Preface: Many enterprises have implemented Kubernetes and containers, and most also run virtual machines. This environment therefore increases operational complexity as well as time and infrastructure costs.
Background: OpenStack, libvirt, Kubernetes, Vagrant, and boot2docker are the most popular alternatives and competitors to KubeVirt. What is the difference between Kubernetes and KubeVirt? Scheduling, networking and storage are all delegated to Kubernetes, while KubeVirt provides the virtualization functionality. KubeVirt allows you to run full virtual machines on Kubernetes alongside regular containers.
WIth KubeVirt, you can declaratively:
-Create a VM
-Schedule a VM on a Kubernetes cluster
-Launch a VM
-Stop a VM
-Delete a VM
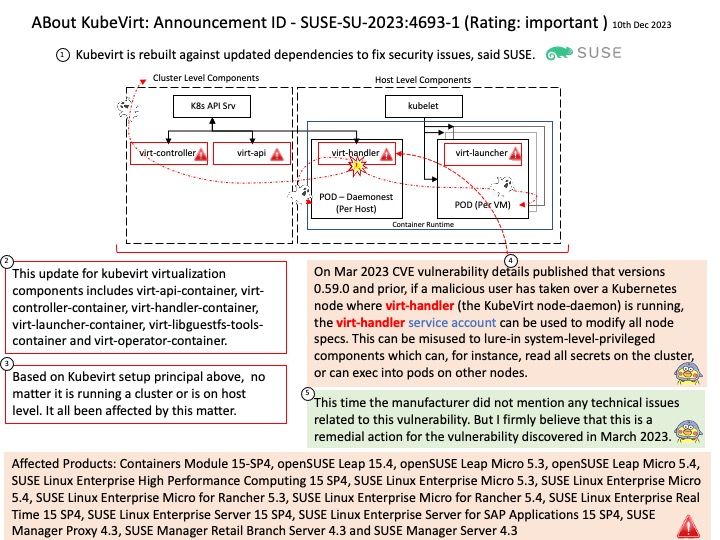
Vulnerability details: On Mar 2023 CVE vulnerability details published that versions 0.59.0 and prior, if a malicious user has taken over a Kubernetes node where virt-handler (the KubeVirt node-daemon) is running, the virt-handler service account can be used to modify all node specs. This can be misused to lure-in system-level-privileged components which can, for instance, read all secrets on the cluster, or can exec into pods on other nodes.
This time the manufacturer did not mention any technical issues related to this vulnerability. But I firmly believe that this is a remedial action for the vulnerability discovered in March 2023.
Official details: Please refer to the link for details – https://www.suse.com/support/update/announcement/2023/suse-su-20234693-1/