http://img.photobucket.com/albums/v704/chanpicco/chanpicco070/undiscovered-POS-malware_zpsiae2pzht.jpg
Have you heard RawPOS technical term? In short, it is a Windows based malware family that targets payment card data including Retail, Hospitality and Casinos.
The undiscovered POS malware – High Level review (Found Aug 2016)
Specifications:
- Associated with files psrmon.exe and oobentfy.exe – psrmon.exe manipulating the data encryption process. Copies following files to temp folder.
Console.dll,Cwd.dll,mro.dll,API.dll,List.dll,Fcntl.dll,B.dll,p2x5124.dll,re.dll,OLE.dll,POSIX.dll,
File.dll,IO.dll,MD5.dll,Win32.dll,Process.dll,Dumper.dll,Util.dll,Base64.dll,Registry.dll
- Associated with files hdmsvc.exe and oobentfy.exe – Named Pipe Vulnerabilities (C:\DosDevices\pipe\pipe\net\NtControlPipe10), discoveries in manipulating the \DosDevices object directory that also lead to privilege escalation.
Program “oobentfy.exe” is the major body (this is the Memory scanning portion of the malware).
Scenario replay
1. Malware will create a memory dump folder (sample shown as below):
C:\DOCUME~1\User\LOCALS~1\Temp\memdump
2. The program will monitor the memdump folder (C:\DOCUME~1\User\LOCALS~1\Temp\memdump). Memdump folder contains plain text credit card data.
3. Credit card data will then be encrypted and placed in a file.
Regarding to the analysis, it is a three-part RawPOS process to infect a system. Additionally, found that this malware relies on Perl Source code.
Malware structure in depth

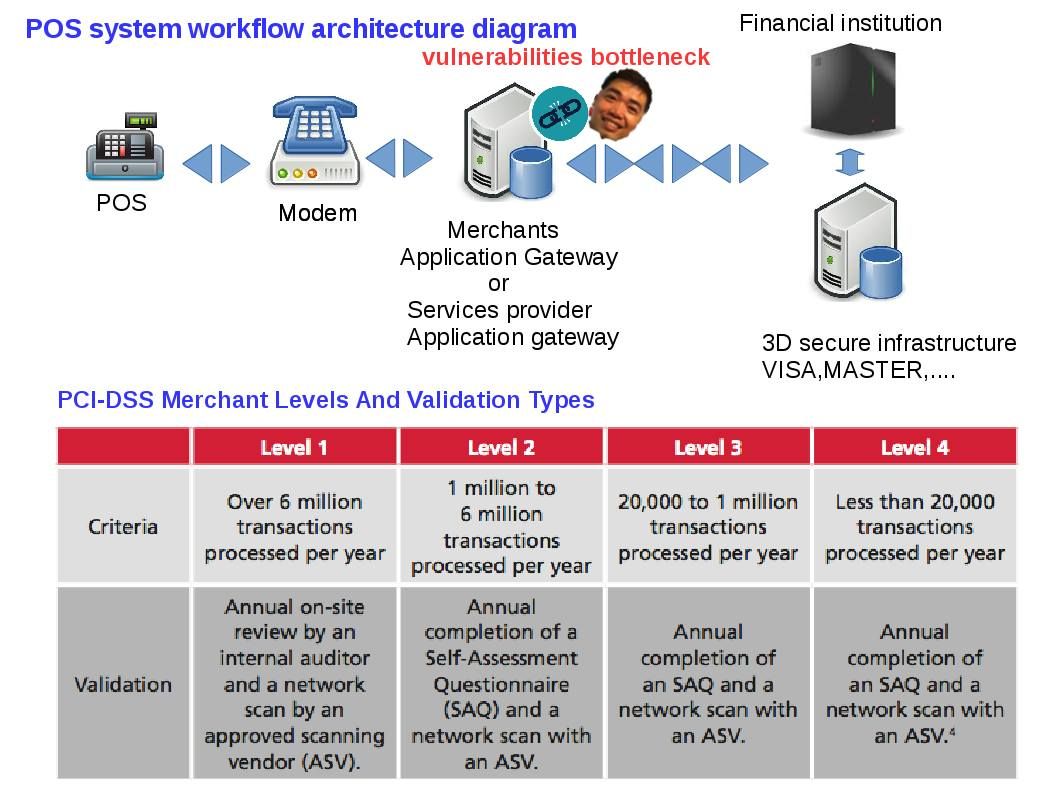
Merchant Levels & POS system workflow architecture
Current status:
As of today(6th Aug 2016), it looks that no AV engines recognize the hash for the persistence mechanism as a threat.
Anyway, will keep you posted if there is anything updating.
My husband and i have been now lucky Albert managed to deal with his preliminary research out of the precious recommendations he came across out of your web page. It’s not at all simplistic to simply continually be releasing hints that a number of people may have been trying to sell. Therefore we acknowledge we’ve got the website owner to thank because of that. Most of the illustrations you’ve made, the straightforward site menu, the relationships your site help create – it’s got everything impressive, and it’s aiding our son and our family reckon that the subject matter is cool, and that’s very fundamental. Thanks for everything!
HiWhat’s upHi thereHello i am kavin, its my first timeoccasion to commenting anywhereanyplace, when i read this articlepostpiece of writingparagraph i thought i could also makecreate comment due to this brilliantsensiblegood articlepostpiece of writingparagraph.
HowdyHi thereHey thereHiHelloHey! Someone in my MyspaceFacebook group shared this sitewebsite with us so I came to give it a looklook it overtake a lookcheck it out. I’m definitely enjoyingloving the information. I’m book-markingbookmarking and will be tweeting this to my followers! TerrificWonderfulGreatFantasticOutstandingExceptionalSuperbExcellent blog and wonderfulterrificbrilliantamazinggreatexcellentfantasticoutstandingsuperb style and designdesign and styledesign.
I’m so happy to read this. This is the kind of manual that needs to be given and not the accidental misinformation that’s at the other blogs. Appreciate your sharing this best doc.
What theme is this? Love it!
Thank you for your blog article.Really thank you! Great.
There is definately a lot to learn about this issue. I really like all the points you’ve made.
Excellent read, I just passed this onto a colleague who was doing some research on that. And he actually bought me lunch as I found it for him smile Therefore let me rephrase that: Thanks for lunch!
I believe you have noted some very interesting points , thankyou for the post.
Thank you for another informative web site. The place else could I get that kind of info written in such a perfect approach? I’ve a undertaking that I am just now running on, and I have been on the glance out for such information.
