Old school boy might remember fundamental of Virtual storage access method (VSAM). I object, banking and financial institution are close with VSAM technologies day to day. Yes, they are using mainframe computer. For instance IBM S390. People discontentment of proprietary payment solution (SWIFT) sounds high! Hackers targeted payment system via the SWIFT, no significant figures show the security weakness of traditional payment system (SWIFT). Do you think the exploit come from fundamental design or it is the operation weakness? The block chain technology (bitcoins) carry out challenge to traditional payment method. For sure that it is a long run of competition. It includes intangible factors. Example: political, conflict of interest on business side, renovation of traditional payment culture,…etc.
Descendant of VSAM File structure,that is blockchain conceptual technology today
Blockchain technology – who is who?
Blockchain technology confusing me! What is bitcoin blockchain? Or it is Ethereum technology? But heard that there is another digital currencies or digital token. Oh! my god, still have smart contracts! Find the answer conclude that it is list of transactions that is replicated across a number of computers.
i. Blockchain keep track of a currency’s balances.Since it is a decentralized networks, blockchain does not have a central point of failure and is better able to avoid malicious attacks.
ii. Ethereum is an public blockchain-based distributed application platform featuring smart contract functionality.
iii. A smart contract is a digitally signed, computable agreement between two or more parties. A virtual third party work as software agent to execute and enforce at least some of the terms of such agreements.
iv. Digital tokens being used to represent different assets on a blockchain.
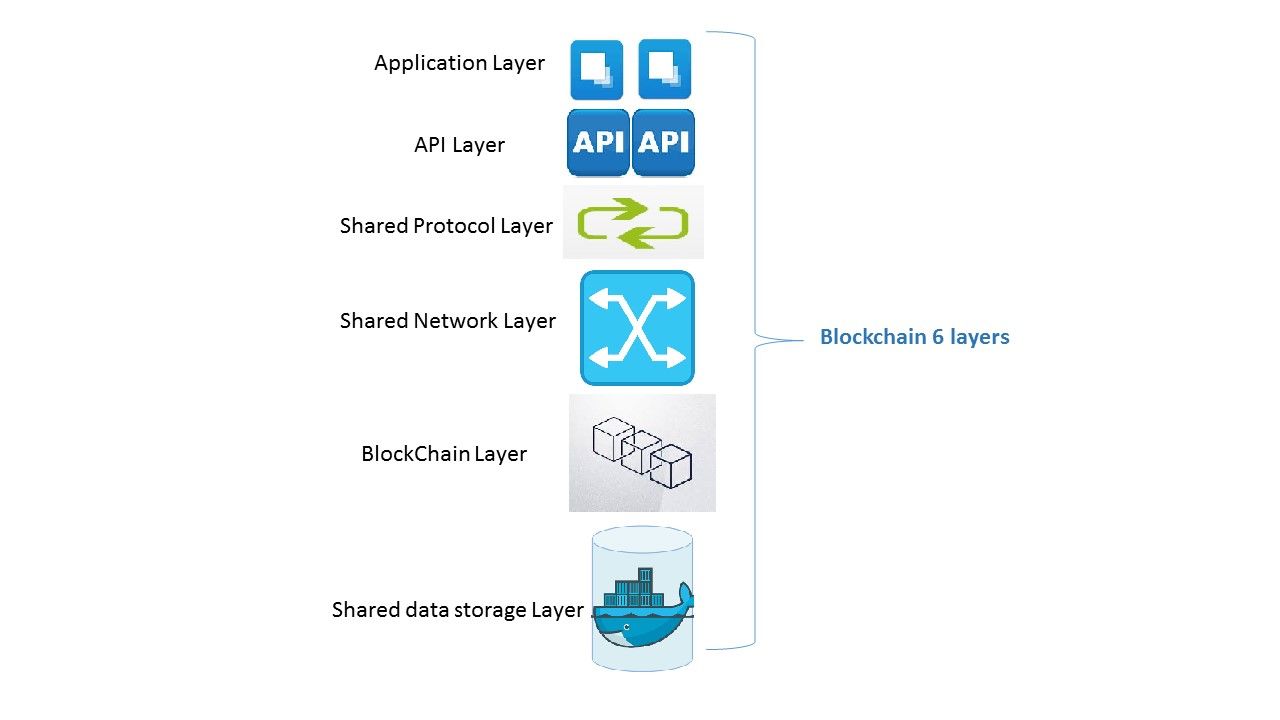
The overall opinion of people feel that BlockChain technologies are advanced compare with traditional payment method. See below diagram, the layering architecture of blockchain not special. If you take a closer look and focus in blockchain and share data storage layer. You will feel that blockchain design concept like IBM Mainframe VSAM file organization structure.
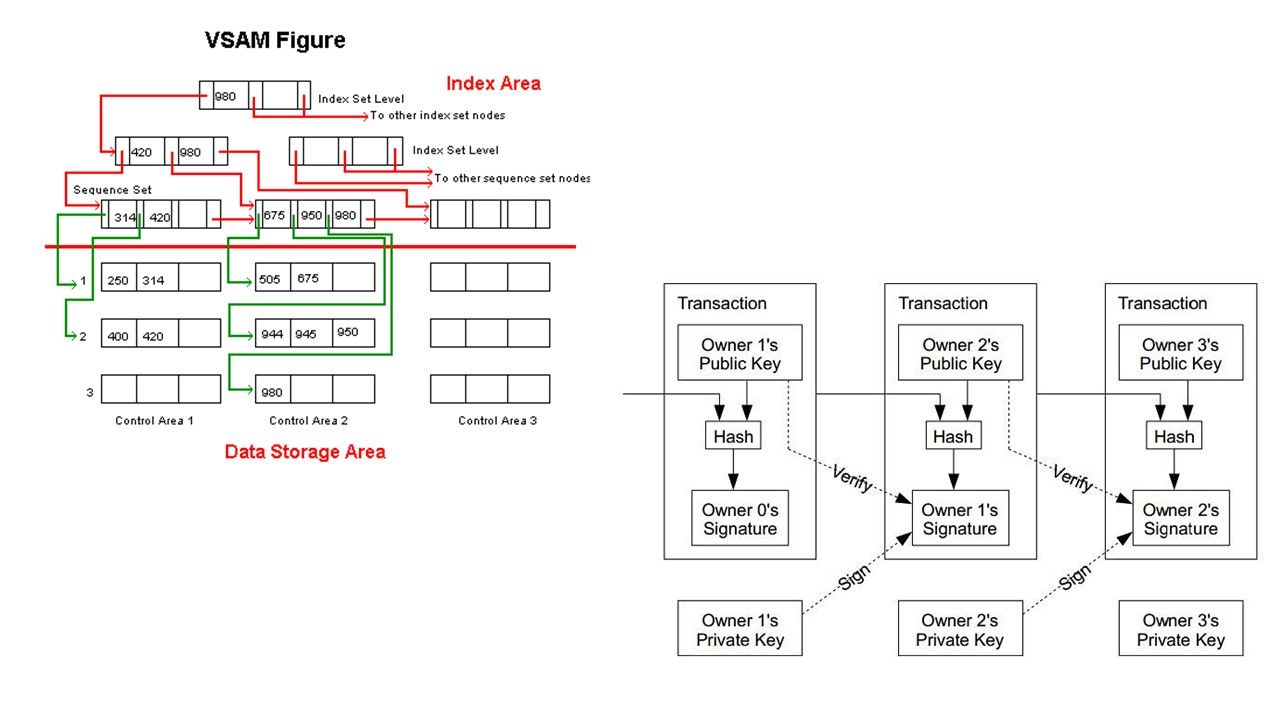
From design point of view, VSAM structure consists of tables, columns, primary keys, indexes, stored procedures, and views (refer to below left hand side diagram). When a direct READ is performed for a VSAM indexed file, based on an alternate index for which duplicates exist, only the first record in the data set (base cluster) with that alternate key value is retrieved. You need a series of READ NEXT statements to retrieve each of the data set records with the same alternate key.
How about block chain design structure? The terminology so called terms includes Transactor, Transaction, Ledger,World stat, Chaincode, Validating peer, Non-validating peer, Consensus and Permissioned network (refer to below right hand side diagram).
Descendant of VSAM File Organization,that is blockchain technology today.
Blockchain Key terms (copy from IBM Bluemix Docs)
The following terms are instrumental in gaining a holistic understanding of blockchain concepts:
Transactor: A network participant connected to the blockchain network through a node, who submits transactions from a client using an SDK or API.
Transaction: A request by a transactor to execute a function on the blockchain network. The transaction types are deploy, invoke, and query, which are implemented through the chaincode functions set forth in the fabric’s API contract.
Ledger: A sequence of cryptographically-linked blocks, containing transactions and the current world state. In addition to data from previous transactions, the ledger also contains the data for currently-running chaincode applications.
World state: Key-value database used by chaincodes to store their state when executed by a transaction.
Chaincode: Embedded logic that encodes the rules for specific types of network transactions. Developers write chaincode applications and deploy them to the network. End users then invoke chaincode through a client-side application that interfaces with a network peer, or node. Chaincode runs network transactions, which if validated, are appended to the shared ledger and modify world state.
Validating peer: A network node that runs the consensus protocol for the network to validate transactions and maintain the ledger. Validated transactions are appended to the ledger, in blocks. If a transaction fails consensus, it is purged from the block and therefore, not written to the ledger. A validating peer (VP) has authority to deploy, invoke and query chaincode.
Non-validating peer: A network node that functions as a proxy, connecting transactors to validating peers. A non-validating peer (NVP) forwards invocation requests to its connected validating peer (VP). It also hosts the event stream server and the REST service.
Consensus: A protocol that maintains the order of blockchain network transactions (deploy and invoke). Validating nodes work collectively to approve transactions by implementing the consensus protocol. Consensus ensures that a quorum of nodes agree on the order of transactions on the shared ledger. By resolving any discrepancies in this order, consensus ensures that all nodes operate on an identical blockchain ledger. See the consensus topic for more information and test cases.
Permissioned network: A blockchain network where each node is required to maintain a member identity on the network, and each node has access to only the transactions that its permissions allow.
For readers who are interested of block chain technology. Please refer below url for reference.
About blockchain (IBM Bluemix Docs)
https://console.ng.bluemix.net/docs/services/blockchain/ibmblockchain_overview.html
Merry Christmas!

Hi there, I found your web site by the use of Google even as looking for a related matter, your site got here up, it seems to be great. I’ve bookmarked it in my google bookmarks.
Great post.
My family every time say that I am killing my time here at net, but I know I am getting familiarity daily
by reading thes nice articles or reviews.
I simply want to say I’m all new to blogging and site-building and definitely loved you’re web page. Most likely I’m likely to bookmark your site . You really have beneficial writings. Appreciate it for revealing your blog site.
I was just looking for this info for a while. After 6 hours of continuous Googleing, finally I got it in your site. I wonder what is the lack of Google strategy that don’t rank this type of informative sites in top of the list. Normally the top sites are full of garbage.
I¡¦ve been exploring for a little for any high-quality articles or blog posts on this kind of house . Exploring in Yahoo I eventually stumbled upon this website. Reading this info So i am satisfied to express that I have an incredibly excellent uncanny feeling I came upon just what I needed. I so much surely will make certain to don¡¦t omit this web site and provides it a look regularly.
I have not checked in here for a while since I thought it was getting boring, but the last several posts are great quality so I guess I will add you back to my everyday bloglist. You deserve it my friend 🙂
Somebody necessarily help to make severely posts I would state. That is the very first time I frequented your website page and to this point? I amazed with the research you made to make this actual publish extraordinary. Fantastic task!
I keep listening to the news bulletin speak about getting boundless online grant applications so I have been looking around for the most excellent site to get one. Could you advise me please, where could i find some?
I¡¦ve been exploring for a little bit for any high-quality articles or blog posts on this kind of area . Exploring in Yahoo I eventually stumbled upon this web site. Studying this info So i am happy to convey that I’ve a very good uncanny feeling I discovered exactly what I needed. I such a lot certainly will make sure to do not disregard this website and provides it a look on a constant basis.
Thank you for the good writeup. It in fact was a amusement account it. Look advanced to far added agreeable from you! By the way, how can we communicate?
It¡¦s actually a nice and helpful piece of information. I am happy that you shared this useful info with us. Please keep us up to date like this. Thank you for sharing.
whoah this blog is magnificent i love reading your articles. Stay up the good work! You already know, lots of persons are hunting around for this info, you can help them greatly.
hello there and thank you for your info – I have definitely picked up anything new from right here. I did however expertise some technical issues using this web site, as I experienced to reload the site lots of times previous to I could get it to load properly. I had been wondering if your hosting is OK? Not that I am complaining, but sluggish loading instances times will often affect your placement in google and can damage your quality score if advertising and marketing with Adwords. Anyway I am adding this RSS to my email and can look out for a lot more of your respective intriguing content. Make sure you update this again very soon..
Wonderful paintings! That is the type of information that are meant to be shared around the net. Shame on Google for no longer positioning this publish upper! Come on over and discuss with my website . Thanks =)
I would like to thank you for the efforts you have put in writing this blog. I am hoping the same high-grade web site post from you in the upcoming also. Actually your creative writing skills has encouraged me to get my own website now. Really the blogging is spreading its wings quickly. Your write up is a good example of it.
hello there and thank you for your information – I’ve definitely picked up something new from right here. I did however expertise several technical issues using this site, as I experienced to reload the website lots of times previous to I could get it to load properly. I had been wondering if your web host is OK? Not that I am complaining, but sluggish loading instances times will sometimes affect your placement in google and could damage your quality score if ads and marketing with Adwords. Anyway I am adding this RSS to my e-mail and can look out for a lot more of your respective intriguing content. Make sure you update this again very soon..
I think other web site proprietors should take this website as an model, very clean and fantastic user genial style and design, as well as the content. You are an expert in this topic!
Wonderful paintings! That is the type of information that should be shared across the web. Disgrace on the seek engines for now not positioning this submit upper! Come on over and visit my web site . Thank you =)
I truly appreciate this post. I have been looking everywhere for this! Thank goodness I found it on Bing. You have made my day! Thank you again
Thank you for another informative site. Where else may I am getting that type of info written in such a perfect manner? I have a challenge that I’m simply now operating on, and I’ve been on the glance out for such information.
Very efficiently written story. It will be beneficial to everyone who employess it, including yours truly :). Keep up the good work – i will definitely read more posts.
I carry on listening to the reports lecture about getting free online grant applications so I have been looking around for the most excellent site to get one. Could you tell me please, where could i find some?
Great post and right to the point. I am not sure if this is in fact the best place to ask but do you guys have any thoughts on where to get some professional writers? Thanks in advance 🙂
I cling on to listening to the reports speak about getting free online grant applications so I have been looking around for the finest site to get one. Could you advise me please, where could i find some?
Good web site! I really love how it is simple on my eyes and the data are well written. I am wondering how I could be notified when a new post has been made. I have subscribed to your feed which must do the trick! Have a nice day!
Its like you read my mind! You seem to know a lot about this, like you wrote the book in it or something. I think that you can do with some pics to drive the message home a bit, but instead of that, this is wonderful blog. An excellent read. I’ll definitely be back.
Hello, i think that i saw you visited my web site thus i came to “return the favor”.I’m attempting to find things to improve my site!I suppose its ok to use some of your ideas!!
Heya i’m for the first time here. I found this board and I find It truly useful & it helped me out much. I hope to give something back and aid others like you aided me.
Wow, wonderful weblog format! How lengthy have you ever been running a blog for? you make blogging look easy. The whole glance of your site is wonderful, let alone the content material!
I loved as much as you’ll receive carried out right here. The sketch is attractive, your authored subject matter stylish. nonetheless, you command get got an shakiness over that you wish be delivering the following. unwell unquestionably come more formerly again since exactly the same nearly a lot often inside case you shield this increase.
It is appropriate time to make some plans for the future and it’s time to be happy. I have read this post and if I could I wish to suggest you few interesting things or tips. Perhaps you can write next articles referring to this article. I wish to read more things about it!
Wonderful beat ! I wish to apprentice while you amend your web site, how could i subscribe for a blog web site? The account aided me a acceptable deal. I had been tiny bit acquainted of this your broadcast provided bright clear concept
Hello, Neat post. There is a problem along with your web site in internet explorer, might check this¡K IE still is the marketplace chief and a big portion of other people will leave out your wonderful writing due to this problem.
Pretty section of content. I just stumbled upon your web site and in accession capital to assert that I acquire in fact enjoyed account your blog posts. Anyway I’ll be subscribing to your augment and even I achievement you access consistently fast.
Excellent beat ! I would like to apprentice while you amend your site, how could i subscribe for a blog website? The account helped me a acceptable deal. I had been a little bit acquainted of this your broadcast provided bright clear concept
This is really interesting, You’re a very skilled blogger. I’ve joined your feed and look forward to seeking more of your fantastic post. Also, I’ve shared your web site in my social networks!
Great blog! I am loving it!! Will be back later to read some more. I am taking your feeds also
Whats Taking place i’m new to this, I stumbled upon this I have found It absolutely useful and it has helped me out loads. I’m hoping to give a contribution & help different users like its aided me. Good job.
I’m extremely impressed with your writing skills and also with the layout on your blog. Is this a paid theme or did you modify it yourself? Either way keep up the nice quality writing, it’s rare to see a great blog like this one today..
Good ¡V I should certainly pronounce, impressed with your site. I had no trouble navigating through all the tabs as well as related information ended up being truly easy to do to access. I recently found what I hoped for before you know it in the least. Reasonably unusual. Is likely to appreciate it for those who add forums or anything, website theme . a tones way for your customer to communicate. Nice task..
I think this is one of the most significant info for me. And i am glad reading your article. But should remark on few general things, The site style is wonderful, the articles is really nice : D. Good job, cheers
What i don’t realize is if truth be told how you’re not actually a lot more neatly-appreciated than you might be right now. You’re so intelligent. You realize therefore considerably with regards to this topic, made me individually imagine it from a lot of various angles. Its like women and men are not involved except it is something to do with Woman gaga! Your individual stuffs nice. All the time deal with it up!
Nice read, I just passed this onto a friend who was doing a little research on that. And he just bought me lunch since I found it for him smile So let me rephrase that: Thank you for lunch!
You completed a few good points there. I did a search on the topic and found nearly all people will agree with your blog.
I have been absent for some time, but now I remember why I used to love this site. Thanks , I¡¦ll try and check back more often. How frequently you update your web site?
We’re a group of volunteers and opening a new scheme in our community. Your website offered us with valuable info to work on. You’ve done an impressive job and our whole community will be grateful to you.
As I web site possessor I believe the content matter here is rattling excellent , appreciate it for your efforts. You should keep it up forever! Best of luck.
Hi, Neat post. There is an issue with your site in web explorer, could check this¡K IE nonetheless is the market chief and a good portion of other folks will miss your excellent writing because of this problem.
I’ve been surfing online more than 3 hours today, yet I never found any interesting article like yours. It’s pretty worth enough for me. In my opinion, if all site owners and bloggers made good content as you did, the net will be a lot more useful than ever before.
I have been surfing online more than three hours lately, but I never found any fascinating article like yours. It is beautiful worth enough for me. In my opinion, if all site owners and bloggers made excellent content material as you did, the net will be much more helpful than ever before.
Heya i’m for the first time here. I found this board and I find It really useful & it helped me out a lot. I hope to give something back and aid others like you helped me.
Hello.This post was extremely interesting, particularly since I was browsing for thoughts on this issue last Saturday.
I¡¦ve been exploring for a bit for any high-quality articles or blog posts in this sort of house . Exploring in Yahoo I eventually stumbled upon this website. Studying this info So i¡¦m satisfied to exhibit that I’ve a very good uncanny feeling I found out just what I needed. I most definitely will make certain to do not disregard this site and provides it a glance regularly.
Good day very cool website!! Man .. Excellent .. Wonderful .. I’ll bookmark your blog and take the feeds additionally¡KI’m glad to find so many useful information here in the submit, we need work out more strategies on this regard, thanks for sharing. . . . . .
I simply wanted to appreciate you all over again. I do not know what I would have achieved in the absence of those points contributed by you relating to such theme. It absolutely was a daunting crisis in my view, however , considering this specialized way you handled that forced me to jump for delight. I’m thankful for the information and in addition have high hopes you really know what a powerful job that you’re putting in educating the mediocre ones with the aid of your website. Most likely you’ve never encountered all of us.
Great site. Lots of helpful info here. I¡¦m sending it to a few pals ans also sharing in delicious. And obviously, thanks for your sweat!
Wow, incredible blog layout! How long have you ever been blogging for? you make blogging glance easy. The total glance of your website is magnificent, let alone the content!
Thanks for another great post. Where else may anybody get that type of info in such an ideal means of writing? I have a presentation subsequent week, and I am on the look for such info.
Wow, marvelous blog layout! How long have you been blogging for? you make blogging look easy. The overall look of your website is excellent, let alone the content!
I do consider all of the ideas you’ve presented to your post. They are very convincing and will definitely work. Still, the posts are too short for beginners. Could you please lengthen them a little from subsequent time? Thanks for the post.
