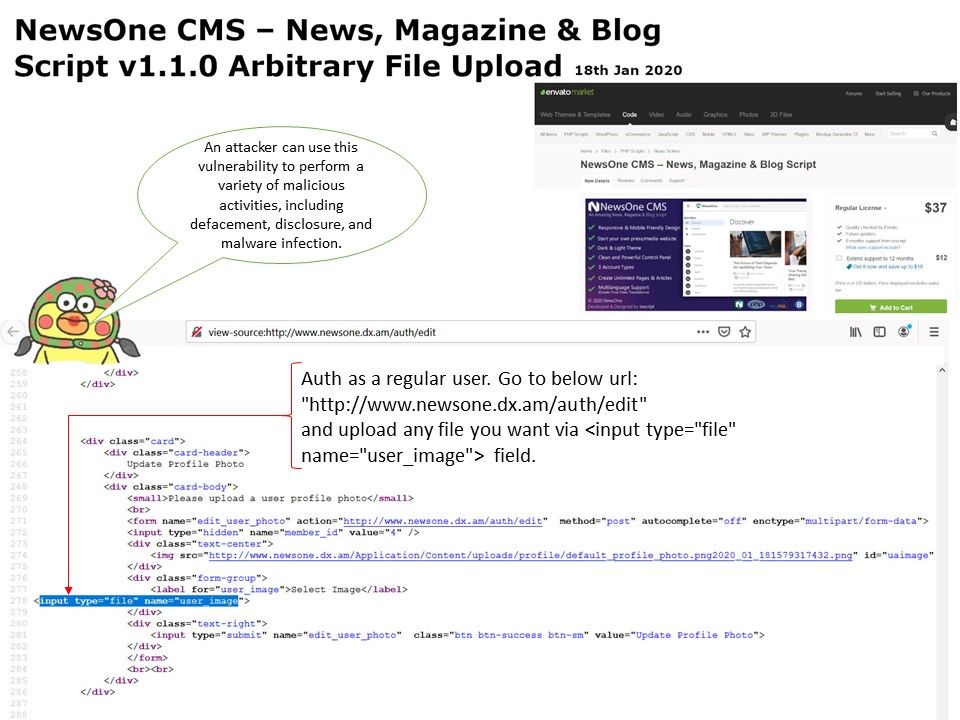
Preface: Do you have doubt for the road map of application penetration test? I believe that it is a logical step. Sometimes, you will concerning the limit time windows for remediation for different of vulnerability result. The penetration tester will narrow down the work scope especially the high risk rating vulnerability item. Since this is the highest priority job which requires customer to do the remedy.
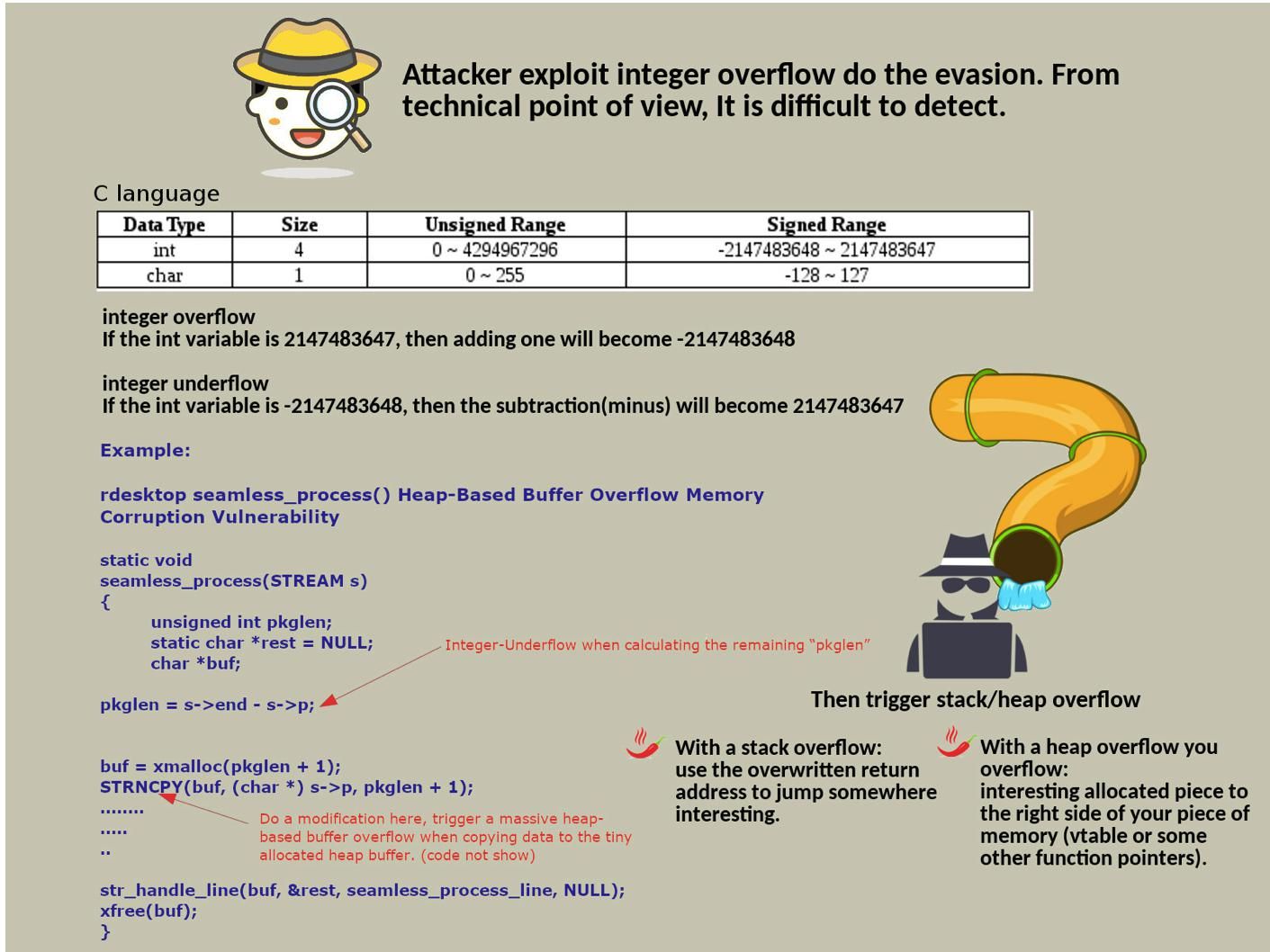
How do you deal with application vulnerabilities? I also encountered this error because the high-risk level vulnerability made me nervous. Believe it or not, whether an application system can do a good vulnerability management sometimes depends