http://img.photobucket.com/albums/v704/chanpicco/chanpicco071/SS7-ASN1-Flaw_zpslcpchclx.jpg
Preface
People might questions leonardo Da Vinci if he still alive. Why did he choose this woman became mona lisa? Since nobody could explain on behalf of him. But strongly believe that this is the original design.
Linux are everywhere today, in workstation, servers, mobile devices and IoT devices. On the other hand, the culture of modern world relies on electronic communications system. Therefore network communication protocol especially TCP/IP protocol and Signaling System 7 are the major elements in nowadays world.
Recall historical data of specific elements (quick & dirty)
1. ASN.1
Originally defined in 1984 as part of CCITT X.409:1984
Design objective:
i. Overcome how different computer systems transmit data
ii. Model parameters exchanged between application entities
2. Signalling System 7
It was developed in 1975
Design objective
i. SS7 controls telephone calls, both wired and wireless, through the use of a control signal that is separate from the actual voice circuit.
ii. It allows phone networks to exchange the information needed for passing calls and text messages between each other.
3. TCP/IP version 4
The first version of this predecessor of modern TCP was written in 1973
Design objective
i. A set of general design guidelines and implementations of specific networking protocols to enable computers to communicate over networks.
ii. TCP/IP provides end-to-end connectivity specifying how data should be formatted, addressed, transmitted, routed and received at the destination.
Flaws found as of today