Fantastic web site. A lot of useful information here. I am sending it to a few pals ans also sharing in delicious. And obviously, thank you in your sweat!
Nice read, I just passed this onto a colleague who was doing a little research on that. And he actually bought me lunch because I found it for him smile So let me rephrase that: Thank you for lunch!
Whats Going down i am new to this, I stumbled upon this I’ve found It positively useful and it has helped me out loads. I’m hoping to contribute & aid different customers like its helped me. Good job.
Hiya, I am really glad I have found this information. Today bloggers publish only about gossips and internet and this is actually annoying. A good site with interesting content, this is what I need. Thank you for keeping this web site, I will be visiting it. Do you do newsletters? Can not find it.
Thank you for the good writeup. It in fact was a amusement account it. Look advanced to more added agreeable from you! By the way, how could we communicate?
Hi there very cool web site!! Man .. Beautiful .. Wonderful .. I’ll bookmark your site and take the feeds additionally¡KI am satisfied to find a lot of useful information right here in the post, we’d like work out extra techniques on this regard, thank you for sharing. . . . . .
Thank you for sharing excellent informations. Your web site is so cool. I’m impressed by the details that you have on this website. It reveals how nicely you perceive this subject. Bookmarked this website page, will come back for more articles. You, my friend, ROCK! I found just the info I already searched all over the place and just could not come across. What an ideal website.
Thank you a lot for sharing this with all people you really realize what you’re speaking about! Bookmarked. Kindly also seek advice from my website =). We could have a link exchange arrangement between us!
Thank you for any other wonderful article. Where else may just anybody get that type of info in such a perfect means of writing? I’ve a presentation next week, and I am on the search for such information.
I loved as much as you will receive carried out right here. The sketch is attractive, your authored subject matter stylish. nonetheless, you command get bought an nervousness over that you wish be delivering the following. unwell unquestionably come more formerly again as exactly the same nearly a lot often inside case you shield this hike.
fantastic points altogether, you just won a new reader. What could you suggest about your submit that you made a few days in the past? Any certain?
Hiya, I’m really glad I have found this information. Today bloggers publish only about gossips and net and this is really annoying. A good web site with interesting content, that’s what I need. Thank you for keeping this website, I’ll be visiting it. Do you do newsletters? Can’t find it.
whoah this weblog is magnificent i like studying your posts. Keep up the great paintings! You already know, many persons are looking around for this info, you could help them greatly.
I like what you guys are up also. Such smart work and reporting! Keep up the superb works guys I¡¦ve incorporated you guys to my blogroll. I think it’ll improve the value of my web site 🙂
I have to express my thanks to the writer just for rescuing me from this matter. Just after looking throughout the world wide web and seeing recommendations which were not helpful, I assumed my entire life was over. Living without the presence of solutions to the issues you have solved as a result of your main article content is a crucial case, and the kind which might have in a wrong way affected my career if I had not come across your blog post. The understanding and kindness in touching a lot of things was very useful. I’m not sure what I would have done if I hadn’t encountered such a subject like this. I’m able to at this point look ahead to my future. Thanks a lot so much for this skilled and result oriented help. I will not think twice to refer your blog to anybody who should get assistance on this subject matter.
Nice read, I just passed this onto a friend who was doing some research on that. And he just bought me lunch since I found it for him smile Therefore let me rephrase that: Thanks for lunch!
It is perfect time to make some plans for the future and it’s time to be happy. I’ve read this post and if I could I want to suggest you few interesting things or tips. Perhaps you can write next articles referring to this article. I desire to read even more things about it!
What i do not realize is in reality how you’re now not actually much more neatly-liked than you might be now. You’re so intelligent. You understand therefore considerably on the subject of this topic, produced me individually imagine it from so many various angles. Its like men and women are not interested unless it¡¦s one thing to accomplish with Woman gaga! Your individual stuffs nice. Always maintain it up!
I truly appreciate this post. I¡¦ve been looking everywhere for this! Thank goodness I found it on Bing. You’ve made my day! Thanks again
There is perceptibly a bunch to know about this. I think you made some good points in features also.
It’s the right occasion to have some schemes for the upcoming. I have browsed this post and if I may possibly, I desire to suggest you a few insightful proposal.
I was excited to find this page. I need to to thank you for ones time due to this fantastic read!! I definitely loved every bit of it and i also have you saved to fav to look at new stuff on your blog.
Howdy here, just turned alert to your blog page through Search engines like google, and have found that it’s seriously useful. I will be grateful for in the event you continue such.
I merely hope to share it with you that I am new to blogging and absolutely loved your report. More than likely I am likely to bookmark your blog post . You indeed have superb article materials. Delight In it for share-out with us your favorite web report
I really hope to notify you that I am new to putting up a blog and certainly loved your article. Quite possibly I am probably to save your blog post . You really have outstanding article blog posts. Be Thankful For it for giving out with us your current domain post
Hello.This article was really fascinating, especially because I was searching for thoughts on this subject last Thursday.
You made some decent points there. I did a search on the topic and found most people will agree with your site.
Keep working ,splendid job!
Thanks for the sensible critique. Me & my neighbor were just preparing to do a little research about this. We got a grab a book from our local library but I think I learned more from this post. I’m very glad to see such wonderful information being shared freely out there.
great issues altogether, you just received a brand new reader. What might you recommend in regards to your put up that you simply made some days ago? Any sure?
Wow! This could be one particular of the most useful blogs We have ever arrive across on this subject. Basically Magnificent. I’m also an expert in this topic so I can understand your effort.
What i do not realize is if truth be told how you’re now not really a lot more smartly-favored than you might be now. You are very intelligent. You recognize therefore significantly in relation to this topic, made me individually believe it from a lot of varied angles. Its like men and women aren’t involved except it is one thing to do with Woman gaga! Your individual stuffs excellent. At all times deal with it up!
Great tremendous things here. I am very happy to look your article. Thanks so much and i am taking a look ahead to touch you. Will you kindly drop me a e-mail?
Excellent weblog here! Additionally your website quite a bit up very fast! What host are you the usage of? Can I get your associate link in your host? I wish my web site loaded up as fast as yours lol
Keep working ,terrific job!
Hello there, I found your web site by means of Google while searching for a comparable subject, your site came up, it seems to be good. I have bookmarked it in my google bookmarks.
I think other web-site proprietors should take this site as an model, very clean and excellent user genial style and design, as well as the content. You’re an expert in this topic!
hey there and thank you for your info – I’ve certainly picked up anything new from right here. I did however expertise some technical points using this website, since I experienced to reload the site a lot of times previous to I could get it to load properly. I had been wondering if your web hosting is OK? Not that I’m complaining, but slow loading instances times will sometimes affect your placement in google and can damage your high quality score if ads and marketing with Adwords. Anyway I’m adding this RSS to my email and can look out for much more of your respective intriguing content. Make sure you update this again very soon..
You completed a few fine points there. I did a search on the subject and found the majority of persons will have the same opinion with your blog.
I do not even know how I ended up here, but I thought this post was great. I do not know who you are but certainly you are going to a famous blogger if you aren’t already 😉 Cheers!
Hi my friend! I want to say that this article is awesome, nice written and include approximately all significant infos. I would like to look more posts like this .
Thanks for every one of your effort on this web site. Gloria really likes engaging in internet research and it’s obvious why. Most people hear all concerning the powerful mode you produce reliable ideas on your website and recommend response from some other people on the idea plus our own simple princess has been being taught a lot. Enjoy the rest of the new year. You’re conducting a wonderful job.
Wow! This can be one particular of the most helpful blogs We’ve ever arrive across on this subject. Actually Magnificent. I’m also an expert in this topic therefore I can understand your hard work.
I’ve been surfing online more than 3 hours today, yet I never found any interesting article like yours. It’s pretty worth enough for me. In my opinion, if all website owners and bloggers made good content as you did, the web will be a lot more useful than ever before.
Great write-up, I¡¦m normal visitor of one¡¦s site, maintain up the excellent operate, and It is going to be a regular visitor for a lengthy time.
I think this is one of the most significant info for me. And i’m glad reading your article. But wanna remark on some general things, The site style is great, the articles is really great : D. Good job, cheers
Useful info. Lucky me I found your site unintentionally, and I am shocked why this coincidence did not came about earlier! I bookmarked it.
I like what you guys are up too. Such smart work and reporting! Carry on the excellent works guys I have incorporated you guys to my blogroll. I think it will improve the value of my site 🙂
You are my breathing in, I possess few blogs and sometimes run out from post :). “Never mistake motion for action.” by Ernest Hemingway.
I don’t even know how I ended up here, but I thought this post was great. I do not know who you are but certainly you are going to a famous blogger if you are not already 😉 Cheers!
I got what you intend, regards for posting .Woh I am delighted to find this website through google. “I would rather be a coward than brave because people hurt you when you are brave.” by E. M. Forster.
It’s very trouble-free to find out any topic on net as compared to books, as I found this post at this web site.|
Hey there, You’ve done an excellent job. I’ll certainly digg it and personally suggest to my friends. I am confident they will be benefited from this web site.
I haven’t checked in here for a while as I thought it was getting boring, but the last few posts are great quality so I guess I will add you back to my everyday bloglist. You deserve it my friend 🙂
I am always looking online for articles that can aid me. Thanks!
Very efficiently written story. It will be useful to everyone who utilizes it, including myself. Keep doing what you are doing – i will definitely read more posts.
I enjoy, result in I found just what I used to be taking a look for. You’ve ended my 4 day lengthy hunt! God Bless you man. Have a great day. Bye
I went over this internet site and I believe you have a lot of excellent info, saved to favorites (:.
There is obviously a lot to realize about this. I suppose you made various good points in features also.
Hello. fantastic job. I did not expect this. This is a fantastic story. Thanks!
Thank you for sharing excellent informations. Your web-site is so cool. I’m impressed by the details that you have on this blog. It reveals how nicely you understand this subject. Bookmarked this website page, will come back for extra articles. You, my pal, ROCK! I found just the info I already searched everywhere and just could not come across. What an ideal website.
As a Newbie, I am always searching online for articles that can aid me. Thank you
Wonderful website. Plenty of helpful information here. I¡¦m sending it to some buddies ans additionally sharing in delicious. And of course, thanks for your effort!
Somebody necessarily assist to make critically articles I might state. That is the very first time I frequented your web page and thus far? I amazed with the research you made to make this particular publish amazing. Great task!
I have been examinating out some of your posts and i can state pretty clever stuff. I will surely bookmark your website.
Hiya, I’m really glad I’ve found this information. Nowadays bloggers publish only about gossips and net and this is actually frustrating. A good web site with interesting content, that’s what I need. Thank you for keeping this website, I’ll be visiting it. Do you do newsletters? Can not find it.
I wish to point out my admiration for your kind-heartedness in support of folks who should have help with your subject matter. Your very own commitment to getting the message all around has been surprisingly effective and have frequently allowed workers like me to achieve their dreams. Your personal valuable help denotes much a person like me and even further to my office workers. Thank you; from all of us.
I¡¦ll immediately seize your rss feed as I can not in finding your email subscription link or newsletter service. Do you’ve any? Kindly allow me recognize in order that I may subscribe. Thanks.
Excellent read, I just passed this onto a friend who was doing some research on that. And he just bought me lunch because I found it for him smile So let me rephrase that: Thank you for lunch!
I’m still learning from you, but I’m trying to reach my goals. I certainly liked reading all that is posted on your website.Keep the information coming. I liked it!
Thank you for the sensible critique. Me and my neighbor were just preparing to do some research on this. We got a grab a book from our area library but I think I learned more from this post. I’m very glad to see such great info being shared freely out there.
Just wish to say your article is as astounding. The clearness in your post is simply nice and i can assume you’re an expert on this subject. Fine with your permission let me to grab your RSS feed to keep up to date with forthcoming post. Thanks a million and please continue the gratifying work.
I like the valuable info you provide in your articles. I will bookmark your weblog and check again here regularly. I’m quite sure I will learn plenty of new stuff right here! Good luck for the next!
You can certainly see your skills in the paintings you write. The world hopes for more passionate writers like you who are not afraid to say how they believe. Always follow your heart. “History is the version of past events that people have decided to agree upon.” by Napoleon.
Thanks for the sensible critique. Me and my neighbor were just preparing to do some research about this. We got a grab a book from our area library but I think I learned more clear from this post. I am very glad to see such wonderful information being shared freely out there.
Hi there, You’ve done an incredible job. I’ll definitely digg it and personally recommend to my friends. I’m sure they will be benefited from this site.
I¡¦ve recently started a site, the information you provide on this web site has helped me greatly. Thanks for all of your time & work.
I¡¦ve been exploring for a little bit for any high-quality articles or weblog posts on this kind of area . Exploring in Yahoo I ultimately stumbled upon this web site. Studying this info So i am happy to show that I have a very just right uncanny feeling I came upon exactly what I needed. I so much indisputably will make sure to do not disregard this website and provides it a glance regularly.
Good web site! I truly love how it is easy on my eyes and the data are well written. I’m wondering how I might be notified when a new post has been made. I’ve subscribed to your feed which must do the trick! Have a great day!
I am continuously invstigating online for posts that can help me. Thank you!
Definitely believe that which you stated. Your favorite justification seemed to be on the net the simplest thing to be aware of. I say to you, I definitely get annoyed while people consider worries that they plainly don’t know about. You managed to hit the nail upon the top and also defined out the whole thing without having side effect , people could take a signal. Will probably be back to get more. Thanks
A lot of thanks for your whole hard work on this web page. My mom takes pleasure in managing internet research and it is easy to see why. Many of us notice all about the compelling medium you present rewarding tricks via your blog and as well as increase participation from some other people about this idea so our own simple princess is actually becoming educated so much. Take pleasure in the remaining portion of the new year. Your carrying out a glorious job.
Bonjour ! Vraiment bien comme site!!!
Pretty nice post. I just stumbled upon your weblog and wanted to say that I have really enjoyed browsing your blog posts. In any case I’ll be subscribing to your rss feed and I hope you write again very soon!
Bonjour ! Il n’y aurai pas des doublons ? Car je viens plusieurs fois les mêmes articles sur votre site !
Thank you for the sensible critique. Me & my neighbor were just preparing to do a little research about this. We got a grab a book from our local library but I think I learned more clear from this post. I’m very glad to see such wonderful information being shared freely out there.
This is very interesting, You are a very skilled blogger. I have joined your rss feed and look forward to seeking more of your wonderful post. Also, I have shared your site in my social networks!
Thank you a bunch for sharing this with all people you actually realize what you are talking about! Bookmarked. Kindly also talk over with my site =). We can have a hyperlink alternate agreement among us!
I am continually searching online for posts that can help me. Thank you!
I was recommended this blog by my cousin. I’m not sure whether this post is written by him as no one else know such detailed about my trouble. You’re incredible! Thanks!
You really make it seem so easy with your presentation but I find this topic to be really something that I think I would never understand. It seems too complicated and very broad for me. I’m looking forward for your next post, I will try to get the hang of it!
Just wanna input that you have a very nice site, I love the layout it actually stands out.
I was very happy to discover this great site. I wanted to thank you for your time for this particularly fantastic read!! I definitely loved every bit of it and i also have you saved as a favorite to see new things in your website.
Hi there, You have done an incredible job. I will certainly digg it and personally recommend to my friends. I am confident they will be benefited from this web site.
You can certainly see your enthusiasm within the work you write. The arena hopes for more passionate writers like you who aren’t afraid to mention how they believe. Always go after your heart.
I carry on listening to the news talk about receiving boundless online grant applications so I have been looking around for the top site to get one. Could you tell me please, where could i get some?
Magnificent beat ! I wish to apprentice whilst you amend your website, how can i subscribe for a weblog site? The account aided me a appropriate deal. I have been tiny bit acquainted of this your broadcast offered vibrant clear concept
Rattling excellent info can be found on website . “I don’t know what will be used in the next world war, but the 4th will be fought with stones.” by Albert Einstein.
I was reading some of your content on this website and I believe this website is really instructive! Keep posting .
Enjoyed looking through this, very good stuff, regards . “We swallow greedily any lie that flatters us, but we sip little by little at a truth we find bitter.” by Denis Diderot.
I’ve been surfing online more than three hours today, yet I never found any interesting article like yours. It is pretty worth enough for me. Personally, if all website owners and bloggers made good content as you did, the web will be much more useful than ever before.
Just wanna remark on few general things, The website design is perfect, the subject matter is really excellent : D.
hi!,I love your writing very much! proportion we keep up a correspondence more about your post on AOL? I require an expert in this area to resolve my problem. May be that is you! Looking forward to see you.
You are my inhalation , I own few web logs and very sporadically run out from to post .I believe this site holds some very superb information for everyone. “I prefer the wicked rather than the foolish. The wicked sometimes rest.” by Alexandre Dumas.
hello there and thank you for your info – I have certainly picked up anything new from right here. I did however expertise a few technical issues using this web site, as I experienced to reload the web site a lot of times previous to I could get it to load properly. I had been wondering if your web hosting is OK? Not that I’m complaining, but sluggish loading instances times will often affect your placement in google and can damage your high quality score if ads and marketing with Adwords. Anyway I’m adding this RSS to my e-mail and could look out for much more of your respective intriguing content. Make sure you update this again soon..
My brother suggested I might like this website. He was totally right. This post truly made my day. You can not imagine just how much time I had spent for this info! Thanks!
A lot of thanks for all your labor on this blog. My mom take interest in getting into research and it’s obvious why. My partner and i hear all concerning the powerful ways you deliver very helpful tips via your web site and as well invigorate participation from other ones on the subject matter plus our favorite girl is in fact studying a whole lot. Take advantage of the remaining portion of the new year. You’re carrying out a remarkable job.
Good web site! I really love how it is simple on my eyes and the data are well written. I’m wondering how I could be notified when a new post has been made. I have subscribed to your RSS which must do the trick! Have a nice day!
This is the right opportunity to have some goals for the possible future. I have read this write-up and if I may just, I desire to suggest to you you very few intriguing recommendation.
I merely want to show you that I am new to blog posting and extremely enjoyed your site. More than likely I am probably to save your blog post . You absolutely have wonderful article content. Value it for expressing with us the best web report
I’m excited to discover this page. I want to to thank you for your time just for this wonderful read!! I definitely enjoyed every little bit of it and i also have you saved to fav to check out new stuff on your web site.
I have not checked in here for a while because I thought it was getting boring, but the last several posts are great quality so I guess I¡¦ll add you back to my daily bloglist. You deserve it my friend 🙂
It’s actually almost unthinkable to come across well-advised individual on this issue, nonetheless you come across as like you realize the things that you’re covering! Thanks A Lot
Remarkably compelling elements that you have said, a big heads up for putting up.
I merely desire to reveal to you that I am new to posting and absolutely adored your webpage. Quite possibly I am probably to save your blog post . You absolutely have extraordinary article materials. Admire it for swapping with us the best domain article
It¡¦s really a nice and helpful piece of information. I am happy that you just shared this helpful information with us. Please keep us informed like this. Thanks for sharing.
My brother recommended I might like this blog. He was entirely right. This post actually made my day. You cann’t imagine simply how much time I had spent for this information! Thanks!
I haven¡¦t checked in here for some time because I thought it was getting boring, but the last few posts are great quality so I guess I¡¦ll add you back to my everyday bloglist. You deserve it my friend 🙂
As I website possessor I believe the content material here is rattling wonderful , appreciate it for your efforts. You should keep it up forever! Best of luck.
I needed to put you one bit of word in order to say thanks a lot once again for all the pleasing secrets you’ve provided here. It was simply wonderfully generous with people like you giving publicly what exactly a lot of people could possibly have made available as an e book to earn some profit for their own end, mostly since you might have tried it if you desired. These creative ideas as well worked as a great way to comprehend other individuals have similar keenness much like my own to figure out great deal more in regard to this problem. I am certain there are many more pleasant times ahead for individuals who start reading your website.
Its like you read my mind! You appear to know so much about this, like you wrote the book in it or something. I think that you can do with some pics to drive the message home a bit, but other than that, this is great blog. A great read. I will definitely be back.
How do i build a blog without using blogger or any of those websites?
Bonjour ! Cool j’ai bien aimé ! Merci pour cette lecture tiptop
Thank you for sharing excellent informations. Your site is very cool. I’m impressed by the details that you¡¦ve on this site. It reveals how nicely you perceive this subject. Bookmarked this web page, will come back for more articles. You, my friend, ROCK! I found simply the information I already searched everywhere and just could not come across. What a perfect web-site.
I’m more than happy to uncover this website. I wanted to thank you for ones time due to this fantastic read!! I definitely savored every part of it and I have you saved to fav to check out new stuff on your site.
I simply wish to reveal to you that I am new to blogging and pretty much enjoyed your webpage. Likely I am most likely to remember your blog post . You seriously have great article material. Get Pleasure From it for sharing with us your website report
It certainly is almost extremely difficult to see well-advised women and men on this matter, still, you come across as like you comprehend exactly what you’re covering! Excellent
Fairly informative highlights that you have said, thanks so much for posting.
