Headline news today provides a 2nd round of reminder to the world that we are under surveillance. Since our hero Edward Snowden heads up to the world earlier. As a result, he such a way may carry a crime of treason. To be honest , I am a little worry about of him. The fact is that the expectation of president in united stated has been changed. Good luck to him at all! If god is present, please give your son Edward’s assistance. He really need you help!
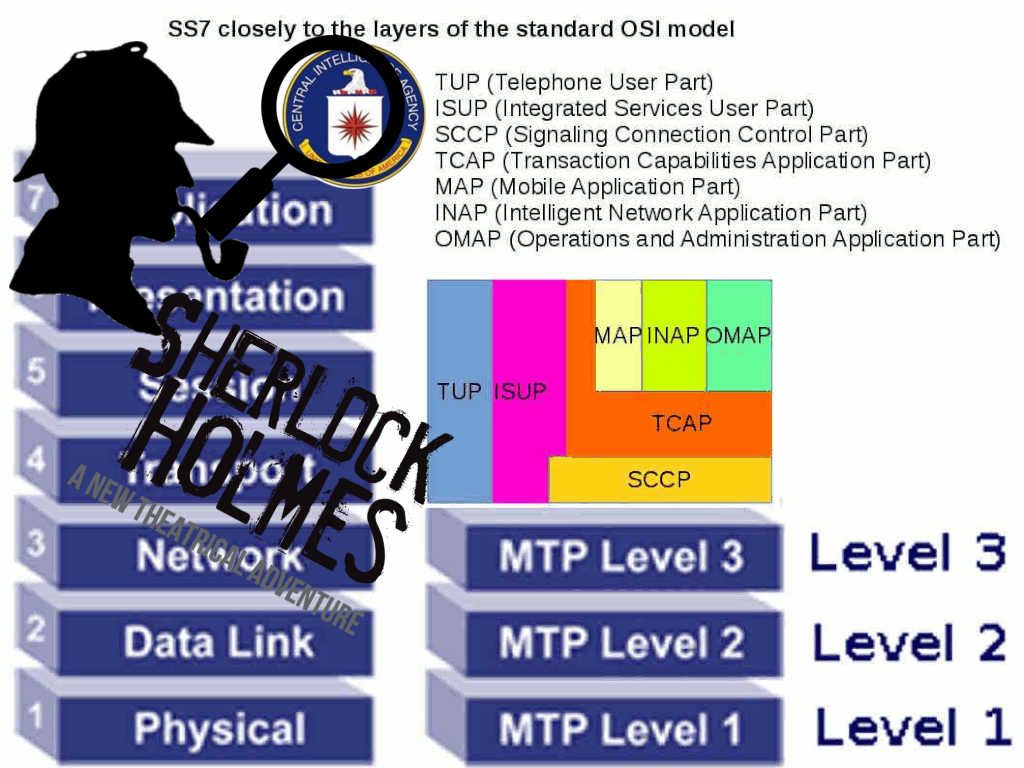
The no. of total 8761 documents posted on wikileak we are not going to discuss here. Just know this is the first full part of the series dubbed Year Zero. However we would like to bring your attention on the weakness of tel-comm industry today. And believed that this is the root causes or you can say this is a backdoor on telecommunication world. Ok, this time all we emulate as Sherlock Holmes. Let’s start.
Speculation
- Flaw found in ASN.1 compiler
Abstract Syntax Notation 1 (ASN.1) background:
Quick and dirty description:
In the field of telecommunications and computer networks, ASN.1 (Abstract Syntax Notation One) is a set of standards describing data representation, encoding, transmission and decoding flexible notation. It provides a formal, unambiguous and precise rules to describe independent of the specific computer hardware object structure. ASN.1 provides application and protocol developers a high-level tool, essentially a data-definition language, for defining protocol syntax and the information that an application exchanges between systems.
