I’ll be sure to bookmark it and come back to read more of your useful info. Thanks for the post. I’ll certainly return.
You can definitely see your skills within the paintings you write. The sector hopes for more passionate writers such as you who are not afraid to mention how they believe. At all times go after your heart. “What power has law where only money rules.” by Gaius Petronius.
Thanks for the sensible critique. Me & my neighbor were just preparing to do some research on this. We got a grab a book from our local library but I think I learned more from this post. I’m very glad to see such great info being shared freely out there.
I precisely wished to thank you very much yet again. I do not know what I could possibly have used without the ways provided by you concerning such subject. It was before the troublesome issue in my opinion, but understanding the well-written fashion you handled the issue took me to weep with gladness. I am just grateful for the information and even pray you find out what an amazing job you were putting in educating people today via your websites. Most probably you haven’t encountered all of us.
I really like your writing style, great info , regards for posting : D.
I have been browsing online more than three hours today, yet I never found any interesting article like yours. It is pretty worth enough for me. In my view, if all web owners and bloggers made good content as you did, the internet will be a lot more useful than ever before.
Very efficiently written article. It will be supportive to anybody who employess it, including myself. Keep doing what you are doing – looking forward to more posts.
You made some clear points there. I looked on the internet for the subject and found most individuals will approve with your site.
Thanks for another informative site. Where else may just I am getting that type of info written in such an ideal means? I’ve a venture that I’m simply now working on, and I have been on the look out for such information.
I like the helpful information you provide in your articles. I’ll bookmark your weblog and check again here regularly. I am quite sure I will learn many new stuff right here! Good luck for the next!
Thanks for sharing excellent informations. Your web site is very cool. I’m impressed by the details that you have on this site. It reveals how nicely you understand this subject. Bookmarked this website page, will come back for more articles. You, my friend, ROCK! I found simply the information I already searched all over the place and simply could not come across. What a perfect website.
I am very happy to read this. This is the type of manual that needs to be given and not the accidental misinformation that is at the other blogs. Appreciate your sharing this best doc.
Computer question (How long does an average person keep a computer for?
Hello.This article was really motivating, particularly since I was looking for thoughts on this topic last week.
I¡¦ll immediately clutch your rss feed as I can not in finding your email subscription hyperlink or newsletter service. Do you’ve any? Please let me recognise in order that I may subscribe. Thanks.
Hello, Neat post. There’s a problem with your website in internet explorer, could test this… IE still is the market chief and a large part of people will omit your wonderful writing due to this problem.
I loved as much as you will receive carried out right here. The sketch is tasteful, your authored material stylish. nonetheless, you command get bought an edginess over that you wish be delivering the following. unwell unquestionably come further formerly again since exactly the same nearly very often inside case you shield this increase.
I am only commenting to make you know what a helpful discovery my cousin’s princess enjoyed reading through your web page. She even learned many pieces, not to mention what it’s like to possess an incredible helping character to make other people with no trouble know precisely chosen impossible subject matter. You truly exceeded people’s expectations. Thank you for displaying these productive, healthy, revealing not to mention fun guidance on your topic to Sandra.
I like what you guys are up also. Such clever work and reporting! Carry on the superb works guys I have incorporated you guys to my blogroll. I think it will improve the value of my website 🙂
I actually wanted to write a simple note in order to thank you for those pleasant techniques you are posting at this site. My time-consuming internet investigation has finally been recognized with sensible facts and strategies to go over with my family and friends. I ‘d repeat that most of us readers are undoubtedly fortunate to dwell in a notable network with very many outstanding professionals with helpful techniques. I feel pretty happy to have seen your entire web pages and look forward to so many more fun times reading here. Thanks again for everything.
Fantastic goods from you, man. I’ve understand your stuff previous to and you are just too fantastic. I actually like what you’ve acquired here, certainly like what you’re stating and the way in which you say it. You make it entertaining and you still take care of to keep it wise. I can’t wait to read far more from you. This is really a great web site.
I have been absent for a while, but now I remember why I used to love this website. Thank you, I¡¦ll try and check back more often. How frequently you update your site?
Hey very cool web site!! Guy .. Excellent .. Wonderful .. I will bookmark your blog and take the feeds also¡KI am happy to find so many helpful information right here in the publish, we’d like work out more techniques on this regard, thanks for sharing. . . . . .
Fantastic items from you, man. I’ve consider your stuff previous to and you are just extremely fantastic. I really like what you have obtained right here, certainly like what you’re saying and the way in which through which you assert it. You make it entertaining and you continue to take care of to stay it sensible. I cant wait to learn much more from you. This is actually a great web site.
Dead composed articles, thank you for information. “He who establishes his argument by noise and command shows that his reason is weak.” by Michel de Montaigne.
Hello, i think that i saw you visited my site thus i came to “return the favor”.I’m attempting to find things to enhance my website!I suppose its ok to use a few of your ideas!!
I was recommended this website by my cousin. I’m not sure whether this post is written by him as nobody else know such detailed about my problem. You’re amazing! Thanks!
I’m still learning from you, but I’m trying to achieve my goals. I absolutely liked reading everything that is written on your site.Keep the information coming. I enjoyed it!
Hello my friend! I wish to say that this post is awesome, great written and come with almost all vital infos. I would like to see extra posts like this .
