Preface
We heard that the new age transformation is coming. As a result it transform the traditional military weapons to electronic codes. The computer technologies such as DDOS (Distributed denial of services), malware and virus similar a killer. It can disrupt the financial activities, daily network communication and health care services. An idea bring to our attention on world war II history was that classic military power result destroyed everything (mankind and properties). But re-built the society and operation after war. It is a harsh and difficult mission! From technical point of view, the victorious might stand on ethics view point to assists defeated side to rebuild the business and economic system. As a matter of fact, the distruction level of war created by military weapon especially missile it is hard to evaluation. And this is the reason let’s cyber warfare appears in coming future! But it started already!
Analytic result on technical articles about cyber warfare
In regards to my study on technical article issued by CSS Eth Zurich (The Center for Security Studies (CSS) at ETH Zurich).The analytic result highlights serveral key factors of Cyber warfare . Cyber warfare was cheaper than traditional military force. It provides a “cleaner” (with less or no bloodshed) suitation. No doubt that less risky for an attacker than other forms of armed conflict. The analytic result defines 5 different types of cyber conflict during their study. They are Cyber War, Cyber Terrorism, Cyber Espionage, internet crime and cyber vandalism.
The specific feature of cyber weapon (in between country to country)
I was sometimes confused with the headline news on prediction on cyber technology war. The questions on my mind is that how electronic weapon or cyber weapon replacing traditional military facilities? Think it over, the appropriate technique might adopted target into the following criteria (see below):
The capabilities of cyber attack techniques ( A transformation of traditional military force)
| Type | Attack technology | Functional feature – objective | Target – Environment | Remark: |
| Cyber Vandalism, Cyber War | IOT & BOTNET (DDOS technique) | Services suspension – electronic communication services (IP-Telephony) | Bank, Fund House , Stock Exchange | |
| Cyber Espionage | Malware | Information gathering | Bank, Fund House, Stock Exchange & government sector | |
| Cyber War, Cyber Vandalism | Ransomware | Services suspension important facility fucntion | nuclear facility , Airlines,TV broadcast station, Radio broadcast station & military facility | Ransomware feature contained facility to supspend the computer services. Besides it capable listen to the instruction of C&C server. On the other hand, the attacker can resume the services once they win the battle. |
| Traditional military force | Bomb | Services Suspension on important facility function and destroy permanently | nuclear facility, military facility, power station, airport & communiation facility (Digital phone system) | |
| Internet Crime, Cyber war | Email phishing and Scam email message | Carry out psychological warfare, implant malware activities in order to fulfill their objective | nuclear facility, military facility, power station, |
Let us dig out one of the attack technique to see how the cyber technology feature fulfill the goal of the cyber warfare features .
Do you think Ransomware is founded by military department?
The first ransomware appear in the world on 1989. A biologist Joseph L. Popp sent 20,000 infected diskettes labeled
“AIDS Information – Introductory Diskettes” to attendees of the World Health Organization’s international AIDS conference.
But after 90 reboots, the Trojan hid directories and encrypted the names of the files on the customer’s computer.
To regain access, the user would have to send $189 to PC Cyborg Corp. at a post office box in Panama.
In 2006, former President George W. Bush was increasingly worried about Iranian efforts at enriching uranium, and ultimately, its hopes to build an atomic bomb. The goal of Stuxnet is going to destroy Iraq nuclear facilities driven by US government. The rumors were told Stuxnet malware destroyed roughly one-fifth of Iran’s centrifuges in 2009.
An unconfirmed information stated that there is a separate operation called Nitro Zeus, which gave the US access into Iran’s air defense systems so it could not shoot down planes, its command-and-control systems so communications would go dead, and infrastructure like the power grid, transportation, and financial systems.
Speculation:
WannaCry infection using EternalBlue, an exploit of Windows’ Server Message Block (SMB) protocol. The U.S. National Security Agency (NSA) had discovered the vulnerability in the past, but used it to create an exploit for its own offensive work, rather than report it to Microsoft. As we know nuclear power facilities control system OS platform relies on Microsoft OS system (see below articles). It may causes people think is there any secret action hide by NSA (National Security Agency). He aroused my interest in questioning who is the key figure to spread WannCry ransome? It looks that there is similarity with Stuxnet worm infection in 2009. Since we all fool by NSA at that time let your computer workstation transform to a cyber army then attack USA enemy. Do you think wanncry is the rehearsal of test or pilot run?
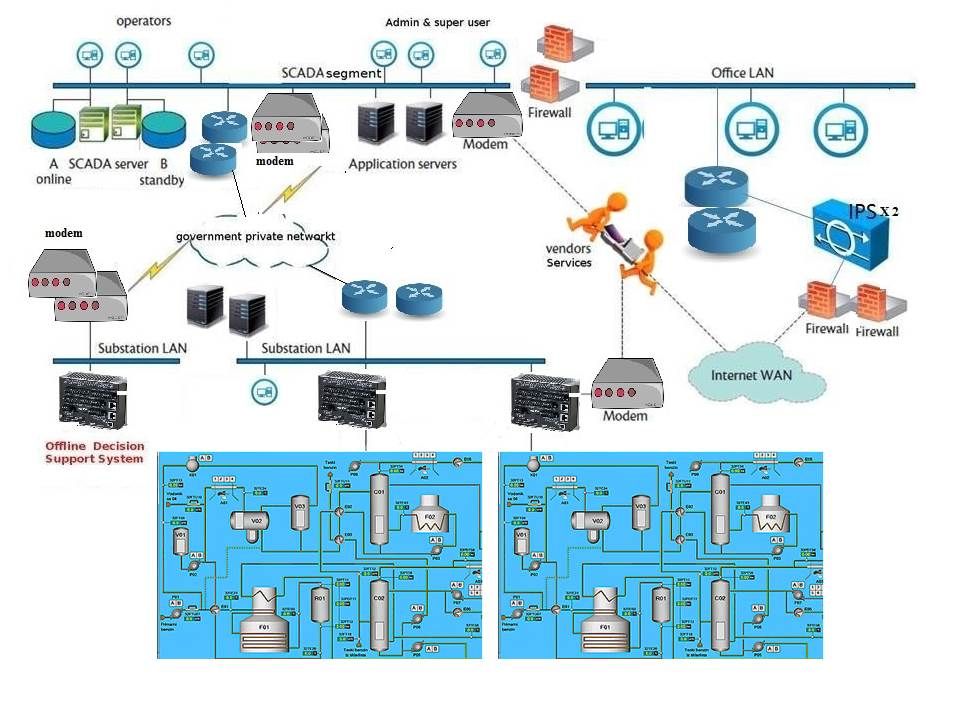
Below diagram is my imagination of the modern nuclear facility environment. The SCADA system pay a key role in nuclear power facility. Ransomeware have capabilities to suspend the services of this facilities. It doesn’t need to destroy anything but the services will be totally shut it down the services. We have seen the real example in UK health care services as a reference. I will stop written here. Should you have any queries, I will try my best to written more in future.
Supplement – The other side of the story on cyber attack (Electronic war between countries) – 13th June 2017
As said on above discussion topic, since it looks not interest to visitors on reflection of comments on feedback. However there is something on my mind need to share.
