SIEM functions play an important role in the IT infrastructure. And therefore the security architect plan to design the SIEM not only focusing for log collection, correlation, alert and report templates. Meanwhile, a critical item must be added to the design objective. That is how to hidden your SIEM. For instance, hacker target most likely is the IT admin or CSO because they have confidental data or priviligies ID on hand. Besides, hacker also interest of the SIEM operation.
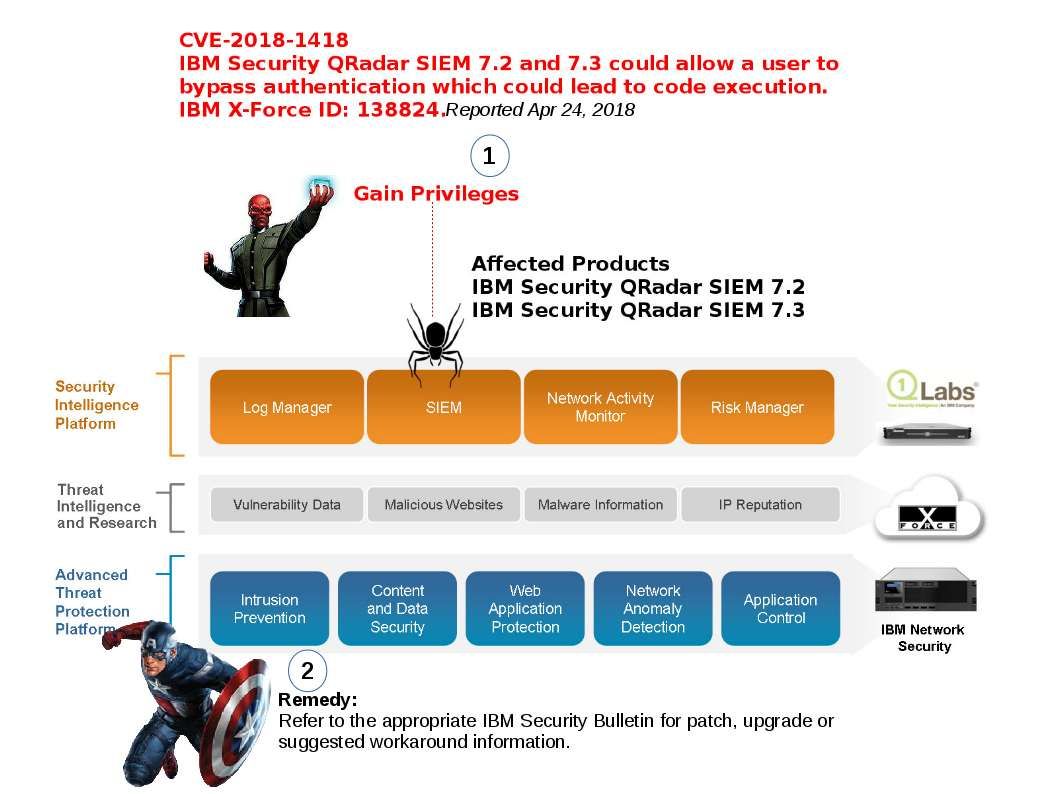
IBM Q Radar announce that a vulnerability occurs in their SIEM. Q-Radar admin must stay alert!
Since IBM do not mention what is the possible cause of this vulnerability.
Reveiw their windows log event collection method. My speculation is shown as below:
QRadar requires XPath query to communcation with windows server.
An XPath query is a log source parameter that filters specific events when the query communicates with a Windows 2008 or newer event log.
The XPath injection also leads to extracting document structure and modify the document information in addition to escalate privileges.
For more details. please see below url for reference.
CVE-2018-1418 – IBM Security QRadar SIEM privilege escalation