My brother recommended I might like this blog. He was totally right. This post truly made my day. You cann’t imagine simply how much time I had spent for this info! Thanks!
I like what you guys are up too. Such smart work and reporting! Keep up the superb works guys I¡¦ve incorporated you guys to my blogroll. I think it will improve the value of my website 🙂
Hi there, just became alert to your blog through Google, and found that it is truly informative. I’m going to watch out for brussels. I will be grateful if you continue this in future. Lots of people will be benefited from your writing. Cheers!
Hey there, You’ve done an excellent job. I will definitely digg it and personally suggest to my friends. I am sure they’ll be benefited from this site.
hey there and thank you for your info – I’ve definitely picked up something new from right here. I did however expertise some technical points using this site, since I experienced to reload the web site many times previous to I could get it to load correctly. I had been wondering if your web host is OK? Not that I’m complaining, but slow loading instances times will often affect your placement in google and can damage your high-quality score if advertising and marketing with Adwords. Well I’m adding this RSS to my email and can look out for much more of your respective interesting content. Make sure you update this again very soon..
I simply want to tell you that I am just new to blogging and actually liked your blog. Almost certainly I’m likely to bookmark your website . You amazingly have remarkable articles. Many thanks for revealing your website.
I have learn a few just right stuff here. Certainly worth bookmarking for revisiting. I surprise how a lot attempt you set to make any such magnificent informative web site.
hey there and thank you for your information – I’ve definitely picked up anything new from right here. I did however expertise several technical points using this site, since I experienced to reload the web site a lot of times previous to I could get it to load correctly. I had been wondering if your web hosting is OK? Not that I’m complaining, but sluggish loading instances times will sometimes affect your placement in google and could damage your quality score if ads and marketing with Adwords. Anyway I’m adding this RSS to my e-mail and could look out for a lot more of your respective interesting content. Ensure that you update this again soon..
Wow! Thank you! I constantly needed to write on my website something like that. Can I include a portion of your post to my blog?
I have been browsing online more than three hours today, yet I never found any interesting article like yours. It is pretty worth enough for me. Personally, if all site owners and bloggers made good content as you did, the net will be a lot more useful than ever before.
It’s the best time to make some plans for the future and it is time to be happy. I’ve read this post and if I could I want to suggest you few interesting things or advice. Perhaps you could write next articles referring to this article. I wish to read even more things about it!
I enjoy you because of all of the work on this website. Betty take interest in engaging in internet research and it’s really simple to grasp why. Almost all notice all relating to the powerful way you provide invaluable guidance via this web blog and even inspire response from other ones on this subject so our own child is certainly starting to learn a whole lot. Take advantage of the rest of the new year. You’re performing a first class job.
Hello.This article was really motivating, particularly since I was investigating for thoughts on this topic last Friday.
Hello, i think that i saw you visited my site thus i came to “return the favor”.I’m trying to find things to improve my website!I suppose its ok to use a few of your ideas!!
I am very happy to read this. This is the type of manual that needs to be given and not the accidental misinformation that’s at the other blogs. Appreciate your sharing this best doc.
It is in point of fact a nice and helpful piece of info. I am glad that you just shared this useful information with us. Please keep us informed like this. Thanks for sharing.
I like the valuable information you provide in your articles. I will bookmark your weblog and check again here regularly. I’m quite certain I will learn a lot of new stuff right here! Good luck for the next!
Good post and straight to the point. I don’t know if this is truly the best place to ask but do you folks have any ideea where to hire some professional writers? Thank you 🙂
I was just seeking this info for some time. After six hours of continuous Googleing, finally I got it in your web site. I wonder what is the lack of Google strategy that don’t rank this kind of informative sites in top of the list. Normally the top sites are full of garbage.
Appreciate you sharing, great article post.Much thanks again. Keep writing.
Pretty section of content. I just stumbled upon your site and in accession capital to assert that I get in fact enjoyed account your blog posts. Anyway I will be subscribing to your feeds and even I achievement you access consistently rapidly.
Thanks , I have just been searching for info about this topic for a while and yours is the best I’ve discovered till now. However, what in regards to the bottom line? Are you sure concerning the supply?
I have to express some appreciation to the writer just for rescuing me from this scenario. After looking throughout the world wide web and coming across basics which were not pleasant, I figured my entire life was gone. Being alive devoid of the approaches to the issues you have resolved as a result of your website is a crucial case, as well as the kind which may have negatively damaged my career if I had not come across your website. Your actual natural talent and kindness in touching every part was priceless. I am not sure what I would’ve done if I had not come upon such a thing like this. I can at this moment look forward to my future. Thanks very much for your professional and result oriented help. I will not think twice to propose your blog post to any person who needs to have guidelines about this problem.
I would like to express my love for your generosity supporting folks who actually need guidance on that field. Your real dedication to passing the message throughout had been extraordinarily insightful and have all the time enabled somebody like me to realize their aims. Your own insightful help and advice implies a lot a person like me and still more to my mates. With thanks; from everyone of us.
Hi there! I know this is kind of off topic but I was wondering if you knew where I could find a captcha plugin for my comment form? I’m using the same blog platform as yours and I’m having difficulty finding one? Thanks a lot!
