Preface: We might have had a debate about the definition of a powerful-enough computer to be called a supercomputer or HPC system.
Technical background:
When Docker creates a container, it creates a new instance of the above six namespaces, and then puts all the processes in the container into these namespaces, so that processes in the Docker container can only see isolated system resources.
A process is visible to other processes in its PID namespace, and to the processes in each direct ancestor PID namespace going back to the root PID namespace.
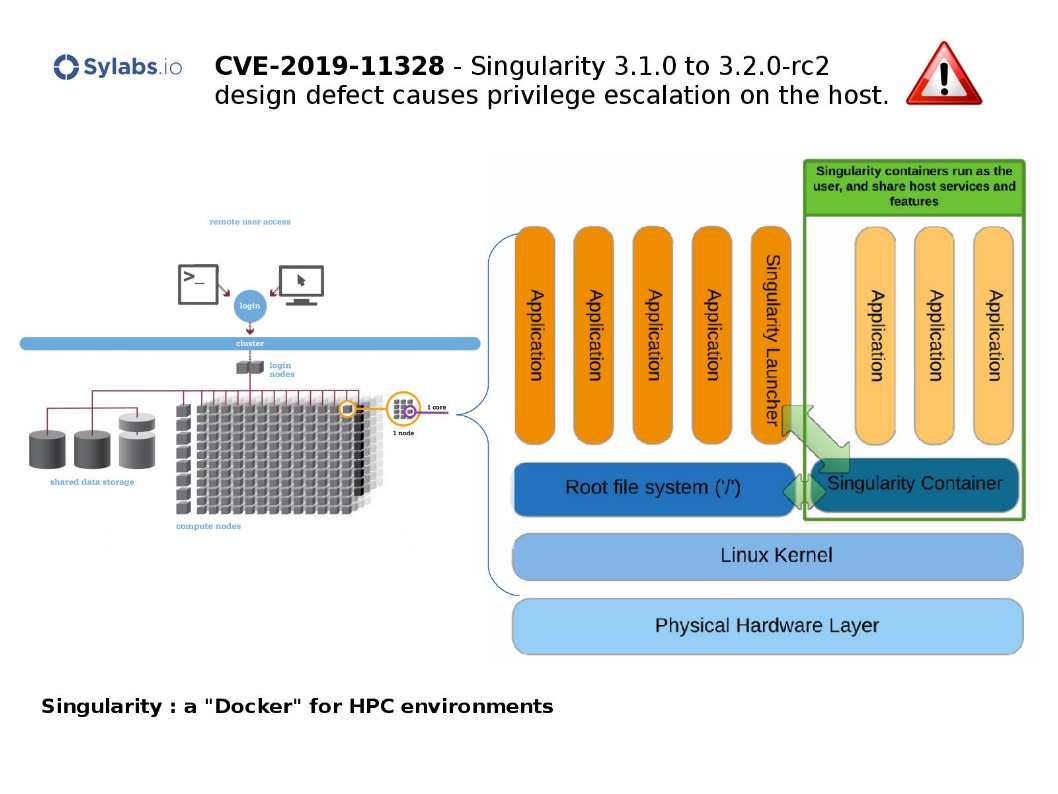
Vulnerability details: A malicious user with local/network access to the host system (e.g. ssh) could exploit this vulnerability due to insecure permissions allowing a user to edit files within /run/singularity/instances/sing//. The manipulation of those files can change the behavior of the starter-suid program when instances are joined resulting in potential privilege escalation on the host.
Remedy: Official announcement via following link – https://github.com/sylabs/singularity/releases/tag/v3.2.0