http://img.photobucket.com/albums/v704/chanpicco/chanpicco070/SSL-bug_zpslno4rp1z.jpg
Background Story:
POODLE attack exploit SSL 3.0 vulnerability found in late 2014, such vulnerability proven that hacker can take this vulnerability advantages execute man-in-the middle attack.
The original POODLE attack is CVE-2014-3566.
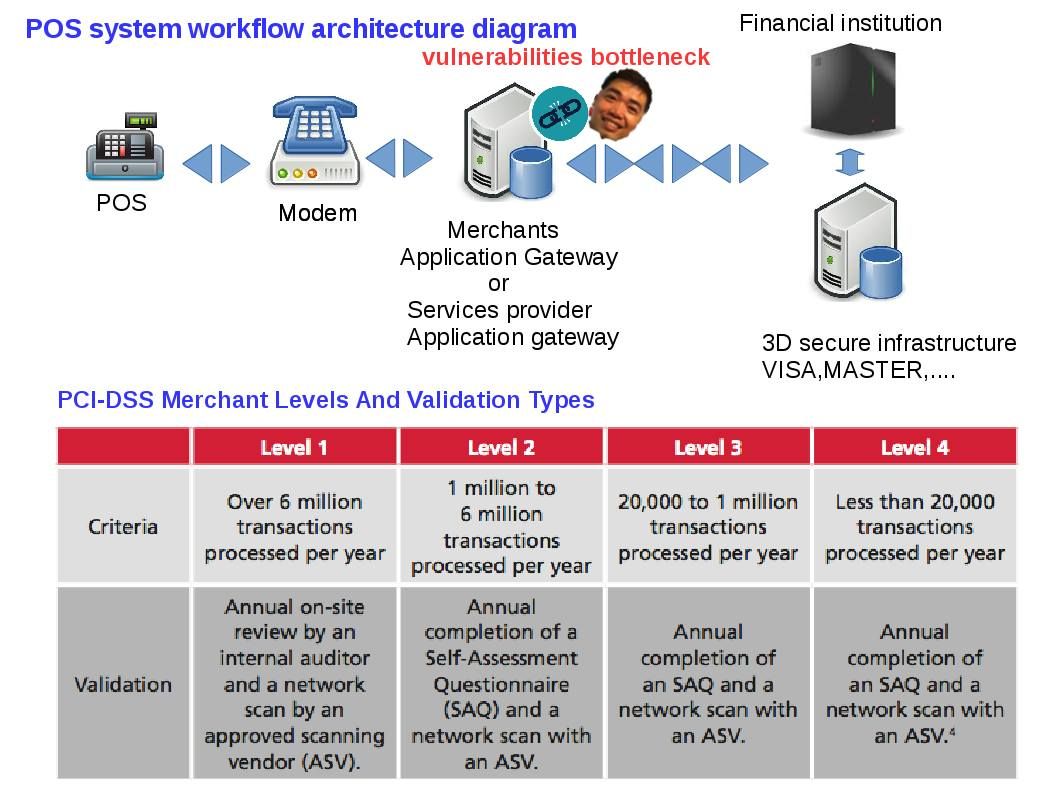
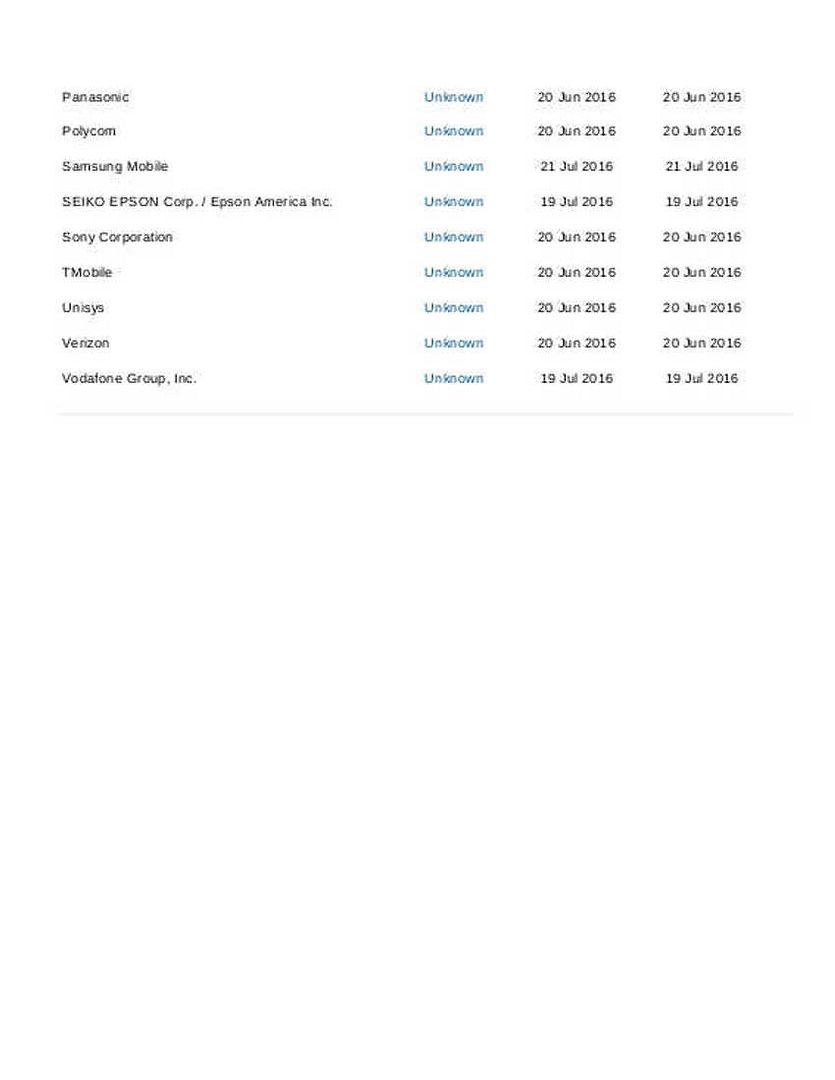
F5 Networks files CVE-2014-8730 proof POODLE attack also apply to transport layer security. Since the poodle side effects looks widely spread out, Payment card industry authority alerts and announce that they gives 14 months to merchants fix this high risk SSL problem. That means the appropriate way is replacing the SSL function (see below statement).
SSL and early TLS are not considered strong cryptography and cannot
be used as a security control after 30th June, 2016. Prior to this date, existing
implementations that use SSL and/or early TLS must have a formal Risk Mitigation and Migration Plan in place.
Effective immediately, new implementations must not use SSL or early TLS.
POS POI terminals (and the SSL/TLS termination points to which they connect)
that can be verified as not being susceptible to any known exploit
s for SSL and early TLS may continue using these as a security control after 30th June, 2016.
About the subject matter ( Cisco ASA software IKEv1 and IKEv2 buffer overflow vulnerability (CVE 2016-1287)
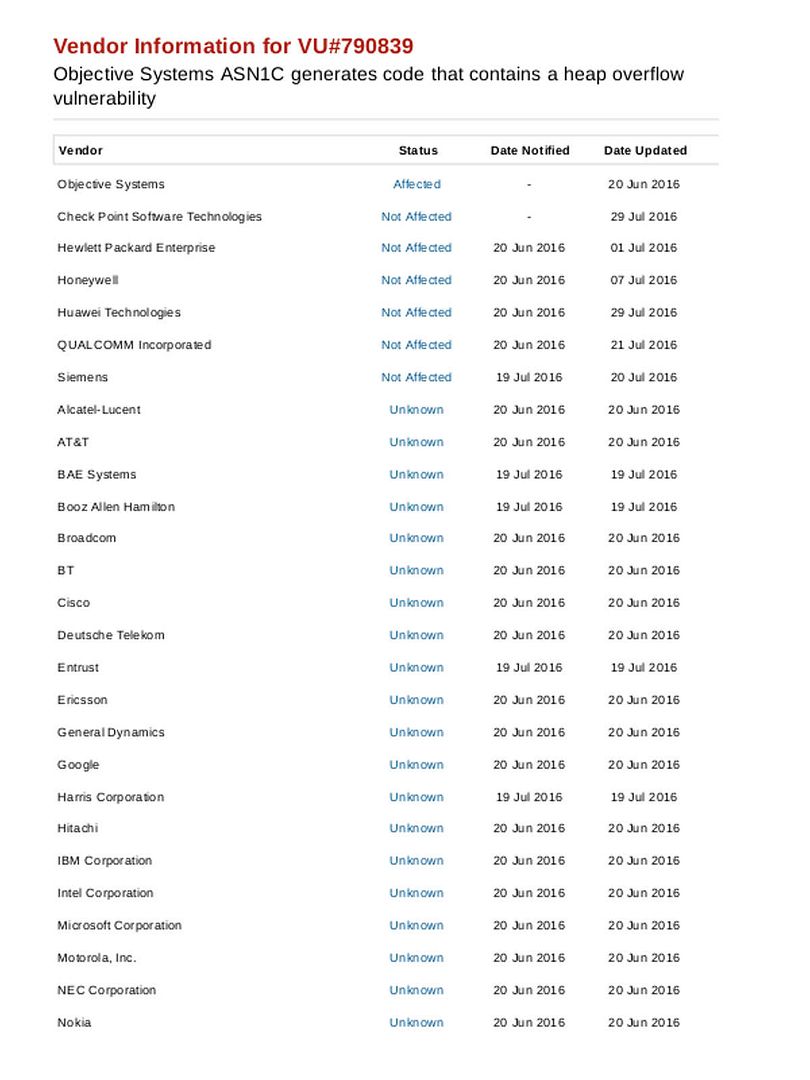