TCP/IP version 4 (CVE-2016-5696)
The difficult part for hacker taking over TCP connection is to guess the source port of the client and the current sequence number. A group of researchers found that open a connection to the server and send with the source of the attacker as much “RST” handshake packets with the wrong sequence mixed with a few spoofed packets. By counting how much “challenge ACK” handshake packet get returned to the attacker side. Attacker might knowing the rate limit one can infer how much of the spoofed packets resulted in a challenge ACK to the spoofed client and thus how many of the guesses where correct. This way can quickly narrow down which values of port and sequence are correct.
http://img.photobucket.com/albums/v704/chanpicco/chanpicco071/ninja-anima-ver2_zpsoonzpftm.gif
Interim solution apply to Linux environment
Linux are everywhere today, in workstation, servers, mobile devices and IoT devices. Append the following to /etc/sysctl.conf:
net.ipv4.tcp_challenge_ack_limit = 999999999
Use “sysctl -p” to activate this feature
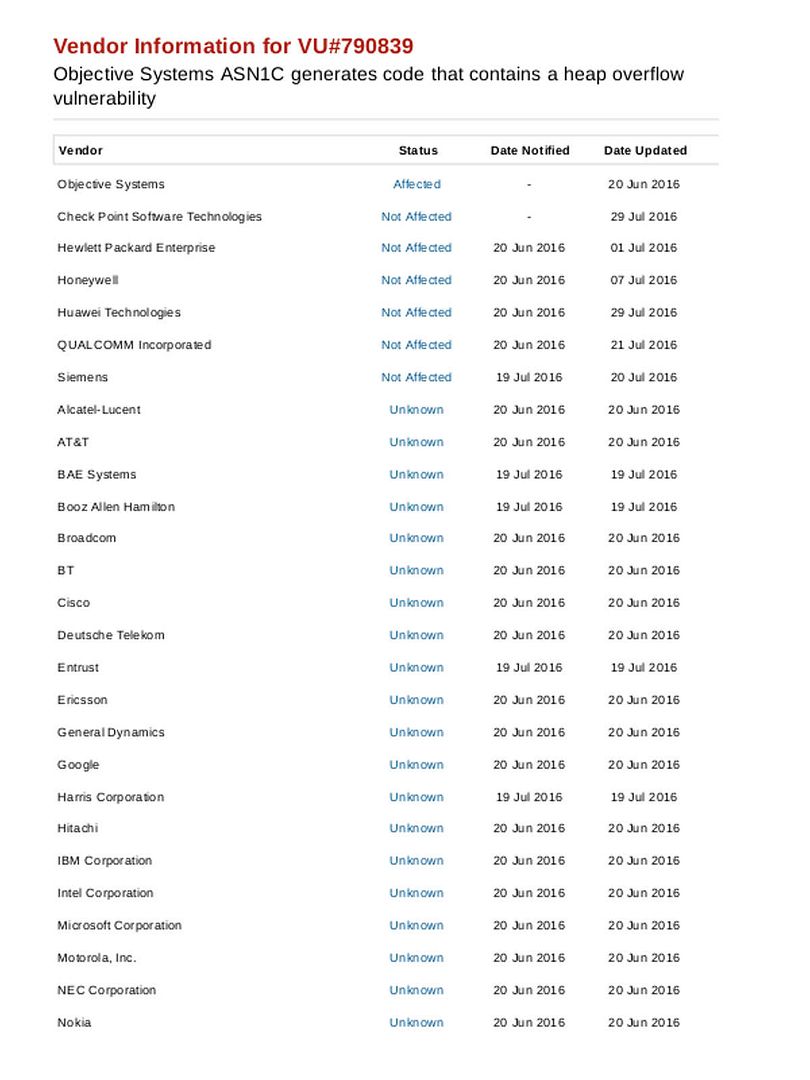
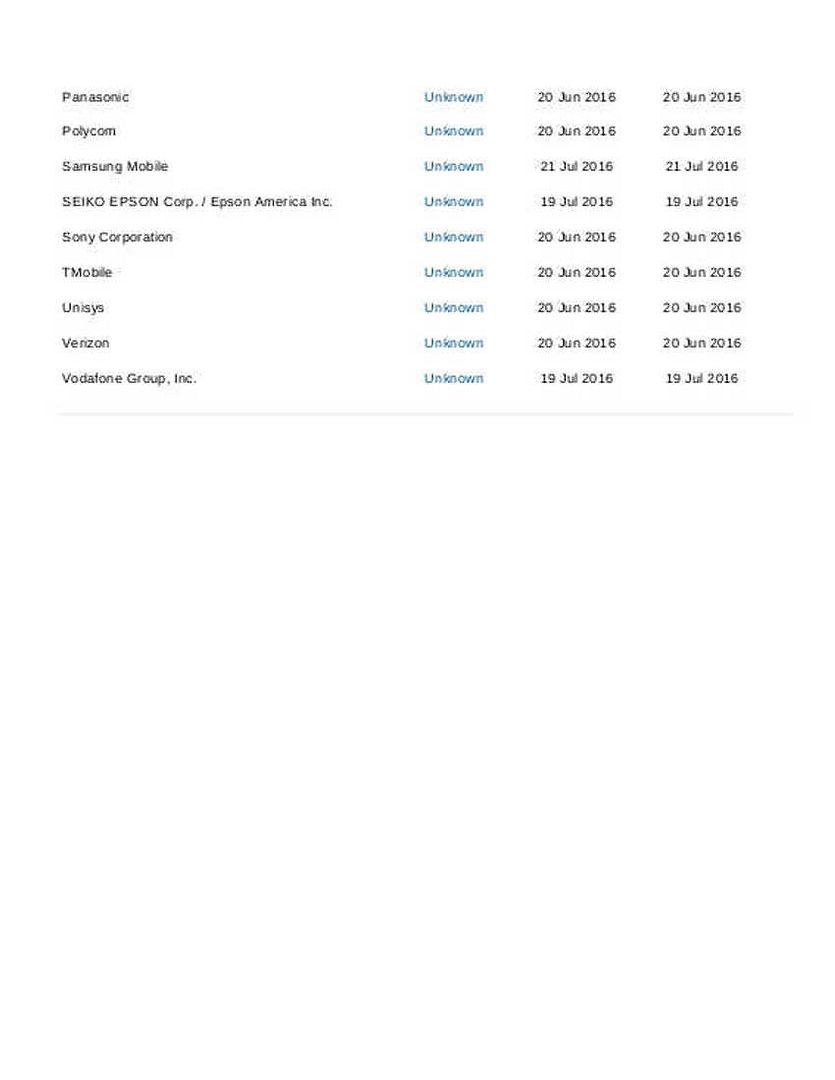
Flaw found in ASN.1 compiler
For more details, please see below:
https://www.linkedin.com/pulse/flaw-found-communications-industry-yet-determined-1-picco
Interim solution: unavailable
Current status: The extent of the vulnerability has yet to be determined, IT folks this vulnerability looks critical. It is hard to imagine what’s the impact at this moment. We keep our eyes open see whether a remediation will be announced by the telecommunication providers?
