Preface: The addition of a forged TCP packet to an existing TCP session. Can only be performed on unsecured sessions (not HTTPS).
About Oracle Critical Patch Update – July 2020 : When I open the related Oracle article. It was amazing that containing a whole bunch of vulnerability details. Meanwhile I had headache that how to conduct my analysis in correct way. As usual, Oracle do not want to disclose the details on vulnerability, may be this is the company policy!
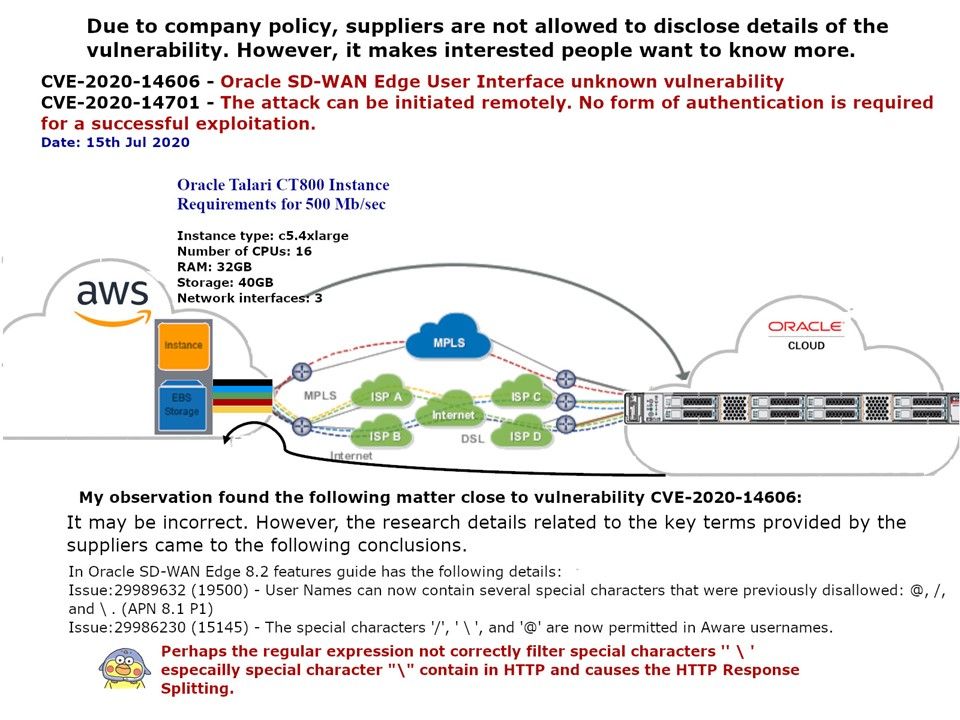
In short, I had did research and analytic on SD WAN topic. As mentioned, the data provided by vendor not clear and therefore I did the analytic and summarize my findings based on below circumstances. My observation found the following matter close to vulnerability (CVE-2020-14606).
In Oracle SD-WAN Edge 8.2 features guide has the following details:
Issue:29989632 (19500) – User Names can now contain several special characters that were previously disallowed: @, /, and \ . (APN 8.1 P1)
Issue:29986230 (15145) – The special characters ‘/’, ‘ \ ‘, and ‘@’ are now permitted in Aware usernames.
Speculation: Perhaps the regular expression not correctly filter special character “\” especially special character “\” contain in HTTP and causes the HTTP Response Splitting.
For the rest of the vulnerabilities, please refer to the link – https://www.oracle.com/security-alerts/cpujul2020verbose.html