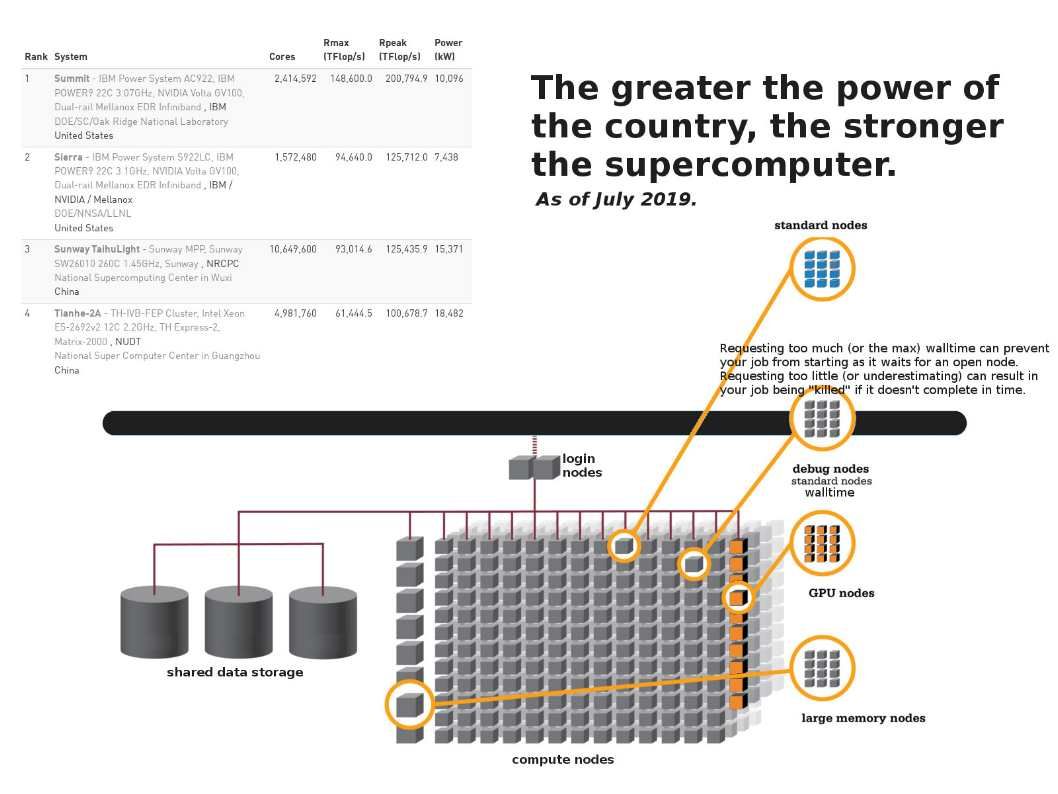
Summit, launched in 2018, delivers 8 times the computational performance of Titan’s 18,688 nodes, using only 4,608 nodes. Summit still carry the flags tell the world that he keep the fast run record.
Over the past decade, Linux Clusters founded and starting the competition with mainframe computer. The most famous IBM crossbar switch encounter doubt to technical world. Does he better than Linux Clusters? Crossbar – The processors are connected with non-internally blocking crossbar switch and communicate with each other via global interleaved memory.
The record shown on the diagram, even though the supercomputer CPU core increase 4 times compare to submit. But it do not have significant growth. Perhaps you may feeling that the bottleneck given from CPU. My personal comment is that crossbar coexists CPU and I/O direct way. Linux cluster form virtual matrix hoop up. But the design limitation is the server hardware instead of CPU. We keep our eye open to see who is the winner on next round? A crossbar switch, as part of a crossbar topology, channels data or signals between two different points in a network.
Remark: The crossbar setup is a matrix where each crossbar switch runs between two points, in a design that is intended to hook up each part of an architecture to every other part.