I really intend to inform you you that I am new to putting up a blog and clearly enjoyed your webpage. More than likely I am prone to store your blog post . You truly have fabulous article information. Truly Appreciate it for discussing with us your main internet site report
I really want to reveal to you that I am new to writing a blog and completely admired your post. Quite possibly I am going to store your blog post . You definitely have great article material. Get Pleasure From it for swapping with us your current blog webpage
I’m more than happy to uncover this website. I wanted to thank you for ones time just for this wonderful read!! I definitely enjoyed every little bit of it and I have you saved as a favorite to see new information on your website.
Seriously intriguing suggestions that you have stated, many thanks for setting up.
I loved as much as you’ll receive carried out right here. The sketch is tasteful, your authored material stylish. nonetheless, you command get got an impatience over that you wish be delivering the following. unwell unquestionably come more formerly again as exactly the same nearly very often inside case you shield this hike.
I’m really impressed with your writing skills and also with the layout on your weblog. Is this a paid theme or did you customize it yourself? Either way keep up the nice quality writing, it is rare to see a nice blog like this one these days..
Well I definitely liked reading it. This tip offered by you is very helpful for good planning.
I intended to create you this bit of remark so as to say thanks over again considering the incredible information you’ve featured above. It has been simply seriously generous with you in giving extensively all many individuals might have offered for sale as an ebook to end up making some bucks on their own, most notably considering the fact that you might have tried it in the event you decided. Those ideas also served to be a fantastic way to recognize that someone else have the identical dream like my very own to figure out much more with respect to this issue. I know there are lots of more enjoyable sessions in the future for folks who scan through your blog.
I merely want to show you that I am new to blog posting and very much adored your webpage. Likely I am probably to save your blog post . You truly have impressive article blog posts. Be Thankful For it for discussing with us your favorite site write-up
I was extremely pleased to uncover this great site. I wanted to thank you for your time for this particularly fantastic read!! I definitely appreciated every little bit of it and I have you book-marked to look at new stuff in your web site.
Magnificent goods from you, man. I’ve understand your stuff previous to and you are just extremely great. I actually like what you have acquired here, really like what you are saying and the way in which you say it. You make it entertaining and you still take care of to keep it wise. I can not wait to read far more from you. This is actually a great website.
Wow, wonderful weblog structure! How long have you been blogging for? you make running a blog glance easy. The total glance of your web site is excellent, let alone the content material!
Hi my friend! I wish to say that this post is awesome, nice written and come with almost all vital infos. I¡¦d like to see extra posts like this .
Hello, Neat post. There is a problem together with your site in internet explorer, could check this¡K IE still is the market leader and a large component to other people will pass over your excellent writing due to this problem.
There is visibly a bunch to identify about this. I suppose you made some nice points in features also.
Wow, marvelous blog layout! How lengthy have you been blogging for? you make running a blog look easy. The whole look of your site is excellent, as well as the content material!
I loved as much as you’ll receive carried out right here. The sketch is attractive, your authored material stylish. nonetheless, you command get got an nervousness over that you wish be delivering the following. unwell unquestionably come more formerly again as exactly the same nearly very often inside case you shield this hike.
I simply intend to show you that I am new to writing a blog and certainly admired your site. Most likely I am likely to store your blog post . You absolutely have magnificent article content. Be Grateful For it for giving out with us your own internet webpage
I merely desire to reveal to you that I am new to having a blog and clearly liked your article. Most likely I am prone to store your blog post . You simply have outstanding article materials. Truly Appreciate it for sharing with us your current site article
Definitely believe that which you said. Your favorite justification seemed to be on the net the simplest thing to be aware of. I say to you, I certainly get annoyed while people think about worries that they just do not know about. You managed to hit the nail upon the top as well as defined out the whole thing without having side-effects , people can take a signal. Will probably be back to get more. Thanks
Well done! Keep up this quality!
I’m extremely pleased to discover this great site. I wanted to thank you for ones time for this particularly fantastic read!! I definitely liked every bit of it and i also have you book marked to see new stuff in your site.
I¡¦m no longer sure the place you are getting your info, but great topic. I needs to spend a while studying more or understanding more. Thanks for wonderful information I was on the lookout for this information for my mission.
Its like you read my mind! You seem to know a lot about this, like you wrote the book in it or something. I think that you can do with some pics to drive the message home a bit, but instead of that, this is great blog. A fantastic read. I’ll definitely be back.
I like what you guys are up also. Such intelligent work and reporting! Carry on the superb works guys I have incorporated you guys to my blogroll. I think it will improve the value of my web site 🙂
Valuable info. Fortunate me I discovered your web site unintentionally, and I am shocked why this twist of fate did not happened earlier! I bookmarked it.
Thank you for the auspicious writeup. It in fact was a amusement account it. Look advanced to far added agreeable from you! However, how could we communicate?
Thanks for sharing superb informations. Your website is so cool. I’m impressed by the details that you have on this web site. It reveals how nicely you understand this subject. Bookmarked this website page, will come back for extra articles. You, my friend, ROCK! I found just the info I already searched everywhere and just couldn’t come across. What an ideal site.
It is the best time to make some plans for the future and it is time to be happy. I have read this post and if I could I wish to suggest you few interesting things or suggestions. Maybe you can write next articles referring to this article. I wish to read even more things about it!
Thank you for all of your effort on this web site. Betty takes pleasure in going through investigations and it is easy to understand why. We all hear all about the lively manner you provide helpful techniques through the website and therefore invigorate participation from people on the matter so our favorite girl is without a doubt discovering a whole lot. Enjoy the remaining portion of the year. You have been conducting a pretty cool job.
I want to express some thanks to the writer just for rescuing me from this type of difficulty. After checking through the the web and obtaining notions which were not pleasant, I believed my entire life was gone. Existing minus the strategies to the problems you’ve resolved as a result of the article is a crucial case, and the ones which might have in a negative way affected my career if I hadn’t discovered your web site. Your actual expertise and kindness in controlling the whole lot was important. I am not sure what I would have done if I had not encountered such a stuff like this. I’m able to now look ahead to my future. Thank you very much for this specialized and result oriented help. I will not be reluctant to propose the website to anybody who should get care about this subject.
Of course, what a fantastic website and instructive posts, I definitely will bookmark your website.Have an awsome day!
Hi, Neat post. There’s a problem along with your website in internet explorer, could test this… IE nonetheless is the marketplace leader and a big element of folks will pass over your wonderful writing due to this problem.
What i do not realize is in reality how you are not actually much more neatly-liked than you may be right now. You are so intelligent. You realize therefore significantly with regards to this matter, made me for my part believe it from numerous numerous angles. Its like men and women don’t seem to be interested except it¡¦s something to do with Lady gaga! Your personal stuffs excellent. Always deal with it up!
I¡¦ll immediately grasp your rss feed as I can’t in finding your email subscription hyperlink or e-newsletter service. Do you have any? Kindly permit me know so that I may subscribe. Thanks.
I together with my guys were reading the good guidelines found on the website and so quickly I had a horrible feeling I never expressed respect to the web blog owner for them. These ladies were definitely as a consequence joyful to learn them and have now in fact been enjoying these things. Thanks for getting really kind and for picking out varieties of wonderful subjects millions of individuals are really wanting to learn about. Our own honest regret for not saying thanks to sooner.
Some genuinely excellent content on this site, thanks for contribution. “Once, power was considered a masculine attribute. In fact, power has no sex.” by Katharine Graham.
I would like to thank you for the efforts you have put in writing this website. I’m hoping the same high-grade blog post from you in the upcoming also. In fact your creative writing skills has inspired me to get my own blog now. Actually the blogging is spreading its wings fast. Your write up is a great example of it.
It¡¦s actually a nice and helpful piece of info. I¡¦m glad that you shared this useful information with us. Please stay us informed like this. Thanks for sharing.
I carry on listening to the reports lecture about getting free online grant applications so I have been looking around for the finest site to get one. Could you tell me please, where could i get some?
I really like your writing style, excellent info , thanks for posting : D.
Hiya very cool website!! Man .. Beautiful .. Amazing .. I’ll bookmark your blog and take the feeds also¡KI’m glad to find a lot of useful information here in the post, we want develop more strategies on this regard, thanks for sharing. . . . . .
It’s appropriate time to make some plans for the future and it’s time to be happy. I have read this post and if I could I wish to suggest you few interesting things or advice. Perhaps you could write next articles referring to this article. I desire to read even more things about it!
Hi my loved one! I wish to say that this post is awesome, nice written and include almost all vital infos. I would like to look more posts like this .
Somebody essentially lend a hand to make critically articles I might state. This is the first time I frequented your web page and to this point? I surprised with the research you made to create this particular post extraordinary. Magnificent task!
Great beat ! I would like to apprentice while you amend your web site, how can i subscribe for a blog website? The account helped me a acceptable deal. I had been a little bit acquainted of this your broadcast offered bright clear concept
I have fun with, lead to I discovered just what I was taking a look for. You have ended my 4 day long hunt! God Bless you man. Have a great day. Bye
I am continually invstigating online for tips that can assist me. Thx!
Thank you for sharing superb informations. Your web site is so cool. I’m impressed by the details that you have on this web site. It reveals how nicely you understand this subject. Bookmarked this web page, will come back for extra articles. You, my pal, ROCK! I found simply the info I already searched everywhere and just could not come across. What an ideal web-site.
Very efficiently written story. It will be supportive to anybody who employess it, including yours truly :). Keep up the good work – for sure i will check out more posts.
Wow! Thank you! I continually wanted to write on my blog something like that. Can I implement a portion of your post to my website?
Excellent goods from you, man. I have understand your stuff previous to and you are just extremely magnificent. I really like what you’ve acquired here, certainly like what you’re saying and the way in which you say it. You make it entertaining and you still take care of to keep it wise. I can’t wait to read far more from you. This is actually a terrific website.
I like this post, enjoyed this one appreciate it for putting up. “To affect the quality of the day that is the art of life.” by Henry David Thoreau.
You can certainly see your expertise within the paintings you write. The world hopes for more passionate writers like you who aren’t afraid to mention how they believe. All the time follow your heart. “Man is the measure of all things.” by Protagoras.
Normally I don’t read article on blogs, but I wish to say that this write-up very pressured me to check out and do so! Your writing taste has been amazed me. Thank you, quite great post.
Keep functioning ,splendid job!
I’m very happy to read this. This is the kind of manual that needs to be given and not the random misinformation that’s at the other blogs. Appreciate your sharing this greatest doc.
I have learn several just right stuff here. Certainly worth bookmarking for revisiting. I surprise how so much effort you put to make this kind of great informative site.
Excellent blog here! Also your web site loads up very fast! What host are you using? Can I get your affiliate link to your host? I wish my web site loaded up as fast as yours lol
Thank you for all of your effort on this site. Gloria takes pleasure in engaging in investigations and it’s easy to see why. Many of us notice all about the powerful way you render sensible tactics through this web site and in addition foster response from other people about this point so our own daughter is in fact starting to learn a lot of things. Have fun with the remaining portion of the new year. You’re the one performing a stunning job.
I¡¦m no longer positive where you are getting your information, however good topic. I must spend some time studying more or understanding more. Thanks for magnificent information I was on the lookout for this information for my mission.
Wow, marvelous blog layout! How long have you been blogging for? you made blogging look easy. The overall look of your web site is great, as well as the content!
I am not sure where you’re getting your info, but great topic. I needs to spend some time learning much more or understanding more. Thanks for fantastic info I was looking for this info for my mission.
I like what you guys are up also. Such clever work and reporting! Carry on the superb works guys I¡¦ve incorporated you guys to my blogroll. I think it will improve the value of my site 🙂
Thank you for the sensible critique. Me & my neighbor were just preparing to do a little research on this. We got a grab a book from our local library but I think I learned more from this post. I am very glad to see such wonderful information being shared freely out there.
I have been browsing online more than three hours today, yet I never found any interesting article like yours. It is pretty worth enough for me. In my view, if all website owners and bloggers made good content as you did, the net will be a lot more useful than ever before.
You actually make it seem really easy with your presentation however I find this matter to be really something that I think I’d never understand. It seems too complex and extremely large for me. I’m taking a look forward for your subsequent post, I will try to get the dangle of it!
Wow! Thank you! I continuously needed to write on my website something like that. Can I implement a portion of your post to my site?
You really make it seem so easy with your presentation but I find this topic to be actually something which I think I would never understand. It seems too complex and extremely broad for me. I’m looking forward for your next post, I’ll try to get the hang of it!
I have been absent for some time, but now I remember why I used to love this website. Thanks , I will try and check back more frequently. How frequently you update your website?
What i do not understood is if truth be told how you are no longer actually much more smartly-preferred than you may be right now. You’re so intelligent. You already know thus considerably with regards to this matter, produced me in my view consider it from numerous various angles. Its like women and men are not interested unless it¡¦s one thing to accomplish with Girl gaga! Your own stuffs great. Always deal with it up!
I simply could not go away your website prior to suggesting that I extremely enjoyed the usual info an individual provide to your guests? Is gonna be back incessantly to check up on new posts
I was studying some of your blog posts on this website and I think this website is real informative ! Keep on posting .
I like what you guys are up also. Such clever work and reporting! Keep up the excellent works guys I’ve incorporated you guys to my blogroll. I think it’ll improve the value of my web site :).
You are my breathing in, I own few blogs and rarely run out from to post .I believe this web site has got some very great info for everyone. “As we grow oldthe beauty steals inward.” by Ralph Waldo Emerson.
Perfectly composed subject material , thankyou for selective information .
You have brought up a very superb details , appreciate it for the post.
I’m extremely impressed with your writing skills as well as with the layout on your blog. Is this a paid theme or did you modify it yourself? Either way keep up the nice quality writing, it is rare to see a nice blog like this one these days..
Excellent read, I just passed this onto a friend who was doing a little research on that. And he just bought me lunch because I found it for him smile Therefore let me rephrase that: Thanks for lunch!
What i don’t understood is if truth be told how you are not really much more well-preferred than you may be right now. You are very intelligent. You understand therefore considerably when it comes to this matter, produced me in my opinion imagine it from numerous various angles. Its like women and men are not interested unless it’s something to accomplish with Woman gaga! Your personal stuffs great. At all times take care of it up!
I have been examinating out a few of your articles and i can claim pretty nice stuff. I will definitely bookmark your site.
I think this is among the most vital information for me. And i am glad reading your article. But should remark on some general things, The web site style is great, the articles is really excellent : D. Good job, cheers
Very good written post. It will be helpful to everyone who utilizes it, including me. Keep up the good work – i will definitely read more posts.
I enjoy, lead to I discovered just what I was looking for. You have ended my 4 day long hunt! God Bless you man. Have a great day. Bye
Thank you for every other informative web site. The place else could I get that type of information written in such a perfect manner? I’ve a venture that I am simply now running on, and I have been at the glance out for such information.
Excellent read, I just passed this onto a friend who was doing a little research on that. And he actually bought me lunch because I found it for him smile Thus let me rephrase that: Thanks for lunch!
As soon as I noticed this site I went on reddit to share some of the love with them.
Thanks for your whole efforts on this website. My mother really loves engaging in investigations and it’s really obvious why. My spouse and i notice all about the dynamic medium you render good guidance by means of your web site and therefore invigorate participation from other ones on that point so my simple princess is without a doubt studying a whole lot. Enjoy the rest of the new year. You’re conducting a fantastic job.
Just wanna tell that this is very useful , Thanks for taking your time to write this.
obviously like your web site but you have to test the spelling on several of your posts. A number of them are rife with spelling issues and I to find it very troublesome to inform the reality nevertheless I will definitely come back again.
Merely a smiling visitant here to share the love (:, btw outstanding pattern .
Some really nice and utilitarian information on this web site, too I believe the style has got excellent features.
Good – I should definitely pronounce, impressed with your website. I had no trouble navigating through all tabs and related information ended up being truly simple to do to access. I recently found what I hoped for before you know it at all. Reasonably unusual. Is likely to appreciate it for those who add forums or something, site theme . a tones way for your customer to communicate. Nice task.
Just wish to say your article is as astonishing. The clearness in your post is simply spectacular and i can assume you’re an expert on this subject. Well with your permission let me to grab your RSS feed to keep up to date with forthcoming post. Thanks a million and please carry on the gratifying work.
Thanks, I have just been searching for information approximately this subject for a long time and yours is the greatest I have came upon till now. However, what in regards to the conclusion? Are you certain in regards to the source?
Wow! Thank you! I permanently wanted to write on my blog something like that. Can I include a fragment of your post to my blog?
Great goods from you, man. I have understand your stuff previous to and you are just extremely great. I really like what you’ve acquired here, really like what you’re stating and the way in which you say it. You make it enjoyable and you still take care of to keep it sensible. I can’t wait to read far more from you. This is really a great web site.
hello!,I really like your writing so a lot! percentage we be in contact more about your post on AOL? I need a specialist on this area to resolve my problem. May be that’s you! Taking a look forward to peer you.
Wow! This can be one particular of the most helpful blogs We’ve ever arrive across on this subject. Basically Magnificent. I am also a specialist in this topic therefore I can understand your hard work.
There is noticeably a bunch to realize about this. I believe you made various good points in features also.
I think other website proprietors should take this website as an model, very clean and magnificent user friendly style and design, let alone the content. You are an expert in this topic!
I enjoy you because of all your effort on this web page. Kate really loves doing internet research and it’s simple to grasp why. I notice all of the powerful manner you convey advantageous techniques through the blog and as well as foster response from people on that area of interest plus our own daughter is always starting to learn a great deal. Take pleasure in the rest of the new year. You are doing a powerful job.
Thanks for any other informative web site. The place else could I am getting that type of information written in such a perfect means? I’ve a challenge that I am simply now working on, and I’ve been at the look out for such info.
Thanks for every other informative website. Where else may just I am getting that type of information written in such a perfect method? I’ve a undertaking that I am just now running on, and I have been on the look out for such information.
I enjoy you because of all of your effort on this web site. Kim take interest in engaging in investigations and it’s really easy to understand why. All of us learn all about the powerful form you provide efficient tips and tricks via the web blog and therefore strongly encourage participation from some others about this content while our favorite princess is now starting to learn a lot of things. Have fun with the rest of the year. You are always doing a dazzling job.
excellent points altogether, you simply won a logo new reader. What would you recommend in regards to your publish that you simply made some days ago? Any positive?
Awsome article and straight to the point. I don’t know if this is actually the best place to ask but do you folks have any thoughts on where to get some professional writers? Thx 🙂
Well I really liked reading it. This subject procured by you is very effective for correct planning.
Wow! This can be one particular of the most helpful blogs We’ve ever arrive across on this subject. Basically Excellent. I am also a specialist in this topic therefore I can understand your hard work.
Thanks a lot for sharing this with all people you actually know what you’re speaking approximately! Bookmarked. Kindly additionally seek advice from my site =). We could have a hyperlink trade agreement between us!
Thank you for the sensible critique. Me & my neighbor were just preparing to do a little research on this. We got a grab a book from our area library but I think I learned more from this post. I am very glad to see such magnificent info being shared freely out there.
Wow! This can be one particular of the most helpful blogs We have ever arrive across on this subject. Actually Great. I am also a specialist in this topic therefore I can understand your hard work.
I loved as much as you’ll receive carried out right here. The sketch is tasteful, your authored subject matter stylish. nonetheless, you command get bought an impatience over that you wish be delivering the following. unwell unquestionably come further formerly again since exactly the same nearly a lot often inside case you shield this hike.
Generally I don’t read post on blogs, however I would like to say that this write-up very forced me to take a look at and do so! Your writing taste has been amazed me. Thanks, very great post.
Wonderful website. Lots of useful info here. I¡¦m sending it to a few pals ans additionally sharing in delicious. And of course, thank you in your sweat!
I wanted to put you the tiny word to be able to say thanks a lot once again for your great tactics you have featured here. This has been really tremendously open-handed with people like you to make extensively precisely what most of us could have advertised as an ebook to help with making some cash for their own end, specifically considering that you might well have done it if you considered necessary. These suggestions as well served like a fantastic way to be aware that other people online have a similar fervor just as my personal own to figure out way more with respect to this condition. I know there are numerous more pleasant moments ahead for individuals that look over your website.
Hi my family member! I wish to say that this post is awesome, nice written and include approximately all significant infos. I would like to see more posts like this.
As soon as I noticed this website I went on reddit to share some of the love with them.
Great write-up, I¡¦m regular visitor of one¡¦s web site, maintain up the excellent operate, and It’s going to be a regular visitor for a long time.
Thanks for sharing excellent informations. Your website is very cool. I am impressed by the details that you¡¦ve on this web site. It reveals how nicely you perceive this subject. Bookmarked this web page, will come back for extra articles. You, my friend, ROCK! I found simply the information I already searched everywhere and simply could not come across. What an ideal website.
I would like to convey my love for your kindness in support of individuals that have the need for help on in this matter. Your very own commitment to passing the solution up and down has been pretty valuable and has constantly encouraged some individuals like me to reach their aims. Your entire important publication denotes a great deal to me and a whole lot more to my colleagues. Thanks a ton; from everyone of us.
I would like to thnkx for the efforts you have put in writing this blog. I am hoping the same high-grade site post from you in the upcoming also. Actually your creative writing abilities has inspired me to get my own blog now. Actually the blogging is spreading its wings rapidly. Your write up is a great example of it.
