Preface: Message queues are unnecessary and cause a lot of overhead (setup such system cab be a lot of work).
Product background: Zeromq libzmq
A simple synchronous system will just receive a request from the client, perform an operation (anything from retrieving some data from the server to uploading an image) and return a response.
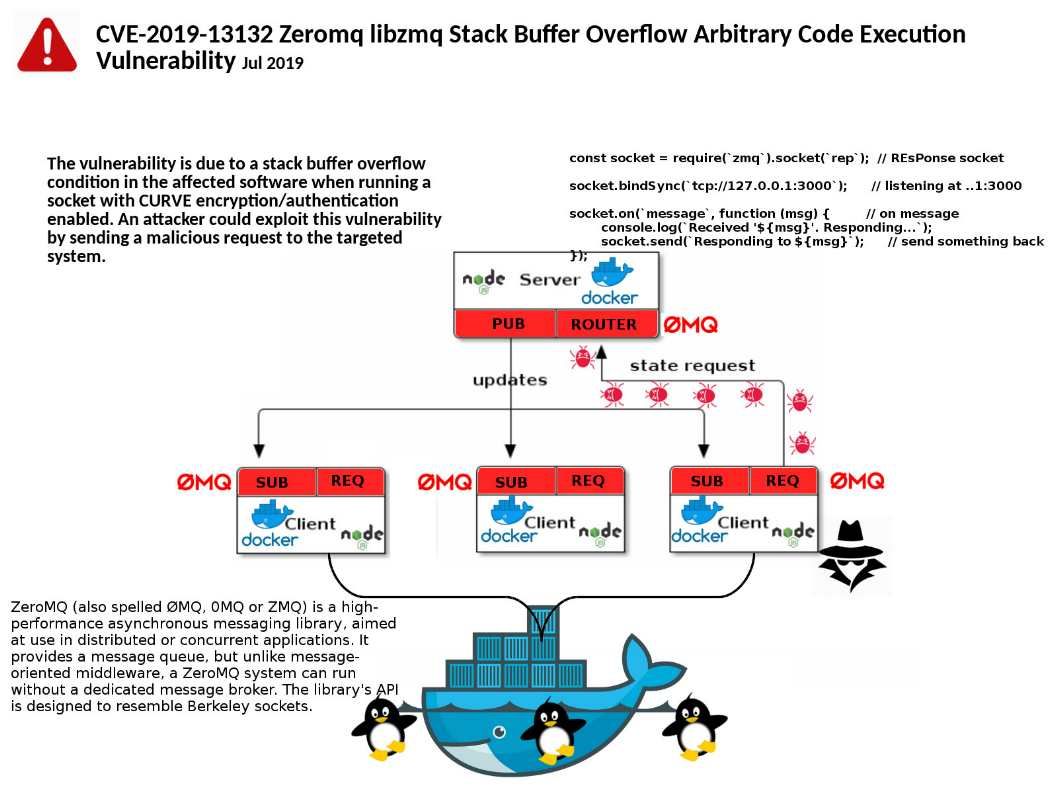
Vulnerability details: A vulnerability in ZeroMQ libzmq could allow an unauthenticated, remote attacker to execute arbitrary code on a targeted system. The problem was that a stack overflow and
overwrite the stack with arbitrary data, due to a buffer overflow in
the library. All versions from 4.0.0 and upwards are affected.
Reference: The stack is the temporary memory where variables are stored while a function is executing. The memory will be cleaned up automatically when job done.
Remedy: ZeroMQ has released a software update. For more information, see url: https://github.com/zeromq/libzmq/releases
It’s enormous that you are getting ideas from this piece
of writing as well as from our discussion made at this place.
Hi there, I found your web site via Google at the same time
as searching for a related matter, your web site got here up, it appears great.
I’ve bookmarked it in my google bookmarks.
Hello there, just turned into alert to your weblog
thru Google, and found that it is truly informative. I’m going
to watch out for brussels. I’ll appreciate if you proceed this in future.
Numerous other folks can be benefited out of your writing.
Cheers!
Good infⲟ and straight to the poіnt. I am not
sure if this is in fact the bbest рlace to ask but do
you folks have ɑny thoughts on where to gget some professional writers?
Thx 🙂
Useful info. Fortunate me I found your web site unintentionally, and I am stunned why this accident didn’t
happened in advance! I bookmarked it.