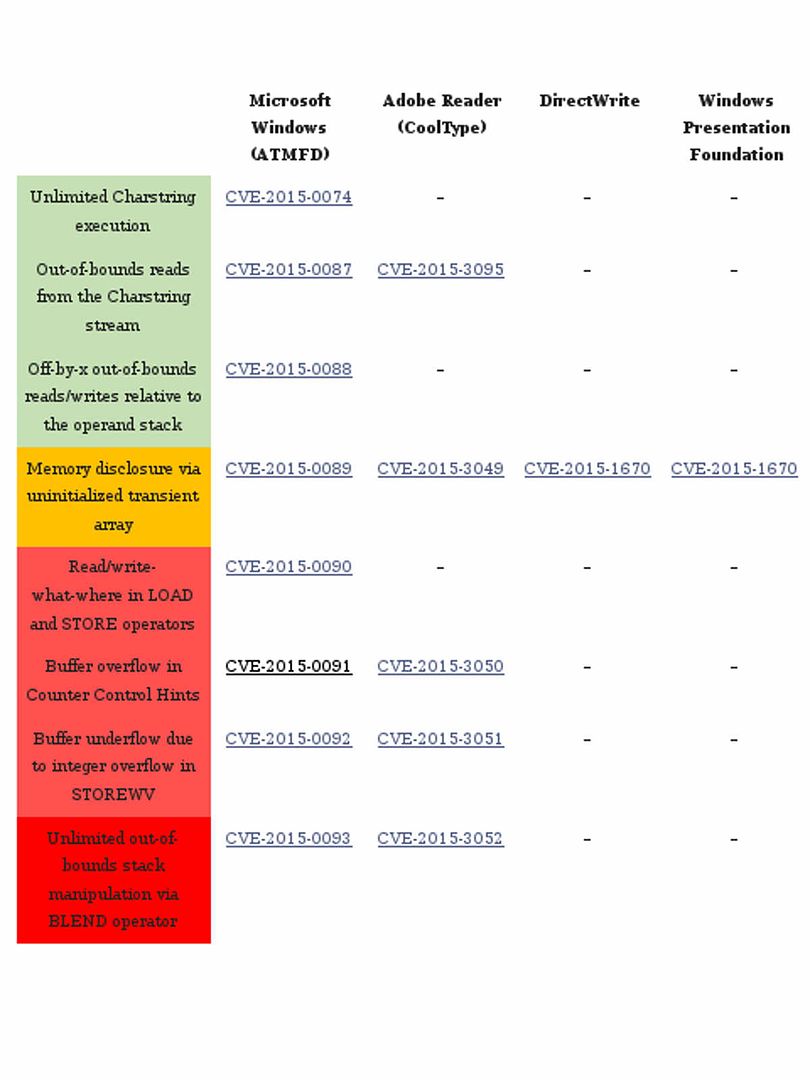
Vulnerability:
A flaw discovered in an ASN.1 compiler, a widely used C/C++ development tool, could have propagated code vulnerable to heap memory corruption attacks, resulting in remote code execution.
Heap memory corruption attacks
Traditional memory corruption exploit can be achieved by pointing to the injected code on the stack or heap which data resides in.
Technical information – vulnerability details
Vulnerability Note VU#790839
Objective Systems ASN1C generates code that contains a heap overflow vulnerability, for more details, please refer to below url for reference.
https://www.kb.cert.org/vuls/id/790839
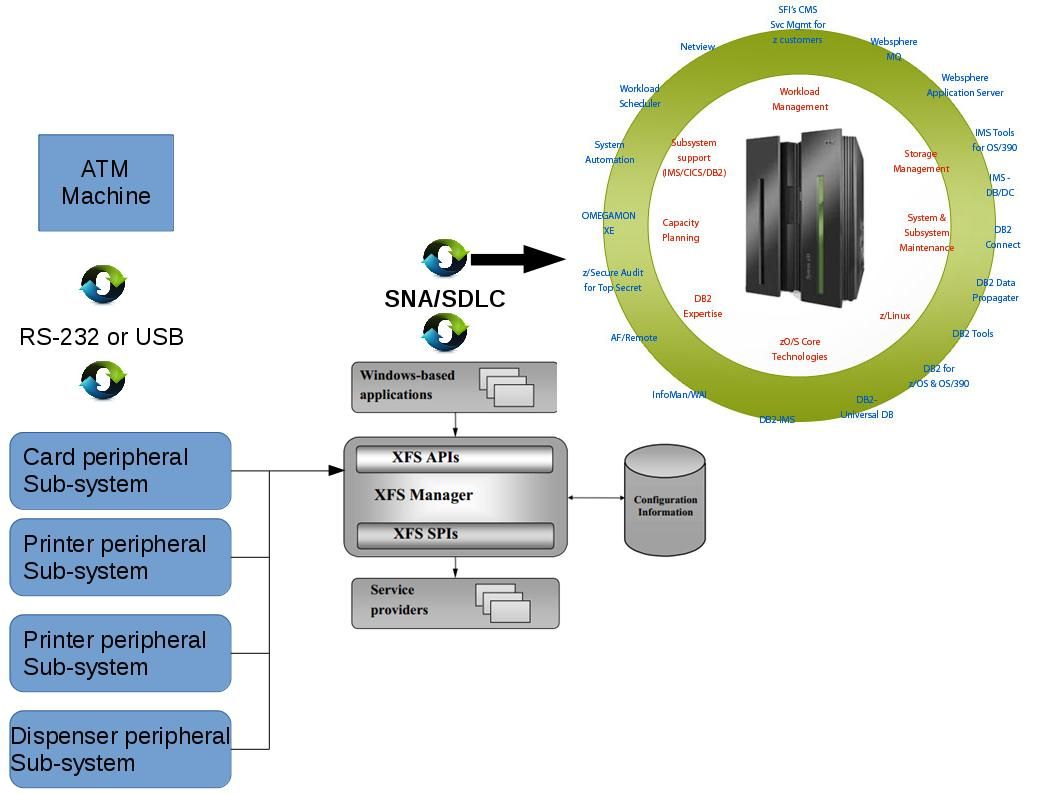
Afterwards, the government agency relies on this design weakness of SS7 to track the movements of the mobile phone user anywhere in the world. From technical point of view, compromise of WhatsApp or Telegram was not direct way. Sometimes no need to install malware to the clients mobile phone. It is exact the abuses of SS7 weaknesses.