North Korea President Kim’s intention show to the world of his governance power. He is in frequent to demonstrate his military power cause US government concerns his equalize of military power in the world. To be honest, it is hard to equal the military and economics power as of today. For instance China nearly become the 1st business economic leader. We all know United state is the leader in this moment. However their economic operation chain should have difficulties to do the 2nd round of transformation. Because some of their capital business and business economy contained made in China element. Since North Korea on finance and business economy are weak. President Kim did such things seems not make sense. I did not visit North Korea however a lot of news on TV might speculate their current situation. I strongly believed that their nuclear facility might operation in 60’s fashion. The SCADA system not possibly supply by Siemens. But learn and develop a windows based SCADA system not difficult. From information point of view, North Korea nuclear facilities might relies on window for Control Systems instead of Linux for control system. And therefore Ransomware type attack can specifics shot the target. Meanwhile the business industry from North Korea all work with Microsoft OS in daily life.
Below are the hints how to eliminate the risks issued by SCADA system vendor. Any interest?
Process control vendors require:
1. A system with a minimal attack surface, so that biweekly or monthly patches are not required
2. A consistent programming interface that will not change every four to five years, requiring a complete rewrite of their software
3. An environment that can be quickly and safely “locked down” to reduce the risk from hacking
4. A system with limited network access, only through specific ports to reduce the risk of network based attacks
5. Support for priority-based multi-tasking, preferably a real-time operating system (RTOS) that supports hard real-time requirements
6. A robust ecosystem of utilities and tools to make development, installation, debugging, and maintenance as easy as it is on consumer systems.
End of this topic
Well said, 100 agree.
Keep working ,fantastic job!
Hi my friend! I wish to say that this article is awesome, great written and come with almost all important infos. I¡¦d like to peer more posts like this .
Having read this I believed it was very informative. I appreciate you finding the time and energy to put this content together. I once again find myself spending a lot of time both reading and commenting. But so what, it was still worth it!
magnificent issues altogether, you just gained a emblem new reader. What may you recommend about your publish that you made some days ago? Any certain?
I like what you guys are up too. Such intelligent work and reporting! Carry on the superb works guys I have incorporated you guys to my blogroll. I think it’ll improve the value of my website 🙂
As I web site possessor I believe the content matter here is rattling fantastic , appreciate it for your hard work. You should keep it up forever! Good Luck.
You are my inspiration , I possess few web logs and often run out from to post .I conceive this web site has got some rattling great info for everyone. “The foundation of every state is the education of its youth.” by Diogenes.
Generally I do not learn article on blogs, however I wish to say that this write-up very pressured me to check out and do it! Your writing taste has been amazed me. Thanks, very nice post.
I have read a few excellent stuff here. Certainly value bookmarking for revisiting. I wonder how much effort you set to create this type of wonderful informative site.
I went over this internet site and I think you have a lot of fantastic info, bookmarked (:.
Whats Happening i am new to this, I stumbled upon this I’ve discovered It absolutely useful and it has aided me out loads. I hope to give a contribution & aid different customers like its helped me. Great job.
I reckon something genuinely interesting about your web blog so I saved to fav.
This is really interesting, You’re a very skilled blogger. I’ve joined your rss feed and look forward to seeking more of your magnificent post. Also, I have shared your web site in my social networks!
Hello.This post was really motivating, especially since I was looking for thoughts on this topic last Tuesday.
I am really impressed with your writing skills and also with the layout on your blog. Is this a paid theme or did you customize it yourself? Anyway keep up the nice quality writing, it is rare to see a nice blog like this one today..
Definitely believe that which you said. Your favorite justification seemed to be on the internet the easiest thing to be aware of. I say to you, I definitely get annoyed while people think about worries that they plainly don’t know about. You managed to hit the nail upon the top and defined out the whole thing without having side-effects , people could take a signal. Will probably be back to get more. Thanks
Hi my family member! I wish to say that this post is amazing, great written and come with approximately all significant infos. I’d like to see more posts like this.
Rattling nice design and good subject matter, very little else we want : D.
Thank you for the good writeup. It in fact was a amusement account it. Look advanced to more added agreeable from you! However, how could we communicate?
As soon as I detected this internet site I went on reddit to share some of the love with them.
Pretty section of content. I just stumbled upon your weblog and in accession capital to assert that I get in fact enjoyed account your blog posts. Anyway I will be subscribing to your augment and even I achievement you access consistently quickly.
Good ¡V I should certainly pronounce, impressed with your website. I had no trouble navigating through all tabs and related information ended up being truly easy to do to access. I recently found what I hoped for before you know it at all. Reasonably unusual. Is likely to appreciate it for those who add forums or something, site theme . a tones way for your customer to communicate. Excellent task..
I genuinely enjoy studying on this web site , it has wonderful content . “We find comfort among those who agree with us–growth among those who don’t.” by Frank A. Clark.
I have been absent for some time, but now I remember why I used to love this website. Thanks, I’ll try and check back more frequently. How frequently you update your site?
Thanks for helping out, excellent information. “Our individual lives cannot, generally, be works of art unless the social order is also.” by Charles Horton Cooley.
Needed to send you the little observation to finally say thanks a lot yet again with your splendid opinions you have shown on this page. It is really extremely generous with you to supply unhampered exactly what many individuals could have marketed as an ebook in making some dough for themselves, most notably now that you could have tried it in case you wanted. These creative ideas likewise served to be the fantastic way to be sure that other individuals have the identical passion really like my own to know more and more regarding this condition. Certainly there are lots of more enjoyable instances in the future for those who check out your blog.
I gotta favorite this website it seems very helpful very beneficial
Wow, wonderful blog layout! How long have you been blogging for? you make blogging look easy. The overall look of your site is excellent, let alone the content!
Utterly composed written content , thanks for selective information .
Hello There. I found your blog using msn. This is a very well written article. I’ll be sure to bookmark it and return to read more of your useful information. Thanks for the post. I will certainly return.
Hi there. I found your blog by way of Google at the same time as searching for a related subject, your website came up. It seems to be great. I’ve bookmarked it in my google bookmarks to come back then.
Good post. I learn something totally new and challenging on sites I stumbleupon on a daily basis. It’s always helpful to read through content from other authors and use a little something from other websites.
Great beat ! I would like to apprentice while you amend your site, how could i subscribe for a blog web site? The account aided me a acceptable deal. I had been a little bit acquainted of this your broadcast provided bright clear idea
I and my pals were actually checking out the nice tips found on your web site then then I had a terrible suspicion I never expressed respect to the web blog owner for those tips. The ladies were warmed to study them and have now clearly been taking pleasure in these things. Appreciate your indeed being considerably considerate and also for opting for variety of perfect resources millions of individuals are really desperate to know about. Our own sincere regret for not expressing appreciation to you earlier.
I think other web-site proprietors should take this web site as an model, very clean and great user friendly style and design, let alone the content. You are an expert in this topic!
My wife and i were really excited that Albert managed to carry out his basic research out of the precious recommendations he discovered in your weblog. It is now and again perplexing to just be giving freely guidelines people today might have been making money from. And we also fully grasp we need the blog owner to appreciate for that. The entire illustrations you have made, the straightforward website navigation, the friendships you help engender – it’s got everything overwhelming, and it’s really making our son and the family imagine that the idea is brilliant, which is certainly extraordinarily serious. Thanks for all the pieces!
Nice blog here! Also your website loads up very fast! What web host are you using? Can I get your affiliate link to your host? I wish my site loaded up as quickly as yours lol
This is very interesting, You are a very skilled blogger. I have joined your rss feed and look forward to seeking more of your wonderful post. Also, I’ve shared your site in my social networks!
Perfectly indited subject matter, appreciate it for selective information. “In the fight between you and the world, back the world.” by Frank Zappa.
