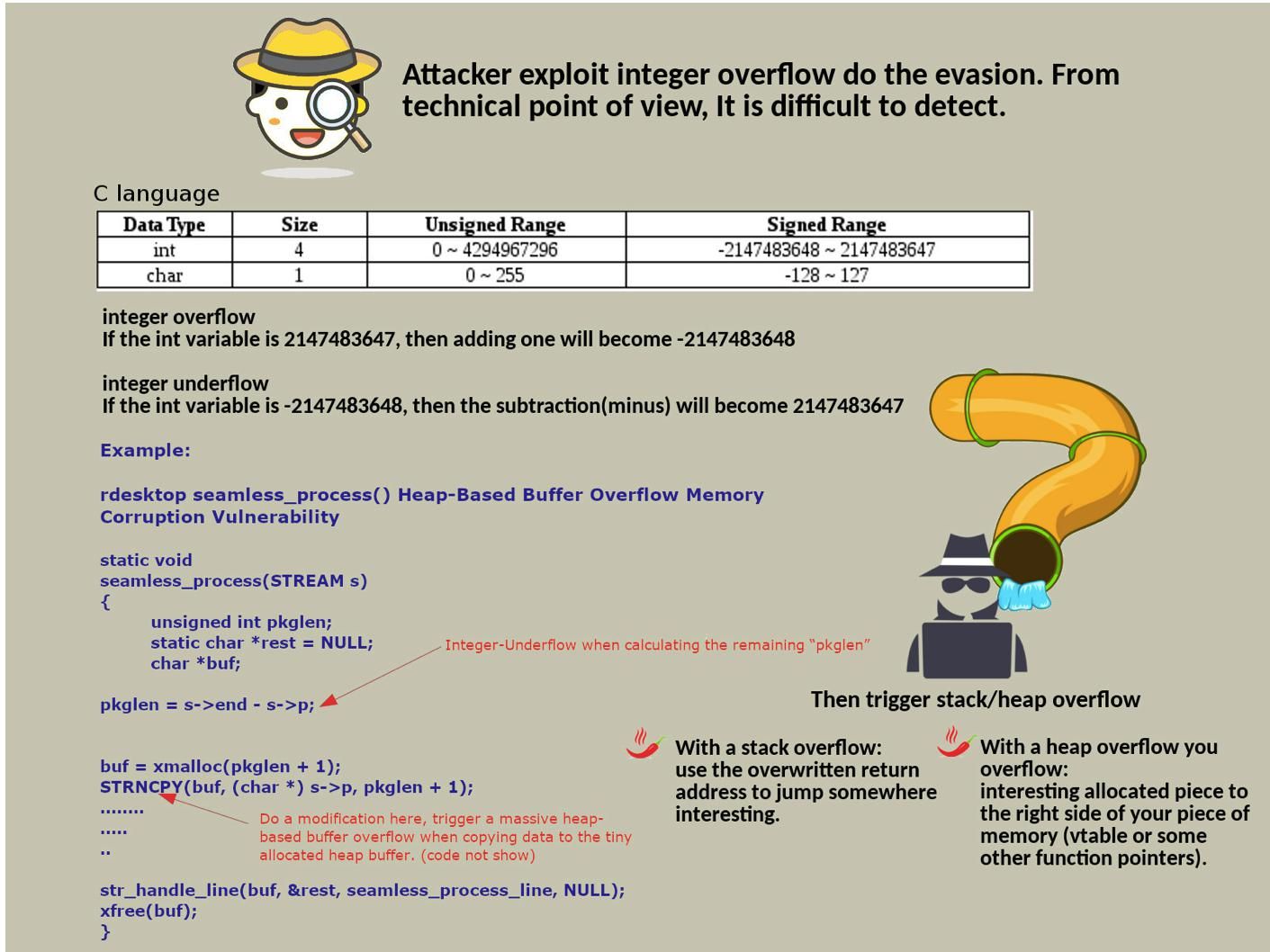
Preface: Malware detection, SIEM and predictive technology enhance the detective and preventive control in cyber security world. However the hacker still have solutions to conduct infiltration thus compromise the system. Attacker exploit integer overflow do the evasion. From technical point of view. It is difficult to detect.
Historical records of cyber attack who exploit integer overflow vulnerability:
Total 329 ethereum tokens vulnerable for integer overflow – 9th Jul 2018 – http://www.antihackingonline.com/potential-risk-of-cve/9th-jul-2018-total-329-ethereum-tokens-vulnerable-for-integer-overflow/
CVE-2018-6983 VMware Workstation and Fusion updates address an integer overflow issue – 22nd Nov 2018 – http://www.antihackingonline.com/potential-risk-of-cve/cve-2018-6983-vmware-workstation-and-fusion-updates-address-an-integer-overflow-issue-22nd-nov-2018/
CVE-2018-20181 rdesktop seamless_process() Heap-Based Buffer Overflow Memory Corruption Vulnerability – https://cxsecurity.com/cveshow/CVE-2018-20181
Observation: According to my observations, there are technical limitation on software engineering, most likely the cyber criminal keen to develop a technique sound like F117. That is invisible to radar (IDS) and infrared (SIEM). Perhaps online web application shall require user input function. Even though software developer introduce pull down menu function. However it is not able to lack of name and password input. So this is the objective we highlight today. Integer overflow technique exact can provides silent attack. As a result it form a bridge let attacker execute the 2nd phase of attack. For instance in C environment, The range of unsigned char is (0 – 255). So if the input password length is 260, it will cause integer overflow . So passwd_len actually has a length of 4, so you can bypass the length limit. If buf parameter has design limitation, stuffed 260 length of data into it, it will cause stack overflow.