Heya i’m for the first time here. I found this board and I find It truly useful & it helped me out much. I hope to give something back and help others like you helped me.
I would like to thnkx for the efforts you have put in writing this blog. I am hoping the same high-grade site post from you in the upcoming also. Actually your creative writing abilities has inspired me to get my own website now. Actually the blogging is spreading its wings rapidly. Your write up is a great example of it.
Hi my family member! I wish to say that this post is amazing, nice written and come with approximately all significant infos. I would like to look more posts like this.
Hello.This post was extremely fascinating, especially because I was browsing for thoughts on this matter last Friday.
I gotta bookmark this internet site it seems very beneficial very helpful
It’s ideal occasion to have some options for the long-term. I have go through this article and if I can possibly, I want to suggest you handful appealing advice.
Thanks!
Hello. excellent job. I did not anticipate this. This is a excellent story. Thanks!
Pretty section of content. I just stumbled upon your site and in accession capital to assert that I get actually enjoyed account your blog posts. Anyway I will be subscribing to your feeds and even I achievement you access consistently rapidly.
Well I truly enjoyed studying it. This tip provided by you is very helpful for proper planning.
Some truly superb info , Glad I discovered this. “Our pleasures were simple-they included survival.” by Dwight D Eisenhower.
Thanks for another magnificent post. Where else could anyone get that type of information in such an ideal way of writing? I’ve a presentation next week, and I am on the look for such information.
You can definitely see your skills in the work you write. The world hopes for more passionate writers like you who aren’t afraid to say how they believe. Always follow your heart.
I do not even know how I ended up here, but I thought this post was great. I do not know who you are but certainly you’re going to a famous blogger if you are not already 😉 Cheers!
Attractive section of content. I just stumbled upon your web site and in accession capital to assert that I acquire in fact enjoyed account your blog posts. Anyway I will be subscribing to your augment and even I achievement you access consistently quickly.
fantastic issues altogether, you just won a new reader. What would you recommend about your publish that you made a few days in the past? Any sure?
Thank you a bunch for sharing this with all people you really realize what you’re speaking about! Bookmarked. Please also consult with my site =). We may have a hyperlink trade contract among us!
I just wanted to construct a quick note in order to say thanks to you for all of the fabulous suggestions you are posting at this website. My time intensive internet lookup has now been rewarded with reputable facts to share with my family and friends. I would claim that many of us website visitors actually are rather fortunate to dwell in a good community with so many brilliant professionals with insightful ideas. I feel rather grateful to have encountered your entire web pages and look forward to tons of more awesome times reading here. Thanks once again for all the details.
Thank you for the auspicious writeup. It in truth was a entertainment account it. Glance complex to far added agreeable from you! However, how can we keep up a correspondence?
HelloHi there, just became aware ofalert to your blog through Google, and found that it isit’s reallytruly informative. I’mI am gonnagoing to watch out for brussels. I willI’ll appreciatebe grateful if you continue this in future. A lot ofLots ofManyNumerous people will be benefited from your writing. Cheers!
Thanks for this!
whoah this weblog is magnificent i really like studying your posts. Keep up the great work! You know, a lot of individuals are hunting round for this info, you could aid them greatly.
I do consider all of the ideas you have offered in your post. They are very convincing and can certainly work. Still, the posts are too quick for novices. May just you please extend them a little from next time? Thanks for the post.
Thanks for your post. I’d like to write my opinion that the price of car insurance differs from one coverage to another, simply because there are so many different facets which contribute to the overall cost. As an example, the make and model of the auto will have a significant bearing on the price tag. A reliable ancient family auto will have a more affordable premium than the usual flashy sports vehicle.
Hello my friend! I want to say that this post is amazing, nice written and include approximately all vital infos. I’d like to see more posts like this.
Thank you for another magnificent article. Where else could anybody get that kind of info in such an ideal way of writing? I’ve a presentation next week, and I am on the look for such info.
I am continually searching online for posts that can help me. Thx!
Hiya, I’m really glad I’ve found this info. Nowadays bloggers publish just about gossips and net and this is really frustrating. A good blog with exciting content, that is what I need. Thanks for keeping this website, I’ll be visiting it. Do you do newsletters? Cant find it.
Lovely website! I am loving it!! Will be back later to read some more. I am bookmarking your feeds also
I wanted to write you one little remark just to say thank you over again for the lovely opinions you have documented at this time. It has been simply surprisingly open-handed of you to grant easily exactly what a number of people would’ve supplied for an e book to end up making some profit on their own, mostly given that you could possibly have tried it in case you decided. Those ideas also worked to become great way to realize that most people have a similar eagerness much like my very own to know more and more with reference to this matter. I know there are many more fun opportunities up front for individuals who read carefully your website.
You’reYou are so coolawesomeinteresting! I don’tI do not supposethinkbelieve I’veI haveI’ve truly readread through anythingsomethinga single thing like thislike that before. So nicegoodgreatwonderful to findto discover somebodysomeoneanother person with somewith a fewwith originaluniquegenuine thoughts on this subjecttopicissuesubject matter. ReallySeriously.. thank you forthanks formany thanks for starting this up. This websiteThis siteThis web site is somethingis one thing that is neededthat’s neededthat is required on the webon the internet, someone with a littlewith somewith a bit of originality!