This is really interesting, You are a very skilled blogger. I have joined your rss feed and look forward to seeking more of your great post. Also, I’ve shared your web site in my social networks!
Thank you a lot for giving everyone an extraordinarily remarkable chance to check tips from this website. It is usually so sweet and also jam-packed with a great time for me and my office mates to search the blog not less than thrice in a week to find out the fresh guidance you have. And indeed, I am usually contented for the amazing creative ideas served by you. Selected 1 facts in this article are really the most beneficial we have all ever had.
Very nice post. I just stumbled upon your blog and wanted to say that I have really enjoyed browsing your blog posts. In any case I will be subscribing to your feed and I hope you write again soon!
whoah this weblog is wonderful i love reading your posts. Stay up the good work! You know, a lot of individuals are looking around for this information, you can aid them greatly.
Thanks a bunch for sharing this with all of us you actually recognise what you are speaking about! Bookmarked. Kindly additionally discuss with my site =). We can have a link trade agreement among us!
I think you have observed some very interesting points , regards for the post.
I’ve been surfing online more than 3 hours today, yet I never found any interesting article like yours. It’s pretty worth enough for me. Personally, if all web owners and bloggers made good content as you did, the internet will be much more useful than ever before.
I like this post, enjoyed this one thanks for posting. “We seldom attribute common sense except to those who agree with us.” by La Rochefoucauld.
Great remarkable things here. I am very glad to look your post. Thanks a lot and i’m looking forward to contact you. Will you please drop me a mail?
I don’t even know how I ended up here, but I thought this post was good. I don’t know who you are but definitely you’re going to a famous blogger if you are not already 😉 Cheers!
Thanks for sharing excellent informations. Your web-site is very cool. I am impressed by the details that you have on this blog. It reveals how nicely you perceive this subject. Bookmarked this website page, will come back for more articles. You, my friend, ROCK! I found just the info I already searched everywhere and simply couldn’t come across. What a perfect web site.
I simply wished to thank you very much yet again. I am not sure the things that I would have made to happen in the absence of those concepts discussed by you over such subject. It had been the fearsome problem in my view, nevertheless finding out a new expert fashion you treated that took me to leap over gladness. I’m just thankful for the help and even have high hopes you realize what a powerful job that you’re undertaking training people thru your blog post. Probably you have never come across all of us.
Helpful info. Lucky me I discovered your site by accident, and I am shocked why this coincidence did not took place in advance! I bookmarked it.
naturally like your web site however you need to test the spelling on several of your posts. Many of them are rife with spelling issues and I in finding it very bothersome to tell the truth however I’ll certainly come again again.
Keep working ,terrific job!
Some genuinely prime content on this website , saved to favorites .
I don’t even know how I ended up here, but I thought this post was great. I do not know who you are but definitely you are going to a famous blogger if you aren’t already 😉 Cheers!
I think other web site proprietors should take this site as an model, very clean and great user genial style and design, as well as the content. You’re an expert in this topic!
I think this is one of the most vital info for me. And i am glad reading your article. But want to remark on some general things, The web site style is perfect, the articles is really excellent : D. Good job, cheers
Hello.This article was extremely motivating, especially since I was browsing for thoughts on this issue last couple of days.
You are a very intelligent individual!
Just wish to say your article is as astonishing. The clearness in your post is just nice and i could assume you’re an expert on this subject. Well with your permission let me to grab your RSS feed to keep up to date with forthcoming post. Thanks a million and please continue the rewarding work.
naturally like your web-site however you have to take a look at the spelling on several of your posts. Several of them are rife with spelling issues and I find it very troublesome to tell the truth nevertheless I will certainly come again again.
Hello, i think that i saw you visited my website so i came to “return the favor”.I’m attempting to find things to enhance my website!I suppose its ok to use a few of your ideas!!
Simply wanna remark on few general things, The website layout is perfect, the written content is rattling excellent. “Some for renown, on scraps of learning dote, And think they grow immortal as they quote.” by Edward Young.
I as well as my pals came digesting the best techniques located on the website while then I had a terrible feeling I had not expressed respect to the site owner for those strategies. The guys were absolutely thrilled to study them and have definitely been taking pleasure in them. We appreciate you actually being quite kind and for having this kind of impressive topics most people are really desperate to understand about. My very own sincere apologies for not expressing appreciation to earlier.
I¡¦ll immediately grasp your rss as I can not find your email subscription link or newsletter service. Do you’ve any? Kindly let me recognise so that I could subscribe. Thanks.
I want to express some appreciation to you just for rescuing me from this setting. Right after exploring through the world-wide-web and seeing tips that were not pleasant, I assumed my entire life was over. Existing without the presence of answers to the issues you have resolved all through your entire article content is a critical case, and those which could have badly damaged my career if I hadn’t come across your web page. Your good know-how and kindness in taking care of the whole thing was priceless. I’m not sure what I would’ve done if I hadn’t come upon such a step like this. I am able to at this time look forward to my future. Thanks very much for the impressive and results-oriented guide. I won’t think twice to recommend your web page to anyone who requires care about this subject matter.
I’ve been browsing online more than three hours today, yet I never found any interesting article like yours. It’s pretty worth enough for me. In my opinion, if all website owners and bloggers made good content as you did, the internet will be a lot more useful than ever before.
Fantastic beat ! I would like to apprentice while you amend your website, how could i subscribe for a blog site? The account aided me a acceptable deal. I had been a little bit acquainted of this your broadcast offered bright clear concept
I genuinely enjoy looking at on this internet site , it holds wonderful blog posts. “Something unpredictable but in the end it’s right, I hope you have the time of your life.” by Greenday.
One thing I want to say is that often before purchasing more personal computer memory, look into the machine in to which it will be installed. If your machine can be running Windows XP, for instance, the memory limit is 3.25GB. Applying in excess of this would simply constitute a waste. Be sure that one’s mother board can handle an upgrade quantity, as well. Good blog post.
I’ll right away seize your rss as I can not in finding your email subscription hyperlink or e-newsletter service. Do you’ve any? Kindly let me realize in order that I could subscribe. Thanks.
Wonderful work! That is the type of info that are supposed to be shared around the internet. Disgrace on the seek engines for no longer positioning this put up higher! Come on over and discuss with my web site . Thanks =)
I am not sure where you’re getting your info, but great topic. I needs to spend some time learning much more or understanding more. Thanks for fantastic information I was looking for this info for my mission.
Very nice post. I just stumbled upon your blog and wanted to say that I have truly enjoyed browsing your blog posts. In any case I will be subscribing to your rss feed and I hope you write again soon!
I think other website proprietors should take this website as an model, very clean and great user friendly style and design, let alone the content. You’re an expert in this topic!
fantastic post, very informative. I wonder why the opposite experts of this sector do not understand this. You should proceed your writing. I am sure, you’ve a huge readers’ base already!
I think other web-site proprietors should take this website as an model, very clean and great user friendly style and design, as well as the content. You’re an expert in this topic!
I needed to compose you that very small word in order to give thanks once again considering the superb tips you’ve shown above. It is wonderfully generous of you to allow extensively what exactly a number of us might have supplied for an e-book to help make some money for their own end, particularly given that you could possibly have tried it if you desired. The thoughts likewise worked as the fantastic way to be sure that other people online have similar dream just like my personal own to grasp significantly more on the topic of this problem. I think there are thousands of more enjoyable situations in the future for many who see your website.
It is really a nice and useful piece of info. I’m satisfied that you just shared this useful information with us. Please stay us informed like this. Thank you for sharing.
I actually wanted to write a message to be able to thank you for all the precious advice you are posting here. My incredibly long internet research has at the end been rewarded with really good insight to exchange with my great friends. I ‘d express that we visitors actually are very much endowed to dwell in a remarkable community with many wonderful individuals with great hints. I feel very grateful to have used the web pages and look forward to so many more fabulous minutes reading here. Thank you again for a lot of things.
Enjoyed looking at this, very good stuff, thankyou . “Whenever you want to marry someone, go have lunch with his ex-wife.” by Francis William Bourdillon.
Some really prize posts on this web site , saved to fav.
I have learn several good stuff here. Certainly worth bookmarking for revisiting. I wonder how a lot attempt you put to make such a excellent informative web site.
I’m really impressed with your writing skills as well as with the layout on your blog. Is this a paid theme or did you customize it yourself? Anyway keep up the nice quality writing, it is rare to see a great blog like this one these days..
Thanks for sharing superb informations. Your web site is very cool. I am impressed by the details that you have on this site. It reveals how nicely you perceive this subject. Bookmarked this website page, will come back for extra articles. You, my pal, ROCK! I found just the info I already searched everywhere and simply couldn’t come across. What an ideal site.
I have read several good stuff here. Certainly price bookmarking for revisiting. I wonder how so much effort you set to make any such excellent informative site.
Very good written article. It will be useful to anyone who usess it, as well as yours truly :). Keep doing what you are doing – for sure i will check out more posts.
Usually I don’t learn post on blogs, however I would like to say that this write-up very compelled me to try and do so! Your writing style has been surprised me. Thank you, quite great post.
I’m not sure where you’re getting your info, but good topic. I needs to spend some time learning much more or understanding more. Thanks for wonderful information I was looking for this information for my mission.
Great paintings! That is the type of info that are meant to be shared around the internet. Shame on Google for now not positioning this post higher! Come on over and seek advice from my website . Thank you =)
Great post. I was checking constantly this blog and I am impressed! Very useful information specially the last part 🙂 I care for such info a lot. I was seeking this certain info for a very long time. Thank you and best of luck.
Its like you read my mind! You seem to know a lot about this, like you wrote the book in it or something. I think that you could do with a few pics to drive the message home a bit, but other than that, this is great blog. A great read. I will definitely be back.
I haven¡¦t checked in here for a while because I thought it was getting boring, but the last few posts are great quality so I guess I will add you back to my daily bloglist. You deserve it my friend 🙂
Thanks for another magnificent post. The place else may just anybody get that type of info in such an ideal manner of writing? I have a presentation next week, and I’m on the look for such information.
Pretty section of content. I just stumbled upon your weblog and in accession capital to assert that I acquire in fact enjoyed account your blog posts. Any way I will be subscribing to your augment and even I achievement you access consistently rapidly.
I’m not sure where you are getting your info, but good topic. I needs to spend some time learning much more or understanding more. Thanks for magnificent information I was looking for this information for my mission.
I¡¦m not sure the place you are getting your info, however good topic. I needs to spend a while learning much more or understanding more. Thank you for fantastic info I used to be looking for this info for my mission.
Helpful information. Fortunate me I discovered your website accidentally, and I am shocked why this coincidence did not came about in advance! I bookmarked it.
Very good written post. It will be valuable to anyone who employess it, as well as me. Keep up the good work – i will definitely read more posts.
Thank you for some other magnificent post. Where else could anyone get that kind of information in such a perfect way of writing? I’ve a presentation next week, and I am on the search for such information.
Very nice info and right to the point. I am not sure if this is really the best place to ask but do you folks have any thoughts on where to employ some professional writers? Thx 🙂
You are a very bright individual!
Its like you read my mind! You appear to know a lot about this, like you wrote the book in it or something. I think that you could do with some pics to drive the message home a little bit, but other than that, this is great blog. An excellent read. I will definitely be back.
Simply wanna remark on few general things, The website design and style is perfect, the content material is really superb. “The stars are constantly shining, but often we do not see them until the dark hours.” by Earl Riney.
Thank you a lot for providing individuals with such a pleasant opportunity to check tips from this website. It’s usually so fantastic and also packed with a good time for me and my office friends to search your site on the least thrice weekly to read through the new tips you have. And indeed, I’m just certainly fascinated concerning the remarkable creative ideas served by you. Certain 1 points in this posting are essentially the most impressive we have all ever had.
Heya i’m for the first time here. I found this board and I find It truly useful & it helped me out much. I hope to give something back and help others like you helped me.
hi, outstanding blog on unctuous loss. suchlike helped.
Hello There. I found your blog using msn. This is a really well written article. I will make sure to bookmark it and return to read more of your useful info. Thanks for the post. I will certainly return.
I have been absent for a while, but now I remember why I used to love this website. Thanks, I’ll try and check back more frequently. How frequently you update your site?
Bonjour ! ca fait pas narcissique comme site quand même ?
I really appreciate this post. I have been looking all over for this! Thank goodness I found it on Bing. You have made my day! Thanks again
I am constantly invstigating online for posts that can facilitate me. Thanks!
I cling on to listening to the news bulletin lecture about receiving boundless online grant applications so I have been looking around for the most excellent site to get one. Could you tell me please, where could i find some?
Heya i’m for the first time here. I found this board and I find It truly useful & it helped me out a lot. I hope to give something back and aid others like you helped me.
Thank you, I have just been looking for information approximately this subject for a long time and yours is the best I’ve found out so far. However, what in regards to the conclusion? Are you positive in regards to the source?
Its like you read my mind! You seem to know so much about this, like you wrote the book in it or something. I think that you can do with some pics to drive the message home a bit, but other than that, this is magnificent blog. A fantastic read. I will certainly be back.
I was just seeking this info for some time. After six hours of continuous Googleing, at last I got it in your website. I wonder what’s the lack of Google strategy that don’t rank this type of informative sites in top of the list. Generally the top web sites are full of garbage.
I would like to thank you for the efforts you have put in writing this website. I’m hoping the same high-grade site post from you in the upcoming also. Actually your creative writing abilities has encouraged me to get my own website now. Really the blogging is spreading its wings quickly. Your write up is a great example of it.
You really make it seem so easy with your presentation however I in finding this matter to be actually something that I believe I would never understand. It kind of feels too complicated and very huge for me. I’m having a look ahead for your subsequent put up, I will attempt to get the grasp of it!
Great tremendous issues here. I am very satisfied to see your post. Thanks a lot and i am having a look ahead to contact you. Will you kindly drop me a mail?
naturally like your web site however you have to take a look at the spelling on several of your posts. A number of them are rife with spelling problems and I to find it very troublesome to inform the truth nevertheless I¡¦ll definitely come back again.
Its like you read my mind! You appear to know a lot about this, like you wrote the book in it or something. I think that you could do with some pics to drive the message home a little bit, but instead of that, this is excellent blog. A fantastic read. I will definitely be back.
I really appreciate this post. I have been looking everywhere for this! Thank goodness I found it on Bing. You have made my day! Thx again
I do believe all of the concepts you have presented in your post. They are very convincing and will definitely work. Still, the posts are too brief for newbies. May just you please extend them a little from subsequent time? Thanks for the post.
Hi, Neat post. There’s an issue together with your web site in web explorer, would test this… IE nonetheless is the marketplace leader and a good component to folks will pass over your excellent writing because of this problem.
Enjoyed looking through this, very good stuff, thankyou . “Talk sense to a fool and he calls you foolish.” by Euripides.
Somebody essentially lend a hand to make seriously posts I might state. That is the first time I frequented your web page and up to now? I surprised with the analysis you made to make this particular publish extraordinary. Excellent process!
Great site. Plenty of helpful info here. I’m sending it to a few buddies ans additionally sharing in delicious. And obviously, thanks to your sweat!
Thank you for the sensible critique. Me & my neighbor were just preparing to do a little research about this. We got a grab a book from our area library but I think I learned more from this post. I’m very glad to see such wonderful information being shared freely out there.
Bonjour ! Il n’y aurai pas des doublons ? Car je viens plusieurs fois les mêmes articles sur votre site !
I appreciate, lead to I found just what I was taking a look for. You’ve ended my four day lengthy hunt! God Bless you man. Have a nice day. Bye
You can definitely see your enthusiasm within the paintings you write. The sector hopes for more passionate writers such as you who are not afraid to say how they believe. At all times go after your heart. “We may pass violets looking for roses. We may pass contentment looking for victory.” by Bern Williams.
Thanks for some other great article. The place else could anyone get that type of info in such a perfect means of writing? I’ve a presentation next week, and I am at the look for such information.
Keep functioning ,splendid job!
I like the valuable info you provide in your articles. I’ll bookmark your blog and check again here regularly. I’m quite sure I will learn a lot of new stuff right here! Best of luck for the next!
Thanks for some other magnificent article. The place else may just anyone get that kind of info in such an ideal approach of writing? I’ve a presentation subsequent week, and I’m on the look for such info.
I have been browsing on-line more than three hours these days, but I by no means found any attention-grabbing article like yours. It is pretty worth enough for me. Personally, if all website owners and bloggers made just right content material as you probably did, the internet will be a lot more helpful than ever before.
I truly appreciate this post. I have been looking everywhere for this! Thank goodness I found it on Bing. You have made my day! Thanks again
I must express my appreciation to this writer just for bailing me out of this particular instance. After researching throughout the world-wide-web and coming across principles that were not productive, I assumed my life was gone. Living minus the strategies to the difficulties you have fixed as a result of your main short article is a critical case, as well as ones which may have adversely damaged my career if I hadn’t come across your blog. Your main capability and kindness in playing with every part was valuable. I am not sure what I would’ve done if I had not encountered such a thing like this. I can at this time relish my future. Thanks a lot so much for this skilled and sensible help. I won’t think twice to suggest your blog post to anyone who ought to have support about this situation.
I just wanted to jot down a quick word to be able to appreciate you for all the splendid advice you are writing at this site. My time-consuming internet search has finally been paid with good knowledge to exchange with my co-workers. I ‘d express that many of us site visitors are really endowed to dwell in a decent site with so many outstanding individuals with valuable guidelines. I feel really privileged to have seen your weblog and look forward to some more exciting times reading here. Thank you once more for everything.
I simply couldn’t leave your web site before suggesting that I extremely enjoyed the usual info a person provide in your guests? Is going to be again frequently to check up on new posts
Simply a smiling visitant here to share the love (:, btw great style .
I want to show some thanks to you for bailing me out of this particular problem. Right after browsing through the world wide web and finding proposals that were not powerful, I was thinking my life was gone. Living without the answers to the problems you’ve sorted out by way of your post is a serious case, as well as the kind which might have adversely affected my career if I hadn’t come across your web page. Your main understanding and kindness in playing with all areas was crucial. I don’t know what I would have done if I had not come across such a thing like this. I can also at this point relish my future. Thanks a lot very much for your professional and sensible help. I will not think twice to propose your web site to anyone who needs recommendations on this situation.
Attractive section of content. I just stumbled upon your website and in accession capital to assert that I acquire in fact enjoyed account your blog posts. Any way I’ll be subscribing to your augment and even I achievement you access consistently rapidly.
I’m still learning from you, as I’m making my way to the top as well. I definitely liked reading all that is written on your site.Keep the aarticles coming. I liked it!
Simply wanna comment that you have a very decent internet site , I the design it actually stands out.
I happen to be writing to let you know of the remarkable encounter my child undergone going through your web page. She realized plenty of details, most notably how it is like to have a marvelous teaching mindset to get others just learn a number of very confusing subject areas. You actually did more than our own desires. Many thanks for imparting the warm and friendly, dependable, revealing and in addition unique tips on your topic to Lizeth.
It can be near impossible to find well-informed men and women on this content, unfortunately you look like you comprehend exactly what you’re covering! Regards
I keep listening to the reports lecture about getting free online grant applications so I have been looking around for the top site to get one. Could you tell me please, where could i get some?
Surprisingly motivating resources you’ll have said, thank you so much for posting.
Keep working ,great job!
Heya i am for the first time here. I found this board and I find It truly useful & it helped me out much. I hope to give something back and help others like you aided me.
I have learn a few just right stuff here. Definitely value bookmarking for revisiting. I surprise how a lot attempt you put to make such a magnificent informative site.
I am writing to let you be aware of of the exceptional encounter our princess developed reading your web site. She came to understand a wide variety of pieces, with the inclusion of how it is like to have a very effective coaching mindset to get other individuals really easily comprehend specific tortuous matters. You really did more than visitors’ expected results. Many thanks for delivering these warm and friendly, trustworthy, informative and as well as cool tips about that topic to Lizeth.
Quite informative knowledge that you have stated, thank you so much for writing.
It is actually mostly extremely difficult to come across well-educated americans on this issue, yet somehow you look like you fully grasp what you’re writing on! Bless You
It can be mostly unthinkable to see well-educated individuals on this content, in addition you seem like you know what you’re preaching about! Thanks A Lot
I merely desire to share it with you that I am new to wordpress blogging and totally valued your review. Most likely I am most likely to save your blog post . You literally have excellent article blog posts. Delight In it for share-out with us your current domain write-up
you’re in point of fact a good webmaster. The web site loading pace is incredible. It kind of feels that you are doing any distinctive trick. Moreover, The contents are masterwork. you’ve performed a magnificent job in this subject!
It’s near unthinkable to come across well-qualified parties on this area, in addition you come across as like you fully understand the things that you’re indicating! Cheers
My spouse and i were fortunate Emmanuel managed to carry out his research because of the precious recommendations he had from your own web page. It is now and again perplexing just to be giving freely secrets and techniques that people today have been selling. And now we understand we have got the writer to thank for this. The most important illustrations you have made, the simple blog menu, the relationships your site aid to create – it is most great, and it’s making our son and the family feel that that article is thrilling, which is certainly seriously fundamental. Thank you for all the pieces!
