Preface: USAT (USIM Application Toolkit) technology is based on the original passive operation mode of the SIM card and adds the new active operation capability of the SIM card, which allows applications and services in the SIM card to actively interact with mobile terminals.
Background: The USAT (USIM Application Toolkit) is a standardized set of commands and protocols that allow mobile applications to interact with the USIM card in 3G and 4G/LTE mobile networks.
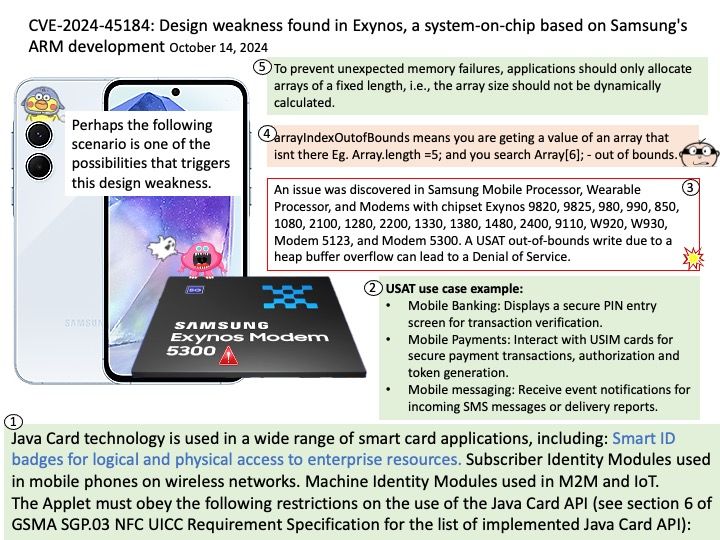
USAT use case example:
Mobile Banking: Displays a secure PIN entry screen for transaction verification.
Mobile Payments: Interact with USIM cards for secure payment transactions, authorization and token generation.
Mobile messaging: Receive event notifications for incoming SMS messages or delivery reports.
Vulnerability details: An issue was discovered in Samsung Mobile Processor, Wearable Processor, and Modems with chipset Exynos 9820, 9825, 980, 990, 850, 1080, 2100, 1280, 2200, 1330, 1380, 1480, 2400, 9110, W920, W930, Modem 5123, and Modem 5300. A USAT out-of-bounds write due to a heap buffer overflow can lead to a Denial of Service.
Official announcement: Please refer to the link for details – https://semiconductor.samsung.com/support/quality-support/product-security-updates/cve-2024-45184/