2. TCP/IP version 4 (CVE-2016-5696)
The difficult part for hacker taking over TCP connection is to guess the source port of the client and the current sequence number. A group of researchers found that open a connection to the server and send with the source of the attacker as much “RST” handshake packets with the wrong sequence mixed with a few spoofed packets. By counting how much “challenge ACK” handshake packet get returned to the attacker side. Attacker might knowing the rate limit one can infer how much of the spoofed packets resulted in a challenge ACK to the spoofed client and thus how many of the guesses where correct. This way can quickly narrow down which values of port and sequence are correct.

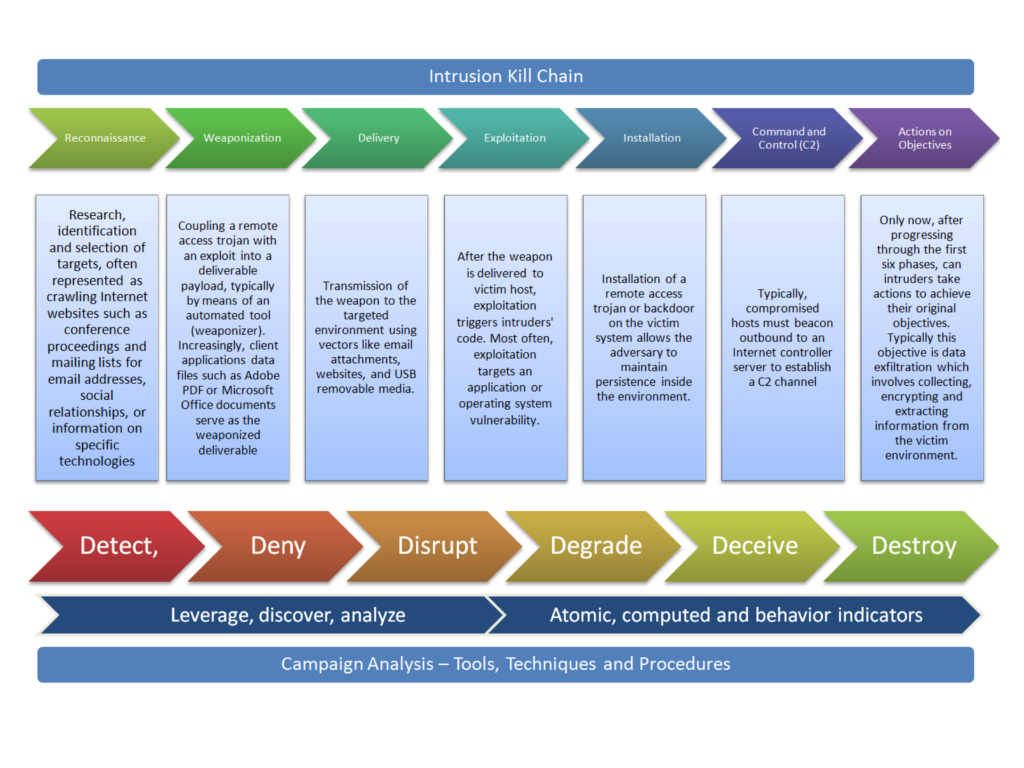
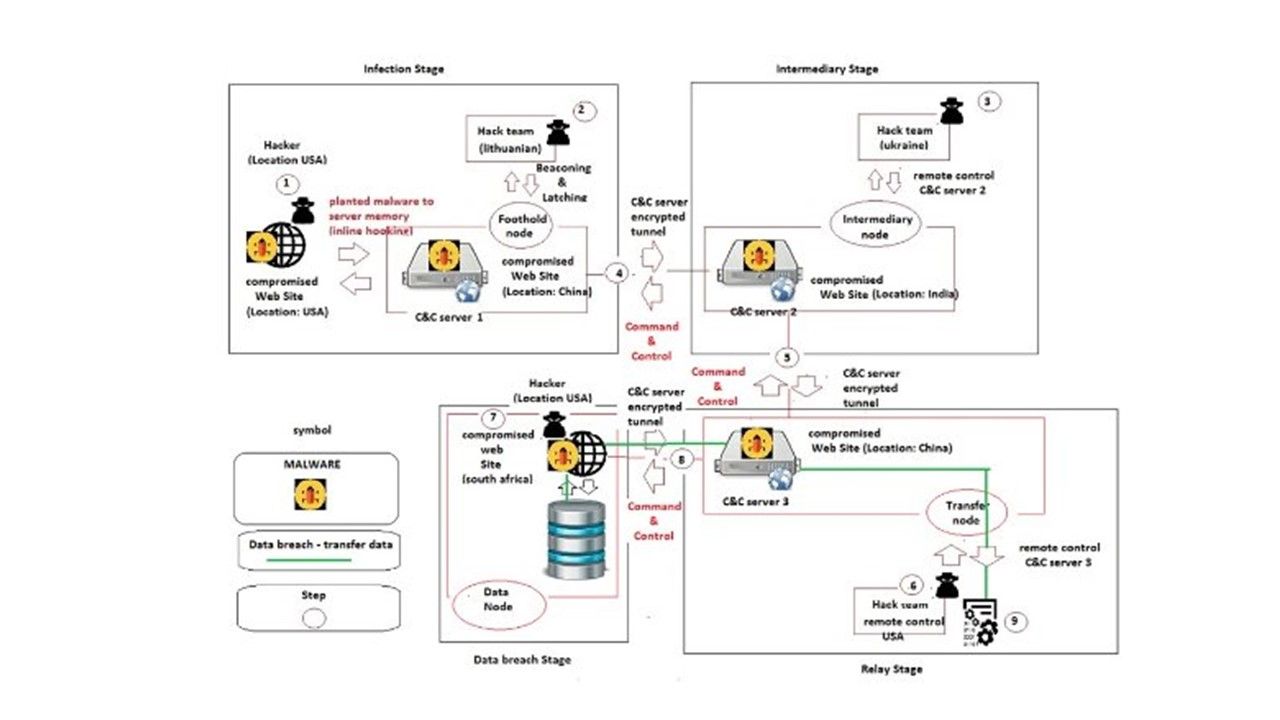