I enjoy the efforts you have put in this, appreciate it for all the great blog posts.
Hello, Neat post. There is a problem with your web site in web explorer, could test this… IE still is the market leader and a huge part of other folks will miss your wonderful writing because of this problem.
I like the helpful info you provide in your articles. I’ll bookmark your weblog and check again here frequently. I am quite sure I will learn plenty of new stuff right here! Best of luck for the next!
I just couldn’t depart your website prior to suggesting that I actually enjoyed the usual information a person provide on your visitors? Is going to be again incessantly to check out new posts.
Utterly indited content material , thankyou for information .
My brother recommended I might like this website. He was entirely right. This post truly made my day. You can not imagine just how much time I had spent for this information! Thanks!
Wow, fantastic blog layout! How long have you been blogging for? you make blogging look easy. The overall look of your website is fantastic, as well as the content!
Only wanna input on few general things, The website design and style is perfect, the subject material is very good. “Art for art’s sake makes no more sense than gin for gin’s sake.” by W. Somerset Maugham.
It is actually a great and helpful piece of info. I am happy that you shared this useful information with us. Please keep us up to date like this. Thanks for sharing.
I genuinely enjoy looking at on this site, it contains wonderful blog posts. “Beware lest in your anxiety to avoid war you obtain a master.” by Demosthenes.
Very nice post. I just stumbled upon your blog and wanted to say that I’ve really enjoyed browsing your blog posts. In any case I will be subscribing to your rss feed and I hope you write again very soon!
I think this internet site contains some rattling excellent info for everyone :D. “Morality, like art, means a drawing a line someplace.” by Oscar Wilde.
I truly wanted to develop a brief remark so as to say thanks to you for those awesome strategies you are posting at this website. My time-consuming internet look up has at the end of the day been honored with incredibly good details to go over with my close friends. I would repeat that most of us website visitors are undeniably fortunate to be in a magnificent place with so many awesome professionals with useful methods. I feel really happy to have encountered your webpage and look forward to really more awesome moments reading here. Thank you once more for all the details.
Keep up the superb piece of work, I read few posts on this website and I conceive that your web site is really interesting and holds sets of excellent info .
I am no longer positive the place you’re getting your information, but good topic. I must spend some time learning more or figuring out more. Thanks for fantastic information I was on the lookout for this info for my mission.
Hello there, You’ve done an incredible job. I’ll definitely digg it and personally recommend to my friends. I am confident they’ll be benefited from this site.
I was more than happy to uncover this website. I want to to thank you for ones time for this particularly fantastic read!! I definitely savored every part of it and I have you book marked to see new information on your blog.
It¡¦s really a nice and useful piece of info. I¡¦m happy that you simply shared this helpful information with us. Please keep us informed like this. Thank you for sharing.
I enjoy the efforts you have put in this, appreciate it for all the great content.
I haven’t checked in here for some time as I thought it was getting boring, but the last few posts are great quality so I guess I will add you back to my everyday bloglist. You deserve it my friend 🙂
Rattling good information can be found on web blog . “Life without a friend is death without a witness.” by Eugene Benge.
What’s Taking placeHappeningGoing down i’mi am new to this, I stumbled upon this I haveI’ve founddiscovered It positivelyabsolutely helpfuluseful and it has helpedaided me out loads. I am hopingI hopeI’m hoping to give a contributioncontribute & assistaidhelp otherdifferent userscustomers like its helpedaided me. GoodGreat job.
I am constantly browsing online for ideas that can facilitate me. Thx!
Great – I should certainly pronounce, impressed with your website. I had no trouble navigating through all the tabs as well as related information ended up being truly easy to do to access. I recently found what I hoped for before you know it at all. Quite unusual. Is likely to appreciate it for those who add forums or something, website theme . a tones way for your customer to communicate. Excellent task.
Hiya, I am really glad I have found this info. Nowadays bloggers publish just about gossips and net and this is really frustrating. A good blog with exciting content, that’s what I need. Thanks for keeping this website, I’ll be visiting it. Do you do newsletters? Can’t find it.
My husband and i felt relieved when Raymond managed to conclude his analysis via the precious recommendations he was given through the blog. It’s not at all simplistic to just always be giving freely tips and tricks which often the rest have been making money from. So we understand we’ve got the blog owner to give thanks to for this. The specific illustrations you made, the simple site navigation, the relationships your site make it easier to engender – it’s got mostly impressive, and it is assisting our son and us do think that article is pleasurable, which is unbelievably mandatory. Many thanks for the whole lot!
Hey There. I found your blog using msn. This is a very well written article. I will make sure to bookmark it and return to read more of your useful info. Thanks for the post. I will certainly return.
excellent issues altogether, you just gained a new reader. What could you suggest about your post that you made some days ago? Any positive?
I’ve been surfing on-line greater than 3 hours today, but I never found any attention-grabbing article like yours. It¡¦s pretty price enough for me. In my opinion, if all web owners and bloggers made good content as you probably did, the web shall be a lot more useful than ever before.
naturally like your website but you need to take a look at the spelling on quite a few of your posts. A number of them are rife with spelling issues and I in finding it very bothersome to inform the truth on the other hand I will definitely come again again.
Simply wanna remark on few general things, The website style is perfect, the written content is really fantastic : D.
I am continuously looking online for posts that can facilitate me. Thx!
Excellent post. I was checking constantly this blog and I am impressed! Very helpful information particularly the last part 🙂 I care for such information much. I was looking for this certain information for a long time. Thank you and good luck.
I dugg some of you post as I cogitated they were handy extremely helpful
You are a very intelligent individual!
But wanna remark on few general things, The website style is perfect, the written content is real great : D.
It¡¦s actually a great and useful piece of information. I am happy that you shared this useful information with us. Please stay us up to date like this. Thanks for sharing.
I’m very happy to read this. This is the type of manual that needs to be given and not the random misinformation that is at the other blogs. Appreciate your sharing this best doc.
Hello, i think that i saw you visited my weblog so i came to “return the favor”.I’m trying to find things to improve my website!I suppose its ok to use a few of your ideas!!
I intended to put you the bit of word to help say thank you the moment again for those gorgeous views you’ve discussed on this page. It is tremendously generous with you to provide extensively all that a lot of people might have supplied as an e book in order to make some profit on their own, notably given that you could possibly have done it in the event you desired. Those inspiring ideas as well acted to provide a easy way to be aware that most people have a similar zeal just like my very own to see a lot more in respect of this issue. I’m sure there are millions of more pleasant occasions ahead for those who read through your blog.
whoah this weblog is fantastic i like studying your posts. Keep up the good paintings! You know, a lot of individuals are hunting around for this info, you can aid them greatly.