SS7 Vulnerability
A proof of concept shown that attacker could use the telephone network to access the voice data of a mobile phone, find its location and collect other information. Hacker able to manipulating USSD commands to spoof financial transactions such as the authorization of purchases or the transfer of funds between accounts.
The hacks exploit the SS7 vulnerability by tricking the telecom network believing the attacker’s phone has the same number as the victim’s phone. We know that hackers can hijack whatsApp and telegram via ss7. A vulnerability found on 2008.
Interim solution
Mobile phone network services provider has employed security experts to perform analysis of the SS7 systems in use to try and prevent unauthorised access.
For additional information details, please refer below:
SS7 hack explained: what can you do about it?
http://img.photobucket.com/albums/v704/chanpicco/chanpicco071/OSI-vs-SS7_zpsk76izco4.gif
How to protect your IT premises in regards to above flaws?
For weakness of TCP/IP protocol, the IP version 6 able to resolve design limitation of sequence number. In the long run, it is recommend IT team get rid of IP version 4. However the truth is that v4 and v6 are mixed mode in nowadays IT world.
The most headache topics are the ANS.1 complier flaw and Signalling system 7 vulnerability. For SS7 vulnerability, since those item of works (remediation and mitigation) are relies on Telecommunication service providers. Mobile phone network services provider employing security experts to perform analysis of the SS7 systems in use to try and prevent unauthorised access. For text messages, avoiding using SMS. As far as we know, whatsapp communication is being encrypted today!
How’s the status of ASN.1 compiler right now?
About SS7 vulnerability information update:
Nokia safeguards network operations with new security features in Sep 2015. The features consisting of Signaling Guard and Security Assessment service, detects and prevents attacks that exploit vulnerabilities in the SS7 protocol. For more details. Please refer to url below:
http://company.nokia.com/en/news/press-releases/2015/09/03/nokia-networks-safeguards-network-operations-with-two-new-security-launches-networksperform
About SS7 vulnerability incident found and reported by German newspaper media on May 2017:
German newspaper (Süddeutsche Zeitung) reported that that hackers relied on SS7 attacks flaw as a backdoor. The vulnerability allow bypass two-factor authentication (2FA) systems to conduct unauthorized wire transfers.
http://www.sueddeutsche.de/digital/it-sicherheit-schwachstelle-im-mobilfunknetz-kriminelle-hacker-raeumen-konten-leer-1.3486504
Wow, amazing weblog structure! How lengthy have you been blogging for? you make running a blog glance easy. The total glance of your web site is excellent, as well as the content material!
I have learned result-oriented things out of your blog post. One other thing to I have noticed is that in many instances, FSBO sellers will reject anyone. Remember, they will prefer to never use your expert services. But if a person maintain a steady, professional relationship, offering assistance and remaining in contact for four to five weeks, you will usually have the capacity to win interviews. From there, a listing follows. Cheers
Hey there, You have done a fantastic job. I will definitely digg it and personally suggest to my friends. I’m sure they will be benefited from this website.
I appreciate you sharing this article post.Really thank you! Awesome.
Spot up for this write-up, I really feel this site wants considerably more consideration. I’ll more likely once more to see far more, many thanks that info.
Pretty element of content. I just stumbled upon your weblog and in accession capital to assert that I get actually enjoyed account your weblog posts. Anyway I will be subscribing to your feeds or even I achievement you get admission to consistently rapidly.
Hello there! This is my first comment here, so I just wanted to give a quick shout out and say I genuinely enjoy reading your articles. Can you recommend any other blogs/websites/forums that deal with the same subjects? Thanks.
Heya i am for the first time here. I found this board and I find It really useful & it helped me out a lot. I hope to give something back and help others like you helped me.
I want to convey my love for your kindness supporting all those that must have guidance on this important content. Your very own commitment to getting the message all through had been exceedingly helpful and have usually permitted women much like me to reach their targets. This useful information means so much to me and even more to my colleagues. Best wishes; from everyone of us.
I would like to thank you for the efforts you’ve put in writing this blog. I am hoping the same high-grade site post from you in the upcoming also. Actually your creative writing skills has encouraged me to get my own blog now. Really the blogging is spreading its wings fast. Your write up is a good example of it.