Just wanna admit that this is invaluable , Thanks for taking your time to write this.
Some genuinely nice and utilitarian info on this site, besides I conceive the design contains excellent features.
I do trust all the concepts you’ve offered in your post. They are very convincing and can definitely work. Still, the posts are too short for novices. May just you please extend them a little from next time? Thanks for the post.
I like the efforts you have put in this, appreciate it for all the great blog posts.
I like this site so much, bookmarked. “American soldiers must be turned into lambs and eating them is tolerated.” by Muammar Qaddafi.
I wanted to put you that little bit of remark to be able to give many thanks over again on the extraordinary tactics you’ve documented on this site. It was really unbelievably generous of you to grant publicly what a number of us could possibly have distributed as an electronic book to earn some dough for their own end, most notably considering the fact that you might well have tried it if you considered necessary. These creative ideas likewise served to provide a good way to fully grasp that most people have similar zeal like my personal own to realize very much more concerning this problem. I know there are lots of more fun opportunities up front for individuals who read through your blog post.
There is clearly a bundle to know about this. I assume you made some good points in features also.
Excellent post. I was checking continuously this blog and I’m impressed! Extremely useful info specially the last part 🙂 I care for such info a lot. I was seeking this certain info for a long time. Thank you and good luck.
I precisely had to appreciate you again. I’m not certain the things that I would have accomplished in the absence of the actual creative concepts documented by you regarding my question. It previously was a real depressing scenario for me, nevertheless spending time with a well-written style you managed the issue took me to cry over gladness. I will be grateful for your assistance and expect you realize what a powerful job you were putting in instructing the mediocre ones by way of your webpage. Most likely you haven’t got to know any of us.
you’re really a excellent webmaster. The web site loading pace is amazing. It seems that you’re doing any distinctive trick. Furthermore, The contents are masterpiece. you’ve done a magnificent process in this subject!
excellent issues altogether, you just won a new reader. What would you suggest about your publish that you just made a few days ago? Any sure?
I have been absent for some time, but now I remember why I used to love this site. Thanks, I will try and check back more frequently. How frequently you update your website?
Excellent website. A lot of helpful info here. I’m sending it to several friends ans additionally sharing in delicious. And of course, thank you to your effort!
It is really a great and useful piece of info. I’m glad that you simply shared this helpful info with us. Please stay us up to date like this. Thank you for sharing.
Rattling good info can be found on web site. “The fundamental defect of fathers is that they want their children to be a credit to them.” by Bertrand Russell.
Fantastic beat ! I wish to apprentice while you amend your site, how can i subscribe for a blog site? The account helped me a acceptable deal. I had been a little bit acquainted of this your broadcast offered bright clear concept
A lot of thanks for all of your effort on this web page. My mom takes pleasure in conducting investigation and it is easy to see why. A lot of people know all about the dynamic tactic you render priceless steps via the web site and as well as boost response from some other people on that idea then our favorite simple princess is actually learning a lot. Take advantage of the rest of the new year. You are always performing a pretty cool job.
Very interesting info!Perfect just what I was searching for!
I have been browsing online more than 3 hours today, yet I never found any interesting article like yours. It is pretty worth enough for me. Personally, if all web owners and bloggers made good content as you did, the web will be much more useful than ever before.
This site was… how do I say it? Relevant!! Finally I’ve found something which helped me. Thanks a lot!
Its superb as your other blog posts : D, regards for putting up. “In the spider-web of facts, many a truth is strangled.” by Paul Eldridge.
Great website! I am loving it!! Will come back again. I am taking your feeds also
I dugg some of you post as I cerebrated they were very helpful extremely helpful
F*ckin’ awesome things here. I’m very happy to peer your post. Thank you a lot and i am having a look ahead to touch you. Will you kindly drop me a mail?
Hello There. I found your blog using msn. This is an extremely well written article. I will make sure to bookmark it and come back to read more of your useful information. Thanks for the post. I’ll definitely comeback.
I loved up to you will receive performed proper here. The comic strip is attractive, your authored material stylish. however, you command get got an edginess over that you would like be handing over the following. unwell no doubt come further previously once more since exactly the same nearly very steadily inside of case you defend this increase.
Hi, Neat post. There is a problem together with your web site in internet explorer, would test this¡K IE nonetheless is the marketplace leader and a large element of people will miss your fantastic writing because of this problem.
Thank you for sharing excellent informations. Your site is very cool. I am impressed by the details that you have on this blog. It reveals how nicely you understand this subject. Bookmarked this website page, will come back for more articles. You, my friend, ROCK! I found simply the info I already searched all over the place and just couldn’t come across. What an ideal web-site.
Great blog post. Fantastic.
I must thank you for the efforts you’ve put in penning this site. I really hope to view the same high-grade blog posts from you later on as well. In truth, your creative writing abilities has encouraged me to get my own site now 😉
I like the efforts you have put in this, regards for all the great posts.
I regard something truly interesting about your weblog so I bookmarked .
Regards for helping out, superb information.
Just wanna tell that this is invaluable , Thanks for taking your time to write this.
Great web site. A lot of useful info here. I am sending it to some buddies ans additionally sharing in delicious. And naturally, thanks on your effort!