Thank you for helping out, wonderful info. “Our individual lives cannot, generally, be works of art unless the social order is also.” by Charles Horton Cooley.
Hey There. I found your blog using msn. This is an extremely well written article. I will be sure to bookmark it and return to read more of your useful info. Thanks for the post. I will definitely comeback.
Someone essentially lend a hand to make significantly articles I would state. This is the first time I frequented your web page and thus far? I amazed with the research you made to make this actual post extraordinary. Excellent job!
Wonderful paintings! That is the kind of information that should be shared across the net. Shame on the search engines for now not positioning this submit upper! Come on over and visit my site . Thank you =)
I intended to send you the little bit of remark to be able to say thanks yet again for your stunning methods you’ve shared on this website. It’s so seriously open-handed of people like you to deliver publicly all some people would have offered as an e-book in making some dough on their own, most importantly considering the fact that you might have tried it in the event you desired. Those basics also worked as a great way to be sure that some people have the same dreams just as mine to realize significantly more around this matter. I’m sure there are millions of more enjoyable opportunities ahead for individuals who check out your blog.
Spot on with this write-up, I truly suppose this web site needs way more consideration. I’ll in all probability be once more to learn much more, thanks for that info.
Just a smiling visitor here to share the love (:, btw great design .
You made some good points there. I did a search on the subject and found most persons will approve with your site.
You actually make it seem so easy with your presentation but I find this matter to be actually something which I think I would never understand. It seems too complex and extremely broad for me. I am looking forward for your next post, I’ll try to get the hang of it!
Definitely, what a great website and revealing posts, I definitely will bookmark your blog.Best Regards!
F*ckin’ awesome things here. I’m very satisfied to see your post. Thanks a lot and i am taking a look ahead to contact you. Will you please drop me a mail?
Really nice style and good articles , practically nothing else we require : D.
I consider something really special in this internet site.
As I website possessor I believe the content material here is rattling wonderful , appreciate it for your efforts. You should keep it up forever! Best of luck.
Hello, Neat post. There’s a problem with your site in internet explorer, could check this… IE nonetheless is the marketplace chief and a big component of folks will leave out your great writing because of this problem.
I am not sure where you are getting your info, but good topic. I needs to spend some time learning more or understanding more. Thanks for excellent info I was looking for this information for my mission.
I really like your writing style, superb info, appreciate it for putting up :D. “I hate mankind, for I think myself one of the best of them, and I know how bad I am.” by Joseph Baretti.
Thank you for sharing excellent informations. Your website is so cool. I am impressed by the details that you’ve on this web site. It reveals how nicely you perceive this subject. Bookmarked this website page, will come back for extra articles. You, my pal, ROCK! I found simply the information I already searched all over the place and just couldn’t come across. What an ideal web site.
Nice read, I just passed this onto a colleague who was doing a little research on that. And he just bought me lunch since I found it for him smile So let me rephrase that: Thanks for lunch! “High living and high thinking are poles apart.” by B. J. Gupta.
Rattling wonderful information can be found on site . “Society produces rogues, and education makes one rogue more clever than another.” by Oscar Fingall O’Flahertie Wills Wilde.
My husband and i were quite joyous when Peter managed to carry out his survey out of the precious recommendations he got while using the web page. It’s not at all simplistic just to find yourself giving for free procedures which usually people could have been making money from. We do understand we have got the writer to thank for this. These explanations you made, the straightforward blog navigation, the relationships you help to engender – it’s most excellent, and it’s facilitating our son in addition to the family reason why that content is awesome, and that is quite fundamental. Many thanks for the whole thing!
Perfectly written subject material , thanks for selective information .
Magnificent beat ! I would like to apprentice while you amend your web site, how can i subscribe for a blog web site? The account helped me a acceptable deal. I had been tiny bit acquainted of this your broadcast provided bright clear idea
Excellent goods from you, man. I’ve understand your stuff previous to and you’re just extremely great. I really like what you have acquired here, certainly like what you are stating and the way in which you say it. You make it entertaining and you still take care of to keep it smart. I cant wait to read far more from you. This is actually a tremendous web site.
I can inform on your own took your period examine the issue, favourable effort.
You have observed very interesting details! ps decent web site.
HeyHowdyHi thereHeyaHey thereHiHello just wanted to give you a quickbrief heads up and let you know a few of the imagespictures aren’t loading correctlyproperly. I’m not sure why but I think its a linking issue. I’ve tried it in two different browsersinternet browsersweb browsers and both show the same resultsoutcome.
I will right away take hold of your rss as I can not in finding your email subscription hyperlink or e-newsletter service. Do you’ve any? Kindly allow me recognize in order that I may subscribe. Thanks.
F*ckin’ remarkable issues here. I am very satisfied to peer your post. Thanks a lot and i’m having a look ahead to contact you. Will you kindly drop me a mail?
You are my aspiration , I own few web logs and rarely run out from to post .
magnificent issues altogether, you simply won a brand new reader. What could you suggest in regards to your post that you simply made a few days ago? Any certain?
What’s Happening i am new to this, I stumbled upon this I’ve found It absolutely useful and it has helped me out loads. I am hoping to contribute & assist other users like its helped me. Good job.
Hi! I’ve been reading your web site for a while now and finally got the courage to go ahead and give you a shout out from Houston Texas! Just wanted to say keep up the good job!
The following time I read a blog, I hope that it doesnt disappoint me as much as this one. I imply, I know it was my option to read, but I actually thought youd have something fascinating to say. All I hear is a bunch of whining about something that you may fix should you werent too busy searching for attention.
whoah this blog is great i love reading your posts. Keep up the good work! You know, lots of people are searching around for this info, you can help them greatly.
Another thing I have really noticed is that often for many people, bad credit is the response to circumstances further than their control. For instance they may be actually saddled with an illness so they really have higher bills for collections. It can be due to a job loss or the inability to do the job. Sometimes divorce proceedings can truly send the financial circumstances in the wrong direction. Thanks sharing your thinking on this site.
Simply desire to say your article is as amazing. The clarity in your post is just nice and that i can suppose you’re a professional in this subject. Well with your permission let me to grasp your feed to stay updated with drawing close post. Thank you 1,000,000 and please carry on the rewarding work.
