Preface: Historically, telecommunications companies have been the largest customer segment for Juniper. Juniper has provided them with on-premises hardware — routers and switches — for the purpose.
Background of XML C parser:
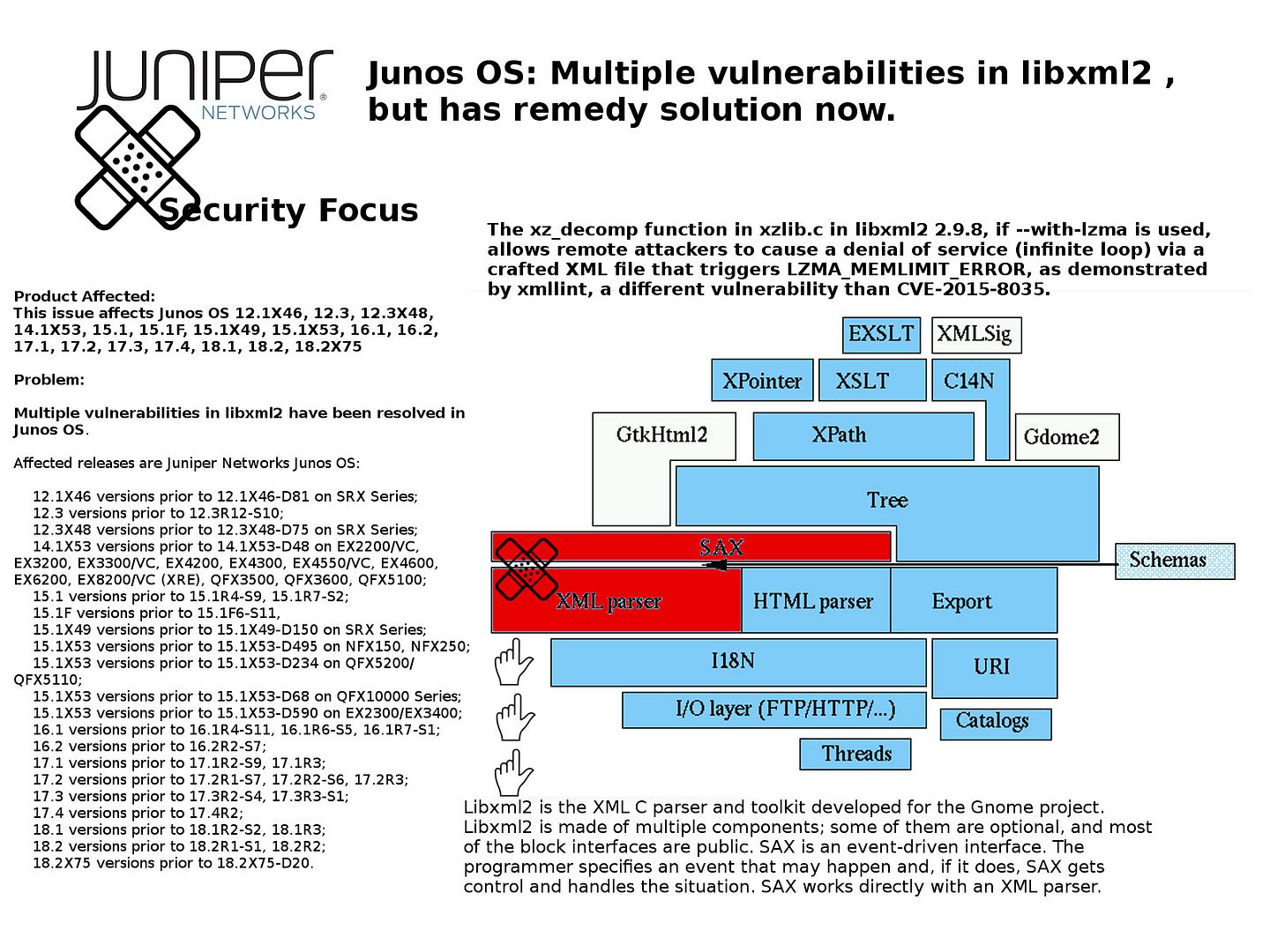
Libxml2 is the XML C parser and toolkit developed for the Gnome project. Libxml2 is made of multiple components; some of them are optional, and most of the block interfaces are public.SAX is an event-driven interface. The programmer specifies an event that may happen and, if it does, SAX gets control and handles the situation. SAX works directly with an XML parser.
Multiple vulnerabilities in libxml2:
The xz_decomp function in xzlib.c in libxml2 2.9.8, if –with-lzma is used, allows remote attackers to cause a denial of service (infinite loop) via a crafted XML file that triggers LZMA_MEMLIMIT_ERROR, as demonstrated by xmllint, a different vulnerability than CVE-2015-8035.
Solution:
For more details, please refer below url:
https://kb.juniper.net/InfoCenter/index?page=content&id=JSA10916&cat=SIRT_1&actp=LIST
Remark: Companies are moving more of their IT needs to the cloud. Traditional IT appliance business life not easy!