Preface: The Global Data Center Blade Server market is projected to grow at a CAGR of 8.35% during the forecast period, reaching a total market size of US$23.535 billion in 2025 from US$14.548 billion in 2019, said ResearchAndMarkets.com’s.
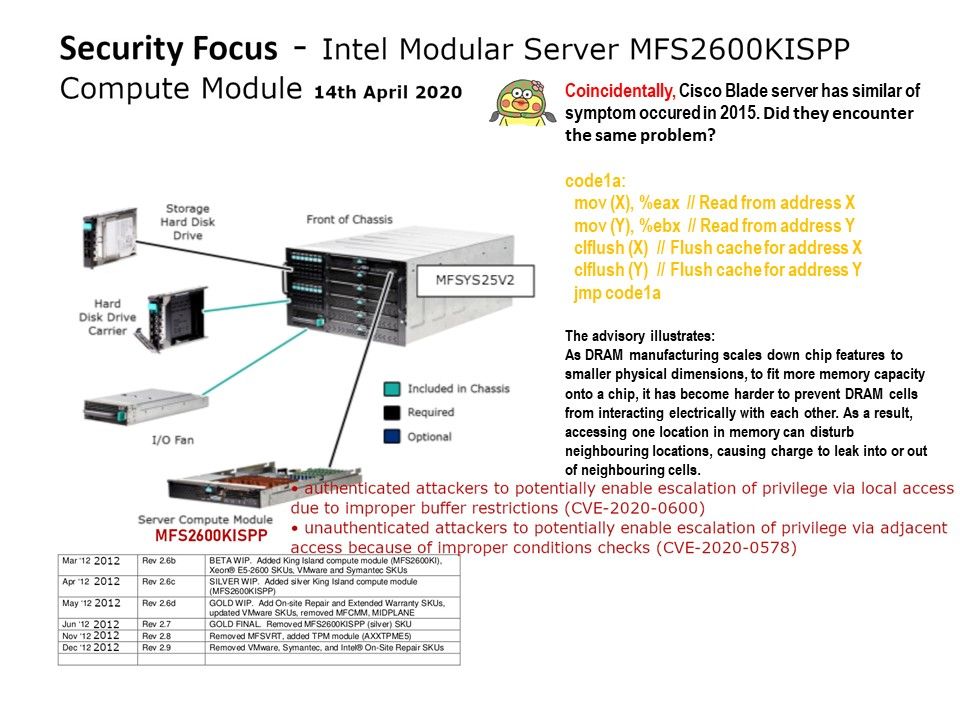
Vulnerability details:
• authenticated attackers to potentially enable escalation of privilege via local access due to improper buffer restrictions (CVE-2020-0600)
• unauthenticated attackers to potentially enable escalation of privilege via adjacent access because of improper conditions checks (CVE-2020-0578)
Observation: Coincidentally, Cisco Blade server has similar of symptom occured in 2015. Did they encounter the same problem?
Synopsis: As DRAM manufacturing scales down chip features to smaller physical dimensions, to fit more memory capacity onto a chip, it has become harder to prevent DRAM cells from interacting electrically with each other. As a result, accessing one location in memory can disturb neighbouring locations, causing charge to leak into or out of neighbouring cells.
Official announcement: https://www.intel.com/content/www/us/en/security-center/advisory/intel-sa-00351.html
.jpg?width=1920&height=1080&fit=bounds)