Hiya, I’m really glad I have found this info. Today bloggers publish only about gossip and internet stuff and this is really irritating. A good blog with exciting content, that is what I need. Thanks for making this website, and I’ll be visiting again. Do you do newsletters by email?
Nice read, I just passed this onto a colleague who was doing some research on that. And he actually bought me lunch because I found it for him smile So let me rephrase that: Thanks for lunch!
hi!,I really like your writing so a lot! share we keep in touch extra about your post on AOL? I need a specialist in this space to unravel my problem. Maybe that’s you! Looking ahead to see you.
I’ve been absent for a while, but now I remember why I used to love this website. Thank you, I will try and check back more frequently. How frequently you update your web site?
I do believe all the ideas you have presented on your post. They’re very convincing and will certainly work. Nonetheless, the posts are too short for starters. May you please prolong them a bit from subsequent time? Thank you for the post.
Thanks, I’ve just been searching for information approximately this subject for ages and yours is the greatest I’ve discovered till now. However, what about the bottom line? Are you positive concerning the source?
I’ve been browsing online more than 3 hours today, but I by no means discovered any fascinating article like yours. It is pretty worth sufficient for me. In my view, if all site owners and bloggers made excellent content as you did, the internet will probably be a lot more helpful than ever before. “Nothing will come of nothing.” by William Shakespeare.
I will right away clutch your rss feed as I can’t to find your e-mail subscription hyperlink or e-newsletter service. Do you have any? Please let me recognize so that I may subscribe. Thanks.
Wow! This could be one particular of the most helpful blogs We’ve ever arrive across on this subject. Actually Excellent. I’m also a specialist in this topic therefore I can understand your hard work.
Great – I should certainly pronounce, impressed with your website. I had no trouble navigating through all tabs and related info ended up being truly easy to do to access. I recently found what I hoped for before you know it at all. Quite unusual. Is likely to appreciate it for those who add forums or something, site theme . a tones way for your client to communicate. Nice task.
whoah this weblog is wonderful i really like reading your posts. Stay up the good work! You recognize, many persons are searching round for this info, you could help them greatly.
Merely a smiling visitor here to share the love (:, btw great style and design .
Some truly quality articles on this site, saved to my bookmarks .
I have been absent for some time, but now I remember why I used to love this website. Thanks, I will try and check back more frequently. How frequently you update your site?
Hello my friend! I wish to say that this post is amazing, great written and come with almost all important infos. I would like to peer extra posts like this .
I truly appreciate this post. I have been looking everywhere for this! Thank goodness I found it on Bing. You’ve made my day! Thanks again
It is in point of fact a nice and useful piece of info. I am happy that you simply shared this helpful information with us. Please keep us informed like this. Thanks for sharing.
Excellent read, I just passed this onto a friend who was doing some research on that. And he actually bought me lunch since I found it for him smile Thus let me rephrase that: Thank you for lunch!
Thank you for the auspicious writeup. It in fact was a amusement account it. Look advanced to far added agreeable from you! By the way, how could we communicate?
Wonderful beat ! I wish to apprentice while you amend your web site, how could i subscribe for a blog website? The account helped me a acceptable deal. I had been tiny bit acquainted of this your broadcast provided bright clear idea
I loved as much as you will receive carried out right here. The sketch is tasteful, your authored subject matter stylish. nonetheless, you command get got an nervousness over that you wish be delivering the following. unwell unquestionably come further formerly again since exactly the same nearly a lot often inside case you shield this hike.
Somebody necessarily lend a hand to make severely articles I would state. This is the very first time I frequented your website page and so far? I amazed with the research you made to create this actual post incredible. Great process!
Pretty section of content. I just stumbled upon your weblog and in accession capital to assert that I acquire in fact enjoyed account your blog posts. Any way I will be subscribing to your augment and even I achievement you access consistently rapidly.
I do accept as true with all the ideas you’ve presented on your post. They’re really convincing and will definitely work. Nonetheless, the posts are too quick for newbies. May you please prolong them a bit from next time? Thanks for the post.
I really like your writing style, good information, regards for posting : D.
Wonderful goods from you, man. I’ve understand your stuff previous to and you are just extremely fantastic. I actually like what you’ve acquired here, really like what you’re saying and the way in which you say it. You make it entertaining and you still care for to keep it sensible. I can’t wait to read far more from you. This is actually a great website.
Great – I should definitely pronounce, impressed with your web site. I had no trouble navigating through all the tabs and related information ended up being truly easy to do to access. I recently found what I hoped for before you know it in the least. Quite unusual. Is likely to appreciate it for those who add forums or something, website theme . a tones way for your customer to communicate. Nice task.
you’re truly a excellent webmaster. The site loading speed is incredible. It kind of feels that you’re doing any unique trick. Also, The contents are masterpiece. you’ve done a wonderful job in this matter!
I in addition to my friends have been viewing the nice information and facts on your site while then got an awful suspicion I had not thanked the web blog owner for those tips. These men were absolutely happy to study them and have clearly been having fun with these things. I appreciate you for being so helpful as well as for considering certain nice things most people are really eager to be informed on. My honest apologies for not expressing appreciation to you sooner.
Undeniably believe that which you stated. Your favorite reason seemed to be on the internet the simplest thing to be aware of. I say to you, I definitely get irked while people think about worries that they just do not know about. You managed to hit the nail upon the top and also defined out the whole thing without having side-effects , people can take a signal. Will probably be back to get more. Thanks
Hi, Neat post. There is a problem together with your web site in web explorer, might check this… IE nonetheless is the marketplace chief and a big component of other folks will omit your excellent writing due to this problem.
I was reading some of your articles on this website and I believe this internet site is very informative! Keep on putting up.
Keep up the great piece of work, I read few articles on this web site and I believe that your weblog is rattling interesting and has bands of wonderful info .
Heya i am for the first time here. I found this board and I find It truly useful & it helped me out much. I hope to give something back and help others like you aided me.
You can certainly see your expertise within the work you write. The world hopes for even more passionate writers such as you who are not afraid to say how they believe. At all times follow your heart.
I have been absent for a while, but now I remember why I used to love this web site. Thank you, I’ll try and check back more often. How frequently you update your website?
I will immediately take hold of your rss feed as I can not to find your email subscription link or e-newsletter service. Do you’ve any? Kindly allow me realize so that I may subscribe. Thanks.
You could certainly see your expertise in the paintings you write. The world hopes for more passionate writers like you who are not afraid to mention how they believe. All the time follow your heart.
obviously like your website however you need to take a look at the spelling on several of your posts. Many of them are rife with spelling problems and I to find it very troublesome to tell the truth then again I¡¦ll certainly come again again.
Good morning there, just turned alert to your web page through Bing, and discovered that it’s truly educational. I will take pleasure in should you continue these.
You have brought up a very superb details , appreciate it for the post.
Keep up the good piece of work, I read few blog posts on this website and I think that your web blog is real interesting and has sets of good information.
I like this post, enjoyed this one thanks for putting up.
I like the helpful info you provide in your articles. I will bookmark your weblog and check again here frequently. I am quite certain I will learn a lot of new stuff right here! Best of luck for the next!
I was studying some of your blog posts on this internet site and I conceive this website is real informative ! Keep on posting .
Hello, Neat post. There’s a problem with your website in internet explorer, might test this… IE still is the marketplace chief and a huge element of other folks will omit your great writing due to this problem.