CVE 2016-1287 was published Feb this year, the founding was that hacker can make use of IKEv1 and IKE v2 vulnerabilities execute a fragmentation heap buffer overflow. The traditional heap overflow is a form of buffer overflow. It happens when a chunk of memory is allocated to the heap and data is written to this memory without any bound checking being done on the data. Regarding to the information provided by Cisco, such vulnerability affected to Cisco ASA Software running on the following products.
- Cisco ASA 5500 Series Adaptive Security Appliances
- Cisco ASA 5500-X Series Next-Generation Firewalls
- Cisco ASA Services Module for Cisco Catalyst 6500 Series Switches and Cisco 7600 Series Routers
- Cisco ASA 1000V Cloud Firewall
- Cisco Adaptive Security Virtual Appliance (ASAv)
- Cisco Firepower 9300 ASA Security Module
- Cisco ISA 3000 Industrial Security Appliance
But information supplement posted by Cisco bring to my attention. See below:
Cisco ASA Software is not affected by this vulnerability if the system is configured to terminate only the following VPN connections:
Clientless SSL
AnyConnect SSL
My understanding is that you can avoid such vulnerability occurs on Cisco products if you are using SSL 3.0 solution. But how about the PODDLE attacks? Besides, this buffer overflow on IKEv1 and IKEv2 looks not limit to Cisco brand name. May be it does not proof or found in the moment. As far as we know, firewall appliances operartion system build by Linux normally. The vendor hardening the OS and add their proprietary applications on top. If attacker can send crafted UDP packets to the affected CISCO products. Is there any possibilities engage similar attacks to other similar OS platform firewall?
Expert analysis on weakness of design
