Preface: How is JavaScript different from Java? · Java is an OOP programming language, and Javascript is an OOP description language.
Background: JSON Web Token (JWT) is an open standard (RFC 7519) that defines a compact and self-contained way for securely transmitting information between parties as a JSON object. This information can be verified and trusted because it is digitally signed. JWT is suitable for stateless scenarios and APIs, while server-side tokens work best for session-based authentication in web applications.
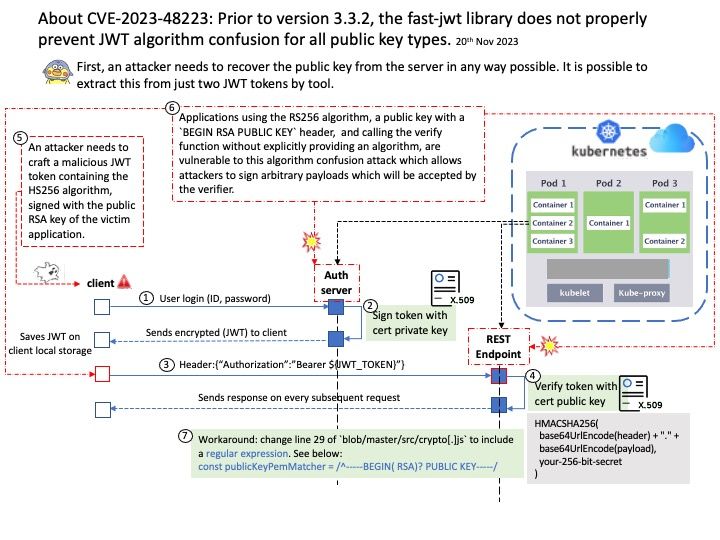
Vulnerability details: The fast-jwt provides fast JSON Web Token (JWT) implementation. Prior to version 3.3.2, fast-jwt library does not properly prevent JWT algorithm confusion for all public key types.
The ‘publicKeyPemMatcher’ in ‘fast-jwt/src/crypto[.]js’ does not properly match all common PEM formats for public keys. To exploit this vulnerability, an attacker needs to craft a malicious JWT token containing the HS256 algorithm, signed with the public RSA key of the victim application.
Attack scenario: This attack will only work if the victim application utilizes a public key containing the `BEGIN RSA PUBLIC KEY` header. Applications using the RS256 algorithm, a public key with a `BEGIN RSA PUBLIC KEY` header, and calling the verify function without explicitly providing an algorithm, are vulnerable to this algorithm confusion attack which allows attackers to sign arbitrary payloads which will be accepted by the verifier.
Solution: Version 3.3.2 contains a patch for this issue.
Workaround: As a workaround, change line 29 of `blob/master/src/crypto[.]js` to include a regular expression.
Official announcement: Official details: Please refer to the link for details – https://nvd.nist.gov/vuln/detail/CVE-2023-48223