I and my pals were found to be digesting the good thoughts found on your website and so instantly I had a horrible suspicion I had not expressed respect to the web blog owner for those strategies. The boys are already as a result excited to study all of them and have truly been using them. I appreciate you for genuinely very accommodating and for figuring out varieties of important areas millions of individuals are really wanting to be informed on. Our own honest regret for not expressing appreciation to you earlier.
Fantastic goods from you, man. I’ve understand your stuff previous to and you are just extremely magnificent. I actually like what you have acquired here, really like what you’re stating and the way in which you say it. You make it entertaining and you still take care of to keep it smart. I cant wait to read much more from you. This is really a tremendous site.
F*ckin’ remarkable issues here. I am very happy to see your post. Thank you so much and i’m taking a look forward to contact you. Will you kindly drop me a e-mail?
Excellent post. I was checking continuously this blog and I am impressed! Extremely helpful information particularly the last part 🙂 I care for such info a lot. I was looking for this particular information for a very long time. Thank you and good luck.
You are my intake, I have few web logs and often run out from post :). “Actions lie louder than words.” by Carolyn Wells.
I really appreciate this post. I have been looking all over for this! Thank goodness I found it on Bing. You have made my day! Thx again
I think you have remarked some very interesting details , thanks for the post.
I savour, cause I found exactly what I was having a look for. You’ve ended my four day long hunt! God Bless you man. Have a nice day. Bye
you are in reality a good webmaster. The website loading velocity is incredible. It kind of feels that you are doing any unique trick. Also, The contents are masterpiece. you’ve performed a fantastic process in this subject!
It is in reality a great and useful piece of information. I¡¦m glad that you just shared this useful info with us. Please stay us informed like this. Thanks for sharing.
I enjoy the efforts you have put in this, appreciate it for all the great content.
I think other site proprietors should take this web site as an model, very clean and wonderful user genial style and design, as well as the content. You are an expert in this topic!
Attractive section of content. I just stumbled upon your site and in accession capital to assert that I acquire in fact enjoyed account your blog posts. Any way I will be subscribing to your augment and even I achievement you access consistently quickly.
Thanks, I’ve just been searching for information approximately this subject for a long time and yours is the best I have discovered so far. But, what concerning the conclusion? Are you certain concerning the source?
Hello, Neat post. There is an issue along with your site in web explorer, may check this… IE still is the marketplace leader and a good portion of folks will omit your magnificent writing because of this problem.
hello!,I like your writing so a lot! share we communicate more approximately your post on AOL? I require a specialist on this area to solve my problem. May be that’s you! Looking forward to peer you.
I like what you guys are up too. Such clever work and reporting! Carry on the superb works guys I have incorporated you guys to my blogroll. I think it will improve the value of my website :).
Very well written information. It will be useful to anybody who employess it, including myself. Keep doing what you are doing – can’r wait to read more posts.
I don’t know whether it’s just me or if perhaps everyone else experiencing problems with your blog. It seems like some of the text on your content are running off the screen. Can someone else please provide feedback and let me know if this is happening to them too? This could be a issue with my web browser because I’ve had this happen before. Many thanks
Hello.This article was really motivating, especially because I was browsing for thoughts on this topic last Friday.
Great post. I was checking continuously this blog and I’m impressed! Very useful info specifically the last part 🙂 I care for such information much. I was looking for this certain info for a long time. Thank you and best of luck.
A person necessarily help to make seriously posts I’d state. This is the very first time I frequented your website page and up to now? I amazed with the research you made to create this actual put up amazing. Magnificent task!
I was suggested this web site by my cousin. I’m not sure whether this post is written by him as no one else know such detailed about my difficulty. You’re amazing! Thanks!
Some truly great information, Sword lily I noticed this. “Men in no way approach so nearly to the gods as in doing good to men.” by Marcus Tullius Cicero.
I truly enjoy looking at on this site, it has got wonderful content . “He who sees the truth, let him proclaim it, without asking who is for it or who is against it.” by Henry George.
magnificent issues altogether, you just gained a emblem new reader. What might you suggest in regards to your put up that you made some days in the past? Any positive?
Wonderful paintings! That is the type of info that are meant to be shared around the web. Shame on Google for not positioning this post higher! Come on over and talk over with my web site . Thank you =)
Definitely, what a splendid website and informative posts, I surely will bookmark your site.All the Best!
I think other site proprietors should take this website as an model, very clean and excellent user genial style and design, as well as the content. You’re an expert in this topic!
I will right away grab your rss feed as I can not in finding your email subscription link or newsletter service. Do you have any? Kindly allow me know in order that I may subscribe. Thanks.
I’ve learn a few good stuff here. Definitely price bookmarking for revisiting. I wonder how so much attempt you set to make any such magnificent informative website.
Generally I don’t learn article on blogs, however I wish to say that this write-up very pressured me to check out and do so! Your writing style has been surprised me. Thank you, quite nice article.
Hey I fairly loved reading through your web . The content material were being very educational. Thank yourself therefore a great deal!
Wow, marvelous blog layout! How long have you been blogging for? you made blogging look easy. The overall look of your site is great, as well as the content!
Some genuinely good info , Glad I noticed this. “Genuine goodness is threatening to those at the opposite end of the moral spectrum.” by Charles Spencer.