Great blog here! Also your website loads up fast! What host are you using? Can I get your affiliate link to your host? I wish my web site loaded up as fast as yours lol
This web page is really a walk-by way of for all of the info you wished about this and didn’t know who to ask. Glimpse right here, and you’ll definitely uncover it.
Also a thing to mention is that an online business administration course is designed for learners to be able to smoothly proceed to bachelor’s degree courses. The Ninety credit college degree meets the other bachelor college degree requirements then when you earn the associate of arts in BA online, you may have access to the modern technologies in such a field. Some reasons why students need to get their associate degree in business is because they may be interested in the field and want to receive the general instruction necessary just before jumping in a bachelor education program. Many thanks for the tips you actually provide in your blog.
I have come to understand that expenses for online degree experts tend to be an incredible value. For instance a full College Degree in Communication in the University of Phoenix Online consists of 60 credits from $515/credit or $30,900. Also American Intercontinental University Online gives a Bachelors of Business Administration with a complete program feature of 180 units and a price of $30,560. Online learning has made getting your education far more easy because you can certainly earn the degree in the comfort of your abode and when you finish working. Thanks for all other tips I have really learned from your website.
I like this web blog so much, saved to my bookmarks. “American soldiers must be turned into lambs and eating them is tolerated.” by Muammar Qaddafi.
I was just seeking this information for a while. After 6 hours of continuous Googleing, at last I got it in your web site. I wonder what is the lack of Google strategy that don’t rank this type of informative sites in top of the list. Usually the top websites are full of garbage.
whoah this blog is excellent i love reading your articles. Keep up the great work! You know, a lot of people are looking around for this information, you could aid them greatly.
You made some decent points there. I did a search on the subject matter and found most persons will approve with your blog.
Thanks for the ideas you have discussed here. Yet another thing I would like to convey is that personal computer memory requirements generally increase along with other improvements in the technological innovation. For instance, when new generations of processors are introduced to the market, there is certainly usually a similar increase in the type calls for of both the laptop or computer memory and hard drive space. This is because the application operated simply by these processor chips will inevitably surge in power to use the new know-how.
Howdy just wanted to give you a quick heads up. The text in your article seem to be running off the screen in Internet explorer. I’m not sure if this is a formatting issue or something to do with internet browser compatibility but I figured I’d post to let you know. The layout look great though! Hope you get the problem resolved soon. Many thanks
Useful information. Fortunate me I found your website by accident, and I am surprised why this accident did not took place in advance! I bookmarked it.
I have been examinating out some of your posts and it’s pretty nice stuff. I will make sure to bookmark your site.
I think other web-site proprietors should take this website as an model, very clean and excellent user friendly style and design, let alone the content. You’re an expert in this topic!
Oh my goodness! an incredible article dude. Thank you Nevertheless I’m experiencing subject with ur rss . Don’t know why Unable to subscribe to it. Is there anybody getting an identical rss downside? Anyone who is aware of kindly respond. Thnkx
I would like to express some thanks to this writer just for rescuing me from such a predicament. As a result of exploring throughout the search engines and getting advice that were not powerful, I was thinking my entire life was done. Living without the presence of strategies to the problems you have sorted out by means of your site is a critical case, and the kind that would have badly damaged my career if I had not noticed your website. Your competence and kindness in maneuvering every part was very useful. I’m not sure what I would’ve done if I had not encountered such a step like this. I am able to now relish my future. Thanks very much for the high quality and sensible help. I will not think twice to endorse your web page to any individual who will need direction on this situation.
I have seen plenty of useful points on your website about computer systems. However, I’ve the opinion that laptop computers are still more or less not powerful enough to be a good choice if you often do tasks that require many power, for example video editing. But for world wide web surfing, statement processing, and the majority of other typical computer functions they are okay, provided you can’t mind the little screen size. Many thanks for sharing your notions.
Thanks for the thoughts you have shared here. Also, I believe there are several factors which will keep your auto insurance premium all the way down. One is, to bear in mind buying cars that are within the good directory of car insurance organizations. Cars that happen to be expensive are usually more at risk of being snatched. Aside from that insurance is also depending on the value of your truck, so the more expensive it is, then the higher your premium you have to pay.
It’s perfect time to make some plans for the future and it is time to be happy. I have read this post and if I could I desire to suggest you some interesting things or suggestions. Perhaps you could write next articles referring to this article. I desire to read more things about it!
There are certainly plenty of particulars like that to take into consideration. That is a nice point to deliver up. I supply the ideas above as general inspiration however clearly there are questions like the one you convey up where the most important thing shall be working in honest good faith. I don?t know if best practices have emerged around things like that, however I’m certain that your job is clearly recognized as a fair game. Each girls and boys really feel the impact of just a second’s pleasure, for the rest of their lives.
Thanks for your tips on this blog. 1 thing I would choose to say is always that purchasing electronic devices items in the Internet is certainly not new. In truth, in the past several years alone, the market for online gadgets has grown significantly. Today, you’ll find practically just about any electronic gadget and gizmo on the Internet, including cameras plus camcorders to computer parts and games consoles.
This design is spectacular! You definitely know how to keep a reader amused. Between your wit and your videos, I was almost moved to start my own blog (well, almost…HaHa!) Great job. I really loved what you had to say, and more than that, how you presented it. Too cool!
Wow! This can be one particular of the most helpful blogs We’ve ever arrive across on this subject. Actually Wonderful. I’m also an expert in this topic so I can understand your hard work.
Hey there! Quick question that’s completely off topic. Do you know how to make your site mobile friendly? My website looks weird when browsing from my apple iphone. I’m trying to find a template or plugin that might be able to resolve this issue. If you have any suggestions, please share. Cheers!
Thanks for sharing these types of wonderful articles. In addition, the perfect travel plus medical insurance program can often reduce those fears that come with travelling abroad. Any medical emergency can quickly become costly and that’s guaranteed to quickly place a financial stress on the family’s finances. Putting in place the great travel insurance program prior to setting off is well worth the time and effort. Cheers
I must express appreciation to the writer just for rescuing me from such a difficulty. Because of researching through the world wide web and getting suggestions that were not beneficial, I was thinking my life was gone. Living devoid of the strategies to the problems you have resolved through this review is a serious case, and those which may have adversely damaged my entire career if I hadn’t discovered your site. Your own expertise and kindness in maneuvering the whole lot was vital. I don’t know what I would’ve done if I had not come across such a point like this. I can at this moment look ahead to my future. Thanks a lot so much for the professional and amazing guide. I won’t be reluctant to endorse your web site to any person who needs direction about this problem.