My husband and i ended up being now comfortable Michael managed to do his investigations from your ideas he obtained from your site. It’s not at all simplistic to simply choose to be offering points that many some others may have been making money from. We know we’ve got the writer to thank because of that. Most of the explanations you made, the straightforward web site navigation, the friendships you will help instill – it’s most powerful, and it is aiding our son in addition to our family know that that content is enjoyable, and that is incredibly indispensable. Thanks for all!
Awesome post. I’m a regular visitor of your website and appreciate you taking the time to maintain the nice site. I’ll be a frequent visitor for a long time.
There is clearly a lot to realize about this. I consider you made some good points in features also.
Wonderful goods from you, man. I have understand your stuff previous to and you are just extremely excellent. I really like what you have acquired here, certainly like what you’re saying and the way in which you say it. You make it entertaining and you still care for to keep it sensible. I can not wait to read far more from you. This is actually a terrific web site.
I like what you guys are up also. Such clever work and reporting! Keep up the superb works guys I have incorporated you guys to my blogroll. I think it will improve the value of my website :).
A person essentially assist to make seriously posts I might state. This is the first time I frequented your web page and so far? I amazed with the analysis you made to create this actual post amazing. Magnificent process!
I was just seeking this information for some time. After 6 hours of continuous Googleing, finally I got it in your website. I wonder what is the lack of Google strategy that do not rank this type of informative websites in top of the list. Normally the top sites are full of garbage.
I have been reading out many of your posts and i can state pretty clever stuff. I will surely bookmark your website.
I’m very happy to read this. This is the type of manual that needs to be given and not the accidental misinformation that’s at the other blogs. Appreciate your sharing this best doc.
As soon as I detected this web site I went on reddit to share some of the love with them.
hi!,I really like your writing so a lot! share we keep up a correspondence more about your post on AOL? I need a specialist in this area to resolve my problem. May be that’s you! Taking a look forward to look you.
Hiya, I am really glad I have found this info. Nowadays bloggers publish just about gossip and web stuff and this is actually frustrating. A good blog with exciting content, that is what I need. Thank you for making this website, and I will be visiting again. Do you do newsletters by email?
Awesome post. I am a normal visitor of your website and appreciate you taking the time to maintain the excellent site. I will be a regular visitor for a long time.
Of course, what a magnificent site and educative posts, I will bookmark your website.All the Best!
Hiya, I’m really glad I have found this information. Today bloggers publish only about gossip and net stuff and this is actually irritating. A good site with interesting content, that’s what I need. Thanks for making this website, and I will be visiting again. Do you do newsletters by email?
Awesome post. I am a normal visitor of your web site and appreciate you taking the time to maintain the excellent site. I’ll be a frequent visitor for a long time.
Hiya, I am really glad I’ve found this information. Nowadays bloggers publish just about gossip and web stuff and this is really annoying. A good blog with exciting content, this is what I need. Thank you for making this site, and I will be visiting again. Do you do newsletters by email?
Awesome post. I am a normal visitor of your web site and appreciate you taking the time to maintain the excellent site. I’ll be a frequent visitor for a really long time.
Awesome post. I’m a regular visitor of your website and appreciate you taking the time to maintain the excellent site. I’ll be a frequent visitor for a really long time.
Awesome write-up. I’m a regular visitor of your website and appreciate you taking the time to maintain the nice site. I will be a frequent visitor for a really long time.
Hiya, I’m really glad I have found this info. Today bloggers publish only about gossip and net stuff and this is actually irritating. A good site with interesting content, that’s what I need. Thanks for making this website, and I will be visiting again. Do you do newsletters by email?
Write more; that’s all I have to say. It seems as though you relied on the video to make your point. You know what you’re talking about, why waste your intelligence on just posting videos to your blog when you could be giving us something enlightening to read?
Hey there. I discovered your website via Google even as searching for a comparable topic, your web site came up. It appears to be good. I’ve bookmarked it in my google bookmarks to visit then.
Awesome post. I am a regular visitor of your site and appreciate you taking the time to maintain the nice site. I will be a frequent visitor for a long time.
Hiya, I’m really glad I have found this information. Nowadays bloggers publish just about gossip and web stuff and this is really irritating. A good website with exciting content, that is what I need. Thank you for making this web-site, and I will be visiting again. Do you do newsletters by email?
Hiya, I’m really glad I have found this information. Today bloggers publish just about gossip and net stuff and this is actually frustrating. A good website with interesting content, that is what I need. Thanks for making this web-site, and I’ll be visiting again. Do you do newsletters by email?
Very efficiently written post. It will be valuable to anyone who usess it, as well as myself. Keep doing what you are doing i will definitely read more posts. bfacbfgkeffa
I have to agree with your statement with this issue and bkceacadekkdeeae
Admiring the hard work you put into your site and detailed information you offer. It’s good to come across a blog every once in a while that isn’t the same unwanted rehashed material. Wonderful read! I’ve bookmarked your site and I’m adding your RSS feeds to my Google account. egaekdkgfade
with people like one to grant visibly all of that numerous populaces would am inflicted with sold for electronic ebook to create selected jumps in favor of their unique terminate, mainly right away kdkdecakcdeckdde
Surely together with your thoughts here and that i adore your blog! Ive bookmarked it making sure that I can come back & read more inside the foreseeable future. ddcdedakdddf
you’re truly a just right webmaster. The site loading speed is incredible. It kind of feels that you are doing any distinctive trick. In addition, The contents are masterpiece. you’ve performed a magnificent task in this subject! dcdcafedgkfbefce
Awesome post. I’m a normal visitor of your blog and appreciate you taking the time to maintain the excellent site. I’ll be a frequent visitor for a long time.
Hey there. I found your web site by means of Google while looking for a comparable matter, your website came up. It seems great. I’ve bookmarked it in my google bookmarks to visit then.
Awesome post. I am a normal visitor of your web site and appreciate you taking the time to maintain the excellent site. I will be a regular visitor for a long time.
Informative Site Hello guys here are some links that contains information which you might find useful yourselves. It is Worth Checking out. bbebdgfecfga
Thanks for the post.Really looking forward to read more. Will read on agefakkeaegdckbe
Your goal is to breed all the different dragons available to you and enter combat against other player’s dragons. fkcdagbecddf
Howdy just wanted to give you a quick heads up. The words in your article seem to be running off the screen in Ie. eadedccfkkeg
Hey there. I found your website by way of Google at the same time as searching for a comparable subject, your web site came up. It seems to be great. I have bookmarked it in my google bookmarks to visit then.
Hi there. I discovered your blog by means of Google even as searching for a comparable topic, your web site came up. It looks good. I have bookmarked it in my google bookmarks to come back then.
Hi there. I found your site via Google whilst searching for a similar matter, your site got here up. It seems good. I’ve bookmarked it in my google bookmarks to come back then.
Hiya, I am really glad I have found this info. Today bloggers publish only about gossip and net stuff and this is actually irritating. A good website with interesting content, that is what I need. Thank you for making this web site, and I’ll be visiting again. Do you do newsletters by email?
Hiya, I am really glad I’ve found this information. Nowadays bloggers publish only about gossip and web stuff and this is really annoying. A good blog with interesting content, this is what I need. Thanks for making this web site, and I’ll be visiting again. Do you do newsletters by email?
Awesome post. I am a regular visitor of your web site and appreciate you taking the time to maintain the nice site. I will be a regular visitor for a really long time.
Awesome post. I’m a regular visitor of your site and appreciate you taking the time to maintain the nice site. I will be a regular visitor for a long time.
