Preface: NVIDIA® offers a wide range of Network Operating Systems (NOS), from the homegrown Ethernet Operating System, NVIDIA Mellanox Onyx™, to native Linux operating systems, NVIDIA Cumulus Linux, and a variety of vendor specific options.
Background: NVIDIA® MLNX-OS® operating system, enables the management and configuration of NVIDIA’s InfiniBand switch system platforms.
NVIDIA MLNX-OS®, an InfiniBand switch operating system for high-performance data centers, enables you to build networks that scale to thousands of compute and storage nodes, while also providing monitoring and provisioning capabilities.
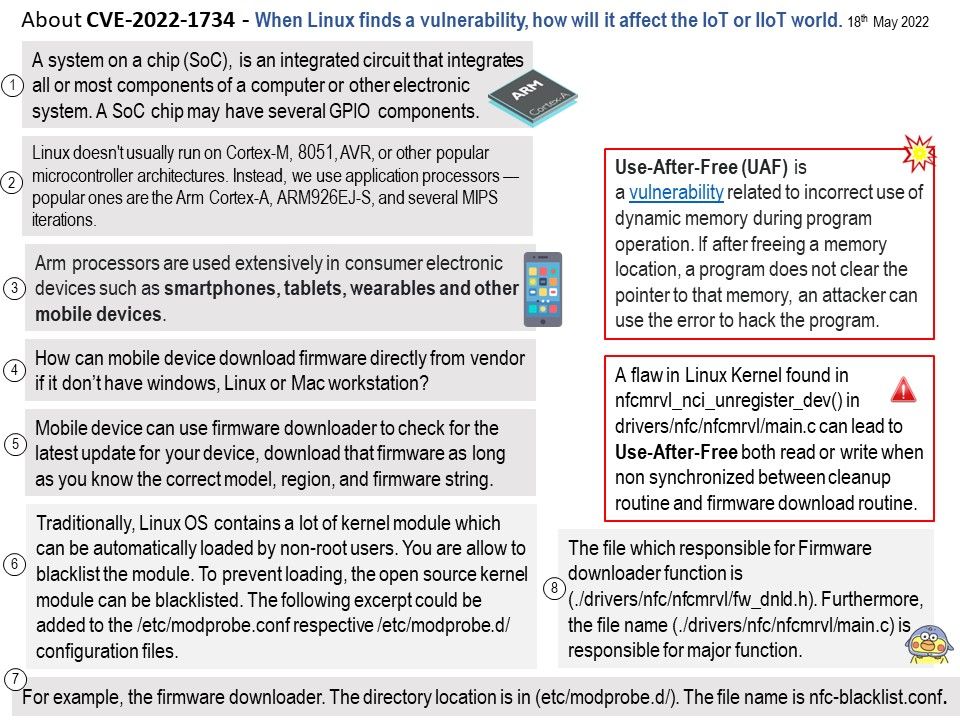
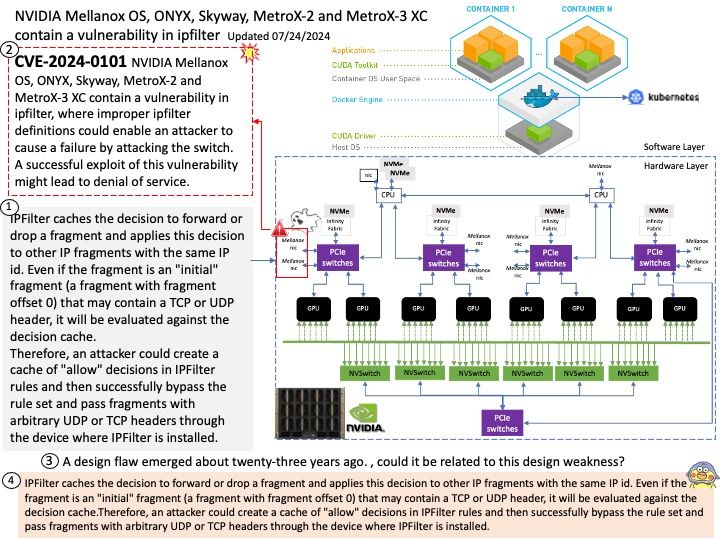
Vulnerability details: CVE-2024-0101 – NVIDIA Mellanox OS, ONYX, Skyway, MetroX-2 and MetroX-3 XC contain a vulnerability in ipfilter, where improper ipfilter definitions could enable an attacker to cause a failure by attacking the switch. A successful exploit of this vulnerability might lead to denial of service.
Ref: A design flaw emerged about twenty-three years ago. , could it be related to this design weakness?
IPFilter caches the decision to forward or drop a fragment and applies this decision to other IP fragments with the same IP id. Even if the fragment is an “initial” fragment (a fragment with fragment offset 0) that may contain a TCP or UDP header, it will be evaluated against the decision cache.Therefore, an attacker could create a cache of “allow” decisions in IPFilter rules and then successfully bypass the rule set and pass fragments with arbitrary UDP or TCP headers through the device where IPFilter is installed.
Official announcement: Please refer to the official announcement for details – https://nvidia.custhelp.com/app/answers/detail/a_id/5559