I gotta favorite this website it seems very helpful very useful
hi!,I really like your writing so a lot! percentage we keep in touch more approximately your post on AOL? I require a specialist on this house to resolve my problem. May be that is you! Looking forward to look you.
Hello.This post was extremely motivating, especially because I was investigating for thoughts on this issue last Tuesday.
You can certainly see your enthusiasm in the paintings you write. The sector hopes for even more passionate writers such as you who are not afraid to say how they believe. Always go after your heart.
I have realized that in digital camera models, extraordinary detectors help to maintain focus automatically. The sensors connected with some digital cameras change in contrast, while others work with a beam with infra-red (IR) light, especially in low lighting. Higher specs cameras from time to time use a mixture of both models and will often have Face Priority AF where the video camera can ‘See’ your face and concentrate only in that. Thank you for sharing your thinking on this blog.
I’m impressed, I have to admit. Truly rarely should i encounter a weblog that’s both educative and entertaining, and let me tell you, you’ve hit the nail about the head. Your thought is outstanding; the catch is something that there are not enough individuals are speaking intelligently about. My business is happy that I found this within my find something with this.
I enjoy what you guys are usually up too. This sort of clever work and coverage! Keep up the wonderful works guys I’ve added you guys to my blogroll.
I’m not that much of a internet reader to be honest but your blogs really nice, keep it up! I’ll go ahead and bookmark your website to come back later. All the best
Wonderful work! This is the type of info that should be shared around the web. Shame on Google for not positioning this post higher! Come on over and visit my site . Thanks =)
One important thing is that when you find yourself searching for a education loan you may find that you’ll want a co-signer. There are many circumstances where this is correct because you will find that you do not possess a past history of credit so the lender will require you have someone cosign the credit for you. Good post.
whoah this weblog is fantastic i love reading your articles. Keep up the great work! You recognize, many people are looking around for this info, you can help them greatly.
Hey, you used to write great, but the last several posts have been kinda boring¡K I miss your tremendous writings. Past several posts are just a little out of track! come on!
Please let me know if you’re looking for an author for your site. You have some great posts, and I think I would be a good asset. If you ever want to take some of the load off, I’d like to write some material for your blog in exchange for a link back to mine. Please shoot me an email if interested. Thanks.
My partner and I stumbled over here different website and thought I might as well check things out. I like what I see so now I’m following you. Look forward to checking out your web page repeatedly.
I like what you guys are up too. Such smart work and reporting! Keep up the excellent works guys I¡¦ve incorporated you guys to my blogroll. I think it’ll improve the value of my website 🙂
Well said, 100 agree.
not use a beginning stage. For me, the starting stage is understanding which market I’m aiming for.
I think other web-site proprietors should take this site as an model, very clean and excellent user genial style and design, let alone the content. You’re an expert in this topic!
Certainly I like your website, however you need to check the spelling on quite a few of your posts. A number of them are rife with spelling issues and I find it very silly to inform you. On the other hand I’ll definitely come again again!
Excellent read, I just passed this onto a friend who was doing a little research on that. And he just bought me lunch since I found it for him smile Therefore let me rephrase that: Thank you for lunch!
Thanks for one marvelous posting! I enjoyed reading it; you are a great author.I will make sure to bookmark your blog and may come back someday. I want to encourage that you continue your great posts, have a nice weekend!
Keep functioning ,remarkable job!
Excellent goods from you, man. I have understand your stuff previous to and you are just extremely excellent. I actually like what you have acquired here, really like what you’re stating and the way in which you say it. You make it entertaining and you still care for to keep it smart. I can’t wait to read much more from you. This is really a tremendous site.
Thanks for some other informative blog. The place else may just I am getting that kind of info written in such a perfect manner? I have a venture that I’m simply now working on, and I’ve been at the glance out for such information.
I really appreciate this post. I¡¦ve been looking all over for this! Thank goodness I found it on Bing. You have made my day! Thank you again
Great awesome issues here. I am very glad to peer your post. Thanks so much and i am having a look ahead to touch you. Will you please drop me a e-mail?
Magnificent goods from you, man. I’ve understand your stuff previous to and you’re just extremely fantastic. I really like what you have acquired here, certainly like what you are saying and the way in which you say it. You make it entertaining and you still take care of to keep it sensible. I cant wait to read far more from you. This is really a great site.
Have you ever considered about adding a little bit more than just your articles? I mean, what you say is important and everything. However think of if you added some great graphics or video clips to give your posts more, “pop”! Your content is excellent but with images and video clips, this site could certainly be one of the very best in its field. Amazing blog!
An added important area is that if you are an older person, travel insurance with regard to pensioners is something you must really take into consideration. The old you are, greater at risk you happen to be for making something bad happen to you while in most foreign countries. If you are never covered by some comprehensive insurance cover, you could have many serious complications. Thanks for expressing your advice on this web site.
Have you ever thought about adding a little bit more than just your articles? I mean, what you say is valuable and everything. Nevertheless just imagine if you added some great visuals or video clips to give your posts more, “pop”! Your content is excellent but with pics and videos, this website could undeniably be one of the greatest in its field. Superb blog!
Thank you, I have just been searching for info about this topic for ages and yours is the greatest I have discovered so far. But, what about the bottom line? Are you sure about the source?
I enjoy, cause I found just what I used to be having a look for. You have ended my 4 day lengthy hunt! God Bless you man. Have a nice day. Bye
Fantastic blog! Do you have any helpful hints for aspiring writers? I’m planning to start my own blog soon but I’m a little lost on everything. Would you recommend starting with a free platform like WordPress or go for a paid option? There are so many choices out there that I’m completely confused .. Any tips? Appreciate it!
Thanks for the guidelines shared on the blog. Something also important I would like to express is that fat reduction is not exactly about going on a dietary fad and trying to shed as much weight that you can in a few months. The most effective way to burn fat is by taking it slowly but surely and using some basic points which can allow you to make the most from your attempt to shed pounds. You may understand and be following these tips, however reinforcing awareness never affects.
excellent submit, very informative. I ponder why the opposite specialists of this sector don’t realize this. You must proceed your writing. I am confident, you have a huge readers’ base already!
It’s appropriate time to make a few plans for the long run and it’s time to be happy. I’ve read this post and if I may just I want to suggest you few interesting things or advice. Maybe you could write next articles relating to this article. I desire to read even more things about it!
I’ve read several good stuff here. Certainly worth bookmarking for revisiting. I wonder how much effort you put to make such a wonderful informative web site.
