Preface: Docker’s introduction of the standardized image format has fueled of interest in the use of containers in the enterprise recently. A Docker container look likes a Virtual machine.
It is without antivirus or malware detector facilities install to Docker container platform. Is that secure?
On the market, there is no such product available in the market. However if you would like to find out something 101 about preventive control. It can find on this short discussion.
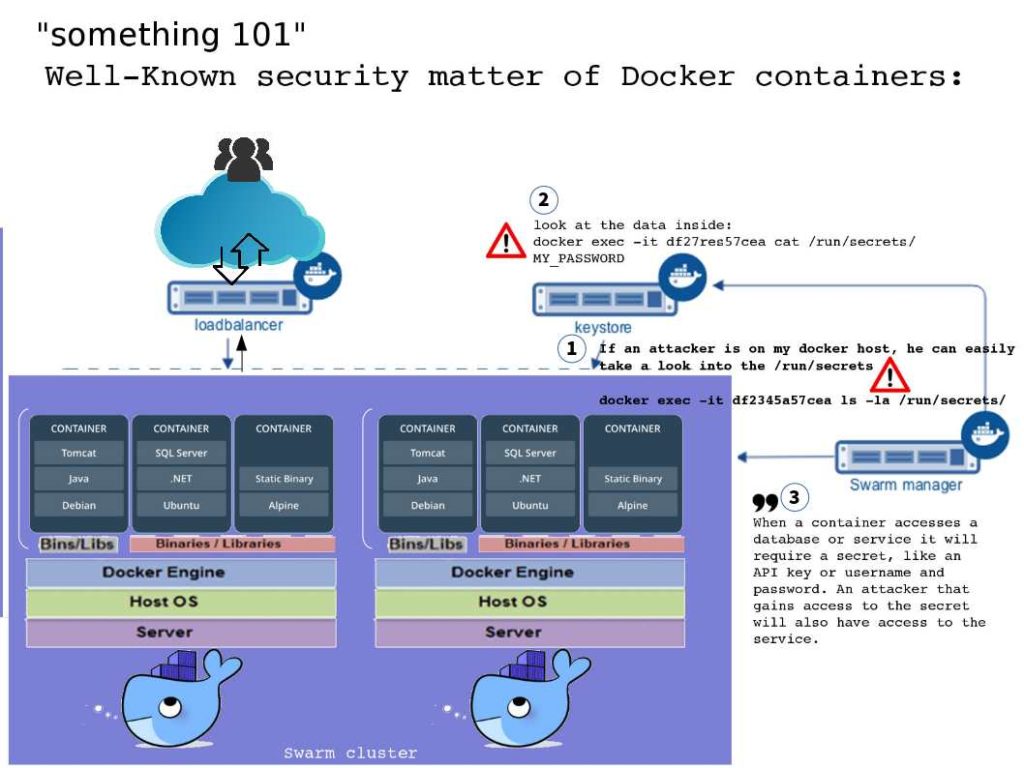
Hints: When a container accesses a database or service it will require a secret, like an API key or username and password. An attacker that gains access to the secret will also have access to the service. For more details, please refer to attached diagram.
Recommendation:
- Ensure that processes in containers do not run as root, so when attacker try to exploiting privileges command, it will be restricted by role base control.
- Cut down on the kernel calls that a container can make to reduce the potential attack surface.
So called “something 101” as usual technical details not suitable describe in long format. See whether we have chance to discuss more in future.