I dugg some of you post as I thought they were very helpful extremely helpful
You have observed very interesting details! ps nice web site.
Regards for helping out, superb info .
I’ve been absent for a while, but now I remember why I used to love this blog. Thank you, I’ll try and check back more frequently. How frequently you update your website?
You actually make it seem so easy together with your presentation but I in finding this topic to be actually one thing that I think I’d never understand. It seems too complex and very vast for me. I’m taking a look forward in your subsequent publish, I will attempt to get the dangle of it!
Wow! This could be one particular of the most beneficial blogs We have ever arrive across on this subject. Actually Great. I’m also an expert in this topic so I can understand your hard work.
Thanks for the ideas you write about through this website. In addition, many young women who seem to become pregnant do not even try and get medical health insurance because they are concerned they couldn’t qualify. Although some states now require that insurers provide coverage despite the pre-existing conditions. Rates on most of these guaranteed programs are usually higher, but when taking into consideration the high cost of medical care it may be a new safer approach to take to protect a person’s financial future.
WONDERFUL Post.thanks for share..more wait .. …
I value the blog post.Much thanks again.
hello there and thank you for your info – I have certainly picked up something new from right here. I did however expertise a few technical issues using this website, as I experienced to reload the web site a lot of times previous to I could get it to load correctly. I had been wondering if your web hosting is OK? Not that I’m complaining, but slow loading instances times will very frequently affect your placement in google and can damage your high quality score if ads and marketing with Adwords. Well I am adding this RSS to my email and can look out for much more of your respective interesting content. Ensure that you update this again very soon..
Needed to put you this little bit of word to thank you so much the moment again for those amazing strategies you have provided above. It’s tremendously open-handed with people like you to deliver openly precisely what some people could possibly have sold as an electronic book to earn some money on their own, particularly now that you could have tried it if you wanted. These things additionally acted to be the good way to fully grasp that someone else have the same eagerness really like my very own to understand good deal more with regards to this matter. I think there are thousands of more fun sessions up front for folks who scan through your website.
Heya i’m for the first time here. I found this board and I find It truly useful & it helped me out much. I hope to give something back and help others like you helped me.
Hi there, You have done an excellent job. I’ll certainly digg it and personally suggest to my friends. I’m confident they will be benefited from this site.
It’s actually a cool and useful piece of info. I’m glad that you shared this helpful info with us. Please keep us informed like this. Thanks for sharing.
Normally I don’t learn article on blogs, but I would like to say that this write-up very forced me to try and do it! Your writing style has been surprised me. Thanks, quite nice post.
Hey there! Quick question that’s totally off topic. Do you know how to make your site mobile friendly? My site looks weird when browsing from my iphone. I’m trying to find a template or plugin that might be able to fix this issue. If you have any recommendations, please share. Thank you!
Hey! I know this is kinda off topic however , I’d figured I’d ask. Would you be interested in exchanging links or maybe guest writing a blog article or vice-versa? My blog goes over a lot of the same topics as yours and I feel we could greatly benefit from each other. If you might be interested feel free to send me an e-mail. I look forward to hearing from you! Great blog by the way!
I delight in, cause I found just what I used to be looking for. You’ve ended my four day lengthy hunt! God Bless you man. Have a great day. Bye
Wonderful blog! I found it while searching on Yahoo News. Do you have any tips on how to get listed in Yahoo News? I’ve been trying for a while but I never seem to get there! Appreciate it
Merely wanna input on few general things, The website pattern is perfect, the articles is really excellent. “The way you treat yourself sets the standard for others.” by Sonya Friedman.
I know this if off topic but I’m looking into starting my own blog and was curious what all is required to get set up? I’m assuming having a blog like yours would cost a pretty penny? I’m not very web smart so I’m not 100 sure. Any suggestions or advice would be greatly appreciated. Thank you
There are definitely plenty of details like that to take into consideration. That is a great point to deliver up. I provide the ideas above as common inspiration but clearly there are questions just like the one you bring up where crucial factor will be working in sincere good faith. I don?t know if finest practices have emerged around things like that, but I am sure that your job is clearly recognized as a fair game. Both girls and boys feel the impression of just a second’s pleasure, for the remainder of their lives.
Do you have a spam issue on this blog; I also am a blogger, and I was wanting to know your situation; many of us have developed some nice methods and we are looking to trade methods with other folks, please shoot me an e-mail if interested.
One thing I want to say is car insurance canceling is a feared experience and if you are doing the suitable things like a driver you’ll not get one. Lots of people do receive the notice that they’ve been officially dropped by their own insurance company they have to struggle to get additional insurance after the cancellation. Low cost auto insurance rates are generally hard to get after the cancellation. Having the main reasons concerning the auto insurance cancelling can help individuals prevent burning off one of the most essential privileges obtainable. Thanks for the concepts shared by your blog.
I’m not that much of a internet reader to be honest but your blogs really nice, keep it up! I’ll go ahead and bookmark your site to come back later on. All the best
Y’all obiously under no circumstances been in the direction of Buc ee’s!! Buc ee’s is definitely THE great!!
I am not sure where you’re getting your info, but good topic. I needs to spend some time learning much more or understanding more. Thanks for magnificent info I was looking for this information for my mission.