I enjoy, cause I discovered exactly what I used to be taking a look for. You have ended my four day lengthy hunt! God Bless you man. Have a great day. Bye
I simply had to thank you very much again. I do not know the things I might have undertaken without the entire concepts discussed by you on my situation. It truly was a real frightful issue in my view, nevertheless considering the well-written manner you processed it took me to jump with contentment. I am just happy for this work and thus hope that you find out what an amazing job you’re accomplishing training men and women using your web page. I am certain you’ve never encountered all of us.
Thanks a bunch for sharing this with all people you really realize what you are speaking about! Bookmarked. Kindly also discuss with my site =). We can have a hyperlink alternate arrangement among us!
I was suggested this web site by my cousin. I’m not sure whether this post is written by him as nobody else know such detailed about my difficulty. You’re incredible! Thanks!
I loved as much as you’ll receive carried out right here. The sketch is tasteful, your authored material stylish. nonetheless, you command get got an edginess over that you wish be delivering the following. unwell unquestionably come further formerly again since exactly the same nearly very often inside case you shield this hike.
Wow, wonderful blog layout! How long have you been blogging for? you made blogging look easy. The overall look of your web site is excellent, as well as the content! gcdeafefbkga
Howdy! This article could not be written any better! Looking at this post reminds me of my previous roommate! He constantly kept preaching about this. I’ll send this information to him. Fairly certain he’s going to have a good read. Thanks for sharing! efedeeekfeeeeedk
Hello there, I discovered your website by the use of Google while looking for a related subject, your web site came up, it seems good. I have bookmarked it in my google bookmarks. bfkgkbdddegd
you are in point of fact a just right webmaster. The site loading velocity is amazing. It sort of feels that you are doing any distinctive trick. Furthermore, The contents are masterpiece. you’ve performed a magnificent process in this subject! fbkagaakddcg
I am really enjoying the themedesign of your blog. Do you ever run into any browser compatibility problems? A handful of my blog readers have complained about my website not operating correctly in Explorer but looks great in Chrome. Do you have any advice to help fix this issue? gbcedbdgkakeccef
I do believe all of the ideas you’ve offered for your post. They are really convincing and will definitely work. Still, the posts are very quick for newbies. May just you please extend them a little from next time? Thank you for the post. bbcggacddadk
Howdy! Would you mind if I share your blog with my twitter group? Theres lots of people that I believe would really enjoy your content. Please let me know. Thanks edebfgedgeacadck
Hello there, just became alert to your blog through Google, and found that it’s really informative. I’m going to watch out for brussels. I’ll be grateful if you continue this in future. Numerous people will be benefited from your writing. Cheers!
There is noticeably a bundle to understand this. I assume you have made specific nice points in features also.
I simply want to say I am just all new to blogging and seriously loved your web blog. Most likely I’m planning to bookmark your blog post . You absolutely come with beneficial well written articles. With thanks for sharing with us your web site.
HiWhat’s upHi thereHello to allevery oneevery single one, it’s reallyactuallyin facttrulygenuinely a nicepleasantgoodfastidious for me to visitgo to seepay a visitpay a quick visit this websiteweb sitesiteweb page, it containsconsists ofincludes valuablepreciouspricelessimportanthelpfuluseful Information.
As a Newbie, I am continuously searching online for articles that can aid me. Thank you
Hello, I think your blog might be having browser compatibility issues. When I look at your website in Safari, it looks fine but when opening in Internet Explorer, it has some overlapping. I just wanted to give you a quick heads up! Other then that, great blog!
Absolutely written subject material , thankyou for entropy.
I am planning to begin my website soon, but I’m a little lost on everything. Can you suggest beginning with a free platform like WordPress or move for a paid option? There are a lot of choices out there which I’m completely confused. Any suggestions? Thank you a lot.
Your very own commitment to getting the message throughout came to be rather potent and have always enabled employees like me to arrive at their desired goals.
Your writing taste has been astounded me. Thank you, very nice article.
The subsequent time I read a weblog, I hope that it doesnt disappoint me as much as this one. I mean, I do know it was my option to read, but I truly thought youd have something attention-grabbing to say. All I hear is a bunch of whining about something that you would fix when you werent too busy searching for attention.
I am really impressed with your writing skills and also with the layout on your blog. Is this a paid theme or did you modify it yourself? Either way keep up the nice quality writing, it is rare to see a nice blog like this one today..
I just like the helpful information you supply for your articles. I will bookmark your blog and check once more here regularly. I’m somewhat sure I will be told lots of new stuff proper right here! Best of luck for the next!