3. Law enforcement backdoor software overview
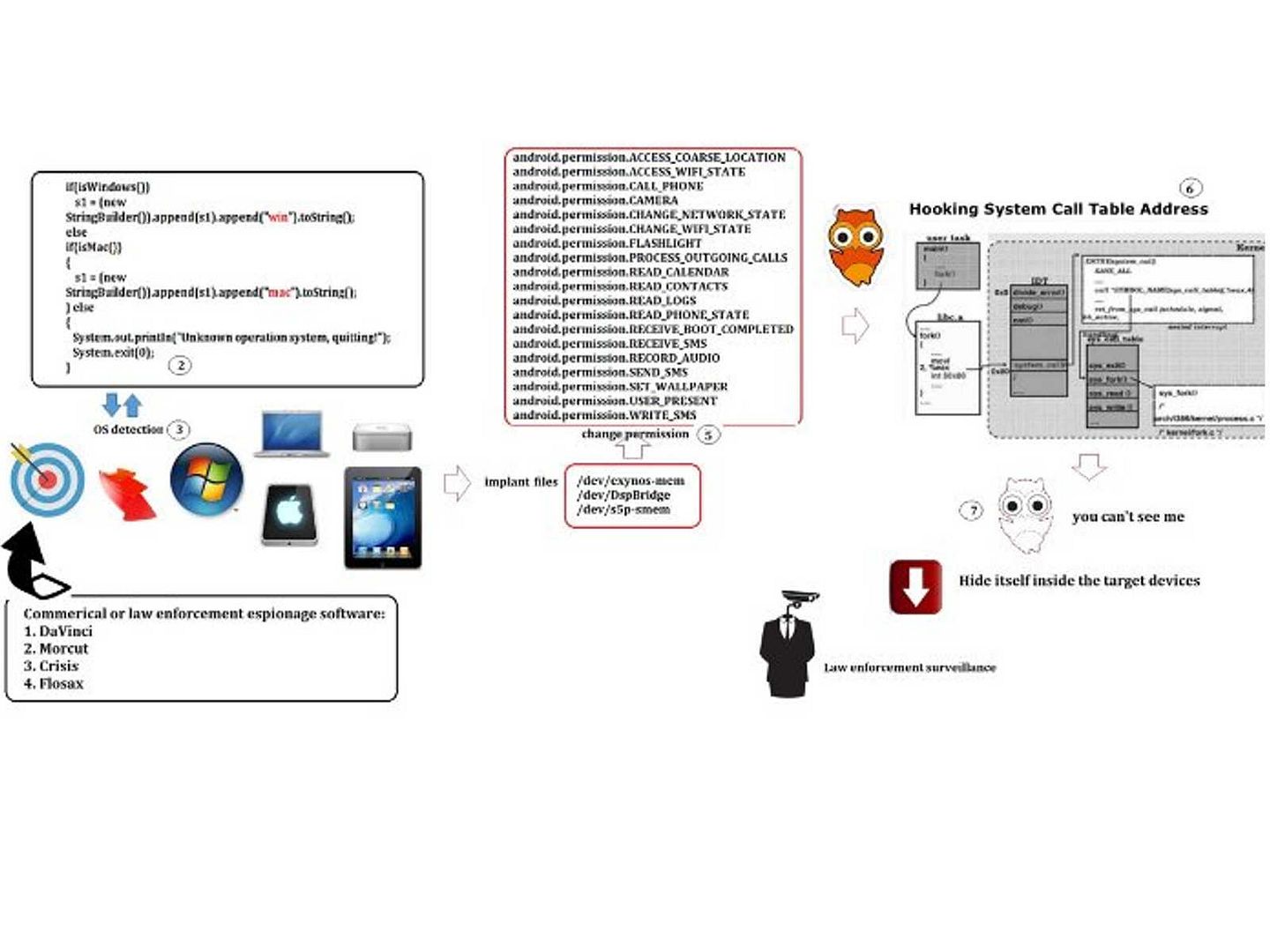
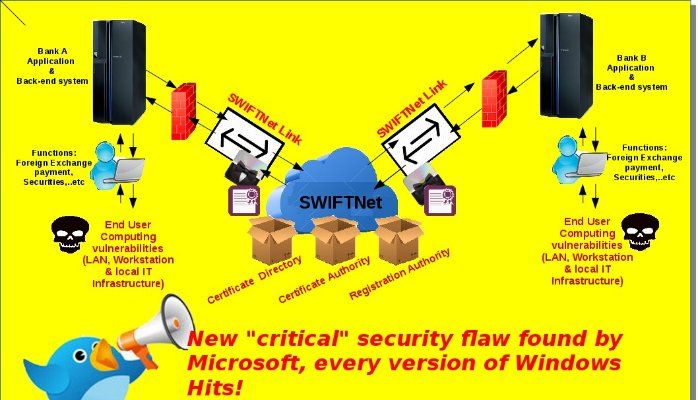
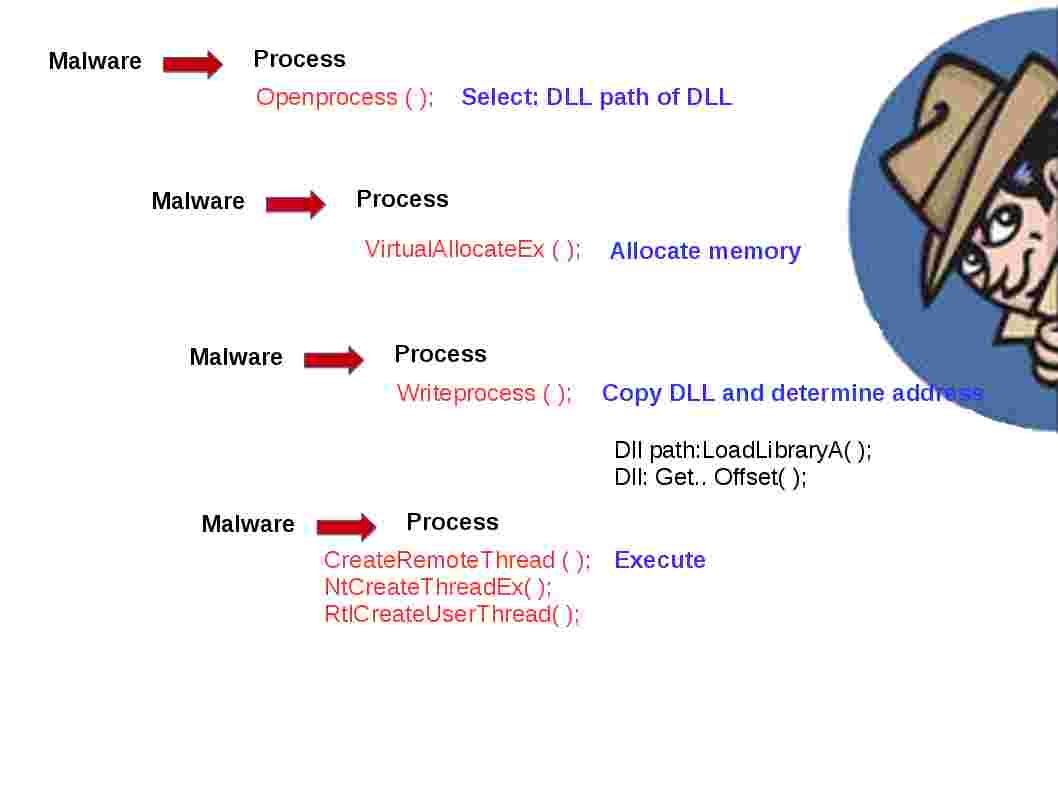
Edward Snowden disclosed global surveillance program in 2013. We all alert that surveillance programs are flooding all around the world. Bring to tech guy attention may more or less is the sniffing technique. How was US government collect personal data and telephone call on our desktop and mobile phone devices? Tech guy with interest on cyber securities may know few hacker group assists law enforcement sector develop monitoring agent software. The brand name includes DaVinci, Morcut, Crisis & Flosax. It looks that the most famous product is the DaVinci. An Italian made surveillance software best perform a lot of actions, such as hidden file transfers, screen capturing, keystroke logging & process injection.
