Preface: Router, SD-WAN,Load-balancer, Firewall and IDS and virtual machine. Their operations are based on Linux operation system.
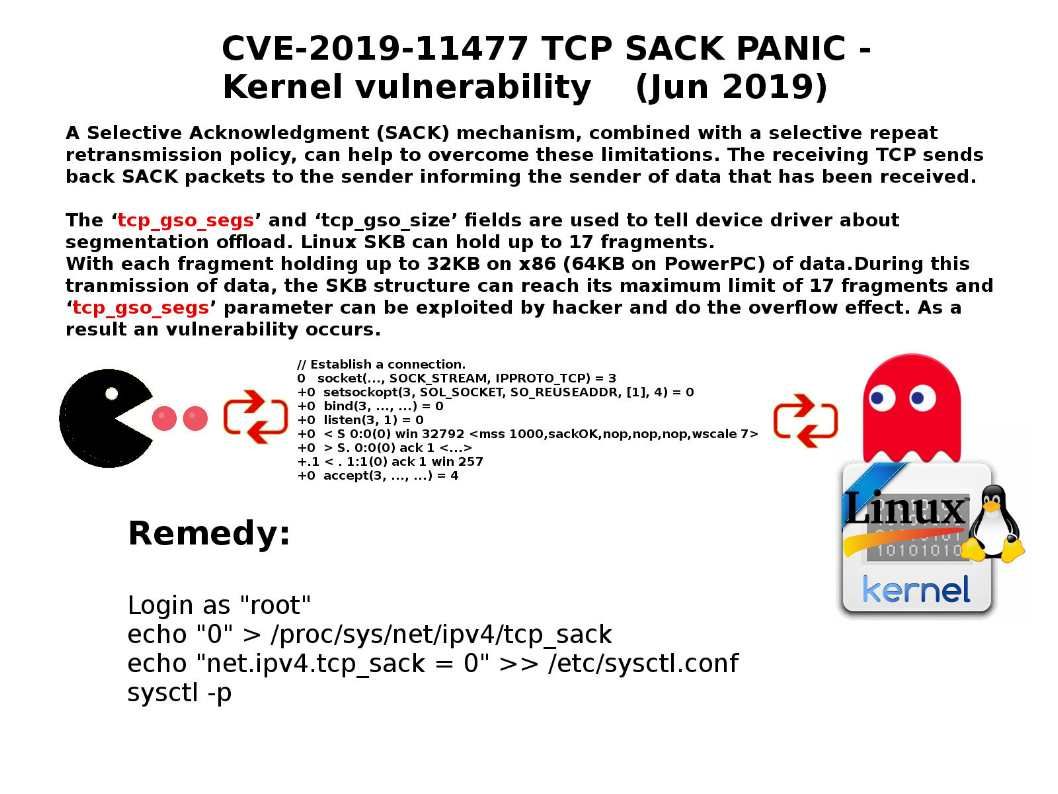
Background: A Selective Acknowledgment (SACK) mechanism, combined with a selective repeat retransmission policy, can help to overcome these limitations. The receiving TCP sends back SACK packets to the sender informing the sender of data that has been received.
Vulnerability details: The ‘tcp_gso_segs’ and ‘tcp_gso_size’ fields are used to tell device driver about segmentation offload. Linux SKB can hold up to 17 fragments.
With each fragment holding up to 32KB on x86 (64KB on PowerPC) of data.During this tranmission of data, the SKB structure can reach its maximum limit of 17 fragments and ‘tcp_gso_segs’ parameter can be exploited by hacker and do the overflow effect. As a result an vulnerability occurs.
Remedy: Login as “root”
echo “0” > /proc/sys/net/ipv4/tcp_sack
echo “net.ipv4.tcp_sack = 0” >> /etc/sysctl.conf
sysctl -p
Reference article: https://kb.cert.org/vuls/id/905115/
Status update (26th Jun 2019) – Linux SACK Panic vulnerability CVE-2019-11477 impact F5 Network. The information shows in following url. https://support.f5.com/csp/article/K78234183