Is it anti-tradition? IT folks, do you white list ifferfsodp9ifjaposdfjhgosurijfaewrwergwea[.]com. Expert was told, the strange design of Wannacry will stop spread the ransomware to known subnet once he can get in touch with his C&C server. But do you think this is a trap? I speculated that ramsomware intend to create this trap fool the guy who think this is a solution and then can easy go to their internal network in 2nd phase. So the better idea is that do not input this domain into your whitelist. Cheers!
Information update on 18th May 2017
Recently Wana Decrypt0r 2.0 C&C server:
- 57g7spgrzlojinas.onion
- xxlvbrloxvriy2c5.onion
- 76jdd2ir2embyv47.onion
- cwwnhwhlz52maqm7.onion
Wana Decrypt0r 2.0 modify the Windows Registry Editor and target the following sub-keys:
HKCU\Software\Microsoft\Windows\CurrentVersion\Run\
HKCU\Software\WanaCrypt0r\
HKCU\Software\WanaCrypt0r\wd
HKCU\Control Panel\Desktop\Wallpaper
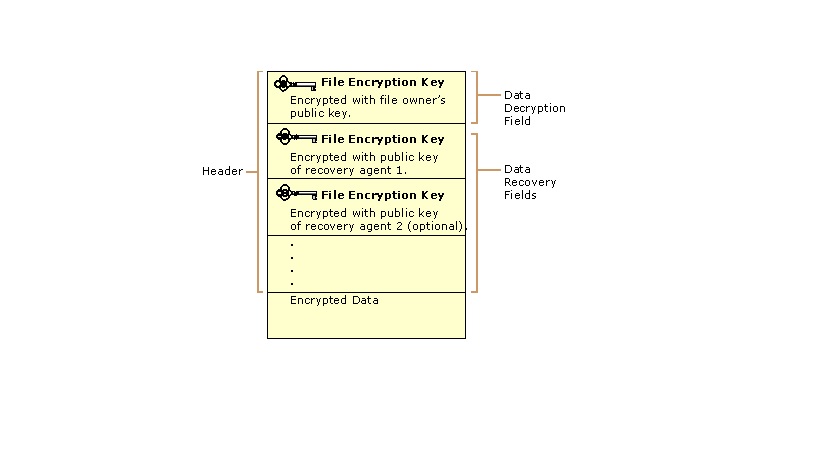
Encryption algorithms:
- AES (Advanced Encryption Standard) 128 – cannot be decrypted the file until you receive the FEK (File Encryption Key). This key may be the only method to decrypt the files .
Structure of an Encrypted File
Rivers-Shamir-Adleman or RSA – Wanncry design objective intent to generate unique public and private keys for each of the files. This makes the decryption of each file separate and very difficult and unique process.
Observation:
Attention: If no data backup on hand, it is hard to say pay the ransom is the solution. Since WanaCrypt0r .WNCRY contained extreme destroy concept and enforce to delete the shadow volume copies and eradicate all chances of reverting your files via backup on the infected computer (see below destroy scenario command syntax). The security concern is that it is hard to guarantee that it is virus free after hard disk encrypt on victim machine. As a matter of fact, WannCry via an Exploit kit, Dll file attack, malicious JavaScript or a drive-by download of the malware. No evident to proof that WannCrypt0r will remove his footprint after victim pay the ransom and therefore victim machine still vulnerable until execute a low level format of the hard disk and reinstall all the application. But it is hard to tell at this moment. Therefore it must be handle the data carefully after you pay the ransom.
The extreme destroy command syntax are shown as below:
- vssadmin delete shadows /all /quiet2.
- wmic shadowcopy delete
Remark: At user level below command can do in the following step: Go to Start Menu-All Programs-Accessories,then right-click Command Prompt and select Run As Administrator,because Administrative privileges are required to use BCDEdit to modify BCD
3. bcdedit /set boostatuspolicy ignoreallfailures
4. bcdedit /set {default} recoveryenabled no & wbadmin delete catalog -quiet
Hints and Resolution found on 19th May 2017
Hints that Windows 7, XP, Windows 2003 (x86 confirmed), Vista and 2008 and 2008 R2 instead of Windows 10 . The OS itself keeps a copy of the two prime numbers that it provided to WannaCry in memory. Those primes can be recovered. It is possible to relies on this feature to compute the encryption key and then used to decrypt all encrypted data. A tool make use of above criteria and might have way to decrypt your data. For more details, please refer to below url for reference.
https://github.com/aguinet/wannakey
If above hints can’t help and you would like to keep the encrypted data. You can do the following.
Backup all your files (00000000.eky and remaining files). May be in future, there is new resolution which provide the key decrypt your data.