Preface: About fifteen years ago, extreme climate sounded the alarm for humanity. But we haven’t woken up yet. As we enter 2025, extreme weather is raging. Are we awake now?
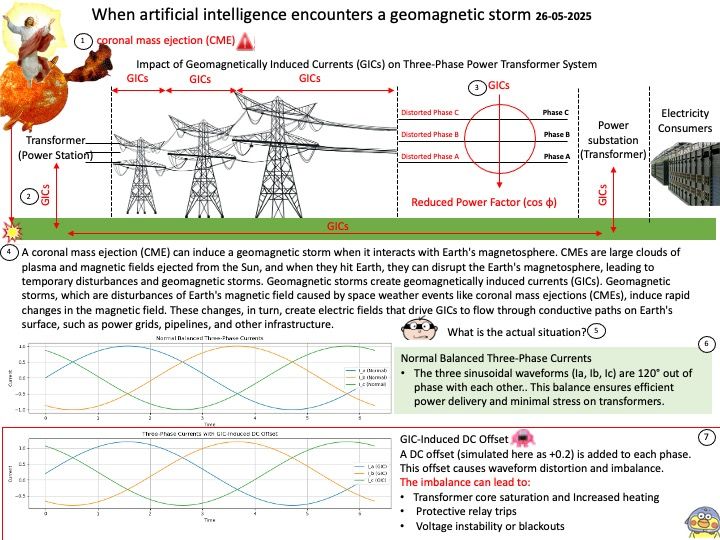
Background: A coronal mass ejection (CME) can induce a geomagnetic storm when it interacts with Earth’s magnetosphere. CMEs are large clouds of plasma and magnetic fields ejected from the Sun, and when they hit Earth, they can disrupt the Earth’s magnetosphere, leading to temporary disturbances and geomagnetic storms.
Geomagnetic storms create geomagnetically induced currents (GICs). Geomagnetic storms, which are disturbances of Earth’s magnetic field caused by space weather events like coronal mass ejections (CMEs), induce rapid changes in the magnetic field. These changes, in turn, create electric fields that drive GICs to flow through conductive paths on Earth’s surface, such as power grids, pipelines, and other infrastructure.
How much electricity does a supercomputer used for artificial intelligence consume?
A single modern AI GPU can consume up to 700 watts of power. A typical supercomputer, especially those used for AI training, can consume significantly more power, with some examples exceeding 4 megawatts (4,000,000 watts). This high power consumption is largely due to the large number of powerful GPUs and other specialized hardware needed for these complex computations.
How does artificial intelligence think about this problem?
Building a supercomputer facility underground with its own dedicated power supply does significantly reduce—but not entirely eliminate—the risks from geomagnetic storms. Here’s a breakdown:
1.Underground Location:
-Provides natural shielding from fluctuating magnetic fields.
-Reduces exposure to induced currents in long conductors.
2.Dedicated Power Supply:
-If it’s isolated from the main power grid (e.g., using local generators, batteries, or renewables), it avoids GICs that typically enter through long transmission lines.
–Shorter internal cabling means less potential for induced voltages.
3.Shielded Infrastructure:
-If the facility uses shielded transformers, GIC-blocking devices, and grounding systems, it can further mitigate risks.
End.