Hello there, You’ve done an excellent job. I will certainly digg it and personally suggest to my friends. I am confident they will be benefited from this web site.
Somebody necessarily help to make severely posts I’d state. That is the first time I frequented your website page and thus far? I amazed with the analysis you made to create this actual submit incredible. Fantastic process!
you’re in reality a excellent webmaster. The web site loading velocity is amazing. It sort of feels that you’re doing any distinctive trick. In addition, The contents are masterpiece. you’ve done a excellent process in this subject!
Someone essentially assist to make severely articles I’d state. This is the very first time I frequented your web page and so far? I amazed with the analysis you made to make this actual submit incredible. Excellent task!
It’s nearly unattainable to find well-aware viewers on this subject, then again you look like you be aware of exactly what you’re talking about! Gratitude
Tremendously alluring data that you have said, thank you for putting up.
It’s mostly unattainable to see well-qualified parties on this content, still, you look like you know exactly what you’re posting on! Cheers
Surprisingly engaging elements that you have remarked, thanks so much for adding.
I really like your writing style, fantastic information, thankyou for posting : D.
I simply need to tell you that I am new to putting up a blog and thoroughly liked your site. Very possible I am likely to remember your blog post . You definitely have magnificent article material. Appreciate it for telling with us the best domain report
It really is mostly impossible to see well-educated readers on this content, however, you look like you realize the things that you’re preaching about! Gratitude
I have not checked in here for a while as I thought it was getting boring, but the last several posts are good quality so I guess I will add you back to my everyday bloglist. You deserve it my friend 🙂
Genuinely useful elements you have mentioned, say thanks a lot for writing.
What i don’t realize is in truth how you are no longer actually a lot more well-favored than you may be now. You are very intelligent. You recognize therefore significantly in terms of this subject, made me for my part consider it from a lot of numerous angles. Its like men and women aren’t involved except it is something to do with Woman gaga! Your individual stuffs outstanding. Always take care of it up!
I simply wish to show you that I am new to posting and totally adored your information. Very possible I am prone to save your blog post . You truly have lovely article information. Like it for share-out with us your web page
There is clearly a lot to know about this. I suppose you made various nice points in features also.
It’s almost extremely difficult to see well-qualified users on this content, even though you appear like you fully grasp exactly what you’re writing about! Bless You
I happen to be writing to let you understand of the fine encounter our child developed using your webblog. She came to find a wide variety of details, which include what it is like to possess a great coaching heart to get the mediocre ones without problems understand a variety of problematic topics. You undoubtedly exceeded people’s expectations. Many thanks for rendering such warm and helpful, healthy, educational as well as easy thoughts on the topic to Sandra.
It can be near impossible to encounter well-informed parties on this content, but you seem like you fully grasp what you’re raving about! Regards
Thank you for the auspicious writeup. It in fact was a amusement account it. Look advanced to far added agreeable from you! By the way, how can we communicate?
Seriously insightful specifics that you have stated, say thanks a lot for submitting.
I do trust all of the concepts you’ve introduced to your post. They’re really convincing and will certainly work. Still, the posts are too brief for newbies. May just you please extend them a bit from subsequent time? Thanks for the post.
I just desire to inform you that I am new to writing a blog and really cherished your review. Likely I am going to remember your blog post . You really have wonderful article blog posts. Delight In it for telling with us the best url webpage
Whats Going down i am new to this, I stumbled upon this I’ve found It absolutely helpful and it has helped me out loads. I hope to contribute & help different users like its aided me. Good job.
I precisely wished to thank you very much all over again. I do not know what I would’ve carried out in the absence of the ideas discussed by you relating to my concern. Certainly was a distressing condition in my position, however , considering the very skilled strategy you dealt with that made me to cry for happiness. I am just happy for your support and then hope that you know what an amazing job you were doing educating many others through your web blog. I know that you haven’t met all of us.
It¡¦s really a cool and useful piece of information. I¡¦m happy that you shared this helpful information with us. Please keep us up to date like this. Thank you for sharing.
I enjoy, cause I found exactly what I used to be having a look for. You have ended my 4 day long hunt! God Bless you man. Have a great day. Bye
I truly appreciate this post. I’ve been looking everywhere for this! Thank goodness I found it on Bing. You’ve made my day! Thx again!
What i don’t understood is actually how you’re now not actually a lot more well-appreciated than you may be right now. You’re so intelligent. You realize thus significantly in terms of this topic, produced me in my view consider it from numerous numerous angles. Its like women and men don’t seem to be fascinated except it is one thing to do with Woman gaga! Your individual stuffs outstanding. At all times take care of it up!
It¡¦s actually a great and useful piece of information. I¡¦m glad that you just shared this helpful info with us. Please stay us informed like this. Thanks for sharing.
Usually I don’t read post on blogs, however I wish to say that this write-up very forced me to take a look at and do so! Your writing style has been amazed me. Thanks, quite nice post.
You could certainly see your skills in the work you write. The world hopes for even more passionate writers like you who aren’t afraid to mention how they believe. Always follow your heart.
I¡¦ve read some just right stuff here. Certainly value bookmarking for revisiting. I wonder how so much effort you set to make this type of fantastic informative website.
Very interesting topic, thank you for posting.
Hi there very cool web site!! Guy .. Beautiful .. Amazing .. I’ll bookmark your blog and take the feeds also¡KI am happy to search out numerous useful information here in the put up, we’d like develop more techniques in this regard, thanks for sharing. . . . . .
Wonderful website. A lot of useful info here. I’m sending it to a few friends ans also sharing in delicious. And naturally, thank you on your effort!
fantastic issues altogether, you simply gained a new reader. What might you suggest about your publish that you simply made some days ago? Any certain?
You are my inspiration , I have few web logs and very sporadically run out from to post .I believe this site holds some very excellent information for everyone. “The expert at anything was once a beginner.” by Hayes.
I like this post, enjoyed this one appreciate it for putting up. “The reward for conformity was that everyone liked you except yourself.” by Rita Mae Brown.
wonderful issues altogether, you simply won a new reader. What might you recommend in regards to your post that you made some days in the past? Any sure?
I think other web-site proprietors should take this web site as an model, very clean and fantastic user genial style and design, let alone the content. You are an expert in this topic!
Perfectly written subject matter, regards for information .
I do accept as true with all of the ideas you’ve presented for your post. They’re very convincing and can definitely work. Still, the posts are very short for starters. May you please extend them a little from next time? Thanks for the post.
I will immediately snatch your rss as I can’t to find your email subscription hyperlink or e-newsletter service. Do you have any? Kindly permit me understand so that I may just subscribe. Thanks.
Good – I should certainly pronounce, impressed with your web site. I had no trouble navigating through all tabs and related info ended up being truly easy to do to access. I recently found what I hoped for before you know it in the least. Quite unusual. Is likely to appreciate it for those who add forums or something, site theme . a tones way for your client to communicate. Nice task.
I’m so happy to read this. This is the type of manual that needs to be given and not the accidental misinformation that’s at the other blogs. Appreciate your sharing this greatest doc.
Hi my family member! I wish to say that this article is awesome, great written and come with approximately all vital infos. I would like to see more posts like this.
Very interesting topic, appreciate it for putting up.
I do trust all the concepts you have introduced on your post. They are very convincing and will definitely work. Still, the posts are very short for novices. May just you please lengthen them a bit from subsequent time? Thank you for the post.
What i do not realize is in fact how you are no longer really much more smartly-appreciated than you may be right now. You’re very intelligent. You understand thus significantly in the case of this matter, produced me for my part consider it from numerous varied angles. Its like women and men don’t seem to be fascinated unless it’s something to accomplish with Lady gaga! Your own stuffs excellent. All the time deal with it up!
You could definitely see your enthusiasm within the work you write. The sector hopes for even more passionate writers such as you who aren’t afraid to say how they believe. Always follow your heart.
I have not checked in here for a while since I thought it was getting boring, but the last few posts are good quality so I guess I¡¦ll add you back to my everyday bloglist. You deserve it my friend 🙂
I am extremely impressed with your writing skills and also with the layout on your blog. Is this a paid theme or did you customize it yourself? Anyway keep up the nice quality writing, it’s rare to see a great blog like this one nowadays..
Very interesting points you have remarked, regards for putting up. “The unspoken word never does harm.” by Kossuth.
Someone essentially assist to make significantly posts I would state. This is the first time I frequented your web page and so far? I amazed with the research you made to make this particular put up incredible. Magnificent task!
Hey There. I found your blog using msn. This is a very well written article. I’ll make sure to bookmark it and return to read more of your useful information. Thanks for the post. I’ll certainly return.
I like what you guys are up also. Such smart work and reporting! Keep up the excellent works guys I’ve incorporated you guys to my blogroll. I think it’ll improve the value of my web site :).
You are my inhalation , I have few blogs and rarely run out from to brand.
I genuinely enjoy reading on this website, it contains superb articles. “A short saying oft contains much wisdom.” by Sophocles.
Simply wish to say your article is as astonishing. The clearness in your post is simply excellent and i could assume you are an expert on this subject. Well with your permission let me to grab your feed to keep up to date with forthcoming post. Thanks a million and please carry on the gratifying work.
I dugg some of you post as I cogitated they were very useful very helpful
hello there and thank you for your info – I have certainly picked up something new from right here. I did however expertise some technical issues using this site, as I experienced to reload the website lots of times previous to I could get it to load properly. I had been wondering if your hosting is OK? Not that I’m complaining, but slow loading instances times will often affect your placement in google and can damage your quality score if ads and marketing with Adwords. Anyway I’m adding this RSS to my email and can look out for a lot more of your respective exciting content. Ensure that you update this again soon..
I would like to thnkx for the efforts you have put in writing this blog. I’m hoping the same high-grade website post from you in the upcoming as well. In fact your creative writing skills has inspired me to get my own web site now. Actually the blogging is spreading its wings rapidly. Your write up is a good example of it.
Whats Happening i am new to this, I stumbled upon this I have discovered It absolutely helpful and it has aided me out loads. I am hoping to give a contribution & help other users like its aided me. Good job.
Excellent read, I just passed this onto a friend who was doing some research on that. And he actually bought me lunch as I found it for him smile So let me rephrase that: Thank you for lunch!
Simply wish to say your article is as amazing. The clearness in your post is just great and i could assume you are an expert on this subject. Fine with your permission let me to grab your RSS feed to keep updated with forthcoming post. Thanks a million and please carry on the rewarding work.
You really make it appear so easy along with your presentation but I to find this matter to be really something that I think I might by no means understand. It kind of feels too complex and very broad for me. I am taking a look ahead to your subsequent submit, I¡¦ll try to get the dangle of it!
Unquestionably believe that which you stated. Your favorite justification appeared to be on the net the simplest thing to be aware of. I say to you, I definitely get irked while people consider worries that they just don’t know about. You managed to hit the nail upon the top as well as defined out the whole thing without having side effect , people could take a signal. Will likely be back to get more. Thanks
Wow! This could be one particular of the most helpful blogs We have ever arrive across on this subject. Actually Wonderful. I am also an expert in this topic so I can understand your hard work.
Excellent site. Lots of helpful info here. I’m sending it to a few friends ans also sharing in delicious. And certainly, thanks for your sweat!
Some genuinely choice content on this website , saved to my bookmarks .
Merely wanna admit that this is very helpful , Thanks for taking your time to write this.
Needed to post you this little bit of remark so as to give thanks once again for your personal extraordinary strategies you have featured at this time. It was really shockingly open-handed with you to offer freely precisely what most people would have offered for an e-book to generate some cash for themselves, mostly since you might have done it in the event you decided. The pointers additionally acted as the great way to be aware that other individuals have a similar fervor similar to mine to realize a whole lot more in terms of this matter. I think there are some more fun times in the future for those who find out your blog post.
I believe you have mentioned some very interesting points , appreciate it for the post.
Hi there, You have done an incredible job. I’ll definitely digg it and personally recommend to my friends. I’m sure they will be benefited from this website.
I truly appreciate this post. I¡¦ve been looking all over for this! Thank goodness I found it on Bing. You have made my day! Thanks again
I do accept as true with all of the ideas you have offered for your post. They’re really convincing and will certainly work. Still, the posts are very quick for starters. May just you please extend them a little from subsequent time? Thanks for the post.
Hiya, I’m really glad I have found this information. Today bloggers publish only about gossips and net and this is actually irritating. A good web site with exciting content, that’s what I need. Thank you for keeping this website, I will be visiting it. Do you do newsletters? Can not find it.
I do not even know how I ended up here, but I thought this post was great. I do not know who you are but certainly you’re going to a famous blogger if you are not already 😉 Cheers!
Hello.This post was extremely fascinating, especially because I was looking for thoughts on this topic last couple of days.
Hello, Neat post. There is a problem with your website in web explorer, might check this¡K IE nonetheless is the marketplace chief and a large portion of other people will pass over your great writing because of this problem.
You made a few good points there. I did a search on the theme and found nearly all folks will agree with your blog.
My wife and i got very comfortable Peter could do his inquiry from the precious recommendations he got while using the site. It’s not at all simplistic to just continually be releasing hints which usually some other people have been selling. And we all do understand we need you to appreciate for that. The illustrations you made, the easy site menu, the relationships you can assist to promote – it is mostly terrific, and it’s letting our son in addition to our family consider that that subject matter is entertaining, which is truly vital. Thank you for the whole thing!
I just could not depart your website prior to suggesting that I actually loved the usual information an individual provide for your visitors? Is gonna be back ceaselessly to check up on new posts
Hey, you used to write excellent, but the last few posts have been kinda boring¡K I miss your great writings. Past few posts are just a little out of track! come on!
I have been surfing online more than three hours today, yet I never found any interesting article like yours. It is pretty worth enough for me. In my view, if all site owners and bloggers made good content as you did, the internet will be a lot more useful than ever before.
Hello, i think that i saw you visited my website so i came to “return the favor”.I’m attempting to find things to improve my website!I suppose its ok to use a few of your ideas!!
I truly appreciate this post. I have been looking all over for this! Thank goodness I found it on Bing. You have made my day! Thanks again
I like the valuable information you provide in your articles. I’ll bookmark your blog and check again here frequently. I am quite certain I will learn lots of new stuff right here! Best of luck for the next!
Hi, Neat post. There is an issue along with your site in internet explorer, would test this¡K IE still is the market leader and a good portion of other people will pass over your excellent writing because of this problem.
Useful info. Lucky me I discovered your website by accident, and I’m shocked why this accident did not happened earlier! I bookmarked it.
hello!,I really like your writing so much! percentage we keep up a correspondence more approximately your article on AOL? I require a specialist in this area to resolve my problem. May be that is you! Taking a look forward to look you.
Hello There. I found your blog using msn. This is an extremely well written article. I will be sure to bookmark it and come back to read more of your useful information. Thanks for the post. I will definitely return.
Nice blog here! Additionally your website loads up fast! What host are you the use of? Can I get your affiliate link on your host? I want my website loaded up as quickly as yours lol
Hello There. I found your blog using msn. This is a really well written article. I’ll be sure to bookmark it and come back to read more of your useful info. Thanks for the post. I’ll certainly comeback.
Excellent beat ! I wish to apprentice while you amend your web site, how could i subscribe for a blog site? The account helped me a acceptable deal. I had been a little bit acquainted of this your broadcast provided bright clear idea
I’ve been browsing on-line more than 3 hours these days, but I never discovered any attention-grabbing article like yours. It¡¦s beautiful worth enough for me. In my view, if all site owners and bloggers made just right content material as you probably did, the net will probably be much more useful than ever before.
Way cool! Some very valid points! I appreciate you writing this article and the rest of the website is also very good.
Magnificent site. Lots of helpful info here. I¡¦m sending it to a few buddies ans additionally sharing in delicious. And naturally, thanks in your sweat!
I’ve been absent for a while, but now I remember why I used to love this website. Thank you, I¡¦ll try and check back more often. How frequently you update your website?
You could definitely see your expertise within the paintings you write. The sector hopes for even more passionate writers such as you who aren’t afraid to say how they believe. At all times go after your heart.
magnificent publish, very informative. I ponder why the other specialists of this sector do not understand this. You should proceed your writing. I’m sure, you’ve a huge readers’ base already!
Nice read, I just passed this onto a colleague who was doing a little research on that. And he just bought me lunch since I found it for him smile Therefore let me rephrase that: Thanks for lunch! “We know what happens to people who stay in the middle of the road. They get run over.” by Ambrose Gwinett Bierce.
I wish to show thanks to the writer just for bailing me out of this difficulty. As a result of browsing throughout the world-wide-web and obtaining ways which were not pleasant, I figured my life was well over. Existing devoid of the strategies to the issues you have fixed by means of the posting is a critical case, and those that might have in a wrong way affected my entire career if I hadn’t come across your web blog. The expertise and kindness in taking care of everything was vital. I am not sure what I would have done if I had not come across such a solution like this. I am able to at this moment look ahead to my future. Thank you very much for your specialized and amazing guide. I will not think twice to suggest your blog post to anyone who needs recommendations about this subject.
I think other site proprietors should take this site as an model, very clean and magnificent user friendly style and design, as well as the content. You’re an expert in this topic!
It¡¦s really a cool and useful piece of info. I¡¦m happy that you simply shared this helpful info with us. Please stay us up to date like this. Thanks for sharing.
I simply couldn’t go away your website prior to suggesting that I extremely loved the standard information a person provide to your visitors? Is gonna be again often in order to investigate cross-check new posts
I like what you guys are up also. Such clever work and reporting! Carry on the superb works guys I’ve incorporated you guys to my blogroll. I think it’ll improve the value of my site :).
My spouse and i have been thrilled when Raymond managed to conclude his reports by way of the ideas he obtained from your blog. It is now and again perplexing to just continually be giving for free points which often most people might have been selling. We really consider we now have the writer to thank for that. The type of illustrations you made, the simple website navigation, the friendships you can make it easier to promote – it’s got many overwhelming, and it’s really assisting our son in addition to our family do think this content is amusing, which is certainly especially essential. Thanks for all the pieces!
Some really superb information, Glad I observed this. “Children require guidance and sympathy far more than instruction.” by Ambrose Gwinett Bierce.
I gotta bookmark this web site it seems very beneficial invaluable
Very nice style and great subject material , hardly anything else we require : D.
Somebody essentially lend a hand to make seriously articles I would state. That is the first time I frequented your website page and to this point? I amazed with the analysis you made to create this actual submit extraordinary. Excellent process!
My wife and i felt so fortunate when Peter managed to deal with his investigation because of the ideas he obtained using your site. It’s not at all simplistic just to be giving for free information and facts which usually some others might have been making money from. And we all already know we now have the blog owner to be grateful to for that. All the illustrations you’ve made, the easy blog navigation, the friendships your site help instill – it’s got many awesome, and it’s really facilitating our son in addition to us feel that the idea is enjoyable, which is highly serious. Thanks for everything!
Some genuinely excellent information, Gladiolus I detected this. “If a child can’t learn the way we teach, maybe we should teach the way they learn.” by Ignacio Estrada.
I am now not certain the place you are getting your info, however good topic. I must spend a while finding out much more or figuring out more. Thank you for wonderful information I used to be in search of this information for my mission.
Hiya, I’m really glad I’ve found this information. Today bloggers publish just about gossips and web and this is actually frustrating. A good site with interesting content, this is what I need. Thank you for keeping this web-site, I will be visiting it. Do you do newsletters? Cant find it.
great post, very informative. I wonder why the other experts of this sector don’t notice this. You should continue your writing. I am confident, you’ve a great readers’ base already!
Its like you read my mind! You seem to know a lot about this, like you wrote the book in it or something. I think that you could do with some pics to drive the message home a bit, but instead of that, this is great blog. A great read. I’ll definitely be back.
You should take part in a contest for one of the most useful blogs on the net. I will recommend this website!
Fantastic beat ! I wish to apprentice while you amend your website, how can i subscribe for a blog web site? The account aided me a acceptable deal. I had been tiny bit acquainted of this your broadcast offered bright clear idea
Good – I should definitely pronounce, impressed with your web site. I had no trouble navigating through all tabs as well as related information ended up being truly simple to do to access. I recently found what I hoped for before you know it at all. Reasonably unusual. Is likely to appreciate it for those who add forums or something, site theme . a tones way for your customer to communicate. Nice task.
You have remarked very interesting points ! ps decent website . “Never take the advice of someone who has not had your kind of trouble.” by Sydney J. Harris.
You could definitely see your expertise in the work you write. The arena hopes for even more passionate writers such as you who are not afraid to say how they believe. All the time go after your heart.
Undeniably believe that which you said. Your favorite justification seemed to be on the internet the simplest thing to be aware of. I say to you, I definitely get annoyed while people think about worries that they just don’t know about. You managed to hit the nail upon the top and defined out the whole thing without having side-effects , people could take a signal. Will likely be back to get more. Thanks
There is visibly a bundle to identify about this. I assume you made certain good points in features also.
I do not even know how I ended up here, but I thought this post was good. I do not know who you are but certainly you’re going to a famous blogger if you aren’t already 😉 Cheers!
There is perceptibly a lot to realize about this. I feel you made certain nice points in features also.