The IKE protocol uses UDP packets, usually on port 500, and generally requires 4–6 packets with 2–3 turn-around times to create an SA on both sides. The negotiated key material is then given to the IPsec stack. If an attacker can send crafted UDP packets to the related firewall products. It looks that similar vulnerability might occurs? The side effects looks serious. The following areas are vulnerable.
- LAN-to-LAN IPsec VPN
- Remote access VPN using the IPsec VPN client
- Layer 2 Tunneling Protocol (L2TP)-over-IPsec VPN connections
- IKEv2 AnyConnect
Expert solution:
(薑越老越辣) The older you get the more experienced you are,Chinese mantra said. The potential damage of this vulnerability was that both two entities (access control and VPN functions) are seat in the same box. If we define separation of functions might mitigate this risk. That is relocate the VPN feature to another box. Do you still remember that the Father of firewall (Checkpoint). Their Firewall design framework was that access control and policy server are running in different boxes. The designer foresee that a single point of failure causes compromise of whole defence system. The cyber world atmosphere has been changed after Unified Threat Management appears in the world. As times go by, maybe new generation of firewall coming soon. Hardware are cheap today. Multi layer functions setup is the fashion cope with advanced cyber threats.
Cisco technical article in regards to CVE 2016-1278
https://tools.cisco.com/security/center/content/CiscoSecurityAdvisory/cisco-sa-20160210-asa-ike
PCI – standard : SSL and early TLS are not considered strong cryptography and cannot be used as a security control after 30th June, 2016. Please refer to attached document (PCI requirement 2.3 on page 5).
https://www.pcisecuritystandards.org/documents/Prioritized_Approach_for_PCI_DSS_v3-1.pdf