Hello.This article was really fascinating, especially since I was investigating for thoughts on this topic last Monday.
Hey there. I found your web site by way of Google while looking for a comparable matter, your website got here up. It appears great. I have bookmarked it in my google bookmarks to come back then.
Hi there. I discovered your site by the use of Google even as looking for a similar subject, your site got here up. It seems to be good. I have bookmarked it in my google bookmarks to visit then.
Awesome write-up. I’m a regular visitor of your web site and appreciate you taking the time to maintain the excellent site. I’ll be a frequent visitor for a long time.
Hiya, I am really glad I have found this information. Nowadays bloggers publish just about gossip and net stuff and this is really annoying. A good website with interesting content, this is what I need. Thank you for making this site, and I’ll be visiting again. Do you do newsletters by email?
A lot of thanks for all your valuable effort on this blog. My niece takes pleasure in managing internet research and it is obvious why. I know all about the lively manner you present great guides via the web blog and even invigorate participation from others on that idea so my daughter is in fact discovering a great deal. Take pleasure in the rest of the new year. You have been doing a great job.
Hey there. I found your web site by means of Google at the same time as searching for a similar matter, your web site came up. It appears great. I have bookmarked it in my google bookmarks to visit then.
Hiya, I am really glad I’ve found this information. Today bloggers publish just about gossip and net stuff and this is really irritating. A good website with exciting content, this is what I need. Thanks for making this website, and I will be visiting again. Do you do newsletters by email?
I respect your work , regards for all the good posts .
Hiya, I am really glad I’ve found this info. Nowadays bloggers publish just about gossip and web stuff and this is actually annoying. A good site with interesting content, this is what I need. Thanks for making this site, and I’ll be visiting again. Do you do newsletters by email?
Awesome post. I’m a regular visitor of your site and appreciate you taking the time to maintain the excellent site. I’ll be a frequent visitor for a really long time.
Awesome post. I am a regular visitor of your site and appreciate you taking the time to maintain the nice site. I will be a regular visitor for a long time.
Awesome write-up. I’m a regular visitor of your blog and appreciate you taking the time to maintain the excellent site. I will be a frequent visitor for a really long time.
Hiya, I am really glad I’ve found this information. Nowadays bloggers publish only about gossip and web stuff and this is actually annoying. A good blog with interesting content, this is what I need. Thanks for making this website, and I’ll be visiting again. Do you do newsletters by email?
Awesome write-up. I’m a normal visitor of your site and appreciate you taking the time to maintain the excellent site. I will be a frequent visitor for a really long time.
Hi there. I found your blog by way of Google at the same time as looking for a comparable subject, your site came up. It appears to be good. I’ve bookmarked it in my google bookmarks to come back then.
Of course, what a fantastic site and enlightening posts, I will bookmark your website.Best Regards!
Hi there. I discovered your web site by way of Google while searching for a related subject, your site came up. It seems good. I have bookmarked it in my google bookmarks to visit then.
Hey there. I found your web site by the use of Google at the same time as looking for a similar topic, your web site got here up. It seems to be good. I have bookmarked it in my google bookmarks to visit then.
Awesome write-up. I’m a normal visitor of your blog and appreciate you taking the time to maintain the excellent site. I’ll be a frequent visitor for a long time.
Hiya, I am really glad I have found this information. Nowadays bloggers publish only about gossip and web stuff and this is really irritating. A good blog with interesting content, that is what I need. Thanks for making this site, and I’ll be visiting again. Do you do newsletters by email?
Hiya, I am really glad I’ve found this information. Nowadays bloggers publish only about gossip and net stuff and this is actually frustrating. A good website with exciting content, that is what I need. Thank you for making this website, and I will be visiting again. Do you do newsletters by email?
I’m also writing to let you understand of the fine experience my friend’s girl had going through your site. She mastered numerous issues, with the inclusion of what it’s like to have a marvelous teaching spirit to get other people effortlessly fully grasp several complicated subject areas. You truly surpassed people’s expected results. I appreciate you for imparting these informative, trustworthy, explanatory as well as easy thoughts on that topic to Evelyn.
you’re in reality a excellent webmaster. The site loading velocity is incredible. It seems that you’re doing any distinctive trick. Furthermore, The contents are masterpiece. you have done a fantastic task on this topic!
I am very happy to read this. This is the type of manual that needs to be given and not the accidental misinformation that’s at the other blogs. Appreciate your sharing this best doc.
Awesome write-up. I am a regular visitor of your website and appreciate you taking the time to maintain the excellent site. I’ll be a frequent visitor for a long time.
Awesome write-up. I’m a regular visitor of your web site and appreciate you taking the time to maintain the excellent site. I’ll be a regular visitor for a really long time.
Hiya, I am really glad I have found this info. Today bloggers publish only about gossip and net stuff and this is really annoying. A good web site with interesting content, this is what I need. Thank you for making this website, and I will be visiting again. Do you do newsletters by email?
Hi, Neat post. There’s an issue together with your website in web explorer, could check this¡K IE still is the market leader and a good element of people will leave out your wonderful writing due to this problem.
Awesome post. I’m a normal visitor of your blog and appreciate you taking the time to maintain the excellent site. I will be a frequent visitor for a long time.
Hiya, I am really glad I’ve found this information. Today bloggers publish only about gossip and web stuff and this is actually frustrating. A good web site with interesting content, this is what I need. Thank you for making this site, and I will be visiting again. Do you do newsletters by email?
Hey there. I discovered your site via Google whilst searching for a comparable subject, your web site got here up. It appears to be great. I’ve bookmarked it in my google bookmarks to visit then.
Hiya, I’m really glad I’ve found this info. Today bloggers publish only about gossip and internet stuff and this is really annoying. A good web site with exciting content, this is what I need. Thank you for making this web-site, and I will be visiting again. Do you do newsletters by email?
Hiya, I’m really glad I’ve found this info. Nowadays bloggers publish just about gossip and internet stuff and this is actually annoying. A good site with interesting content, this is what I need. Thanks for making this web site, and I’ll be visiting again. Do you do newsletters by email?
Hello there. I found your site by the use of Google at the same time as looking for a comparable topic, your website came up. It seems good. I’ve bookmarked it in my google bookmarks to come back then.
Thanks a bunch for sharing this with all folks you really understand what you are speaking about! Bookmarked. Kindly also visit my website =). We will have a hyperlink alternate arrangement between us!
Hey there. I discovered your site by the use of Google whilst looking for a comparable topic, your site came up. It appears good. I’ve bookmarked it in my google bookmarks to visit then.
Awesome write-up. I am a regular visitor of your web site and appreciate you taking the time to maintain the nice site. I will be a frequent visitor for a long time.
Hiya, I’m really glad I’ve found this info. Today bloggers publish only about gossip and net stuff and this is actually irritating. A good website with exciting content, that is what I need. Thanks for making this web-site, and I’ll be visiting again. Do you do newsletters by email?
Awesome post. I am a normal visitor of your blog and appreciate you taking the time to maintain the nice site. I’ll be a frequent visitor for a long time.
Awesome post. I am a regular visitor of your site and appreciate you taking the time to maintain the excellent site. I will be a frequent visitor for a really long time.
Hello there. I discovered your web site by way of Google even as searching for a comparable matter, your web site came up. It looks good. I’ve bookmarked it in my google bookmarks to visit then.
Hi there. I discovered your web site by way of Google whilst looking for a related matter, your site got here up. It looks great. I have bookmarked it in my google bookmarks to visit then.