Interest story happened on July 2015
A cyber-surveillance company believes a government may have been behind a massive hack of its systems that saw huge chunks of its code stolen. For more details, please refer to below URL:
http://eandt.theiet.org/news/2015/jul/hacking-team-breach.cfm
After you read this article, you may have questions? Since 2015 data breaches incidents happened in frequent. It is hard to believe that how weakness of cyber defense setup in the world. No matter how many anti defense facilities you built in your firm. Seems there is no appropriate solution to fight against cyber crime. Do you think all the incidents happened within 2015 to 2016 are related hacker code exposed in July 2015?
Reference:
Law enforcement surveillance software technical features:
Available surveillance modules
Accessed files
Address Book
Applications used
Calendar
Contacts
Device Type
Files Accessed
Keylogging
Saved Passwords
Mouse Activity (intended to defeat virtual keyboards)
Record Calls and call data
Screenshots
Take Photographs with webcam
Record Chats
Copy Clipboard
Record Audio from Microphone
With additional Voice and silence detection to conserve space
Realtime audio surveillance (“live mic:” module is only available for Windows Mobile)
Device Position
URLs Visited
Create conference calls (with a silent 3rd party)
Infect other devices (depreciated since v. 8.4)
Suggestion to reader:
Since the world situation became more complex today no matter political and people’s livelihood. A solution will let you easy to know your mobile phone status. Are you under government surveillance program?
If you are android phone user, go to playstore download a free program names SnoopSnitch. The SnoopSnitch which can warn when certain SS7 attacks occur against a phone and can detect voyeur’s jump into your phone.
Bye!