I dugg some of you post as I cerebrated they were handy very beneficial
As I website possessor I believe the content material here is rattling fantastic , appreciate it for your efforts. You should keep it up forever! Best of luck.
Well I really enjoyed studying it. This information offered by you is very effective for correct planning.
I am now not positive where you’re getting your information, but great topic. I needs to spend a while learning much more or figuring out more. Thanks for wonderful information I was on the lookout for this information for my mission.
Aw, this was an extremely nice post. Spending some time and actual effort to generate a good article… but what can I say… I hesitate a whole lot and don’t seem to get nearly anything done.
Very interesting information!Perfect just what I was searching for! “Better and ugly face than an ugly mind.” by James.
I would like to change my blogger archive frequency from 1 month to longer, like 3 months. How do I do this?.
It¡¦s really a nice and helpful piece of information. I¡¦m glad that you shared this helpful info with us. Please stay us informed like this. Thanks for sharing.
Merely wanna comment on few general things, The website design is perfect, the subject material is really superb : D.
Definitely, what a fantastic site and enlightening posts, I definitely will bookmark your website.Best Regards!
You completed a number of fine points there. I did a search on the subject and found the majority of folks will consent with your blog.
Terrific paintings! That is the type of information that are supposed to be shared around the internet. Disgrace on Google for now not positioning this put up upper! Come on over and talk over with my website . Thanks =)
Great post. I was checking constantly this blog and I am impressed! Extremely helpful information specifically the last part 🙂 I care for such information much. I was seeking this particular information for a very long time. Thank you and best of luck.
hello!,I love your writing very so much! share we keep in touch extra approximately your post on AOL? I require a specialist on this space to resolve my problem. Maybe that is you! Having a look ahead to look you.
I’ve been browsing online more than 3 hours nowadays, yet I never discovered any interesting article like yours. It¡¦s lovely value enough for me. In my opinion, if all website owners and bloggers made just right content material as you probably did, the web will likely be a lot more helpful than ever before.
Whats Happening i’m new to this, I stumbled upon this I have found It positively useful and it has aided me out loads. I’m hoping to give a contribution & assist other users like its aided me. Good job.
Definitely, what a splendid website and illuminating posts, I will bookmark your site.All the Best!
I in addition to my friends came reviewing the excellent key points located on your site and so all of the sudden I had a terrible feeling I never expressed respect to the web site owner for those techniques. Those boys ended up totally glad to learn them and have now without a doubt been taking advantage of them. Thanks for truly being very helpful and also for finding varieties of amazing areas most people are really wanting to discover. My personal honest regret for not expressing appreciation to you sooner.
I do believe all the ideas you’ve introduced in your post. They are very convincing and will certainly work. Still, the posts are too quick for novices. May just you please extend them a little from next time? Thanks for the post.
Thank you for sharing excellent informations. Your site is so cool. I’m impressed by the details that you have on this blog. It reveals how nicely you perceive this subject. Bookmarked this website page, will come back for extra articles. You, my friend, ROCK! I found simply the information I already searched all over the place and simply couldn’t come across. What a perfect web site.
I and my friends appeared to be analyzing the good suggestions on your web blog then suddenly came up with an awful suspicion I had not thanked the site owner for them. These people came consequently warmed to see them and have in effect unquestionably been using these things. Appreciation for turning out to be quite thoughtful as well as for opting for certain beneficial guides most people are really desirous to discover. My personal honest apologies for not expressing appreciation to sooner.
Great work! This is the type of info that should be shared around the web. Shame on Google for not positioning this post higher! Come on over and visit my web site . Thanks =)
of course like your website however you have to test the spelling on quite a few of your posts. Several of them are rife with spelling problems and I in finding it very bothersome to tell the reality nevertheless I will surely come back again.
Hi my friend! I wish to say that this article is amazing, nice written and include almost all important infos. I would like to look more posts like this .
You could definitely see your enthusiasm in the work you write. The world hopes for more passionate writers such as you who are not afraid to mention how they believe. At all times go after your heart. “There are only two industries that refer to their customers as users.” by Edward Tufte.
A lot of thanks for every one of your labor on this web page. My aunt takes pleasure in participating in investigation and it’s really simple to grasp why. We all know all regarding the powerful way you produce sensible tips and tricks on the web blog and as well as encourage response from the others on this subject then our girl has always been learning a great deal. Enjoy the remaining portion of the year. You have been performing a great job.
Whats Going down i’m new to this, I stumbled upon this I have found It positively useful and it has aided me out loads. I hope to contribute & aid other users like its helped me. Great job.
Thanks for sharing superb informations. Your site is very cool. I’m impressed by the details that you have on this site. It reveals how nicely you understand this subject. Bookmarked this web page, will come back for extra articles. You, my friend, ROCK! I found simply the info I already searched all over the place and just could not come across. What a perfect site.
I would like to thank you for the efforts you’ve put in writing this site. I am hoping the same high-grade web site post from you in the upcoming as well. In fact your creative writing abilities has inspired me to get my own blog now. Actually the blogging is spreading its wings quickly. Your write up is a great example of it.
You made some nice points there. I looked on the internet for the issue and found most people will approve with your website.
As I site possessor I believe the content material here is rattling magnificent , appreciate it for your hard work. You should keep it up forever! Good Luck.
Good website! I really love how it is easy on my eyes and the data are well written. I am wondering how I might be notified when a new post has been made. I’ve subscribed to your feed which must do the trick! Have a great day!
I’ve been absent for some time, but now I remember why I used to love this web site. Thanks , I will try and check back more frequently. How frequently you update your website?
I’m so happy to read this. This is the kind of manual that needs to be given and not the accidental misinformation that is at the other blogs. Appreciate your sharing this greatest doc.
I simply want to say I am beginner to blogging and site-building and seriously loved this web site. Most likely I’m likely to bookmark your blog . You surely come with good writings. Thanks a bunch for sharing your web page.
Thanks for sharing superb informations. Your web site is so cool. I am impressed by the details that you¡¦ve on this web site. It reveals how nicely you understand this subject. Bookmarked this web page, will come back for extra articles. You, my pal, ROCK! I found simply the info I already searched everywhere and simply couldn’t come across. What an ideal web-site.
Valuable information. Fortunate me I found your web site by chance, and I am shocked why this coincidence did not happened in advance! I bookmarked it.
We’re a group of volunteers and starting a new scheme in our community. Your site offered us with valuable info to work on. You’ve done an impressive job and our entire community will be thankful to you.
I have been surfing online more than three hours today, yet I never found any interesting article like yours. It’s pretty worth enough for me. In my view, if all web owners and bloggers made good content as you did, the net will be much more useful than ever before.
Good website! I truly love how it is simple on my eyes and the data are well written. I’m wondering how I could be notified whenever a new post has been made. I have subscribed to your feed which must do the trick! Have a nice day!
certainly like your web-site however you need to take a look at the spelling on quite a few of your posts. A number of them are rife with spelling problems and I to find it very bothersome to tell the reality on the other hand I¡¦ll certainly come again again.
Wow! This could be one particular of the most helpful blogs We’ve ever arrive across on this subject. Basically Excellent. I’m also an expert in this topic so I can understand your hard work.
I am just writing to make you be aware of what a helpful experience our girl found using your webblog. She even learned numerous things, which included how it is like to possess a very effective giving nature to make many others with ease grasp a variety of very confusing issues. You truly did more than our expected results. I appreciate you for providing these invaluable, healthy, educational and even unique thoughts on your topic to Tanya.
I loved as much as you will receive carried out right here. The sketch is attractive, your authored subject matter stylish. nonetheless, you command get got an nervousness over that you wish be delivering the following. unwell unquestionably come more formerly again since exactly the same nearly very often inside case you shield this increase.
Thank you, I’ve just been looking for information approximately this subject for a while and yours is the greatest I have discovered so far. However, what about the bottom line? Are you positive concerning the supply?
Somebody essentially lend a hand to make critically posts I might state. That is the first time I frequented your web page and thus far? I amazed with the research you made to make this actual publish extraordinary. Excellent process!
I keep listening to the news broadcast lecture about receiving boundless online grant applications so I have been looking around for the finest site to get one. Could you advise me please, where could i find some?
Great ¡V I should definitely pronounce, impressed with your site. I had no trouble navigating through all tabs and related info ended up being truly easy to do to access. I recently found what I hoped for before you know it in the least. Quite unusual. Is likely to appreciate it for those who add forums or anything, website theme . a tones way for your customer to communicate. Nice task..
Hi, Neat post. There’s an issue along with your website in web explorer, could check this¡K IE still is the market leader and a huge element of other folks will omit your excellent writing because of this problem.
It’s the best time to make some plans for the future and it’s time to be happy. I have read this post and if I could I desire to suggest you some interesting things or tips. Perhaps you can write next articles referring to this article. I want to read more things about it!
This is one awesome blog. Will read on…
Great tremendous things here. I¡¦m very satisfied to look your article. Thanks so much and i am looking forward to touch you. Will you please drop me a mail?
you are in reality a excellent webmaster. The site loading speed is amazing. It kind of feels that you are doing any unique trick. Moreover, The contents are masterpiece. you’ve done a wonderful process in this matter!
I cling on to listening to the news bulletin talk about getting boundless online grant applications so I have been looking around for the best site to get one. Could you advise me please, where could i find some?
Simply a smiling visitor here to share the love (:, btw great layout.
I have to voice my passion for your kindness supporting individuals that have the need for help with this particular niche. Your very own dedication to passing the solution across became amazingly significant and have encouraged those like me to realize their targets. Your valuable instruction can mean a lot a person like me and a whole lot more to my mates. Best wishes; from each one of us.
It is in point of fact a great and helpful piece of information. I am happy that you shared this helpful info with us. Please stay us informed like this. Thanks for sharing.
I am so happy to read this. This is the kind of manual that needs to be given and not the accidental misinformation that’s at the other blogs. Appreciate your sharing this best doc.
Hello, you used to write magnificent, but the last several posts have been kinda boring… I miss your great writings. Past few posts are just a little out of track! come on!
Your place is valueble for me. Thanks!…
Nice blog here! Also your web site so much up fast! What web host are you the usage of? Can I get your associate link for your host? I wish my website loaded up as quickly as yours lol
I think this is among the so much important info for me. And i am satisfied reading your article. But wanna observation on few general things, The website taste is wonderful, the articles is truly nice : D. Good activity, cheers
My spouse and i felt very contented that Jordan could finish up his research while using the precious recommendations he received from your very own weblog. It is now and again perplexing to simply always be giving out tips and tricks that some other people might have been making money from. Therefore we do know we need the writer to thank for this. The entire explanations you’ve made, the easy website navigation, the relationships your site give support to foster – it is all amazing, and it’s really aiding our son and our family imagine that that subject is amusing, which is certainly seriously vital. Thank you for the whole lot!
You made some nice points there. I looked on the internet for the topic and found most people will approve with your blog.
hey there and thank you on your info – I’ve certainly picked up something new from right here. I did then again expertise some technical issues using this web site, since I skilled to reload the website many instances previous to I may just get it to load properly. I have been puzzling over if your hosting is OK? No longer that I’m complaining, however sluggish loading circumstances times will very frequently affect your placement in google and could harm your quality ranking if advertising and ***********|advertising|advertising|advertising and *********** with Adwords. Well I am adding this RSS to my email and can glance out for a lot more of your respective intriguing content. Make sure you update this once more very soon..
Just wanna comment on few general things, The website design and style is perfect, the content is rattling good. “The enemy is anybody who’s going to get you killed, no matter which side he’s on.” by Joseph Heller.
Hi would you mind stating which blog platform you’re working with? I’m planning to start my own blog in the near future but I’m having a tough time choosing between BlogEngine/Wordpress/B2evolution and Drupal. The reason I ask is because your design seems different then most blogs and I’m looking for something completely unique. P.S Apologies for being off-topic but I had to ask!
It’s hard to finddifficult to findnearly impossible to findhard to come by knowledgeableeducatedwell-informedexperienced people on thisabout thisfor thisin this particular topicsubject, but youhowever, you sound likeseem like you know what you’re talking about! Thanks
I loved as much as you’ll receive carried out right here. The sketch is tasteful, your authored material stylish. nonetheless, you command get got an shakiness over that you wish be delivering the following. unwell unquestionably come more formerly again since exactly the same nearly a lot often inside case you shield this hike.
Exceptional post but I was wanting to know if you could write a litte more on this subject? I’d be very grateful if you could elaborate a little bit more. Thanks!
Great ¡V I should certainly pronounce, impressed with your site. I had no trouble navigating through all the tabs as well as related information ended up being truly easy to do to access. I recently found what I hoped for before you know it at all. Quite unusual. Is likely to appreciate it for those who add forums or something, web site theme . a tones way for your client to communicate. Excellent task..
I would like to thnkx for the efforts you’ve put in writing this site. I’m hoping the same high-grade blog post from you in the upcoming as well. Actually your creative writing abilities has encouraged me to get my own site now. Really the blogging is spreading its wings quickly. Your write up is a great example of it.
What i do not realize is actually how you’re not really much more well-liked than you might be right now. You are so intelligent. You realize therefore significantly relating to this subject, made me personally consider it from a lot of varied angles. Its like men and women aren’t fascinated unless it’s one thing to accomplish with Lady gaga! Your own stuffs outstanding. Always maintain it up!
I have been absent for some time, but now I remember why I used to love this site. Thanks , I’ll try and check back more often. How frequently you update your web site?
I’ve noticed that repairing credit activity needs to be conducted with tactics. If not, you may find yourself destroying your standing. In order to reach your goals in fixing your credit ranking you have to see to it that from this moment you pay any monthly expenses promptly in advance of their booked date. It really is significant since by not necessarily accomplishing so, all other moves that you will take to improve your credit rating will not be powerful. Thanks for revealing your ideas.
Thank you for the sensible critique. Me & my neighbor were just preparing to do a little research about this. We got a grab a book from our area library but I think I learned more clear from this post. I’m very glad to see such wonderful info being shared freely out there.
WONDERFUL Post.thanks for share..extra wait .. …
Anyone else having issues viewing this on mobile device?
Keep working ,remarkable job!
Hello there, just became aware of your blog through Google, and found that it is really informative. I’m going to watch out for brussels. I will appreciate if you continue this in future. A lot of people will be benefited from your writing. Cheers!
One other issue issue is that video games can be serious anyway with the principal focus on knowing things rather than leisure. Although, there’s an entertainment part to keep the kids engaged, every single game is usually designed to develop a specific experience or curriculum, such as math or technology. Thanks for your posting.
Hello There. I discovered your blog using msn. This is a very neatly written article. I’ll make sure to bookmark it and come back to learn extra of your helpful info. Thank you for the post. I’ll definitely return.
I like what you guys are up also. Such smart work and reporting! Keep up the excellent works guys I have incorporated you guys to my blogroll. I think it will improve the value of my site 🙂
Another thing I’ve noticed is always that for many people, poor credit is the result of circumstances further than their control. One example is they may have been saddled by having an illness so they have large bills for collections. It could be due to a occupation loss or even the inability to do the job. Sometimes divorce can truly send the finances in the wrong direction. Thanks sharing your ideas on this blog site.
Magnificent goods from you, man. I’ve be mindful your stuff prior to and you are simply extremely great. I actually like what you have received right here, certainly like what you’re saying and the best way during which you assert it. You make it enjoyable and you still take care of to stay it smart. I can’t wait to learn far more from you. That is really a wonderful web site.
What I have seen in terms of pc memory is the fact that there are technical specs such as SDRAM, DDR and so forth, that must go with the features of the motherboard. If the personal computer’s motherboard is rather current and there are no os issues, updating the storage space literally requires under 1 hour. It’s among the list of easiest laptop or computer upgrade methods one can think about. Thanks for spreading your ideas.
I have been surfing on-line greater than three hours lately, yet I by no means found any interesting article like yours. It is beautiful price enough for me. Personally, if all webmasters and bloggers made good content as you did, the web might be much more useful than ever before.
Greetings I am so delighted I found your website, I really found you by mistake, while I was browsing on Aol for something else, Nonetheless I am here now and would just like to say kudos for a tremendous post and a all round enjoyable blog (I also love the theme/design), I don’t have time to browse it all at the moment but I have bookmarked it and also added in your RSS feeds, so when I have time I will be back to read much more, Please do keep up the excellent work.
Hey there, You have done a fantastic job. I will definitely digg it and individually suggest to my friends. I am confident they’ll be benefited from this web site.
HeyHowdyHi thereHeyaHey thereHiHello just wanted to give you a quickbrief heads up and let you know a few of the imagespictures aren’t loading correctlyproperly. I’m not sure why but I think its a linking issue. I’ve tried it in two different browsersinternet browsersweb browsers and both show the same resultsoutcome.
I needed to write you one bit of note to help give thanks once again just for the lovely basics you have provided on this website. This has been really strangely generous with people like you to deliver publicly all that most of us might have offered for sale as an electronic book to generate some money for their own end, certainly considering the fact that you might well have done it in the event you desired. Those principles in addition worked as a great way to comprehend some people have the same eagerness the same as my own to realize great deal more when considering this issue. I’m certain there are a lot more pleasant sessions ahead for individuals that read through your blog post.
I’m truly enjoying the design and layout of your website. It’s a very easy on the eyes which makes it much more enjoyable for me to come here and visit more often. Did you hire out a designer to create your theme? Outstanding work!
Finally someone that knows what they’re talking about.
I would like to add that in case you do not surely have an insurance policy otherwise you do not belong to any group insurance, you may well make use of seeking the help of a health insurance agent. Self-employed or individuals with medical conditions commonly seek the help of the health insurance specialist. Thanks for your article.
Throughout this great design of things you secure a B- just for hard work. Where you misplaced us ended up being on your particulars. As it is said, the devil is in the details… And it could not be much more true at this point. Having said that, permit me tell you what did deliver the results. The writing is certainly rather engaging and that is probably why I am taking an effort to comment. I do not really make it a regular habit of doing that. Next, while I can easily see a leaps in reasoning you come up with, I am definitely not convinced of exactly how you appear to connect your ideas which produce your conclusion. For the moment I will, no doubt subscribe to your position however wish in the foreseeable future you connect the dots better.
Hi there, i read your blog occasionally and i own a similar one and i was just wondering if you get a lot of spam comments? If so how do you reduce it, any plugin or anything you can advise? I get so much lately it’s driving me crazy so any assistance is very much appreciated.
I think this is one of the most important information for me. And i’m glad reading your article. But want to remark on some general things, The website style is wonderful, the articles is really great : D. Good job, cheers
This is very interesting, You are a very skilled blogger. I’ve joined your feed and look forward to seeking more of your wonderful post. Also, I’ve shared your site in my social networks!
It’s really a nice and helpful piece of info. I’m glad that you shared this useful info with us. Please keep us informed like this. Thanks for sharing.
According to my observation, after a the foreclosure home is offered at a sale, it is common for any borrower in order to still have a remaining unpaid debt on the mortgage loan. There are many loan merchants who aim to have all fees and liens cleared by the subsequent buyer. However, depending on particular programs, polices, and state laws and regulations there may be several loans that aren’t easily fixed through the shift of lending products. Therefore, the obligation still lies on the lender that has obtained his or her property in foreclosure process. Many thanks sharing your ideas on this blog.
Thanks for the write-up. I have continually noticed that many people are eager to lose weight simply because wish to look slim plus attractive. However, they do not often realize that there are more benefits so that you can losing weight as well. Doctors assert that over weight people suffer from a variety of disorders that can be perfectely attributed to the excess weight. Fortunately that people that are overweight and also suffering from diverse diseases can reduce the severity of the illnesses by means of losing weight. It is easy to see a progressive but noted improvement in health when even a minor amount of losing weight is attained.
wonderful points altogether, you just received a brand new reader. What might you recommend about your publish that you just made some days in the past? Any certain?
I keep listening to the news update talk about getting free online grant applications so I have been looking around for the most excellent site to get one. Could you advise me please, where could i get some?
Hey there! I know this is kind of off topic but I was wondering if you knew where I could find a captcha plugin for my comment form? I’m using the same blog platform as yours and I’m having problems finding one? Thanks a lot!
I do agree with all the concepts you have introduced in your post. They’re really convincing and will certainly work. Still, the posts are too quick for newbies. May you please lengthen them a little from subsequent time? Thank you for the post.
I have read so many articlespostsarticles or reviewscontent regardingconcerningabouton the topic of the blogger lovers butexcepthowever this articlepostpiece of writingparagraph is reallyactuallyin facttrulygenuinely a nicepleasantgoodfastidious articlepostpiece of writingparagraph, keep it up.
I¡¦ve read several good stuff here. Certainly price bookmarking for revisiting. I surprise how a lot effort you set to make the sort of magnificent informative website.
This is aThat is a very goodgreatgoodreally good tip especiallyparticularly to those new tofresh to the blogosphere. BriefShortSimple but very accurateprecise informationinfo… Thanks forThank you forMany thanks forAppreciate your sharing this one. A must read articlepost!
What i do not understood is actually how you’re no longer really a lot more smartly-preferred than you may be now. You are so intelligent. You already know thus considerably in terms of this matter, produced me personally believe it from so many varied angles. Its like women and men don’t seem to be interested unless it is one thing to accomplish with Woman gaga! Your individual stuffs great. At all times handle it up!
