Preface: On 24th Oct, 2024, Researchers from Azure® Research, Microsoft® have provided to AMD a paper titled “Principled Microarchitectural Isolation on Cloud CPUs.” In their paper, the researchers describe a potential side-channel vulnerability on AMD CPUs. AMD believes that existing mitigation recommendations for prime and probe side-channel attacks remain applicable to the presented vulnerability.
Background: A two-bit saturating up-down counter is a type of counter used in computer architecture, particularly in branch prediction mechanisms. Here’s a brief overview:
- Two-bit: The counter uses two bits, allowing it to represent four states (00, 01, 10, 11).
- Up-down: The counter can increment (count up) or decrement (count down) based on the input signal.
- Saturating: The counter does not wrap around when it reaches its maximum (11) or minimum (00) value. Instead, it stays at these values if further increments or decrements are attempted.
How It Works:
- States: The counter has four states: 00, 01, 10, and 11.
- Incrementing: If the counter is at 11 and receives an increment signal, it remains at 11. Similarly, if it is at 00 and receives a decrement signal, it stays at 00.
- Usage: These counters are often used in branch prediction to keep track of the history of branch outcomes and make predictions based on this history.
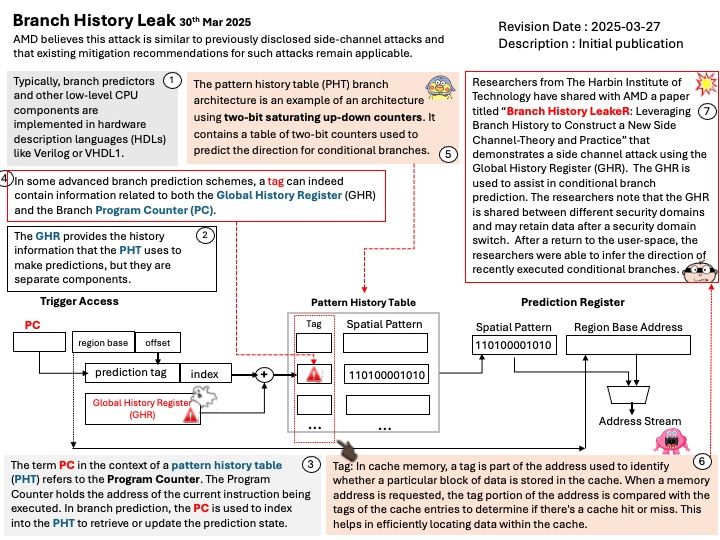
Ref: The pattern history table (PHT) branch architecture is an example of an architecture using two-bit saturating up-down counters. It contains a table of two-bit counters used to predict the direction for conditional branches.
About Branch History Leak:
Researchers from The Harbin Institute of Technology have shared with AMD a paper titled “Branch History LeakeR: Leveraging Branch History to Construct a New Side Channel-Theory and Practice” that demonstrates a side channel attack using the Global History Register (GHR). The GHR is used to assist in conditional branch prediction. The researchers note that the GHR is shared between different security domains and may retain data after a security domain switch. After a return to the user-space, the researchers were able to infer the direction of recently executed conditional branches.
Official announcement: Please refer to the link for details – https://www.amd.com/en/resources/product-security/bulletin/amd-sb-7026.html