on how hard the penetration tester analyzes the collected information. Below example can let you know my statement is true.
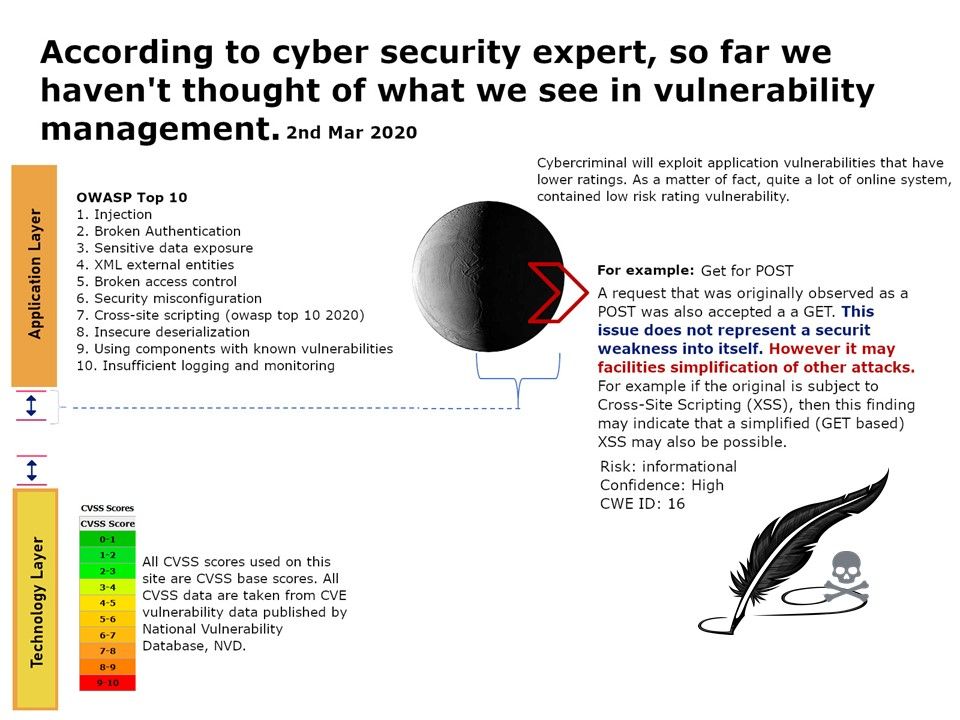
Get for POST (Risk: informational) – A request that was originally observed as a POST was also accepted a a GET. This issue does not represent a securit weakness into itself. However it may facilities simplification of other attacks. For example if the original is subject to Cross-Site Scripting (XSS), then this finding may indicate that a simplified (GET based) XSS may also be possible.
Hey Guys, don’t be worry too much. But you should be careful when you do the application penetration test report next time. Be remember that ask your consultant once you got a question.