Hi there. I found your site by the use of Google even as looking for a similar topic, your web site got here up. It looks good. I’ve bookmarked it in my google bookmarks to come back then.
Hi there. I discovered your web site by means of Google whilst looking for a similar subject, your website came up. It looks good. I’ve bookmarked it in my google bookmarks to come back then.
Hiya, I’m really glad I have found this info. Today bloggers publish just about gossip and web stuff and this is really annoying. A good website with interesting content, this is what I need. Thanks for making this website, and I’ll be visiting again. Do you do newsletters by email?
Hi there. I discovered your site by way of Google even as searching for a similar subject, your site came up. It seems to be great. I’ve bookmarked it in my google bookmarks to come back then.
Awesome post. I’m a normal visitor of your web site and appreciate you taking the time to maintain the excellent site. I will be a frequent visitor for a really long time.
Hello there. I discovered your website by the use of Google while searching for a comparable matter, your site came up. It seems great. I have bookmarked it in my google bookmarks to come back then.
Hey there. I found your website by way of Google at the same time as searching for a comparable topic, your site got here up. It seems great. I have bookmarked it in my google bookmarks to visit then.
Awesome write-up. I’m a normal visitor of your blog and appreciate you taking the time to maintain the nice site. I’ll be a frequent visitor for a long time.
Excellent read, I just passed this onto a colleague who was doing some research on that. And he actually bought me lunch because I found it for him smile So let me rephrase that: Thanks for lunch!
Hello there. I discovered your site by way of Google while looking for a similar matter, your web site got here up. It seems to be great. I have bookmarked it in my google bookmarks to come back then.
Hiya, I’m really glad I have found this information. Nowadays bloggers publish just about gossip and web stuff and this is actually annoying. A good web site with interesting content, that’s what I need. Thank you for making this site, and I will be visiting again. Do you do newsletters by email?
Awesome write-up. I’m a regular visitor of your web site and appreciate you taking the time to maintain the excellent site. I will be a regular visitor for a really long time.
Good web site! I really love how it is simple on my eyes and the data are well written. I am wondering how I might be notified whenever a new post has been made. I’ve subscribed to your RSS which must do the trick! Have a great day!
Thank you for the good writeup. It in fact was a amusement account it. Look advanced to far added agreeable from you! However, how could we communicate?
Simply desire to say your article is as astounding. The clarity in your post is simply cool and i can assume you’re an expert on this subject. Fine with your permission let me to grab your feed to keep up to date with forthcoming post. Thanks a million and please continue the enjoyable work.
I was just seeking this info for some time. After 6 hours of continuous Googleing, at last I got it in your website. I wonder what is the lack of Google strategy that don’t rank this kind of informative sites in top of the list. Usually the top web sites are full of garbage.
Hello there. I found your site by means of Google even as looking for a comparable matter, your website came up. It looks great. I’ve bookmarked it in my google bookmarks to come back then.
Hey there. I discovered your web site by way of Google while looking for a comparable subject, your web site got here up. It seems good. I’ve bookmarked it in my google bookmarks to come back then.
Hi there. I discovered your website by the use of Google whilst searching for a similar matter, your web site came up. It looks great. I’ve bookmarked it in my google bookmarks to visit then.
Awesome write-up. I’m a normal visitor of your website and appreciate you taking the time to maintain the nice site. I will be a frequent visitor for a long time.
I loved as much as you will receive carried out right here. The sketch is tasteful, your authored material stylish. nonetheless, you command get got an edginess over that you wish be delivering the following. unwell unquestionably come more formerly again since exactly the same nearly a lot often inside case you shield this increase.
You completed a few fine points there. I did a search on the issue and found mainly persons will agree with your blog.
Hey there. I discovered your site by way of Google while searching for a similar topic, your web site came up. It appears to be great. I’ve bookmarked it in my google bookmarks to visit then.
Good info and right to the point. I am not sure if this is really the best place to ask but do you guys have any ideea where to get some professional writers? Thanks in advance 🙂
Hello there. I discovered your website by means of Google at the same time as looking for a comparable subject, your website got here up. It seems to be good. I’ve bookmarked it in my google bookmarks to come back then.
I’m really impressed with your writing skills and also with the layout on your weblog. Is this a paid theme or did you customize it yourself? Either way keep up the excellent quality writing, it’s rare to see a nice blog like this one today..
I don’t even know how I ended up here, but I thought this post was good. I do not know who you are but definitely you’re going to a famous blogger if you are not already 😉 Cheers!
I have been checking out many of your articles and i must say pretty good stuff. I will surely bookmark your website.
Awesome post. I am a normal visitor of your site and appreciate you taking the time to maintain the nice site. I’ll be a regular visitor for a really long time.
Awesome write-up. I am a regular visitor of your web site and appreciate you taking the time to maintain the excellent site. I will be a regular visitor for a really long time.
Awesome post. I’m a normal visitor of your web site and appreciate you taking the time to maintain the nice site. I will be a regular visitor for a long time.
Hiya, I’m really glad I have found this information. Today bloggers publish just about gossip and net stuff and this is actually frustrating. A good blog with exciting content, that is what I need. Thank you for making this website, and I’ll be visiting again. Do you do newsletters by email?
Hello there. I discovered your site by means of Google whilst searching for a related topic, your web site got here up. It seems good. I’ve bookmarked it in my google bookmarks to come back then.
Hiya, I’m really glad I have found this info. Nowadays bloggers publish only about gossip and internet stuff and this is actually irritating. A good site with exciting content, that’s what I need. Thanks for making this web-site, and I will be visiting again. Do you do newsletters by email?
Hey there. I found your site by the use of Google even as searching for a comparable subject, your web site got here up. It looks great. I’ve bookmarked it in my google bookmarks to visit then.
hey there and thank you for your information – I’ve definitely picked up something new from right here. I did however expertise several technical points using this website, as I experienced to reload the website many times previous to I could get it to load properly. I had been wondering if your web hosting is OK? Not that I am complaining, but slow loading instances times will sometimes affect your placement in google and can damage your high quality score if advertising and marketing with Adwords. Anyway I am adding this RSS to my email and can look out for much more of your respective intriguing content. Make sure you update this again soon..
Hello there. I found your website by means of Google even as looking for a comparable subject, your site got here up. It appears to be good. I have bookmarked it in my google bookmarks to visit then.
Hi there. I discovered your site by way of Google even as looking for a comparable matter, your website came up. It looks good. I’ve bookmarked it in my google bookmarks to come back then.
Hello there. I found your website by the use of Google whilst looking for a similar subject, your web site got here up. It seems good. I have bookmarked it in my google bookmarks to visit then.
Awesome post. I’m a regular visitor of your blog and appreciate you taking the time to maintain the nice site. I will be a frequent visitor for a really long time.
Awesome post. I am a normal visitor of your web site and appreciate you taking the time to maintain the excellent site. I will be a frequent visitor for a really long time.
Hi there. I found your blog via Google at the same time as looking for a related matter, your website got here up. It seems good. I’ve bookmarked it in my google bookmarks to visit then.
For most up-to-date news you have to go to see world wide web and
on the web I found this web page as a most excellent site for most up-to-date updates.
I’m planning to start my blog soon, but I’m a little lost on everything. Would you suggest starting with a free platform like WordPress or go for a paid option? There are so many choices out there that I’m completely confused. Any suggestions? Thanks a lot.
