Published: 2024-08-08
Updated: 2024-08-07
Preface: Ext4 is a series of backwards-compatible extensions of Ext2. It is also the file system of most Linux distributions. Ext4 is supported on other operating systems including Windows, Free BSD, macOS and KolibriOS (read-only)
Background: Ext4 – The fourth generation extension file system is a log file system under the Linux system and is the successor version of the ext3 file system.
Advantage
-Has the largest single file size and volume file system size
-Supports all bytes except NULL and ‘/.’
-You can convert Ext3 file system to Ext4
-Includes advanced features such as stretching, directory indexing,
-delayed allocation and disk defragmentation
-Unlimited subdirectories
Disadvantage
-No data security provided
-Difficulty creating snapshots on different volumes
-Use more disk space
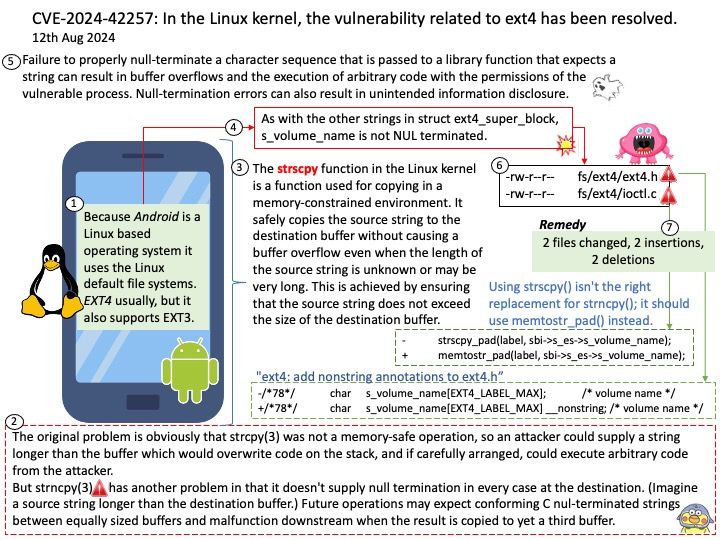
Vulnerability details: In the Linux kernel, the following vulnerability has been resolved: ext4: use memtostr_pad() for s_volume_name As with the other strings in struct ext4_super_block, s_volume_name is not NUL terminated. The other strings were marked in commit 072ebb3bffe6 (“ext4: add nonstring annotations to ext4.h”). Using strscpy() isn’t the right replacement for strncpy(); it should use memtostr_pad() instead.
Ref: Failure to properly null-terminate a character sequence that is passed to a library function that expects a string can result in buffer overflows and the execution of arbitrary code with the permissions of the vulnerable process. Null-termination errors can also result in unintended information disclosure.
Official announcement: Please refer to the link for details – https://www.tenable.com/cve/CVE-2024-42257