Preface: Switched Fabric or switching fabric is a network topology in which network nodes interconnect via one or more network switches.
What is Cisco ACI? – Cisco ACI is a tightly coupled policy-driven solution that integrates software and hardware. The hardware for Cisco ACI is based on the Cisco Nexus 9000 family of switches. The software and integration points for ACI include a few components, including Additional Data Center Pod, Data Center Policy Engine, and Non-Directly Attached Virtual and Physical Leaf Switches.
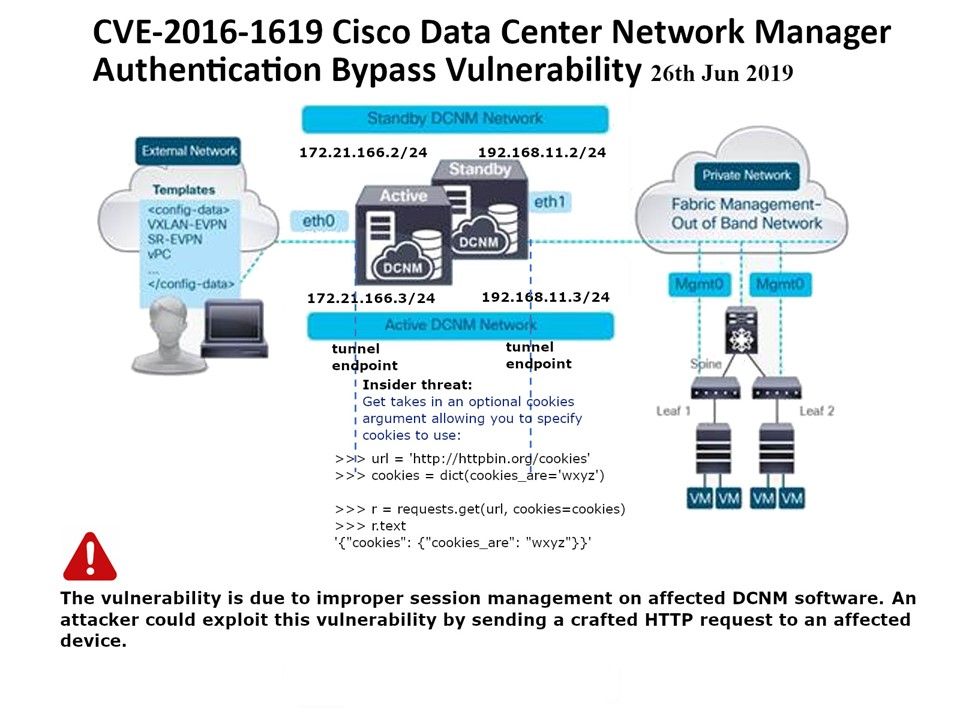
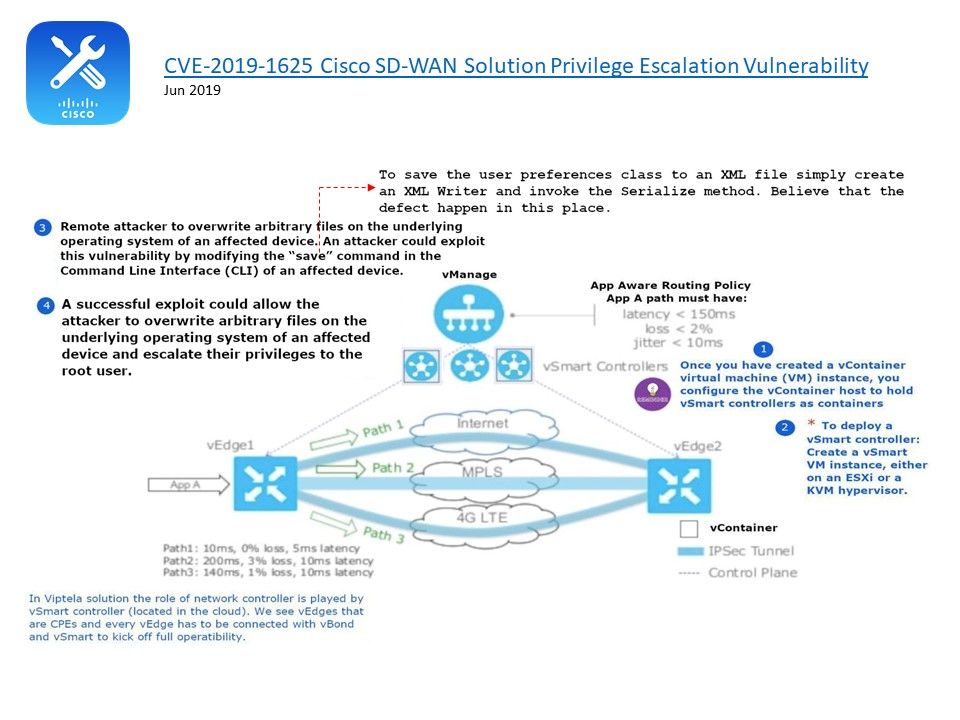
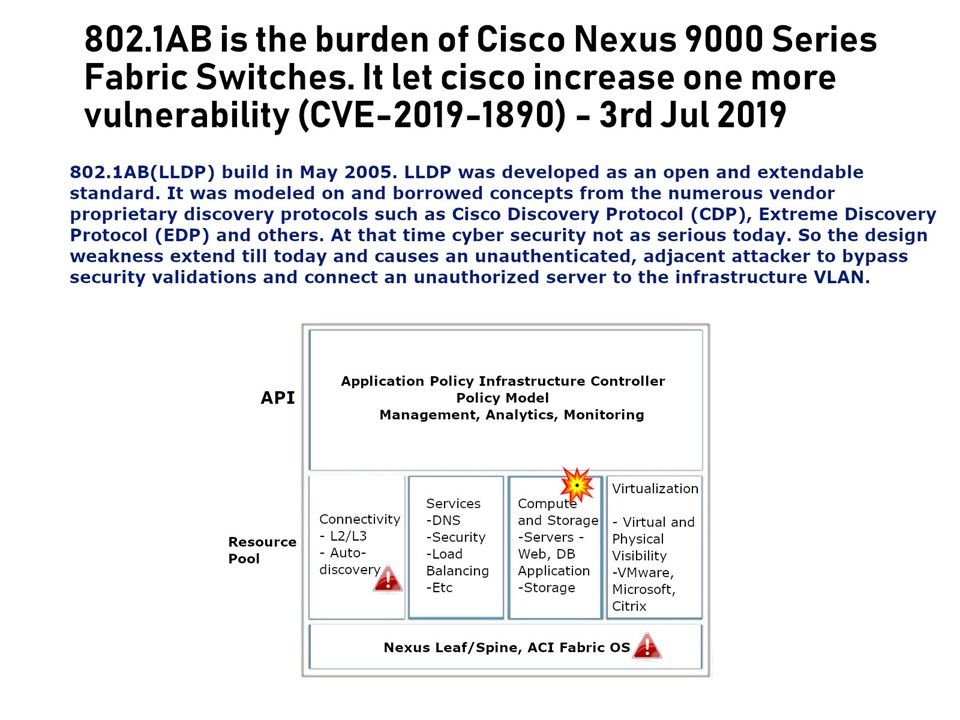
Vulnerability background & details: 802.1AB(LLDP) build in May 2005. LLDP was developed as an open and extendable standard. It was modeled on and borrowed concepts from the numerous vendor proprietary discovery protocols such as Cisco Discovery Protocol (CDP), Extreme Discovery Protocol (EDP) and others. At that time cyber security not as serious today. So the design weakness extend till today and causes an unauthenticated, adjacent attacker to bypass security validations and connect an unauthorized server to the infrastructure VLAN.
We seen the impact posted by Cisco. They state that if strict mode is configured, this vulnerability cannot be exploited. Strict mode enforces further firmware security checks before allowing a connection.
Remark: Only Cisco Discovery Protocol provides an additional capability not found in LLDP-MED that allows the switch to extend trust to the phone. That is the phone will be trusted to mark the packets received on the PC port accordingly.
Official announcement – https://tools.cisco.com/security/center/content/CiscoSecurityAdvisory/cisco-sa-20190703-n9kaci-bypass