Preface: The vendor announce that they found vulnerability on their product means they are responsible. Even though it is not a good news. But believe that it is under control.
Product background: Data Center Network Manager (DCNM) is the network management platform for all NX-OS-enabled deployments .
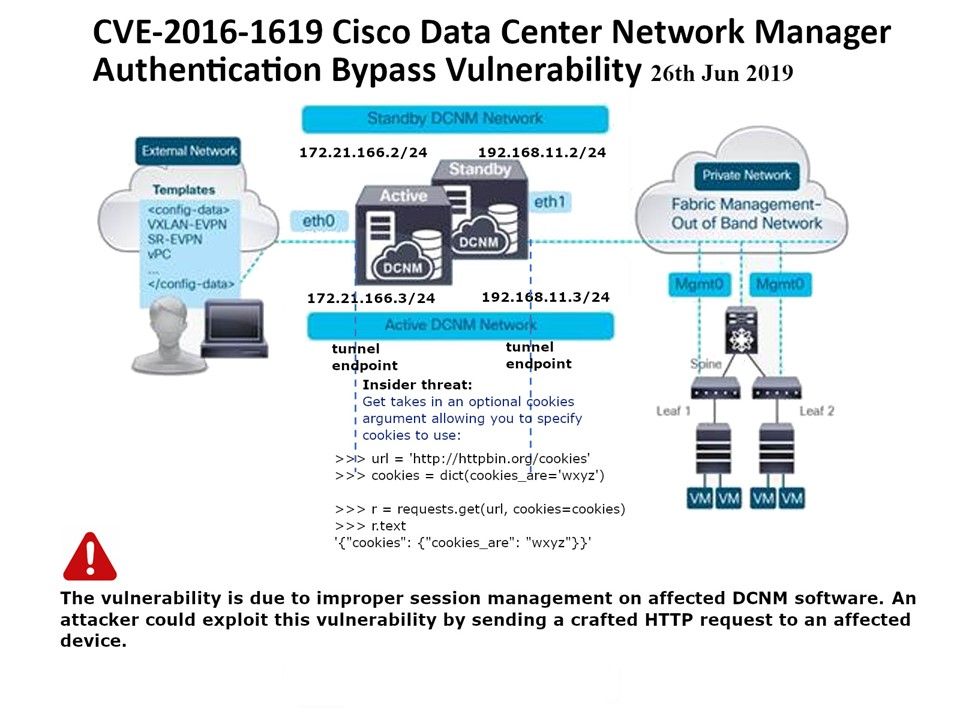
Vulnerability details: Authentication Bypass Vulnerability occurs due to improper session management. An attacker could exploit this vulnerability by sending a crafted HTTP request to the affected device. As a result it bypass credential input and receive victim login connection.
Information supplement: Why should a session be maintained? When there is a series of continuous request and response from a same client to a server, the server cannot identify from which client it is getting requests. Because HTTP is a stateless protocol. When there is a need to maintain the conversational state, session tracking is needed.
Refer to attach diagram, an hints will provide an idea to you what is happen on such design weakness.
Vendor announcement: Please refer to URL https://tools.cisco.com/security/center/content/CiscoSecurityAdvisory/cisco-sa-20190626-dcnm-bypass
Additional: Arbitrary File Upload and Remote Code Execution Vulnerability – https://tools.cisco.com/security/center/content/CiscoSecurityAdvisory/cisco-sa-20190626-dcnm-codex