Thank you for the sensible critique. Me & my neighbor were just preparing to do a little research about this. We got a grab a book from our local library but I think I learned more from this post. I am very glad to see such great information being shared freely out there.
Very nice post. I just stumbled upon your weblog and wanted to say that I have really enjoyed browsing your blog posts. After all I will be subscribing to your feed and I hope you write again very soon!
Im grateful for the article.Much thanks again.
My brother recommended I might like this web site. He was totally right. This post truly made my day. You cann’t imagine simply how much time I had spent for this information! Thanks!
Hiya, I’m really glad I have found this information. Nowadays bloggers publish only about gossips and net and this is really annoying. A good web site with interesting content, this is what I need. Thank you for keeping this site, I will be visiting it. Do you do newsletters? Cant find it.
Some truly wonderful work on behalf of the owner of this web site , perfectly great content .
Great work! This is the kind of information that are meant to be shared around the internet. Disgrace on Google for no longer positioning this put up higher! Come on over and seek advice from my web site . Thank you =)
Wow! Thank you! I constantly wanted to write on my blog something like that. Can I implement a fragment of your post to my site?
Good read, enjoyed it!
Pretty nice post. I just stumbled upon your blog and wanted to say that I have really enjoyed browsing your blog posts. In any case I’ll be subscribing to your feed and I hope you write again soon
I loved as much as you will receive carried out right here. The sketch is attractive, your authored subject matter stylish. nonetheless, you command get bought an impatience over that you wish be delivering the following. unwell unquestionably come further formerly again as exactly the same nearly a lot often inside case you shield this increase.
Say, you got a nice blog post.Really thank you! Want more.
Thumb up for this post.
I like what you guys are up too. Such intelligent work and reporting! Keep up the superb works guys I have incorporated you guys to my blogroll. I think it’ll improve the value of my site 🙂
Very well written article. It will be supportive to anyone who usess it, including yours truly :). Keep up the good work – can’r wait to read more posts.
Its like you read my mind! You appear to know a lot about this, like you wrote the book in it or something. I think that you can do with some pics to drive the message home a bit, but other than that, this is great blog. A great read. I will definitely be back.
Great post. I was checking constantly this blog and I am impressed! Very helpful information specifically the last part 🙂 I care for such information much. I was looking for this certain information for a very long time. Thank you and good luck.
I will right away snatch your rss feed as I can not find your e-mail subscription hyperlink or e-newsletter service. Do you have any? Kindly let me recognise so that I could subscribe. Thanks.
A round of applause for your blog.Thanks Again. Much obliged.
I have not checked in here for some time since I thought it was getting boring, but the last few posts are good quality so I guess I¡¦ll add you back to my daily bloglist. You deserve it my friend 🙂
I loved as much as you will receive carried out right here. The sketch is attractive, your authored material stylish. nonetheless, you command get bought an edginess over that you wish be delivering the following. unwell unquestionably come more formerly again since exactly the same nearly very often inside case you shield this increase.
Hello, there. I know this is off-topic, but I was wondering which blog platform are you using for this site? I’m getting fed up of WordPress because I’ve had problems with hackers and I’m looking at options for another platform. I would be fantastic if you could point me in the direction of a good platform
Great post.Much thanks again. Want more.
Keep functioning ,splendid job!
I as well as my buddies came going through the best solutions on the blog then all of a sudden got an awful feeling I had not expressed respect to the website owner for those techniques. Those young boys happened to be as a result warmed to read through all of them and now have honestly been having fun with them. I appreciate you for actually being well kind as well as for deciding upon some excellent themes millions of individuals are really eager to discover. Our sincere apologies for not expressing gratitude to sooner.
I truly appreciate this post. I¡¦ve been looking everywhere for this! Thank goodness I found it on Bing. You’ve made my day! Thanks again
It¡¦s in reality a nice and helpful piece of info. I¡¦m satisfied that you shared this helpful info with us. Please stay us up to date like this. Thank you for sharing.
Major thankies for the article.Much thanks again.
Thanks so much for the blog.Really looking forward to read more. Fantastic.
I found your blog website on google and verify a few of your early posts. Continue to maintain up the superb operate. I simply further up your RSS feed to my MSN News Reader. Searching for forward to studying extra from you later on!…
Wow! Thank you! I continually wanted to write on my website something like that. Can I implement a fragment of your post to my blog?
I’ve been exploring for a bit for any high-quality articles or weblog posts on this sort of house . Exploring in Yahoo I eventually stumbled upon this site. Reading this info So i am satisfied to show that I’ve a very good uncanny feeling I discovered just what I needed. I such a lot unquestionably will make sure to don’t fail to remember this site and give it a look on a constant basis.
Major thankies for the blog article.Thanks Again. Really Cool.
Thanks a bunch for sharing this with all of us you actually know what you are talking about! Bookmarked. Please also visit my web site =). We could have a link exchange arrangement between us!
I¡¦ll immediately grasp your rss feed as I can not to find your email subscription hyperlink or e-newsletter service. Do you have any? Kindly allow me recognise in order that I may subscribe. Thanks.
I was suggested this website by my cousin. I am not sure whether this post is written by him as no one else know such detailed about my trouble. You are wonderful! Thanks!