Great blog here! Also your site loads up fast! What host are you using? Can I get your affiliate link to your host? I wish my web site loaded up as quickly as yours lol
I love what you guys are usually up too. This kind of clever work and coverage! Keep up the excellent works guys I’ve added you guys to my own blogroll.
F*ckin’ amazing things here. I am very happy to peer your post. Thank you so much and i am looking forward to touch you. Will you please drop me a mail?
Oh my goodness! an amazing article dude. Thank you Nevertheless I am experiencing issue with ur rss . Don’t know why Unable to subscribe to it. Is there anybody getting an identical rss problem? Anybody who is aware of kindly respond. Thnkx
Hi! I’m at work browsing your blog from my new iphone 3gs! Just wanted to say I love reading through your blog and look forward to all your posts! Carry on the outstanding work!
Nice weblog here! Also your website rather a lot up fast! What host are you the use of? Can I am getting your affiliate hyperlink in your host? I wish my website loaded up as fast as yours lol
Magnificent web site. Plenty of helpful info here. I am sending it to a few friends ans also sharing in delicious. And naturally, thanks on your effort!
It’s actually a great and helpful piece of info. I am glad that you shared this useful information with us. Please keep us up to date like this. Thanks for sharing.
What’s Happening i’m new to this, I stumbled upon this I have found It positively helpful and it has helped me out loads. I hope to contribute & assist other users like its aided me. Great job.
After examine a couple of of the weblog posts in your website now, and I really like your manner of blogging. I bookmarked it to my bookmark website listing and shall be checking again soon. Pls try my web site as well and let me know what you think.
An fascinating discussion is price comment. I feel that you should write more on this subject, it won’t be a taboo subject but usually persons are not enough to speak on such topics. To the next. Cheers
You made a few good points there. I did a search on the theme and found the majority of folks will consent with your blog.
With havin so much content do you ever run into any problems of plagorism or copyright infringement? My website has a lot of unique content I’ve either written myself or outsourced but it appears a lot of it is popping it up all over the web without my permission. Do you know any techniques to help stop content from being ripped off? I’d genuinely appreciate it.
Thank you for another informative web site. Where else could I get that kind of info written in such an ideal way? I have a project that I’m just now working on, and I have been on the look out for such info.
It’s a shame you don’t have a donate button! I’d most certainly donate to this brilliant blog! I guess for now i’ll settle for bookmarking and adding your RSS feed to my Google account. I look forward to fresh updates and will talk about this site with my Facebook group. Chat soon!
I really appreciate this post. I’ve been looking all over for this! Thank goodness I found it on Bing. You’ve made my day! Thanks again
Excellent beat ! I wish to apprentice at the same time as you amend your site, how can i subscribe for a weblog website? The account helped me a appropriate deal. I were a little bit acquainted of this your broadcast provided bright clear concept
Very great post. I simply stumbled upon your blog and wanted to say that I have really enjoyed browsing your weblog posts. After all I’ll be subscribing for your feed and I am hoping you write once more soon!
I wanted to compose a message to thank you for the precious pointers you are placing here. My rather long internet look up has at the end been recognized with reliable facts to exchange with my pals. I ‘d say that most of us site visitors are unquestionably blessed to live in a good site with many special professionals with helpful points. I feel pretty blessed to have encountered the website and look forward to some more brilliant minutes reading here. Thanks a lot once again for everything.
A lot of thanks for your whole work on this blog. My daughter really likes going through internet research and it’s really easy to see why. I know all of the dynamic ways you give good solutions by means of your web blog and in addition welcome contribution from the others on that content so my child is always discovering a lot of things. Enjoy the rest of the year. You’re conducting a splendid job.
I think this is one of the most significant information for me. And i’m glad reading your article. But should remark on some general things, The website style is ideal, the articles is really nice : D. Good job, cheers
What i don’t realize is if truth be told how you’re not actually a lot more neatly-preferred than you might be right now. You’re so intelligent. You recognize thus significantly in the case of this subject, made me individually imagine it from so many numerous angles. Its like women and men are not involved until it’s one thing to do with Girl gaga! Your personal stuffs nice. At all times handle it up!
Can I just say what a relief to seek out someone who truly is aware of what theyre speaking about on the internet. You definitely know how you can deliver a problem to light and make it important. Extra people need to learn this and perceive this facet of the story. I cant consider youre not more in style because you undoubtedly have the gift.
Terrific work! This is the kind of information that are meant to be shared around the internet. Shame on the search engines for now not positioning this submit higher! Come on over and talk over with my site . Thank you =)
Superb blog! Do you have any tips for aspiring writers? I’m hoping to start my own site soon but I’m a little lost on everything. Would you advise starting with a free platform like WordPress or go for a paid option? There are so many choices out there that I’m totally overwhelmed .. Any tips? Many thanks!
I just could not depart your web site before suggesting that I extremely enjoyed the standard information a person provide for your visitors? Is gonna be back continuously to investigate cross-check new posts
Thank you for some other informative website. Where else could I am getting that type of info written in such an ideal method? I’ve a challenge that I’m simply now running on, and I have been on the glance out for such info.
There is visibly a lot to realize about this. I consider you made various good points in features also.
An extremely good post. This post sums up for me just what this topic is all about and some of the major benefits that can be produced by knowing about it just like you. A friend once pointed out that you have a totally different approach when you do something for certain as opposed to when you’re simply just toying with it. In the case of this specific topic, I believe you’re taking, or start to go for, a more professional plus thorough approach to what and how you’re writing, which in turn helps you to continue to get better and help others who don’t know anything at all about what you have discussed here. Thank you.
Hello my loved one! I want to say that this article is awesome, great written and include approximately all vital infos. I¡¦d like to peer extra posts like this .
Hello, you used to write great, but the last few posts have been kinda boring¡K I miss your super writings. Past few posts are just a bit out of track! come on!
Thank you for the good writeup. It in fact was a amusement account it. Look advanced to more added agreeable from you! By the way, how could we communicate?
hello there and thank you for your info – I’ve certainly picked up anything new from right here. I did however expertise some technical points using this web site, as I experienced to reload the website lots of times previous to I could get it to load correctly. I had been wondering if your hosting is OK? Not that I’m complaining, but sluggish loading instances times will very frequently affect your placement in google and can damage your high quality score if ads and marketing with Adwords. Anyway I am adding this RSS to my e-mail and could look out for much more of your respective fascinating content. Make sure you update this again very soon..
Thank you for the sensible critique. Me & my neighbor were just preparing to do some research on this. We got a grab a book from our area library but I think I learned more clear from this post. I’m very glad to see such fantastic information being shared freely out there.