This message is posted here using XRumer + XEvil 4.0
XEvil 4.0 is a revolutionary application that can bypass any antibot CAPTCHA’s.
Captcha Bypass Google (ReCaptcha-1, ReCaptcha-2), Facebook, BING, Hotmail, Yahoo,
Yandex, VKontakte, Captcha Com – and over 8.4 million other types!
You read this – it means it works! 😉
Details on the official website of XEvil.Net, there is a free demo version.
Check YouTube video “XEvil ReCaptcha2”
I was just seeking this info for some time. After six hours of continuous Googleing, at last I got it in your web site. I wonder what is the lack of Google strategy that don’t rank this kind of informative websites in top of the list. Generally the top sites are full of garbage. gefgdggkkebb
Enjoyed examining this, very good stuff, thankyou. Talk sense to a fool and he calls you foolish. by Euripides. kedeeadgeebdfaee
You have brought up a very excellent details , regards for the post. ddadgfdbefbd
with people like one to grant visibly all of that numerous populaces would am inflicted with sold for electronic ebook to create selected jumps in favor of their unique terminate, mainly right away eecdddcddkdbedkg
I am really enjoying the themedesign of your blog. Do you ever run into any browser compatibility problems? A handful of my blog readers have complained about my website not operating correctly in Explorer but looks great in Chrome. Do you have any advice to help fix this issue? aaaddaabbadd
Write more, thats all I have to say. Literally, it seems as though you relied on the video to make your point. You clearly know what youre talking about, why throw away your intelligence on just posting videos to your weblog when you could be giving us something enlightening to read? bkdeabcdcfcebedf
Do you mind if I quote a few of your posts as long as I provide credit and sources back to your weblog? My blog is in the very same niche as yours and my users would truly benefit from a lot of the information you present here. Please let me know if this alright with you. Thank you! gkkegddcabdk
Some really quality blog posts on this internet site , saved to fav. gckbkeeebecc
Hiya, I am really glad I have found this information. Nowadays bloggers publish just about gossips and web and this is really annoying. A good blog with interesting content, that is what I need. Thanks for keeping this website, I’ll be visiting it. Do you do newsletters? Can not find it. akadkgecagefcdee
I am just seeming both for blog sites which give independent, nutritious commentary on all difficulties or blogging sites which have a liberal or droppedwing slant. Thank you.. eeeddcedfdae
I am now not certain the place you’re getting your info, however good topic. I needs to spend some time learning more or figuring out more. Thank you for magnificent info I was on the lookout for this information for my mission. agfgfgfdkabcabkc
Very great post. I just stumbled upon your weblog and wanted to mention that I’ve truly enjoyed surfing around your blog posts.
After all I’ll be subscribing in your feed and I
am hoping you write again very soon!
Appreciate the recommendation. Will try it out.
Only wanna tell that this is very useful , Thanks for taking your time to write this. dbgkgcaecbkg
There are some attentiongrabbing points in time in this article but I dont know if I see all of them heart to heart. There may be some validity however I will take maintain opinion until I look into it further. Good article , thanks and we would like extra! Added to FeedBurner as properly eeeafebfkfbk
There is visibly a bunch to realize about this. I consider you made various good points in features also. kabgdebckccf
Just wanna remark on couple of general issues, The web site style is perfect, the subject matter is rattling excellent dcedgkagakbgfdfa
Thank you, I have just been searching for information approximately this subject for ages and yours is the best I have came upon till now. But, what concerning the conclusion? Are you certain in regards to the supply? bfdeckegbeke
I really like your writing style, excellent info, thank you for putting up ddcgbacedgdc
It is actually a nice and helpful piece of information. I am happy that you simply shared this helpful information with us. Please stay us informed like this. Thank you for sharing. gbakgccgkbfk
Thanks for the post.Really looking forward to read more. Will read on kbcddeedcdcfdakd
Wow, marvelous blog structure! How long have you been running a blog aadecddkffaf
Great article post.Really thank you! Fantastic. feeebfbfaebeaeac
Good web site! I really love how it is easy on my eyes and the data are well written. I am wondering how I might be notified whenever a new post has been made. I’ve subscribed to your RSS which must do the trick! Have a great day! fddcgbdeeede
Thanks so much for the article.Much thanks again. Great. abdcdeddcafc
Hello! This post could not be written any better! Reading through this post reminds me of my good aegdeabgbcbgekab
I think this is one of the most significant information for me. And i’m glad reading your article. But should remark on some general things, The web site style is wonderful, the articles is really excellent D. Good job, cheers egebddddgddf
Hi, yup this post is truly fastidious and I have learned lot of things from it ebcbagabebdkgdec
What is the website that means it is easy to understand podcasts and blog sites? I don’t get an iPod, does that make any difference? . accefeebagec
Spot lets start off perform on this writeup, I seriously consider this astounding internet site needs much more consideration. Ill apt to become once again to find out to read considerably a lot more, thank you that information. ekcacedkdkabgeek
You are my breathing in, I possess few blogs and very sporadically run out from to brand. edefgcgdedcd
whoah this blog is fantastic i really like studying your articles. Keep up the good paintings! You understand, many individuals are looking around for this info, you could aid them greatly. fdcefedabkddbdcd
Thanks a bunch for sharing this with all of us you actually realize what you’re talking approximately! Bookmarked. Kindly also visit my web site . We will have a hyperlink exchange arrangement among us! dbeegeeckfbf
Wow, wonderful blog layout! How long have you been blogging for? you made blogging look easy. The overall look of your web site is excellent, as well as the content! ddkdkddccddddbcg
Aw, this was a really good post. Spending some time and actual effort to generate a superb article… but what can I say…
I procrastinate a whole lot and never seem to get anything done.
Some truly prime content on this website , saved to my bookmarks .
Major thanks for the article.Really thank you! Will read on
Some truly prime content on this website , saved to my bookmarks .
Yeah bookmaking this wasn at a bad determination outstanding post!
I gotta favorite this internet site it seems very helpful very useful
Thanks a lot for the article post.Really looking forward to read more.
I am just starting to learn about all of this. Thanks!
You saved me a lot of hassle just now.
I simply want to mention I’m new to weblog and absolutely enjoyed you’re website. Probably I’m going to bookmark your blog post . You definitely have remarkable posts. With thanks for sharing with us your web site.
It as hard to come by well-informed people on this subject, however, you sound like you know what you are talking about! Thanks
It as hard to come by well-informed people on this subject, however, you sound like you know what you are talking about! Thanks
Major thanks for the article.Really thank you! Will read on
Major thanks for the article.Really thank you! Will read on
I gotta favorite this internet site it seems very helpful very useful
Thanks a lot for the article post.Really looking forward to read more.
Right away I am ready to do my breakfast, later than having my breakfast coming again to read more news.
It as hard to come by well-informed people on this subject, however, you sound like you know what you are talking about! Thanks
pretty valuable material, overall I believe this is worth a bookmark, thanks
pretty valuable material, overall I believe this is worth a bookmark, thanks
I gotta favorite this internet site it seems very helpful very useful
Some truly prime content on this website , saved to my bookmarks .
I gotta favorite this internet site it seems very helpful very useful
It as hard to come by well-informed people on this subject, however, you sound like you know what you are talking about! Thanks
Right away I am ready to do my breakfast, later than having my breakfast coming again to read more news.
Yeah bookmaking this wasn at a bad determination outstanding post!
I gotta favorite this internet site it seems very helpful very useful
Say, you got a nice article post.Really looking forward to read more. Will read on
Thanks a lot for the article post.Really looking forward to read more.
