Preface: GS register is used to differentiate between usermode and kernel mode range of address, after adding the relevant logical address component. The instruction swapgs is used to swap the GS register with the MSR values, and only in privileged mode this can be done.
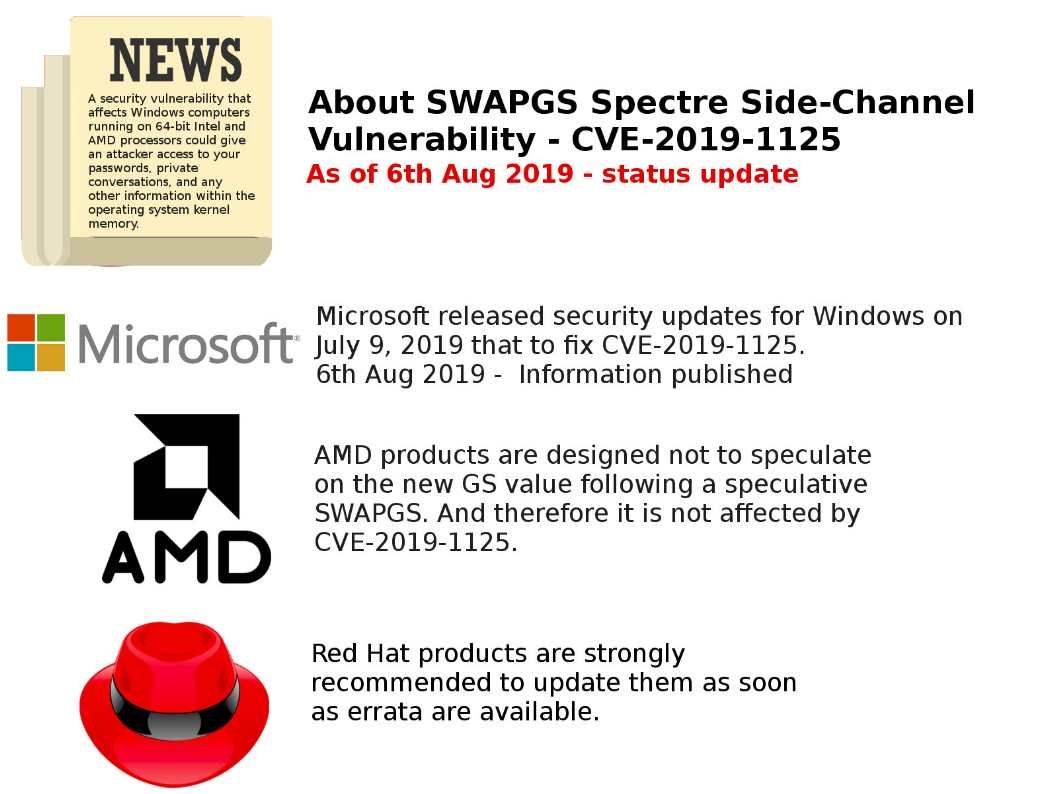
Vulnerability details: CVE-2019-1125 was made public today or also referred to as the “SWAPGS” vulnerability as a new variant of Spectre V1 affecting Intel and AMD chips under Windows and Linux operation system. The SWAPGS vulnerability allows attackers to gain read access to privileged memory and builds off existing Spectre fixes. But AMD confirmed that its products are not vulnerable to this attack. Red Hat said it needs to update the Linux kernel to prevent SWAPGS vulnerabilities from affecting Intel and AMD chips.
Microsoft official announcement: https://portal.msrc.microsoft.com/en-us/security-guidance/advisory/CVE-2019-1125
Red Hat official announcement: https://access.redhat.com/articles/4329821