Preface: Xiaomi and Samsung are MediaTek’s biggest clients
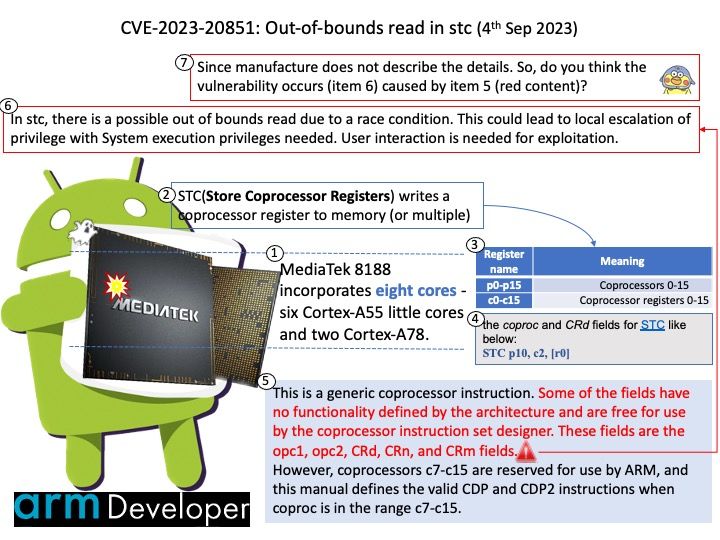
Background: MediaTek 8188 (MT8188) is a 64-bit ARM SoC introduced by MediaTek in 2022. The chip incorporates eight cores – six Cortex-A55 little cores and two Cortex-A78. Cortex-A78 can operate at up to 2.6 GHz. Cortex-A55 can operate at up to 2.0 GHz.
STC(Store Coprocessor Registers) writes a coprocessor register to memory (or multiple). It is unlikely to get much use out of the STC instruction without some custom coprocessor to use it on, since the behaviour and meaning of the generic coprocessor instructions is defined by the coprocessor itself.
Vulnerability details: In stc, there is a possible out of bounds read due to a race condition. This could lead to local escalation of privilege with System execution privileges needed. User interaction is needed for exploitation.
Remark: According to my observation (predicting the possible cause of this vulnerability), please refer to the attached picture.
Reference I:
STC is available in all versions of the ARM architecture.
STC2 is available in ARMv5T and above.
Reference II:
Race conditions are most commonly associated with computer science and programming. They occur when two computer program processes, or threads, attempt to access the same resource at the same time and cause problems in the system. Race conditions are considered a common issue for multithreaded applications.
Official announcement: For details, please refer to link – https://corp.mediatek.com/product-security-bulletin/September-2023