Merely wanna say that this is very beneficial , Thanks for taking your time to write this.
I like what you guys are up also. Such clever work and reporting! Carry on the superb works guys I have incorporated you guys to my blogroll. I think it will improve the value of my website :).
I¡¦ve been exploring for a little bit for any high-quality articles or blog posts in this kind of space . Exploring in Yahoo I finally stumbled upon this website. Reading this info So i¡¦m satisfied to convey that I have a very excellent uncanny feeling I discovered just what I needed. I most indubitably will make certain to do not disregard this website and provides it a glance on a continuing basis.
Very interesting information!Perfect just what I was looking for! “Water is the most neglected nutrient in your diet but one of the most vital.” by Kelly Barton.
I have learn a few excellent stuff here. Certainly value bookmarking for revisiting. I surprise how much effort you place to make one of these excellent informative website.
Hello.This article was extremely interesting, particularly since I was searching for thoughts on this issue last Wednesday.
Wow! Thank you! I continuously needed to write on my blog something like that. Can I include a part of your post to my blog?
I will right away take hold of your rss as I can’t in finding your e-mail subscription hyperlink or newsletter service. Do you have any? Kindly let me recognise so that I could subscribe. Thanks.
of course like your web-site but you have to check the spelling on quite a few of your posts. Many of them are rife with spelling problems and I in finding it very bothersome to inform the reality however I will certainly come again again.
I went over this website and I conceive you have a lot of fantastic info, saved to my bookmarks (:.
I loved as much as you’ll receive carried out right here. The sketch is attractive, your authored material stylish. nonetheless, you command get bought an impatience over that you wish be delivering the following. unwell unquestionably come further formerly again as exactly the same nearly a lot often inside case you shield this hike.
Generally I do not read post on blogs, but I would like to say that this write-up very compelled me to take a look at and do it! Your writing taste has been surprised me. Thanks, quite great article.
Thanks for the sensible critique. Me and my neighbor were just preparing to do a little research about this. We got a grab a book from our local library but I think I learned more from this post. I am very glad to see such excellent info being shared freely out there.
Hello. Great job. I did not anticipate this. This is a splendid story. Thanks!
Thanks for all your valuable effort on this web page. Ellie take interest in setting aside time for investigations and it’s obvious why. We learn all concerning the lively means you produce invaluable guides on this website and attract contribution from others on the content and our own girl is certainly discovering a whole lot. Take pleasure in the rest of the new year. You have been carrying out a glorious job.
obviously like your web-site however you have to check the spelling on several of your posts. A number of them are rife with spelling problems and I in finding it very troublesome to inform the reality on the other hand I will surely come back again.
excellent points altogether, you just gained a new reader. What might you recommend about your put up that you just made some days in the past? Any positive?
You madeYou’ve madeYou have made some decentgoodreally good points there. I lookedchecked on the interneton the webon the net for more infofor more informationto find out moreto learn morefor additional information about the issue and found most individualsmost people will go along with your views on this websitethis sitethis web site.
Excellent blog here! Also your website a lot up very fast! What host are you the use of? Can I am getting your associate link for your host? I want my website loaded up as fast as yours lol
Usually I don’t read article on blogs, but I wish to say that this write-up very compelled me to check out and do it! Your writing taste has been surprised me. Thanks, very great article.
Hey there, You have done an excellent job. I’ll definitely digg it and personally recommend to my friends. I am sure they will be benefited from this site.
I’m not sure where you are getting your info, but good topic. I needs to spend some time learning more or understanding more. Thanks for excellent info I was looking for this information for my mission.
Thank you for the sensible critique. Me & my neighbor were just preparing to do some research on this. We got a grab a book from our local library but I think I learned more from this post. I am very glad to see such wonderful information being shared freely out there.
I needed to send you one little bit of observation just to thank you so much the moment again considering the awesome tips you’ve discussed on this page. It is really shockingly open-handed with people like you to convey freely precisely what a number of people might have distributed as an e-book in order to make some bucks for themselves, notably considering the fact that you could possibly have done it if you ever considered necessary. Those points in addition served to become a easy way to fully grasp that other people online have similar keenness just like my very own to grasp great deal more in terms of this matter. I am sure there are a lot more enjoyable times ahead for those who read through your blog post.
You could certainly see your enthusiasm in the paintings you write. The world hopes for more passionate writers like you who aren’t afraid to mention how they believe. Always follow your heart. “Every man serves a useful purpose A miser, for example, makes a wonderful ancestor.” by Laurence J. Peter.
I’ve been browsing online greater than three hours lately, but I never found any fascinating article like yours. It is pretty value sufficient for me. Personally, if all website owners and bloggers made excellent content material as you probably did, the internet might be much more useful than ever before.
Great tremendous issues here. I¡¦m very satisfied to peer your post. Thank you so much and i am having a look forward to contact you. Will you please drop me a e-mail?
I wasI used to be able to find good infoinformationadvice from your blog postsblog articlesarticlescontent.
I dugg some of you post as I thought they were extremely helpful very helpful
I really like your writing style, superb information, appreciate it for putting up :D. “Faith is a continuation of reason.” by William Adams.
Hi, Neat post. There is an issue along with your site in web explorer, may check this… IE nonetheless is the market chief and a huge section of people will pass over your magnificent writing due to this problem.
hi!,I really like your writing so much! percentage we keep up a correspondence extra approximately your article on AOL? I need a specialist in this space to solve my problem. May be that’s you! Looking ahead to peer you.
I’m really impressed with your writing skills and also with the layout on your weblog. Is this a paid theme or did you customize it yourself? Anyway keep up the excellent quality writing, it is rare to see a nice blog like this one nowadays..
I am glad for commenting to let you know of the exceptional encounter our daughter went through visiting the blog. She discovered a wide variety of issues, including what it is like to possess an amazing teaching mood to have many others really easily have an understanding of a variety of complex subject matter. You truly did more than our desires. Many thanks for churning out the powerful, trustworthy, revealing and cool guidance on your topic to Tanya.
Some genuinely nice and useful information on this internet site, besides I believe the style and design contains good features.
I am really impressed with your writing skills as well as with the layout on your weblog. Is this a paid theme or did you customize it yourself? Either way keep up the nice quality writing, it is rare to see a nice blog like this one today..
Wow, marvelous blog layout! How long have you been blogging for? you made blogging look easy. The overall look of your website is fantastic, let alone the content!
Very good information can be found on site . “You have to learn that if you start making sure you feel good, everything will be okay.” by Ruben Studdard.
As a Newbie, I am permanently browsing online for articles that can be of assistance to me. Thank you
I must express thanks to you for rescuing me from such a situation. As a result of scouting throughout the online world and finding notions which were not helpful, I believed my entire life was done. Existing devoid of the strategies to the issues you’ve solved by means of your entire review is a crucial case, as well as ones that would have badly damaged my career if I had not noticed your blog. Your capability and kindness in maneuvering all the details was vital. I don’t know what I would have done if I had not come upon such a thing like this. I am able to now look forward to my future. Thanks for your time so much for this high quality and result oriented guide. I will not think twice to propose your blog to anybody who desires assistance about this matter.
We’re a group of volunteers and starting a new scheme in our community. Your web site provided us with valuable info to work on. You’ve done a formidable job and our entire community will be thankful to you.
Some truly choice posts on this web site , saved to my bookmarks .
I’m just commenting to make you be aware of what a extraordinary experience my cousin’s girl had studying your web site. She even learned some details, which include how it is like to possess an awesome coaching nature to make a number of people smoothly master specific complex things. You truly exceeded my expected results. Thanks for distributing the beneficial, trustworthy, revealing and in addition cool thoughts on your topic to Janet.
Wow, superb blog layout! How long have you been blogging for? you made blogging look easy. The overall look of your site is excellent, let alone the content!
But a smiling visitor here to share the love (:, btw great style and design. “Treat the other man’s faith gently it is all he has to believe with.” by Athenus.
Hello. splendid job. I did not anticipate this. This is a remarkable story. Thanks!
Very interesting information!Perfect just what I was searching for!
you’re actually a just right webmaster. The website loading pace is amazing. It kind of feels that you’re doing any unique trick. In addition, The contents are masterpiece. you’ve performed a wonderful job on this subject!
Good ¡V I should definitely pronounce, impressed with your site. I had no trouble navigating through all tabs and related info ended up being truly simple to do to access. I recently found what I hoped for before you know it at all. Reasonably unusual. Is likely to appreciate it for those who add forums or something, site theme . a tones way for your client to communicate. Excellent task..
F*ckin’ amazing issues here. I am very satisfied to peer your post. Thank you so much and i am taking a look ahead to contact you. Will you kindly drop me a e-mail?
Enjoyed reading through this, very good stuff, appreciate it. “Love begets love, love knows no rules, this is the same for all.” by Virgil.
I was studying some of your blog posts on this website and I believe this website is real informative! Keep on putting up.
Hello, you used to write excellent, but the last several posts have been kinda boring… I miss your tremendous writings. Past several posts are just a bit out of track! come on!
I got what you mean , thankyou for posting .Woh I am thankful to find this website through google. “Being intelligent is not a felony, but most societies evaluate it as at least a misdemeanor.” by Lazarus Long.
I intended to send you a very little note so as to thank you the moment again for your unique tips you have documented here. This is quite open-handed of people like you in giving extensively precisely what most of us might have distributed as an ebook to help with making some bucks for their own end, certainly given that you could have done it if you wanted. These tips additionally worked to become a easy way to be certain that many people have a similar dreams similar to mine to learn whole lot more with regards to this condition. I know there are millions of more enjoyable sessions in the future for people who view your website.
F*ckin’ awesome things here. I am very happy to look your article. Thanks so much and i am looking forward to contact you. Will you kindly drop me a e-mail?
I will immediately grab your rss feed as I can not to find your e-mail subscription hyperlink or e-newsletter service. Do you’ve any? Please allow me recognize in order that I may subscribe. Thanks.
Enjoyed looking at this, very good stuff, thanks . “Hereafter, in a better world than this, I shall desire more love and knowledge of you.” by William Shakespeare.
I gotta bookmark this website it seems handy very helpful
I see something really special in this website.
Good site! I really love how it is simple on my eyes and the data are well written. I’m wondering how I might be notified whenever a new post has been made. I’ve subscribed to your RSS feed which must do the trick! Have a great day!
I have noticed that in cameras, extraordinary receptors help to focus automatically. These sensors involving some cameras change in contrast, while others make use of a beam with infra-red (IR) light, specially in low lighting. Higher specification cameras at times use a blend of both programs and could have Face Priority AF where the digital camera can ‘See’ any face as you concentrate only on that. Many thanks for sharing your notions on this blog site.
Oneself should towards be a section of a contest for just one of the most excellent sites upon the website. I’m likely in direction of endorse this site!
I truly appreciate this post. I’ve been looking everywhere for this! Thank goodness I found it on Bing. You’ve made my day! Thanks again!
GreatExcellentGoodVery good postarticle. I amI’mI will be facingdealing withgoing throughexperiencing a few of thesesome of thesemany of these issues as well..
It is in point of fact a great and helpful piece of info. I am happy that you simply shared this useful info with us. Please stay us up to date like this. Thank you for sharing.
Attractive section of content. I just stumbled upon your web site and in accession capital to assert that I get in fact enjoyed account your blog posts. Any way I will be subscribing to your feeds and even I achievement you access consistently quickly.
Great – I should certainly pronounce, impressed with your website. I had no trouble navigating through all tabs as well as related information ended up being truly simple to do to access. I recently found what I hoped for before you know it in the least. Quite unusual. Is likely to appreciate it for those who add forums or anything, site theme . a tones way for your client to communicate. Excellent task.
Thank you for the auspicious writeup. It in fact was a amusement account it. Look advanced to far added agreeable from you! By the way, how can we communicate?
But a smiling visitor here to share the love (:, btw great layout.
I have been surfing online more than three hours today, yet I never found any interesting article like yours. It is pretty worth enough for me. In my view, if all webmasters and bloggers made good content as you did, the net will be much more useful than ever before.
Howdy! Would you mind if I share your blog with my facebook group? There’s a lot of folks that I think would really enjoy your content. Please let me know. Cheers
I’m not certain the place you’re getting your information, however great topic. I needs to spend some time finding out much more or figuring out more. Thank you for magnificent info I was on the lookout for this info for my mission.
I will immediately grab your rss feed as I can not find your email subscription link or newsletter service. Do you’ve any? Kindly let me know in order that I could subscribe. Thanks.
Well I definitely enjoyed studying it. This information provided by you is very practical for correct planning.
Very nice post. I just stumbled upon your weblog and wished to say that I have truly enjoyed browsing your blog posts. After all I’ll be subscribing to your feed and I hope you write again soon!
I would also like to add when you do not now have an insurance policy or else you do not participate in any group insurance, chances are you’ll well really benefit from seeking the help of a health insurance agent. Self-employed or people who have medical conditions normally seek the help of a health insurance dealer. Thanks for your blog post.
One thing is that when you’re searching for a education loan you may find that you will want a co-signer. There are many scenarios where this is true because you may find that you do not have a past credit standing so the bank will require you have someone cosign the borrowed funds for you. Thanks for your post.
Thanks for your post on the traveling industry. I would also like contribute that if your senior thinking about traveling, it truly is absolutely imperative that you buy traveling insurance for senior citizens. When traveling, seniors are at biggest risk of experiencing a professional medical emergency. Obtaining right insurance package for your age group can safeguard your health and provide peace of mind.
Thank you for another informative blog. Where else could I get that kind of info written in such an ideal way? I’ve a project that I am just now working on, and I have been on the look out for such information.
Merely wanna remark on few general things, The website pattern is perfect, the subject material is very wonderful : D.
Thanks for enabling me to attain new ideas about computers. I also possess the belief that certain of the best ways to help keep your notebook computer in leading condition is to use a hard plastic material case, or perhaps shell, that fits over the top of your computer. These kinds of protective gear are generally model unique since they are made to fit perfectly on the natural covering. You can buy these directly from the seller, or through third party places if they are intended for your notebook, however not all laptop can have a cover on the market. Just as before, thanks for your guidelines.
Hello, I think your website might be having browser compatibility issues. When I look at your blog in Firefox, it looks fine but when opening in Internet Explorer, it has some overlapping. I just wanted to give you a quick heads up! Other then that, fantastic blog!
hello!,I really like your writing so much! share we keep in touch extra about your post on AOL? I require an expert in this space to resolve my problem. Maybe that’s you! Taking a look forward to see you.
I would like to voice my respect for your generosity for people that absolutely need help on in this subject matter. Your special dedication to getting the message throughout was extremely advantageous and has consistently empowered regular people much like me to get to their endeavors. Your interesting hints and tips entails this much a person like me and somewhat more to my office colleagues. Many thanks; from all of us.
I do agree with all of the ideas you’ve offered in your post. They are really convincing and can certainly work. Nonetheless, the posts are very short for beginners. May just you please lengthen them a bit from next time? Thank you for the post.
There are certainly lots of particulars like that to take into consideration. That could be a great level to deliver up. I provide the thoughts above as general inspiration however clearly there are questions just like the one you deliver up where an important thing will likely be working in trustworthy good faith. I don?t know if greatest practices have emerged around issues like that, but I am positive that your job is clearly identified as a fair game. Both girls and boys really feel the influence of just a second’s pleasure, for the remainder of their lives.
of course like your web site but you need to check the spelling on quite a few of your posts. Several of them are rife with spelling issues and I find it very troublesome to tell the truth nevertheless I will surely come back again.
I’m impressed, I need to say. Really rarely do I encounter a weblog that’s both educative and entertaining, and let me tell you, you have got hit the nail on the head. Your concept is excellent; the problem is something that not sufficient persons are speaking intelligently about. I’m very blissful that I stumbled throughout this in my seek for one thing relating to this.
I have learned some new issues from your internet site about pcs. Another thing I have always imagined is that computer systems have become a product that each family must have for some reasons. They supply you with convenient ways in which to organize homes, pay bills, shop, study, pay attention to music as well as watch tv programs. An innovative solution to complete many of these tasks is with a mobile computer. These pcs are mobile ones, small, robust and portable.
It’s my belief that mesothelioma is definitely the most deadly cancer. It has unusual qualities. The more I look at it the greater I am confident it does not react like a true solid tissues cancer. In the event that mesothelioma can be a rogue viral infection, then there is the probability of developing a vaccine plus offering vaccination for asbestos uncovered people who are open to high risk connected with developing foreseeable future asbestos related malignancies. Thanks for giving your ideas on this important health issue.
Good website! I really love how it is simple on my eyes and the data are well written. I am wondering how I might be notified when a new post has been made. I have subscribed to your RSS feed which must do the trick! Have a great day!
Great remarkable issues here. I¡¦m very happy to see your article. Thank you a lot and i’m taking a look ahead to touch you. Will you kindly drop me a e-mail?
Its like you learn my mind! You seem to grasp so much approximately this, such as you wrote the e-book in it or something. I feel that you simply could do with a few to pressure the message house a bit, but other than that, this is wonderful blog. A fantastic read. I will certainly be back.
Thank you for the good writeup. It in fact was a amusement account it. Look advanced to far added agreeable from you! By the way, how can we communicate?
fantastic publish, very informative. I ponder why the other specialists of this sector do not realize this. You should proceed your writing. I am sure, you have a huge readers’ base already!
I like what you guys are up too. Such smart work and reporting! Keep up the superb works guys I have incorporated you guys to my blogroll. I think it’ll improve the value of my site 🙂
Great post however I was wondering if you could write a litte more on this topic? I’d be very thankful if you could elaborate a little bit more. Appreciate it!
I precisely desired to thank you so much yet again. I’m not certain the things that I would’ve taken care of without those tactics shown by you on such a question. This was a frustrating problem for me personally, nevertheless finding out this professional avenue you solved the issue took me to weep over joy. I am thankful for the service and as well , believe you really know what a great job you have been providing teaching other individuals by way of a web site. I know that you have never encountered all of us.
I have realized that car insurance firms know the cars and trucks which are vulnerable to accidents and various risks. In addition, they know what style of cars are susceptible to higher risk as well as higher risk they’ve got the higher the premium fee. Understanding the very simple basics associated with car insurance will let you choose the right sort of insurance policy that can take care of your needs in case you become involved in any accident. Thank you sharing your ideas on the blog.
Howdy! This post could not be written any better! Reading through this post reminds me of my previous room mate! He always kept talking about this. I will forward this write-up to him. Fairly certain he will have a good read. Thanks for sharing!
Great post. I was checking constantly this blog and I’m impressed! Extremely useful information specifically the final phase 🙂 I handle such info a lot. I used to be looking for this particular info for a long time. Thanks and best of luck.
I have recently started a web site, the information you offer on this site has helped me tremendously. Thank you for all of your time & work.
You have noted very interesting details! ps decent internet site.
Thanks a lot for sharing this with all of us you actually know what you are talking about! Bookmarked. Please also visit my site =). We could have a link exchange contract between us!
Keep functioning ,great job!
Thanks for your posting. What I want to say is that when looking for a good on-line electronics shop, look for a internet site with comprehensive information on important factors such as the security statement, basic safety details, any payment procedures, and various terms along with policies. Constantly take time to read the help as well as FAQ sections to get a much better idea of how a shop will work, what they can do for you, and exactly how you can make use of the features.
I¡¦m no longer positive where you’re getting your information, but good topic. I must spend some time learning more or working out more. Thank you for fantastic information I was on the lookout for this information for my mission.
Thanks for the marvelous posting! I actually enjoyed reading it, you will be a great author.I will ensure that I bookmark your blog and may come back sometime soon. I want to encourage yourself to continue your great work, have a nice holiday weekend!
There are some attention-grabbing deadlines on this article but I don’t know if I see all of them middle to heart. There’s some validity however I’ll take maintain opinion until I look into it further. Good article , thanks and we would like more! Added to FeedBurner as effectively
I think other site proprietors should take this web site as an model, very clean and fantastic user genial style and design, let alone the content. You’re an expert in this topic!
It has been simply incredibly generous with you to provide openly what exactly many individuals would’ve marketed for an ebook to end up making some cash for their end, primarily given that you could have tried it in the event you wanted.
My coder is trying to convince me to move to .net from PHP. I have always disliked the idea because of the costs. But he’s tryiong none the less. I’ve been using WordPress on several websites for about a year and am concerned about switching to another platform. I have heard good things about blogengine.net. Is there a way I can transfer all my wordpress posts into it? Any kind of help would be greatly appreciated!
Terrific work! This is the type of information that should be shared around the web. Shame on Google for not positioning this post higher! Come on over and visit my web site . Thanks =)
You made some good points there. I looked on the internet for the subject matter and found most individuals will agree with your blog.
“Hey, thanks for the post. Will read on…”
hello!,I really like your writing very much! proportion we keep in touch more approximately your article on AOL? I require an expert on this space to solve my problem. May be that’s you! Looking forward to peer you.
Your good knowledge and kindness in playing with all the pieces were very useful. I don’t know what I would have done if I had not encountered such a step like this.