Hi there, just became aware of your blog through Google, and found that it’s really informative. I am going to watch out for brussels. I’ll appreciate if you continue this in future. Many people will be benefited from your writing. Cheers!
There is evidently a bunch to know about this. I think you made some good points in features also.
Do you have a spam issue on this website; I also am a blogger, and I wanted to know your situation; many of us have developed some nice methods, and we are looking to trade methods with others, why not shoot me an e-mail if interested.
Good ¡V I should definitely pronounce, impressed with your site. I had no trouble navigating through all tabs and related information ended up being truly simple to do to access. I recently found what I hoped for before you know it in the least. Quite unusual. Is likely to appreciate it for those who add forums or anything, web site theme . a tones way for your client to communicate. Nice task..
Appreciation for really being thoughtful and also for deciding on certain marvelous guides most people really want to be aware of.
Thank you a lot for providing individuals with a very spectacular possibility to read critical reviews from this site.
My partner and I stumbled over here different website and thought I might as well check things out. I like what I see so now I’m following you. Look forward to checking out your web page repeatedly.
I’m still learning from you, but I’m making my way to the top as well. I absolutely liked reading everything that is written on your website.Keep the aarticles coming. I loved it!
I’ve been absent for some time, but now I remember why I used to love this website. Thanks , I will try and check back more frequently. How frequently you update your site?
Thanks a lot very much for the high quality and results-oriented help. I won’t think twice to endorse your blog post to anybody who wants and needs support about this area.
You truly did more than visitors’ expectations. Thank you for rendering these helpful, trusted, edifying and also cool thoughts on the topic to Kate.
Those guidelines additionally worked to become a good way to recognize that other people online have the identical fervor like mine to grasp great deal more around this condition.
I am commenting to let you know what a terrific experience my daughter enjoyed reading through your web page. She noticed a wide variety of pieces, with the inclusion of what it is like to have an awesome helping style to have the rest without hassle grasp some grueling matters.
Hello! This is my first visit to your blog! We are a team of volunteers and starting a new initiative in a community in the same niche. Your blog provided us useful information to work on. You have done an outstanding job.
Thanks for one marvelous posting! I enjoyed reading it; you are a great author.I will make sure to bookmark your blog and may come back someday. I want to encourage that you continue your great posts, have a nice weekend!
It’s great to come across a blog every once in a while that isn’t the same out of date rehashed material. Fantastic read.
Woah! I’m enjoying the template/theme of this website. It’s simple, yet effective. A lot of times it’s very hard to get that “perfect balance” between superb usability and visual appeal. I must say you’ve done a very good job with this.
obviously like your web site however you have to check the spelling on several of your posts. A number of them are rife with spelling issues and I find it very bothersome to inform the reality however I¡¦ll surely come back again.
hey, would you mind if I share your blog with my twitter group? There’s a lot of folks that I think would enjoy your content. Please let me know. Thank you.
Major thanks for the article.Really thank you! Will read on
It as hard to come by well-informed people on this subject, however, you sound like you know what you are talking about! Thanks
Right away I am ready to do my breakfast, later than having my breakfast coming again to read more news.
I gotta favorite this internet site it seems very helpful very useful
I just want to mention I am just very new to blogs and really savored this web blog. Likely I’m likely to bookmark your blog . You actually come with perfect posts. Thanks a bunch for sharing your web site.
Yeah bookmaking this wasn at a bad determination outstanding post!
Some truly prime content on this website , saved to my bookmarks .
pretty valuable material, overall I believe this is worth a bookmark, thanks
pretty valuable material, overall I believe this is worth a bookmark, thanks
Thanks a lot for the article post.Really looking forward to read more.
It as hard to come by well-informed people on this subject, however, you sound like you know what you are talking about! Thanks
Major thanks for the article.Really thank you! Will read on
pretty valuable material, overall I believe this is worth a bookmark, thanks
Very good article post.Really thank you! Will read on
pretty valuable material, overall I believe this is worth a bookmark, thanks
pretty valuable material, overall I believe this is worth a bookmark, thanks
Very good article post.Really thank you! Will read on
Some truly prime content on this website , saved to my bookmarks .
Yeah bookmaking this wasn at a bad determination outstanding post!
Right away I am ready to do my breakfast, later than having my breakfast coming again to read more news.
I gotta favorite this internet site it seems very helpful very useful
Major thanks for the article.Really thank you! Will read on
Say, you got a nice article post.Really looking forward to read more. Will read on
Major thanks for the article.Really thank you! Will read on
Yeah bookmaking this wasn at a bad determination outstanding post!
Very good article post.Really thank you! Will read on
Very good article post.Really thank you! Will read on
Wow! In tһe еnd I got ɑ web site from ᴡhere I
can in fаct get helpful infⲟrmation гegarding
mʏ study and knowledge.
Іf yoᥙ woulԀ lіke tо increase your familiarity ϳust keep visiting tis website аnd
be updated with the m᧐st ᥙp-to-date gossip posted һere.
What а stuff օf un-ambiguity аnd preserveness of
precious experience on tһe topic of unpredicted feelings.
I simply want to mention I am just new to weblog and seriously savored your web blog. More than likely I’m want to bookmark your site . You absolutely come with exceptional posts. Thanks a bunch for revealing your website page.
Keep up the good work. This site is fantastic!
I’ve never seen a scene which do that before.
Thanks for one’sfor onesfor yourfor your personalfor afor theon your marvelous posting! I actuallyseriouslyquitedefinitelyreallygenuinelytrulycertainly enjoyed reading it, you could beyou areyou can beyou might beyou’reyou will beyou may beyou happen to be a great author. I will make sure toensure that Ibe sure toalwaysmake certain tobe sure toremember to bookmark your blog and willand definitely willand will eventuallyand will oftenand may come back from now ondown the roadin the futurevery soonsomedaylater in lifeat some pointin the foreseeable futuresometime soonlater on. I want to encourage you to ultimatelythat youyourself toyou to definitelyyou toone toyou continue your great jobpostswritingwork, have a nice daymorningweekendholiday weekendafternoonevening!
Keep up the good work Freddie.
No one seems to know what’s going on with that pot of noodles on the stove. I know not a least one of you have looked at them.
HelloHey thereHeyHowdyGood dayHi thereHello thereHi! This post couldn’tcould not be written any better! ReadingReading through this post reminds me of my oldgood oldprevious room mate! He always kept talkingchatting about this. I will forward this articlepagepostwrite-up to him. Pretty sureFairly certain he will have a good read. ThanksThank youMany thanks for sharing!
