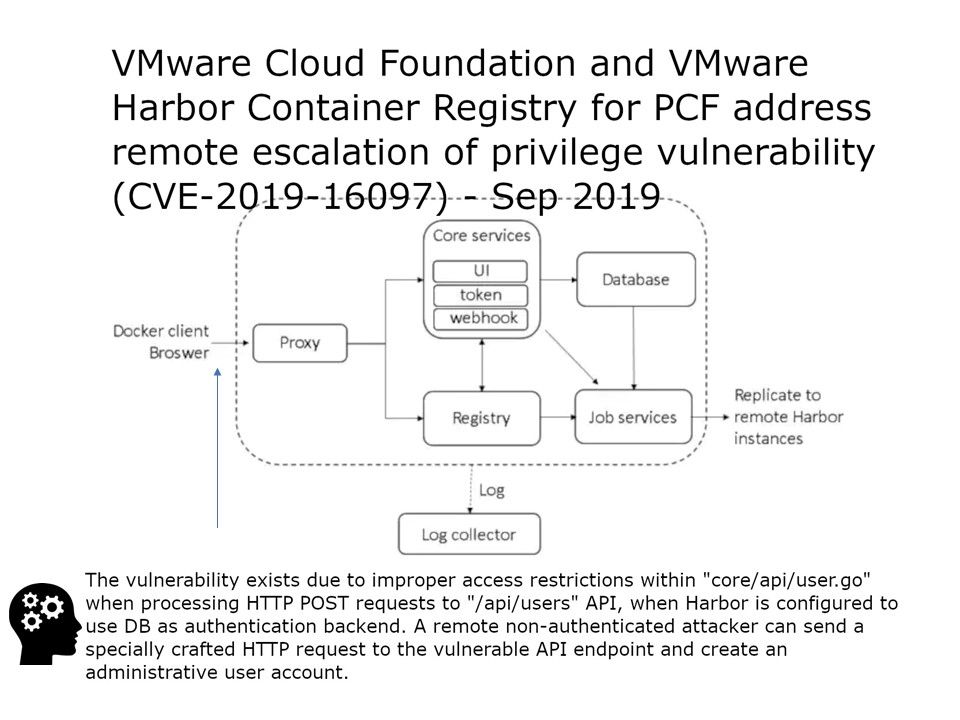
Background: There are six major modules in harbor. The default components of each harbor are packaged into a docker container, so the harbor can be deployed via compose, which is divided into 8 containers and run through docker-compose ps.
Vulnerability details: A vulnerability in the POST /api/users API of Harbor may allow for a remote escalation of privilege.
The vulnerability exists due to improper access restrictions within “core/api/user.go” when processing HTTP POST requests to “/api/users” API, when Harbor is configured to use DB as authentication backend. A remote non-authenticated attacker can send a specially crafted HTTP request to the vulnerable API endpoint and create an administrative user account.
Reminder:
a. When using LDAP mode, user’s self-registration is disabled.
b. Database(db_auth) – Users are stored in the local database.
A user can register himself/herself in Harbor in this mode.
Official announcement: https://www.vmware.com/security/advisories/VMSA-2019-0015.html