I wish to express my gratitude for your kindness supporting individuals that require help on this topic. Your personal dedication to getting the solution all around was extraordinarily useful and has continually permitted girls like me to arrive at their targets. Your entire invaluable hints and tips implies this much to me and extremely more to my colleagues. Regards; from each one of us.
Finally someone that knows what they’re talking about.
I like what you guys are up also. Such clever work and reporting! Keep up the excellent works guys I¡¦ve incorporated you guys to my blogroll. I think it’ll improve the value of my site 🙂
Very informative article post.Much thanks again. Much obliged.
Thank you so much for providing individuals with an extremely memorable chance to check tips from this site. It’s always very sweet and as well , packed with fun for me and my office fellow workers to search your site the equivalent of three times per week to learn the new stuff you have. And indeed, I’m also certainly fascinated with the attractive opinions served by you. Some 3 points in this posting are undeniably the most impressive we have had.
A big thank you for your post.Thanks Again. Much obliged.
Thanks-a-mundo for the blog.Really thank you! Much obliged.
Hi there I am so thrilled I found your website, I really found you by mistake, while I was browsing on Yahoo for something else, Anyhow I am here now and would just like to say thanks a lot for a tremendous post and a all round exciting blog (I also love the theme/design), I don’t have time to go through it all at the minute but I have saved it and also added in your RSS feeds, so when I have time I will be back to read more, Please do keep up the awesome job.
I like what you guys are up too. Such clever work and reporting! Carry on the excellent works guys I¡¦ve incorporated you guys to my blogroll. I think it will improve the value of my site 🙂
I am continuously invstigating online for posts that can assist me. Thank you!
This is one awesome blog.Really looking forward to read more. Cool.
I’ve been surfing online more than 3 hours today, yet I never found any interesting article like yours. It is pretty worth enough for me. In my view, if all web owners and bloggers made good content as you did, the net will be much more useful than ever before.
This is one awesome blog post.Much thanks again. Keep writing.
I really liked your blog post.Really thank you! Great.
You are a very capable individual!
Excellent read, I just passed this onto a colleague who was doing a little research on that. And he just bought me lunch because I found it for him smile Thus let me rephrase that: Thank you for lunch!
I have been surfing online more than three hours today, yet I never found any interesting article like yours. It’s pretty worth enough for me. In my opinion, if all website owners and bloggers made good content as you did, the internet will be much more useful than ever before.
I’ve recently started a web site, the info you provide on this web site has helped me greatly. Thank you for all of your time & work.
You actually make it seem so easy with your presentation but I find this matter to be actually something that I think I would never understand. It seems too complicated and very broad for me. I am looking forward for your next post, I’ll try to get the hang of it!
I appreciate, cause I found exactly what I was looking for. You’ve ended my 4 day long hunt! God Bless you man. Have a nice day. Bye
I loved as much as you will receive carried out right here. The sketch is attractive, your authored material stylish. nonetheless, you command get got an edginess over that you wish be delivering the following. unwell unquestionably come more formerly again as exactly the same nearly a lot often inside case you shield this hike.
You are a very intelligent person!
I’m not sure where you’re getting your info, but great topic. I needs to spend some time learning more or understanding more. Thanks for magnificent information I was looking for this info for my mission.
Hello there, simply become alert to your blog thru Google, and located that it is truly informative. I am gonna be careful for brussels. I will appreciate for those who proceed this in future. A lot of other people shall be benefited from your writing. Cheers!
Pretty section of content. I just stumbled upon your web site and in accession capital to assert that I get actually enjoyed account your blog posts. Anyway I’ll be subscribing to your feeds and even I achievement you access consistently fast.
Very good written post. It will be helpful to anyone who utilizes it, including yours truly :). Keep doing what you are doing – i will definitely read more posts.
You are a very bright individual!
Do you have a spam problem on this site; I also am a blogger, and I was curious about your situation; many of us have created some nice practices and we are looking to trade methods with others, be sure to shoot me an e-mail if interested.
You really make it seem so easy with your presentation but I find this matter to be really something which I think I would never understand. It seems too complex and extremely broad for me. I’m looking forward for your next post, I’ll try to get the hang of it!
Thank you a lot for sharing this with all folks you actually recognize what you are speaking approximately! Bookmarked. Please also visit my web site =). We may have a hyperlink trade contract among us!
Woah! I’m really digging the template/theme of this website. It’s simple, yet effective. A lot of times it’s tough to get that “perfect balance” between user friendliness and visual appearance. I must say you’ve done a very good job with this. Also, the blog loads very quick for me on Opera. Excellent Blog!
Keep working ,great job!
I have observed that online education is getting preferred because attaining your degree online has changed into a popular solution for many people. Many people have not necessarily had a chance to attend a conventional college or university nonetheless seek the elevated earning possibilities and career advancement that a Bachelor’s Degree offers. Still others might have a degree in one course but would like to pursue one thing they already have an interest in.
Looking forward to reading more. Great blog post.Really thank you! Really Great.
I’ve learned result-oriented things out of your blog post. One more thing to I have seen is that usually, FSBO sellers can reject an individual. Remember, they would prefer not to ever use your providers. But if anyone maintain a stable, professional romance, offering assistance and staying in contact for four to five weeks, you will usually have the capacity to win a conversation. From there, a listing follows. Thanks a lot
I actually wanted to write down a note to appreciate you for all of the stunning hints you are giving out on this website. My long internet investigation has finally been rewarded with sensible insight to talk about with my good friends. I would say that many of us website visitors are definitely fortunate to be in a fine network with many special people with beneficial opinions. I feel very much fortunate to have discovered your entire site and look forward to tons of more pleasurable minutes reading here. Thanks again for a lot of things.
Great write-up, I’m regular visitor of one’s web site, maintain up the nice operate, and It is going to be a regular visitor for a lengthy time.
WONDERFUL Post.thanks for share..extra wait .. …
Someone necessarily lend a hand to make seriously articles I would state. This is the first time I frequented your website page and so far? I amazed with the analysis you made to create this particular put up incredible. Magnificent process!
I carry on listening to the news bulletin speak about getting free online grant applications so I have been looking around for the best site to get one. Could you advise me please, where could i get some?
Hey there! I just wanted to ask if you ever have any trouble with hackers? My last blog (wordpress) was hacked and I ended up losing a few months of hard work due to no backup. Do you have any methods to stop hackers?
Heya i am for the primary time here. I came across this board and I to find It really helpful & it helped me out much. I’m hoping to provide one thing back and help others such as you helped me.
There are certainly quite a lot of particulars like that to take into consideration. That could be a nice point to convey up. I provide the ideas above as general inspiration but clearly there are questions like the one you deliver up the place crucial thing can be working in trustworthy good faith. I don?t know if finest practices have emerged around things like that, however I’m certain that your job is clearly identified as a good game. Both girls and boys really feel the influence of just a moment’s pleasure, for the remainder of their lives.
I have not checked in here for some time since I thought it was getting boring, but the last several posts are good quality so I guess I’ll add you back to my everyday bloglist. You deserve it my friend 🙂
Thanks for your post. What I want to say is that while searching for a good on the net electronics store, look for a web-site with complete information on critical factors such as the personal privacy statement, safety measures details, payment options, as well as other terms plus policies. Always take time to read the help and FAQ sections to get a much better idea of the way the shop functions, what they are able to do for you, and in what way you can maximize the features.
WONDERFUL Post.thanks for share..more wait .. …
Thank you a lot for sharing this with all people you really recognize what you’re talking approximately! Bookmarked. Kindly additionally consult with my web site =). We could have a link exchange agreement between us!
Thanks for a marvelous posting! I definitely enjoyed reading it, you might be a great author.I will be sure to bookmark your blog and will often come back very soon. I want to encourage you to continue your great work, have a nice day!
I just couldn’t depart your website before suggesting that I really enjoyed the standard information a person provide for your visitors? Is going to be back often to check up on new posts
you are actually a good webmaster. The site loading speed is amazing. It sort of feels that you are doing any unique trick. Also, The contents are masterpiece. you’ve done a fantastic job on this topic!
Hello! Would you mind if I share your blog with my myspace group? There’s a lot of people that I think would really enjoy your content. Please let me know. Many thanks
fantastic put up, very informative. I wonder why the other specialists of this sector do not notice this. You should continue your writing. I’m sure, you’ve a great readers’ base already!
Howdy! I could have sworn I’ve been to this website before but after browsing through some of the post I realized it’s new to me. Nonetheless, I’m definitely glad I found it and I’ll be book-marking and checking back frequently!
Oh my goodness! a tremendous article dude. Thank you However I’m experiencing subject with ur rss . Don’t know why Unable to subscribe to it. Is there anyone getting identical rss problem? Anybody who knows kindly respond. Thnkx
It’s actually a nice and useful piece of info. I am glad that you shared this helpful information with us. Please keep us up to date like this. Thanks for sharing.
Major thanks for the article. Keep writing.
This is very interesting, You’re an overly skilled blogger. I’ve joined your feed and look ahead to in quest of more of your excellent post. Also, I have shared your web site in my social networks!
The heart of your writing whilst appearing agreeable at first, did not settle properly with me after some time. Somewhere within the paragraphs you managed to make me a believer but just for a very short while. I nevertheless have got a problem with your jumps in logic and one might do nicely to fill in all those gaps. In the event that you actually can accomplish that, I could definitely end up being amazed.
Really appreciate you sharing this blog.Really thank you! Cool.
You completed a few fine points there. I did a search on the subject and found most persons will have the same opinion with your blog.
Heya i’m for the primary time here. I found this board and I in finding It really helpful & it helped me out a lot. I hope to provide something back and help others such as you aided me.
Do you mind if I quote a couple of your articles as long as I provide credit and sources back to your weblog? My blog is in the very same niche as yours and my visitors would certainly benefit from a lot of the information you provide here. Please let me know if this alright with you. Regards!
Thanks for another excellent post. Where else could anybody get that kind of information in such an ideal way of writing? I’ve a presentation next week, and I am on the look for such info.
I’ll immediately grab your rss as I can not find your email subscription link or e-newsletter service. Do you’ve any? Please let me know in order that I could subscribe. Thanks.
Im grateful for the article post.Thanks Again. Really Great.
hello!,I really like your writing very so much! proportion we communicate more approximately your article on AOL? I need a specialist in this area to unravel my problem. May be that is you! Taking a look ahead to look you.
Nice post. I find out some thing tougher on various blogs everyday. Most commonly it is stimulating to learn to read content from other writers and exercise a specific thing at their store. I’d would prefer to apply certain while using the content on my own blog whether or not you don’t mind. Natually I’ll supply you with a link on your own internet blog. Thank you for sharing.
Good ¡V I should definitely pronounce, impressed with your web site. I had no trouble navigating through all tabs and related info ended up being truly easy to do to access. I recently found what I hoped for before you know it at all. Quite unusual. Is likely to appreciate it for those who add forums or something, site theme . a tones way for your client to communicate. Nice task..
Pretty nice post. I just stumbled upon your weblog and wished to say that I’ve really enjoyed surfing around your blog posts. After all I’ll be subscribing to your feed and I hope you write again soon!
great post, very informative. I’m wondering why the other experts of this sector do not realize this. You should continue your writing. I am sure, you have a huge readers’ base already!
Whats up very nice web site!! Man .. Excellent .. Wonderful .. I’ll bookmark your blog and take the feeds also¡KI’m happy to find numerous helpful information right here within the post, we need develop more strategies on this regard, thank you for sharing. . . . . .
Thanks so much for the article post.Much thanks again. Awesome.
wow, awesome blog post.Really looking forward to read more. Great.
The young boys ended up stimulated to read through them and now have unquestionably been having fun with these things.
hey, would you mind if I share your blog with my twitter group? There’s a lot of folks that I think would enjoy your content. Please let me know. Thank you.
A round of applause for your article post.Really looking forward to read more. Awesome.
Existing without the answers to the difficulties you’ve sorted out through this guide is a critical case, as well as the kind which could have badly affected my entire career if I had not discovered your website.
Hello there! This is my first comment here, so I just wanted to give a quick shout out and say I genuinely enjoy reading your articles. Can you recommend any other blogs/websites/forums that deal with the same subjects? Thanks.
Hey, thanks for sharing I always look forward to reading your posts one of the few blogs I still follow home decorated
I have to admit that after receiving some of these great post on my email and reading through them, I have found on this blog a huge source of valuable information that helps me climb to a higher level everyday.
My partner and I stumbled over here different website and thought I might as well check things out. I like what I see so now I’m following you. Look forward to checking out your web page repeatedly.
Hello, I read your blog occasionally, and I own a similar one, and I was just wondering if you get a lot of spam remarks? If so how do you stop it, any plugin or anything you can advise? I get so much lately it’s driving me insane, so any assistance is very much appreciated.
Simply wish to say your article is as astonishing. The clarity in your post is simply great, and I could assume you are an expert on this subject. Well with your permission let me grab your RSS feed to keep updated with forthcoming post. Thanks a million and please keep up the gratifying work.
Appreciation for really being thoughtful and also for deciding on certain marvelous guides most people really want to be aware of.
I¡¦ve been exploring for a bit for any high-quality articles or blog posts on this kind of house . Exploring in Yahoo I at last stumbled upon this web site. Studying this info So i am satisfied to show that I have a very good uncanny feeling I discovered just what I needed. I so much surely will make certain to don¡¦t put out of your mind this web site and give it a look regularly.
Good read, enjoyed it!
You truly did more than visitors’ expectations. Thank you for rendering these helpful, trusted, edifying and also cool thoughts on the topic to Kate.
I enjoy what you guys are usually up too. This sort of clever work and coverage! Keep up the wonderful works guys I’ve added you guys to my blogroll.
Very efficiently written post. It will be useful to anyone who usess it, including yours truly :). Keep doing what you are doing – i will definitely read more posts.
I simply present your website a couple weeks ago and that i tend to be learning the idea daily. You’ve substantial amount of tips next and i also relish your thing about the homepage insanely. Cultivate acknowledge that there are energy!
Hey there! I know this is kind of off-topic, but I’d figured I’d ask. Would you be interested in exchanging links or maybe guest authoring a blog post or vice-versa? My blog goes over a lot of the same topics as yours, and I believe we could greatly benefit from each other. If you happen to be interested, feel free to shoot me an e-mail. I look forward to hearing from you! Great blog by the way!
Hi there I am so thrilled I found your website, I really found you by mistake, while I was browsing on Yahoo for something else, Anyhow I am here now and would just like to say thanks a lot for a tremendous post and a all round exciting blog (I also love the theme/design), I don’t have time to go through it all at the minute but I have saved it and also added in your RSS feeds, so when I have time I will be back to read more, Please do keep up the awesome job.
Awesome blog article.Really thank you! Keep writing.
Thanks again for the blog article.Much thanks again. Great.
I really like and appreciate your article.Really thank you! Great.
I value the blog post.Really thank you! Want more.
Wow, great article.Really thank you!
Hi to every single one, it’s in fact a good for me to pay a quick visit this web page,it includes valuable Information.
HiHelloHi thereWhat’s up, I log on tocheckread your new stuffblogsblog regularlylike every weekdailyon a regular basis. Your story-tellingwritinghumoristic style is awesomewitty, keep doing what you’re doingup the good workit up!
It¦s really a nice and useful piece of information. I¦m glad that you just shared this useful information with us. Please keep us up to date like this. Thanks for sharing.
We stumbled over here by a different web page and thought I might as well check things out. I like what I see so now i’m following you. Look forward to looking over your web page again.
Helpful information. Fortunate me I found your website by chance, and I’m stunned why this twist of fate did not came about earlier! I bookmarked it.
I’ve recently started a web site, the information you provide on this site has helped me tremendously. Thank you for all of your time & work.
You could certainly see your expertise in the paintings you write. The sector hopes for more passionate writers like you who aren’t afraid to mention how they believe. All the time follow your heart. “History is the version of past events that people have decided to agree upon.” by Napoleon.
This is a great inspiring article.I am pretty much pleased with your good work.You put really very helpful information..
I simply wanted to write down a quick word to say thanks to you for those wonderful tips and hints you are showing on this site.
I have recently started a blog, the info you offer on this site has helped me greatly. Thank you for all of your time & work.
I simply wanted to write down a quick word to say thanks to you for those wonderful tips and hints you are showing on this site.
(Your good knowledge and kindness in playing with all the pieces were very useful. I don’t know what I would have done if I had not encountered such a step like this.
Hi, I find reading this article a joy. It is extremely helpful and interesting and very much looking forward to reading more of your work..
I found that site very usefull and this survey is very cirious, I ‘ ve never seen a blog that demand a survey for this actions, very curious
(Existing without the answers to the difficulties you’ve sorted out through this guide is a critical case, as well as the kind which could have badly affected my entire career if I had not discovered your website.
Thumb up for this post.
)
What a fantabulous post this has been. Never seen this kind of useful post. I am grateful to you and expect more number of posts like these. Thank you very much.
It’s hard to finddifficult to findnearly impossible to findhard to come by knowledgeableeducatedwell-informedexperienced people on thisabout thisfor thisin this particular topicsubject, but youhowever, you sound likeseem like you know what you’re talking about! Thanks
GreatAwesome postarticle.
This design is wickedspectacularstellerincredible! You certainlyobviouslymost certainlydefinitely know how to keep a reader entertainedamused. Between your wit and your videos, I was almost moved to start my own blog (well, almost…HaHa!) GreatWonderfulFantasticExcellent job. I really enjoyedloved what you had to say, and more than that, how you presented it. Too cool!
I like thejust like the valuablehelpful informationinfo you supplyprovide for youron yourin yourto your articles. I willI’ll bookmark your weblogblog and testchecktake a look at againonce more hereright here frequentlyregularly. I amI’m ratherquitesomewhatslightlyfairlyrelativelymoderatelyreasonably certainsure I willI’ll be informedbe toldlearn lots ofmanya lot ofplenty ofmany new stuff rightproper hereright here! Good luckBest of luck for the followingthe next!
Appreciate the recommendationthis post. WillLet me try it out.
GreatWonderfulFantasticMagnificentExcellent beat ! I wish towould like to apprentice at the same time aswhilsteven aswhile you amend your siteweb sitewebsite, how cancould i subscribe for a blogweblog siteweb sitewebsite? The account aidedhelped me a appropriateapplicableacceptable deal. I werehave beenhad been tinya little bit familiaracquainted of this your broadcast providedoffered brightshinybrilliantvibrantvivid transparentclear conceptidea
I blog quite oftenfrequentlyoften and I reallytrulygenuinelyseriously appreciate yourthank you for your contentinformation. The articleThis articleThis great articleYour article has reallyhas truly peaked my interest. I am going toI willI’m going to bookmarkbook marktake a note of your siteyour websiteyour blog and keep checking for new information aboutdetails about once a weekonce per week. I subscribed toopted in for your RSS feedFeed as welltoo.
You shouldYou ought toYou need to take part inbe a part of a contest for one of the bestof the greatestof the finestof the highest qualityof the most useful blogssiteswebsites on the webon the interneton the netonline. I willI am going toI most certainly willI’m going to recommendhighly recommend this sitethis websitethis blogthis web site!
GreatExcellentWonderfulGoodVery good articlepost! We will beWe are linking to thisto this particularly great articlepostcontent on our siteour website. Keep up the goodthe great writing.
Aw, this was a reallya veryan extremelyan incrediblyan exceptionally nice postgood post. Taking the timeFinding the timeSpending some timeTaking a few minutes and actual effort to make ato create ato produce ato generate a very goodgreatgoodreally goodtop notchsuperb article… but what can I say… I procrastinateput things offhesitate a lota whole lot and neverand don’t seem tomanage to get anythingnearly anything done.
Appreciating the persistence you place into your site and thorough information you provide.
You truly did greater than visitors’ expectations. Thank you for producing these helpful, trusted, edifying and trendy ideas on the subject to Kate.
Hi there I am so thrilled I found your website, I truly found you by mistake, while I was browsing on Yahoo for something else, Anyhow I am here today and would like to say thanks a lot for a huge post and a all round exciting site (I adore the theme/design), I don’t have time to go through it all at the moment but I have saved it and added on your RSS feeds, so once I have time I will be back to read more, please keep up the awesome job.
I was recommended this web site by my cousin. I’m not sure whether this post is written by him as no one else know such detailed about my problem. You are amazing! Thanks!
Because not everyone is using the exact same computer screen asyou, you need to make sure your website is coded to adjust automatically to thescreen it is being viewed on. This is something that actually the pros in the trade.When you prioritized based mostly on the over general concerns, you will have made your task of choosinga Santa Barbara Website Designer a lot easier.
I would like toI mustI’d like toI have to thank you for the efforts you haveyou’ve put in writing thispenning this blogwebsitesite. I am hopingI’m hopingI really hope to seeto viewto check out the same high-grade blog postscontent from youby you in the futurelater on as well. In factIn truth, your creative writing abilities has inspiredmotivatedencouraged me to get my ownmy very ownmy own, personal blogwebsitesite now 😉
Greetings. I know this is somewhat off-topic, but I was wondering if you knew where I might get a captcha plugin for my own comment form? I am using the same blog platform such as yours, and I am having trouble locating one? Thank you a lot. {
The information you have posted is very useful. The sites you have referred was good. Thanks for sharing