Preface: CIS Center for Internet Security Urge PHP customer stay alert of the zero-day vulnerability. It could allow for Arbitrary Code Execution. 27th Sep 2019
Vulnerability details: A vulnerability has been discovered in PHP, which could allow an attacker to execute arbitrary code. PHP is prone to a heap-based buffer-overflow vulnerability because the application fails to properly bounds-check user-supplied data before copying it into an insufficiently sized buffer. Specifically, this issue exists in the ‘mb_eregi()’ function.
SYSTEMS AFFECTED: PHP versions 7.3 prior to 7.3.10
Additional details: The feature of “mb_eredi( )” is executes the case insensitive regular expression match with multibyte support. Since this function did not properly bounds-check user-supplied data. As a result, it will copy string it into sized buffer(array). If no matches are found, regs is set to an empty array. This buffer area (array) is located in heap of memory. We known heap is an area of pre-reserved computer main storage ( memory ) that a program process can use to store data in some variable amount that won’t be known until the program is running.
When this happens, the buffer that is assumed to be freed will be expected to hold two pointers FD and BK in the first 8 bytes of the formerly allocated buffer. BK gets written into FD and can be used to overwrite a pointer.
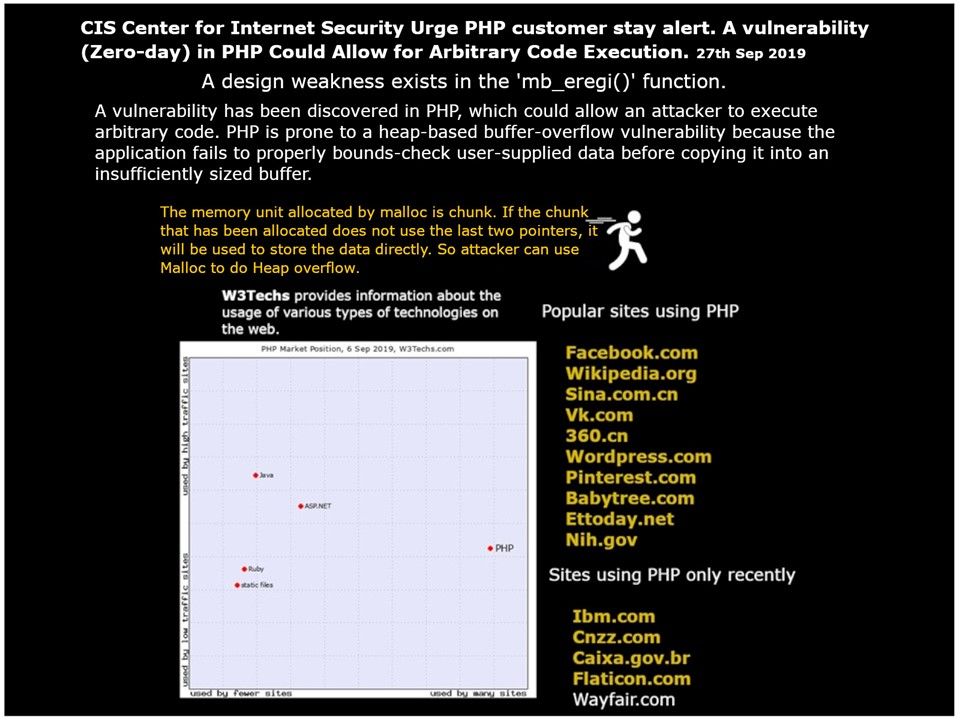
Reference: The memory unit allocated by malloc is chunk. If the chunk that has been allocated does not use the last two pointers, it will be used to store the data directly. So attacker can use Malloc to do Heap overflow.
Remedy: Reference URL – https://www.php.net/downloads.php#gpg