Very good article post.Really thank you! Will read on
Say, you got a nice article post.Really looking forward to read more. Will read on
Say, you got a nice article post.Really looking forward to read more. Will read on
Yeah bookmaking this wasn at a bad determination outstanding post!
I gotta favorite this internet site it seems very helpful very useful
Very good article post.Really thank you! Will read on
What a totally amazing website. You’ve got something special going on here!
HurrahWow! FinallyAt lastAfter allIn the end I got a blogweblogwebpagewebsiteweb site from where I canbe able toknow how tobe capable of reallyactuallyin facttrulygenuinely takegetobtain usefulhelpfulvaluable datainformationfacts regardingconcerning my study and knowledge.
I admire the beneficial information and facts you provide in your posts. I will bookmark your blog and have my children examine up right here often. From: home interior decoration design ideas
“I am just starting to learn about all of this. Thanks for your help!”
This is very interesting, You’re a very skilled blogger. I’ve joined your rss feed and look forward to seeking more of your fantastic post. Also, I have shared your website in my social networks!
But a smiling visitor here to share the love (:, btw great design .
Major thanks for the article.Really thank you! Will read on
Needed to compose you a very little word to thank you yet again regarding the nice suggestions you’ve contributed here.
that’s why I bookmarked this page for get news feed with perfectly information in the next coming post ,
(Existing without the answers to the difficulties you’ve sorted out through this guide is a critical case, as well as the kind which could have badly affected my entire career if I had not discovered your website.
You have mentioned very interesting points ! ps nice website . “Justice is the truth in action.” by Jeseph Joubert.
Thank you for such a well written article. It’s full of insightful information and entertaining descriptions. Your point of view is the best among many.
Good day very cool website!! Man .. Excellent ..
Amazing .. I’ll bookmark your web site and take
the feeds also? I am satisfied to find a lot of useful information right here within the put up, we need develop extra techniques in this regard,
thank you for sharing. . . . . .
I precisely had to appreciate you again. I do not know the things that I would’ve achieved in the absence of the entire thoughts shown by you over such a situation. This has been an absolute troublesome problem for me personally, but being able to see this specialised avenue you resolved it made me to jump for fulfillment. Now i’m happy for the work and sincerely hope you really know what a powerful job you are always doing educating some other people through your website. I’m certain you haven’t come across all of us.
You made some really good points there. I checked on the internet for
more info about the issue and found most individuals will go along with your views on this web site.
We are a group of volunteers and starting a new scheme in our community.
Your website provided us with valuable info to work on. You
have done a formidable job and our whole community will be
thankful to you.
Asking questions are actually good thing if you are not understanding something completely, but this paragraph offers pleasant
understanding yet.
Pretty! This was a really wonderful article. Thanks for supplying these details.
This is very interesting, You are a very skilled blogger.
I’ve joined your rss feed and look forward to seeking
more of your great post. Also, I’ve shared your web site in my social networks!
What i don’t understood is in reality how you’re no longer really much more smartly-favored than you may be right now.
You are so intelligent. You already know thus considerably when it comes to this
subject, made me in my opinion consider it from a lot of various
angles. Its like men and women are not fascinated unless
it is one thing to do with Woman gaga! Your
personal stuffs excellent. All the time handle it up!
You ought to take part in a contest for one of the most useful
sites on the net. I will recommend this site!
I love it when people get together and share thoughts. Great site, stick with it!
I will right away seize your rss as I can not in finding your email subscription hyperlink
or newsletter service. Do you have any? Please permit
me know so that I may just subscribe. Thanks.
It’s the best time to make a few plans for the future and it is time to be happy.
I’ve read this post and if I may just I want to recommend you few attention-grabbing things
or suggestions. Perhaps you could write subsequent articles regarding
this article. I wish to learn more things approximately
it!
I love what you guys are up too. This kind of clever work and reporting!
Keep up the awesome works guys I’ve added you guys to my blogroll.
What’s up i am kavin, its my first occasion to commenting anywhere, when i read this post
i thought i could also make comment due to this sensible post.
I am sure this paragraph has touched all the internet viewers, its really really fastidious article on building up new web site.
It is the best time to make some plans for the future and
it’s time to be happy. I have read this post and if
I could I desire to suggest you some interesting things or suggestions.
Perhaps you can write next articles referring to this article.
I wish to read more things about it!
Hi, yeah this article is in fact nice and I have learned lot
of things from it about blogging. thanks.
It’s been simply incredibly generous with you to provide publicly what exactly many people would’ve promoted for an ebook to wind up making some money for their ending, primarily given that you might have attempted it in case you wanted.
When I initially remarked I clicked the “Notify me when new comments are added” checkbox and each time a comment is inserted I get many emails with the same remark. Are there any way you may eliminate people from this service? Thanks. {
We are a group of volunteers and starting a new scheme
in our community. Your site offered us with valuable information to work on. You have done an impressive
job and our whole community will be grateful to you.
It is always so pleasant and full of a lot of pleasure for me personally and my workplace coworkers to search your site a minimum of thrice in each week to observe the new advice you have got.
I need to to thank you for this wonderful read!!
I certainly enjoyed every bit of it. I have you book-marked to look at new stuff
you post…
I was suggested this web site through my cousin. I am no longer certain whether this publish is
written by him as nobody else recognise such exact
approximately my trouble. You’re incredible!
Thank you!
Pretty section of content. I just stumbled upon your weblog and in accession capital to assert
that I get in fact enjoyed account your blog posts.
Anyway I’ll be subscribing to your feeds and even I achievement you access consistently rapidly.
I am really impressed with your writing abilities as smartly as with the format to your weblog.
Is this a paid subject or did you modify it your self?
Anyway keep up the nice high quality writing, it is rare to look
a great blog like this one these days..
What a stuff of un-ambiguity and preserveness of valuable know-how concerning unpredicted
feelings.
Pretty portion of content. I simply stumbled upon your site and
in accession capital to say that I acquire actually enjoyed account your blog posts.
Anyway I’ll be subscribing on your augment and even I fulfillment you get right of entry to persistently
quickly.
Wonderful article! This is the kind of info that are meant
to be shared around the net. Disgrace on the search engines for now
not positioning this post upper! Come on over and consult with my site .
Thanks =)
You really make it seem so easy with your presentation but I find this
matter to be really something which I think I would never understand.
It seems too complex and extremely broad for me. I’m looking
forward for your next post, I will try to get the hang of
it!
This design is spectacular! You most certainly know how to keep a reader amused.
Between your wit and your videos, I was almost moved to
start my own blog (well, almost…HaHa!) Wonderful job.
I really enjoyed what you had to say, and more
than that, how you presented it. Too cool!
Write more, thats all I have to say. Literally, it seems as though you relied on the video to make your point.
You obviously know what youre talking about, why throw away your intelligence on just posting videos to
your blog when you could be giving us something informative to
read?
Ahaa, its pleasant conversation regarding this piece of
writing here at this webpage, I have read all that, so now me also commenting at this place.
If some one desires to be updated with most up-to-date technologies afterward he must be pay
a visit this website and be up to date every day.
Hey there, You’ve done a fantastic job. I will certainly digg it and personally suggest
to my friends. I’m sure they will be benefited from this website.
It’s very straightforward to find out any topic
on web as compared to books, as I found this post at this website.
You can definitely see your skills within the work you write.
The sector hopes for even more passionate writers such as you who are not afraid to mention how they believe.
All the time go after your heart.