I’m extremely impressed with your writing skills as well as with the layout on your weblog. Is this a paid theme or did you customize it yourself? Either way keep up the excellent quality writing, it’s rare to see a nice blog like this one nowadays..
I appreciate you sharing this article post. Great.
hi!,I really like your writing very a lot! share we keep up a correspondence extra about your post on AOL? I require a specialist on this space to unravel my problem. May be that’s you! Having a look forward to peer you.
Very neat blog.Much thanks again. Great.
I like the helpful information you provide in your articles. I will bookmark your blog and check again here frequently. I am quite sure I will learn a lot of new stuff right here! Best of luck for the next!
I not to mention my guys were actually following the great recommendations found on your web site and instantly I had a terrible feeling I had not expressed respect to the web blog owner for those secrets. Most of the people were absolutely passionate to study them and have undoubtedly been using those things. I appreciate you for truly being considerably kind and then for deciding upon such incredibly good topics most people are really wanting to learn about. My sincere regret for not saying thanks to sooner.
Appreciating the persistence you put into your blog and detailed information you provide.
Thanks for the sensible critique. Me and my neighbor were just preparing to do some research about this. We got a grab a book from our local library but I think I learned more from this post. I am very glad to see such great information being shared freely out there.
I loved your article.Really thank you! Great.
A round of applause for your blog post.Thanks Again. Want more.
Hey there! I know this is kind of off-topic, but I’d figured I’d ask. Would you be interested in exchanging links or maybe guest authoring a blog post or vice-versa? My blog goes over a lot of the same topics as yours, and I believe we could greatly benefit from each other. If you happen to be interested, feel free to shoot me an e-mail. I look forward to hearing from you! Great blog by the way!
I simply want to mention I am just all new to weblog and certainly enjoyed your web page. Likely I’m likely to bookmark your site . You surely have good stories. Thanks for sharing your webpage.
Say, you got a nice post.Thanks Again. Will read on…
Does your website have a contact page? I’m having a tough time
locating it but, I’d like to shoot you an email. I’ve got some
recommendations for your blog you might be interested in hearing.
Either way, great blog and I look forward to seeing it grow over time.
I really like and appreciate your post. Will read on…
B2B2B2
Hi pals, enjoyable paragraph as well as great prompting commented listed below, I am actually actually delighting in by these.
HelloHey thereHeyGood dayHowdyHi thereHello thereHi! Do you know if they make any plugins to protectsafeguard against hackers? I’m kinda paranoid about losing everything I’ve worked hard on. Any suggestionsrecommendationstips?
Those are yours alright! . We at least need to get these people stealing images to start blogging! They probably just did a image search and grabbed them. They look good though!
My brother suggestedrecommended I might like this blogwebsiteweb site. He was totallyentirely right. This post actuallytruly made my day. You cann’tcan not imagine justsimply how much time I had spent for this informationinfo! Thanks!
Thanks for the post, keep sharing more articles with us
Ꮋello there, ϳust changd into aware of yоur blog via Goߋgle, and ⅼocated tһat it іѕ truly informativе.I’m going to watch out for brussels. I willappreciate should you continue this in future. Lots of folks will bbe benefited oout oоfyour wгiting. Cheers!
I simply want to mention I am just beginner to blogging and absolutely liked this web page. Probably I’m planning to bookmark your blog . You really have superb writings. Thanks for revealing your web-site.
I love the efforts you have put in this, thanks for all the great posts.
Love to read it,Waiting For More new Update and I Already Read your Recent Post its Great Thanks.
It’sIt isIts not my first time to visitgo to seepay a visitpay a quick visit this websiteweb sitesiteweb page, i am visitingbrowsing this websiteweb sitesiteweb page dailly and takegetobtain nicepleasantgoodfastidious datainformationfacts from here everydaydailyevery dayall the time.
Greetings! Very helpfulVery useful advice within thisin this particular articlepost! It is theIt’s the little changes that makewhich will makethat producethat will make the biggestthe largestthe greatestthe most importantthe most significant changes. Thanks a lotThanksMany thanks for sharing!
Hmm, it seems like your site ate my first comment (it had been really long) so I figure I will just sum it up what I’d composed and say, I am thoroughly enjoying your site. I am an aspiring blog author, but I am still new to the entire thing. Do you have some recommendations for newbie blog writers? I’d appreciate it. {
Your valuable important points imply much a man like me and more to my workplace workers. With thanks; from everybody of us.
I’d love to be a part of team where I could get information from other experienced people that share the exact same interest. If you have any recommendations, please allow me to know. Thank you.
Greetings. I know this is somewhat off-topic, but I was wondering if you knew where I could get a captcha plugin for my own comment form? I’m using the exact same blog platform such as yours, and I’m having trouble locating one? Thanks a lot. {
Wonderful paintings! That is the kind of information that should be shared around the net. Shame on Google for now not positioning this post higher! Come on over and seek advice from my web site . Thanks =)
Hello! This is my first visit to your site! We are a group of volunteers and beginning a brand new initiative in a neighborhood at the exact same niche. Your site supplied us helpful information to work on. You have done an outstanding job. {
I think that thanks for the valuabe information and insights you have so provided here.
that’s why I bookmarked this page for get news feed with perfectly information in the next coming post ,