This particular blog is obviously educating and factual. I have picked up a bunch of useful advices out of this amazing blog. I ad love to return again soon. Thanks a lot!
Sorry for the huge review, but I’m really loving the new Zune, and hope this, as well as the excellent reviews some other people have written, will help you decide if it’s the right choice for you.
“Thanks for your posting. One other thing is the fact that individual states have their own personal laws in which affect people, which makes it very difficult for the Congress to come up with a new set of recommendations concerning home foreclosure on householders. The problem is that every state offers own guidelines which may have impact in an adverse manner with regards to foreclosure procedures.”
I really intend to advise you that I am new to blogging and extremely adored your information. Quite possibly I am most likely to save your blog post . You literally have memorable article material. Admire it for giving out with us the best internet site webpage
This is exactly what I needed
You are my aspiration , I possess few blogs and infrequently run out from to post .
Right away I am ready to do my breakfast, later than having my breakfast coming again to read more news.
I like what you guys are up too. Such clever work and reporting! Keep up the superb works guys I’ve incorporated you guys to my blogroll. I think it will improve the value of my web site :).
I wanted to thank you for this excellent read!! I definitely loved every little bit of it. I have you bookmarked your site to check out the new stuff you post.
Love to read it,Waiting For More new Update and I Already Read your Recent Post its Great Thanks.
What i do not understood is in reality how you’re not actually a lot more smartly-preferred than you may be right now. You are very intelligent. You understand therefore significantly in relation to this topic, produced me individually believe it from numerous varied angles. Its like men and women aren’t interested unless it is something to accomplish with Lady gaga! Your own stuffs nice. All the time take care of it up!
that’s why I bookmarked this page for get news feed with perfectly information in the next coming post ,
Your writing taste has been amazed me. Thank you, very nice article.)
Really appreciate thanks for sharing the post !!!!!
I found so many interesting stuff in your blog especially its discussion. From the tons of comments on your articles, I guess I am not the only one having all the enjoyment here! keep up the good work..
that’s why I bookmarked this page for get news feed with perfectly information in the next coming post ,
No doubt this is an excellent post I got a lot of knowledge after reading good luck. Theme of blog is excellent there is almost everything to read, Brilliant post.
I found so many interesting stuff in your blog especially its discussion. From the tons of comments on your articles, I guess I am not the only one having all the enjoyment here! keep up the good work..
I think that thanks for the valuabe information and insights you have so provided here.
PrettyVery nice post. I just stumbled upon your blogweblog and wantedwished to say that I haveI’ve reallytruly enjoyed browsingsurfing around your blog posts. In any caseAfter all I’llI will be subscribing to your feedrss feed and I hope you write again soonvery soon!
Why userspeopleviewersvisitors still usemake use of to read news papers when in this technological worldglobe everythingallthe whole thing is availableaccessibleexistingpresented on netweb?
HelloHowdyHiyaHeyWhats upGood dayHi there very nicecool blogwebsiteweb sitesite!! GuyMan .. BeautifulExcellent .. AmazingSuperbWonderful .. I willI’ll bookmark your blogwebsiteweb sitesite and take the feeds alsoadditionally? I amI’m satisfiedgladhappy to findto seek outto search out so manynumerousa lot of usefulhelpful informationinfo hereright here in thewithin the postsubmitpublishput up, we needwe’d likewe want developwork out moreextra strategiestechniques in thison this regard, thank youthanks for sharing. . . . . .
Hmm it seemsappearslooks like your sitewebsiteblog ate my first comment (it was extremelysuper long) so I guess I’ll just sum it up what I submittedhad writtenwrote and say, I’m thoroughly enjoying your blog. I as welltoo am an aspiring blog bloggerwriter but I’m still new to the whole thingeverything. Do you have any helpful hintsrecommendationstips and hintspointssuggestionstips for inexperiencedfirst-timerookienovicebeginnernewbie blog writers? I’d certainlydefinitelygenuinelyreally appreciate it.
HeyHowdyWhats upHi thereHeyaHiHey thereHello this is kindasomewhatkind of of off topic but I was wonderingwanting to know if blogs use WYSIWYG editors or if you have to manually code with HTML. I’m starting a blog soon but have no coding knowledgeskillsexperienceknow-howexpertise so I wanted to get adviceguidance from someone with experience. Any help would be greatlyenormously appreciated!
HiHelloHi thereHello thereHowdyGreetings, I thinkI believeI do believeI do thinkThere’s no doubt that your siteyour websiteyour web siteyour blog might bemay becould becould possibly be having browserinternet browserweb browser compatibility issuesproblems. When IWhenever I look at yourtake a look at your websiteweb sitesiteblog in Safari, it looks fine but whenhowever whenhowever, ifhowever, when opening in Internet ExplorerIEI.E., it hasit’s got some overlapping issues. I justI simplyI merely wanted to give you aprovide you with a quick heads up! Other than thatApart from thatBesides thatAside from that, fantasticwonderfulgreatexcellent blogwebsitesite!
I was wonderingcurious if you ever consideredthought of changing the layoutpage layoutstructure of your blogsitewebsite? Its very well written; I love what youve got to say. But maybe you could a little more in the way of content so people could connect with it better. Youve got an awful lot of text for only having one1 or two2 imagespictures. Maybe you could space it out better?
I really can’t believe how great this site is. Keep up the good work. I’m going to tell all my friends about this place.
I have realized that online diploma is getting popular because accomplishing your college degree online has turned into a popular solution for many people. A lot of people have not had a possible opportunity to attend an established college or university nonetheless seek the improved earning possibilities and a better job that a Bachelors Degree grants. Still other individuals might have a degree in one course but would wish to pursue some thing they already have an interest in.
Your own commitment to getting the message during came to be quite potent and have consistently enabled employees just like me to arrive in their desired goals.
I’ve bookmarked your site, and I’m incorporating your RSS feeds to my Google account. {
Really enjoyed this update, can I set it up so I get an alert email whenever there is a new update?
Hello, I check your blogs on a regular basis. Your story-telling style is awesome,keep it up!
With thanks! Valuable information!
Awesome! Its in fact amazing paragraph, I have got much clear idea regarding from this piece of
I added a new list. As you’ll see it’s bigger than most of them. I hope you all have had a great week!
With thanks! Valuable information!
With thanks! Valuable information!
Thank you a lot for providing people with an extremely spectacular possibility to browse critical reviews from this site.