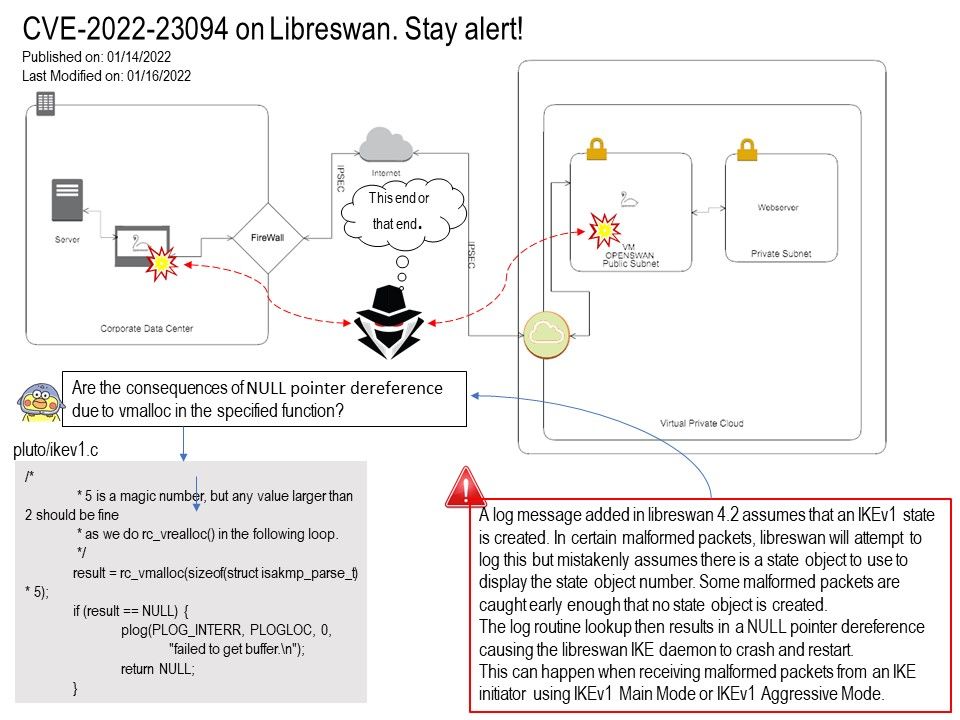
Preface: Pluto is an IKE (“IPsec Key Exchange”) daemon. Pluto is an implementation of IKE. It runs as a daemon on a network node. Currently, this network node must be a LINUX system running the KLIPS
or NETKEY implementation of IPsec, or a FreeBSD/NetBSD/Mac OSX system running the KAME implementation of IPsec.
Background: Libreswan is a free software implementation of the most widely supported and standardized VPN protocol using “IPsec” and the Internet Key Exchange (“IKE”). Most IPsec deployments fall into two types of deployment. The first type is the Remote Access, where roaming users (phones, laptops) connect to the corporate network. The second type of IPsec network is where two or more IPsec gateways connects different networks together.
Is Libreswan safe? This open-source VPN is secure if you’re a Linux user since it uses a built-in “XFRM” IPsec stack and DDNS crypto library. The VPN is compatible with Linux distribution such as RHEL/EPEL, Arch Linux, and Fedora.
What is xfrm interface?
The design of virtual xfrm interfaces interfaces was discussed at the Linux IPsec workshop 2018. This patchset implements these interfaces as the IPsec userspace and kernel developers agreed. The purpose of these interfaces is to overcome the design limitations that the existing (Virtual Tunnel Interfaces) VTI devices have.
Vulnerability details: According to vendor announcement. Libreswan 4.2 through 4.5 allows remote attackers to cause a denial of service (NULL pointer dereference and daemon crash) via a crafted IKEv1 packet because pluto/ikev1[.]c wrongly expects that a state object exists.
Observation: Are the consequences of NULL pointer dereference due to vmalloc in the specified function?
Mitigation: If all configured connections are using IKEv2, the IKEv1 subsystem can be disabled by adding the option ikev1-policy=drop to the “config setup” section of ipsec[.]conf. Alternatively, libreswan can be compiled with USE_IKEv1=false.
OR Install version 4.6.
Official announcement: For details of the official announcement, please see the homepage – https://libreswan.org/
.jpg?width=1920&height=1080&fit=bounds)
.jpg)