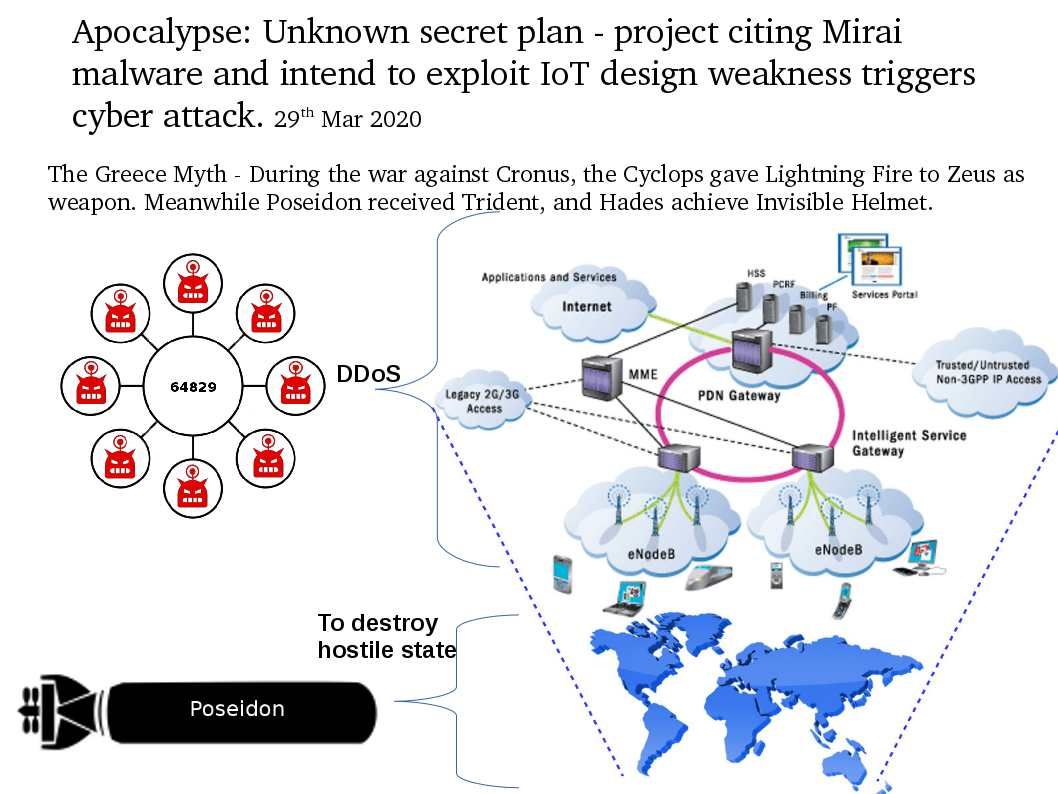
Preface: The Greece Myth – During the war against Cronus, the Cyclops gave Lightning Fire to Zeus as weapon. Meanwhile Poseidon received Trident, and Hades achieve Invisible Helmet.
Background: The strategic outsourced concept of IT services not limited to commercial In-house IT team. It is also practiced in intelligence circles.
The group claimed that it is inspired by Mirai. The primary approach of attack is exploit factory default logins and common username/password combinations for IoT devices. Once a password attack was successful, the device would be integrated into the botnet.
Mirai DDoS attack capabilities include SYN flooding, User Datagram Protocol flooding, ACK flooding and HTTP GET, POST and HEAD attacks. Mirai continues to be successful for a well-known reason: Its targets are IoT devices with hardcoded credentials found in a simple web search.
Details: In past decade, even though how was the attack technique you has. Perhaps the destructive power will be limited by society situation. Comparing today, all the people at least has a mobile phone and wireless router at home. The threat actors can conduct a DDoS to web hosting or collaboration service cloud within an hour. The headline news uncovers the contractors of the Russian national secret service FSB was hack which let the world know this conspiracy.
Perhaps this is a alert signal to smart city.
You may be interested of article shown below: