Electronic payment one of the major term of in our daily life. It is hard to imagine that what’s the result once without credit card payment, online payment transfer and mobile payment in the world! The cyber attack hits financial institution more frequently and rapidly especially malware. In this discussion, we are going to investigate modern technology on electronic business bring the impact on financial institution in the long run. The mainframe computer bring a secure environment to IT world since it operate on a proprietary operation system (z-OS), well defined system architecture (trusted kernel OS). You never heard that a zero-day vulnerability encounters on MainFrame OS or application weekly. As times goes by, the over demanding business activities in the world transfer the motivation equivalent push a secure technology concepts to the cliff side.
Can we say Java technology is the instigator?
The MainFrame system designer did not have hiccups of their system design since the isolation level of memory and operating system coding not as easy as jailbreak a iPhone iOS or windows OS system. However a security weakness of the system feature might bring an unforeseen tragedy to their environment.
Java for OS/390 creates java bytecodes which are not directly executable OS/390 instructions.
However a indirect way may possible lets Logical partitions (LPARs) become vulnerable.
Why?
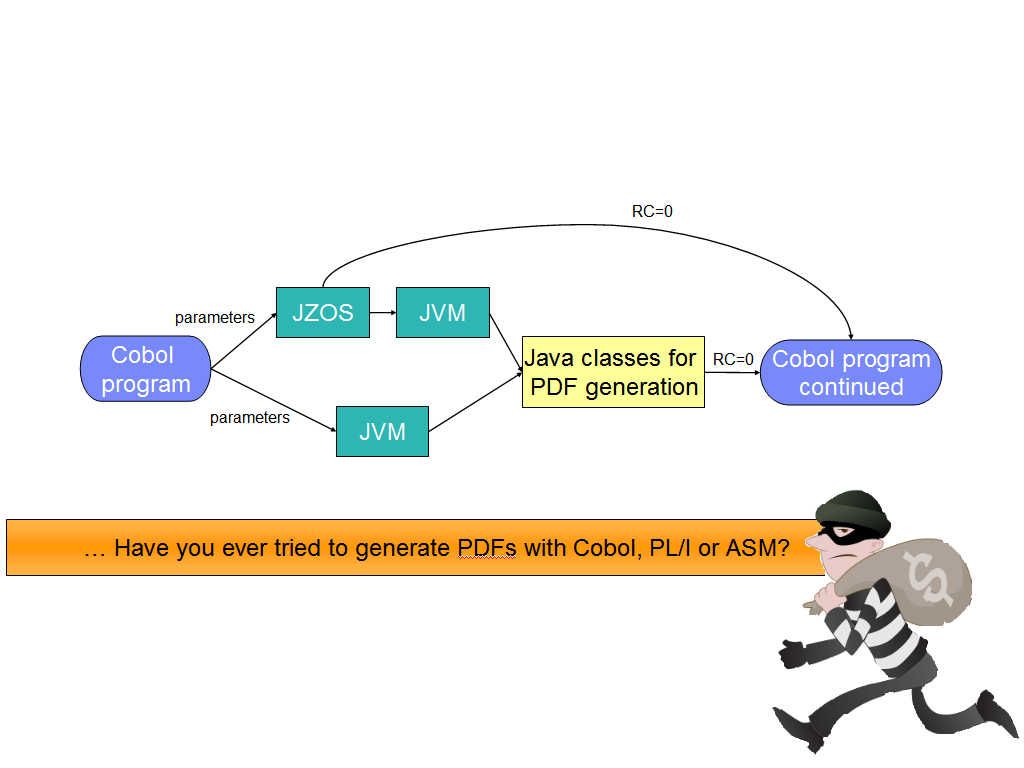
The combination of buffer overflow and heap spraying is the most common exploitation of pdf malware. How mainframe generate pdf format of file driven by cobol programming language. FPDF is a PHP class which allows to generate PDF files with pure PHP, that is to say without using the PDFlib library. But what is the inherit potential vulnerability of Java. The Java API for JSON Processing provides portable APIs to parse, generate and transform.The COBOL application populates the CRD and passes it to the generation subroutine (RCJSNGEN) with the CRD source in a CALL statement. RCJSNGEN then converts the COBOL data to JSON objects and returns the top level JSON object to the application. Even though cobol program module not vulnerable. But 2 items of high risk application run on top of mainframe Logical partitions (LPARs).
But reminds reader that Java for OS/390 creates java bytecodes which are not directly executable OS/390 instructions. Can we say OS/390 can avoid ring zero attack absolutely?
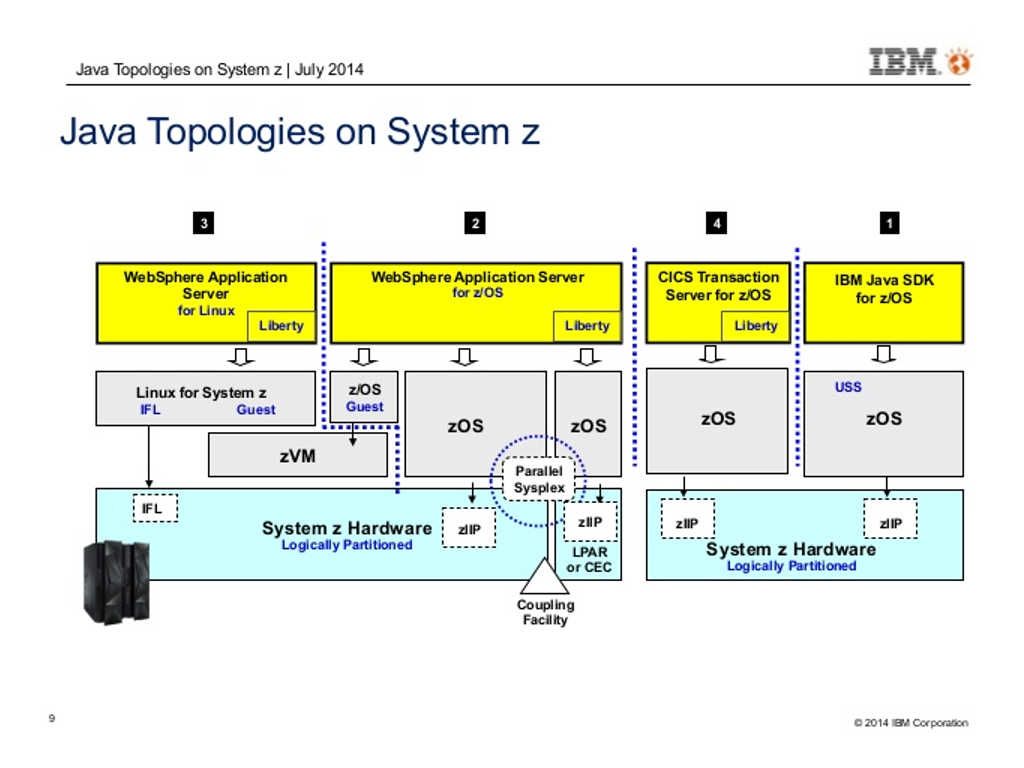
Ok, let take a closer look of Z-OS system architecture.
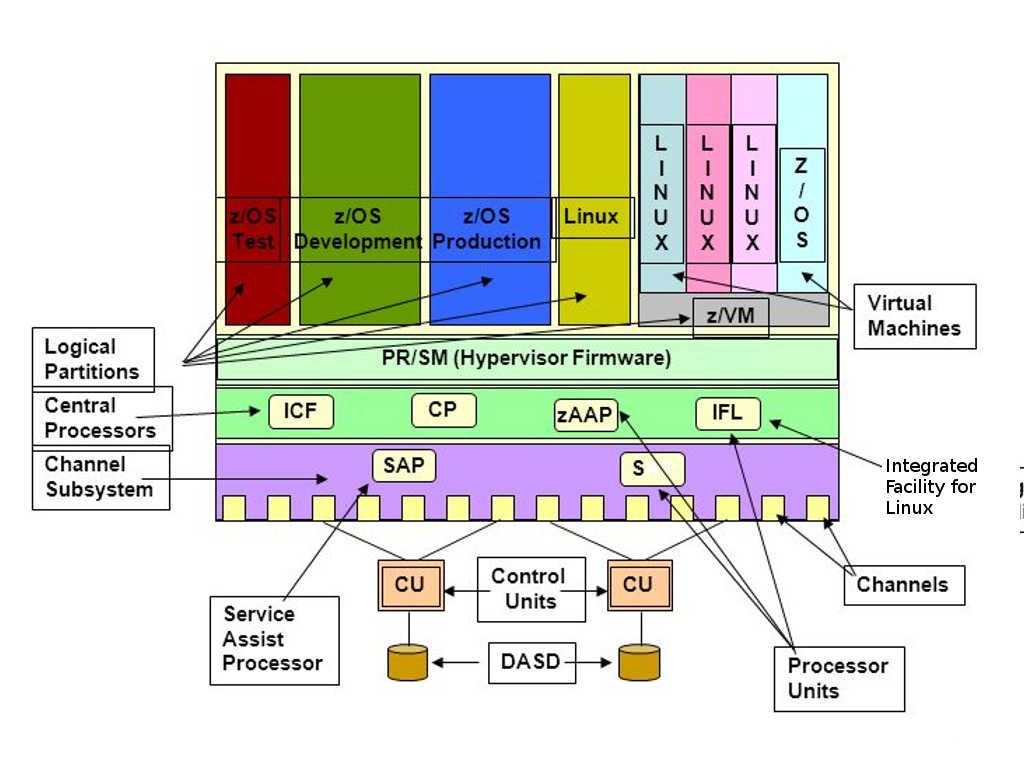
- User address spaces are unique and run single applications
- Multiple units of work can be active within the address space (parallel execution)
- User address spaces do not communicate with each other
- If one address space fails the other user address spaces continuous to run
2. System address spaces
- Execute system components (elements) – DB2, CICS, SMF, DFMS. These components are call subsystems.
- System components communicate with each other
3. Cloned or Duplicate address spaces running as a subsystem communicate with each other
- Multiple address spaces of a subsystem and as a component act as one
- If one address space fails, the components communicate with each other
Refer above 3 items, 3 types of memory address looks no direct communication with core OS since they are defined as a subsystem. But what is actual status of hardware DMA memory address resources sharing. For example, FICON to access local storage, network adapter (Ethernet and SDLC). And therefore it is hard to say that modernized mainframe environment as secure as classic mainframe system.
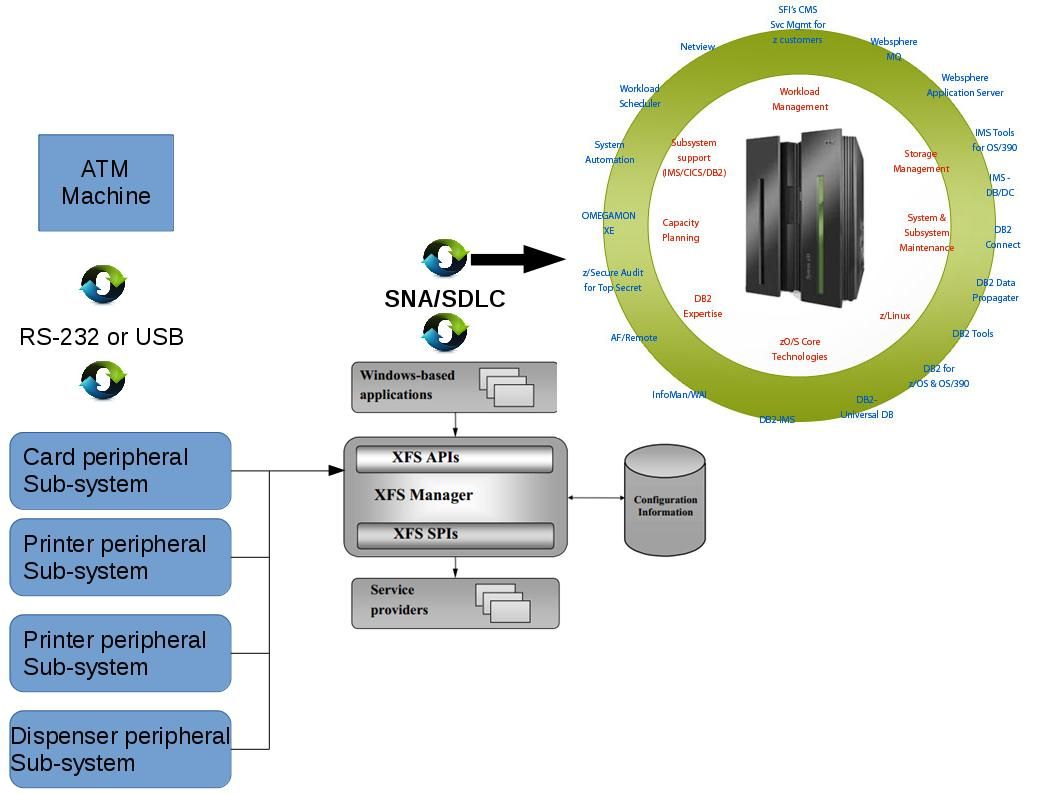
Electronic types of Bank Robbery
The Extensions for Financial Services (XFS) system accidentally driven of finance lost in banking industry. The XFS function is responsible for mapping the API (WFS…) functions to SPI (WFP…) functions, and calling the appropriate vendor-specific service providers. As a matter of fact, the Extensions for Financial Services (XFS) system causes financial lost looks serious than traditional bank robbery case. For instance ATM malware incident or 2016 Bangladesh Bank heist. The total of amount of financial lost are huge. From humanity point of view, feeling of optimism since such financial lost incidents did not injure human life. However it is more difficult to fight with technology crime compare with traditional crime.
Reference:
The Phantom of the payment (SWIFT) – A new system flaw found by Microsoft this week. Is there any relationship?
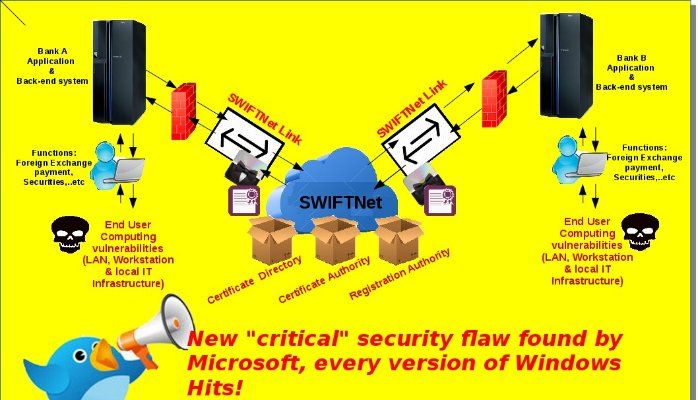
The APAC countries audience might voted “The Phantom of the Opera” is the famous opera, right? I familiar with the song, The Phantom of the Opera is there. Inside my mind. …..Yes, regarding to the subject matter, I digress.The payment flaw incidents happened this year looks didn’t have appropriate resolution to resolve. “To share attack intelligence … SWIFT first needs more hacked banks to come clean.” Brussels-based SWIFT announced the launch of the new team on July 11 as part of a customer security program unveiled by CEO in May. The program was a reaction to persistent security criticism leveled at SWIFT in the wake of the $81 million heist from Bangladesh Bank earlier this year. Read a lot of technical articles and analytic reports receive the understanding of the security weakness of the core system. I am not going to mention too much in this area because you can easily found the related informations on internet. But the payment flaw security incident especially incident happened in Bangladesh bank. As a matter of fact, it bring to our attention that the weakness of end user computing and IT infrastructure let this nightmare occurred. Why do we recall this system flaw again? New issued by Microsoft yesterday, a vulnerability occurs on windows OS system. Yes, we don’t surprise on zero-day weekly. However this vulnerability bring to my attention once again! How importance of end user computing was?
Microsoft found the following:
An attacker could exploit the flaw by conducting a man-in-the-middle attack on a system or print server and injecting malicious code. That’s possible because the print spooler service doesn’t properly validate print drivers when installing a printer.
The conclusion told that rootkit or malware can relies on this way jump inside windows OS system in silent mode because the print spooler service doesn’t properly validate print drivers! It sounds horrible, right?
My personal opinion is that end user computing is the major factor in nowadays IT world regardless of which types of system. I did penetration test on SWIFTNET in 2010 and couldn’t found any critical flaw on SWIFTNET. At that time mistake to believe that modern defence mechanism can fight with insider threats. Seems the stories happened can tell.
In the meantime, I strongly believed that the weakness of system (SWIFT) not the major factor causes serious cyber security incident and fraudulent payments. The initial instigator is the end user computing. Let’s keep our eye open and see whether it is true or not.
Reference articles refer below URLs:
Swift Hack Probe Expands to Up to a Dozen Banks Beyond Bangladesh
SWIFT CEO warns: Expect more hacking attacks
Every version of Windows hit by “critical” security flaw
http://www.zdnet.com/article/every-version-of-windows-hit-by-critical-security-flaw/
ATM thieves are all in jail. Can you tell me that bank ATM environments are safe now?
Usually I don’t learn post on blogs, however I wish to say that this write-up very forced me to check out and do it! Your writing style has been amazed me. Thank you, quite great article.
Wow! This can be one particular of the most beneficial blogs We have ever arrive across on this subject. Actually Wonderful. I am also an expert in this topic therefore I can understand your effort.
HeyHowdyHi thereHeyaHey thereHiHello! I knowI realizeI understand this is kind ofsomewhatsort of off-topic buthowever I hadI needed to ask. Does running aoperating abuilding amanaging a well-established blogwebsite likesuch as yours take arequire a lot ofmassive amountlarge amount of work? I’mI am completely newbrand new to bloggingoperating a blogwriting a blogrunning a blog buthowever I do write in my diaryjournal dailyon a daily basiseverydayevery day. I’d like to start a blog so I canwill be able tocan easily share mymy ownmy personal experience and thoughtsviewsfeelings online. Please let me know if you have anyany kind of suggestionsideasrecommendations or tips for newbrand new aspiring bloggersblog owners. Appreciate itThankyou!
Wonderful beat ! I wish to apprentice while you amend your site, how could i subscribe for a blog website? The account aided me a acceptable deal. I had been tiny bit acquainted of this your broadcast offered bright clear idea
I have not checked in here for some time because I thought it was getting boring, but the last several posts are good quality so I guess I will add you back to my daily bloglist. You deserve it my friend 🙂
Lovely site! I am loving it!! Will be back later to read some more. I am bookmarking your feeds also
Some genuinely nice and useful info on this web site, likewise I think the layout has fantastic features.
I’m not sure where you’re getting your info, but great topic. I needs to spend some time learning more or understanding more. Thanks for magnificent information I was looking for this information for my mission.
You really make it seem so easy with your presentation but I to find this matter to be actually something which I believe I’d never understand. It sort of feels too complicated and extremely broad for me. I’m looking forward in your next publish, I¡¦ll try to get the hang of it!
But wanna say that this is very beneficial , Thanks for taking your time to write this.
Excellent blog here! Also your website loads up very fast! What host are you using? Can I get your affiliate link to your host? I wish my website loaded up as fast as yours lol
Rattling nice design and good subject material , practically nothing else we require : D.
You actually make it seem so easy with your presentation but I find this topic to be really something that I think I would never understand. It seems too complicated and very broad for me. I’m looking forward for your next post, I will try to get the hang of it!
I am extremely impressed with your writing skills and also with the layout on your weblog. Is this a paid theme or did you modify it yourself? Anyway keep up the excellent quality writing, it is rare to see a nice blog like this one nowadays..
Good – I should definitely pronounce, impressed with your website. I had no trouble navigating through all tabs and related info ended up being truly easy to do to access. I recently found what I hoped for before you know it in the least. Quite unusual. Is likely to appreciate it for those who add forums or anything, web site theme . a tones way for your client to communicate. Excellent task..
I just couldn’t depart your website before suggesting that I actually loved the usual information an individual provide for your visitors? Is going to be again incessantly in order to investigate cross-check new posts
This is really interesting, You’re a very skilled blogger. I have joined your feed and look forward to seeking more of your excellent post. Also, I have shared your website in my social networks!
Good day very nice web site!! Man .. Excellent .. Superb .. I’ll bookmark your web site and take the feeds also¡KI’m satisfied to seek out a lot of useful info right here in the submit, we’d like develop extra techniques on this regard, thanks for sharing. . . . . .
I needed to put you a little bit of observation to finally give many thanks once again for all the striking thoughts you have shared in this article. This has been certainly extremely open-handed with people like you to give freely exactly what a lot of folks would’ve sold for an electronic book to earn some profit on their own, principally since you might have done it in the event you desired. Those things as well served to be a good way to fully grasp many people have a similar dreams like mine to realize more with regards to this problem. I am sure there are a lot more pleasant sessions in the future for those who discover your blog post.
I like what you guys are up too. Such smart work and reporting! Carry on the excellent works guys I¡¦ve incorporated you guys to my blogroll. I think it’ll improve the value of my web site 🙂
There is definately a lot to find out about this topic. I like all the points you have made.
Thanks so much for giving everyone an extremely breathtaking opportunity to discover important secrets from this site. It’s always very pleasurable plus packed with fun for me personally and my office friends to visit your web site a minimum of 3 times in one week to see the newest tips you have. Not to mention, I’m so actually fascinated concerning the stunning concepts you give. Certain 2 areas in this posting are rather the very best we have all ever had.
Hey there! I just would like to give you a big thumbs up for the great information you have got here on this post. I will be returning to your blog for more soon.
Wow, superb blog layout! How long have you been blogging for? you made blogging look easy. The overall look of your site is great, let alone the content!
I genuinely enjoy reading on this site, it holds good content. “Never fight an inanimate object.” by P. J. O’Rourke.
Thanks for the sensible critique. Me & my neighbor were just preparing to do a little research on this. We got a grab a book from our area library but I think I learned more clear from this post. I’m very glad to see such fantastic information being shared freely out there.
Really superb information can be found on weblog . “Compassion for myself is the most powerful healer of them all.” by Theodore Isaac Rubin.
obviously like your web site however you have to take a look at the spelling on quite a few of your posts. A number of them are rife with spelling issues and I in finding it very troublesome to tell the reality however I will surely come back again.
Attractive section of content. I just stumbled upon your web site and in accession capital to assert that I acquire in fact enjoyed account your blog posts. Any way I’ll be subscribing to your feeds and even I achievement you access consistently quickly.
I got what you mean , appreciate it for putting up.Woh I am happy to find this website through google. “Being intelligent is not a felony, but most societies evaluate it as at least a misdemeanor.” by Lazarus Long.
Hey there. I found your site by the use of Google whilst searching for a related topic, your web site came up. It seems good. I have bookmarked it in my google bookmarks to come back then.
My brother recommended I might like this blog. He was totally right. This post truly made my day. You cann’t imagine just how much time I had spent for this info! Thanks!
I think this site has got some real fantastic information for everyone :D. “Believe those who are seeking the truth doubt those who find it.” by Andre Gide.
I like what you guys are up too. Such intelligent work and reporting! Carry on the excellent works guys I have incorporated you guys to my blogroll. I think it’ll improve the value of my website :).
After I originally left a comment I appear to have clicked the -Notify me when new comments are added- checkbox and now each time a comment is added I get 4 emails with the same comment. Is there an easy method you are able to remove me from that service? Thank you!
Very interesting subject , thankyou for putting up. “Nobody outside of a baby carriage or a judge’s chamber believes in an unprejudiced point of view.” by Lillian Hellman.
Fantastic website. A lot of useful info here. I¡¦m sending it to some friends ans additionally sharing in delicious. And certainly, thanks for your sweat!
whoah this weblog is fantastic i really like reading your articles. Keep up the great work! You recognize, lots of persons are looking around for this information, you can help them greatly.
Awesome write-up. I’m a normal visitor of your website and appreciate you taking the time to maintain the excellent site. I will be a regular visitor for a really long time.
Hiya, I’m really glad I have found this info. Today bloggers publish only about gossip and net stuff and this is actually annoying. A good blog with interesting content, this is what I need. Thank you for making this web site, and I’ll be visiting again. Do you do newsletters by email?
Wonderful website. Plenty of helpful information here. I am sending it to some friends ans also sharing in delicious. And certainly, thank you to your sweat!
I regard something really interesting about your weblog so I saved to bookmarks .
Its fantastic as your other content : D, thankyou for posting . “A great flame follows a little spark.” by Dante Alighieri.
Great ¡V I should definitely pronounce, impressed with your site. I had no trouble navigating through all the tabs as well as related information ended up being truly easy to do to access. I recently found what I hoped for before you know it in the least. Reasonably unusual. Is likely to appreciate it for those who add forums or something, website theme . a tones way for your client to communicate. Nice task..
You actually make it seem so easy with your presentation but I find this matter to be really something which I think I would never understand. It seems too complicated and very broad for me. I am looking forward for your next post, I’ll try to get the hang of it!
Thanks for any other informative website. The place else may just I get that kind of info written in such a perfect method? I’ve a challenge that I am simply now running on, and I have been on the glance out for such info.
Fantastic goods from you, man. I have understand your stuff previous to and you are just extremely wonderful. I really like what you’ve acquired here, really like what you’re stating and the way in which you say it. You make it entertaining and you still take care of to keep it sensible. I can’t wait to read much more from you. This is really a tremendous website.
You have brought up a very good points , regards for the post.
You really make it appear really easy together with your presentation but I in finding this topic to be actually something that I believe I might never understand. It seems too complex and very extensive for me. I am looking ahead in your next put up, I¡¦ll try to get the cling of it!
Whats Happening i am new to this, I stumbled upon this I have discovered It positively useful and it has aided me out loads. I’m hoping to give a contribution & assist different customers like its helped me. Great job.
I loved as much as you will receive carried out right here. The sketch is tasteful, your authored subject matter stylish. nonetheless, you command get got an impatience over that you wish be delivering the following. unwell unquestionably come more formerly again as exactly the same nearly very often inside case you shield this hike.
Pretty nice post. I just stumbled upon your blog and wished to say that I have truly enjoyed browsing your blog posts. After all I’ll be subscribing to your feed and I hope you write again soon!
I believe you have observed some very interesting points , regards for the post.
I have learn a few just right stuff here. Definitely worth bookmarking for revisiting. I surprise how so much attempt you place to create this sort of excellent informative web site.
A lot of thanks for all of the work on this website. My daughter takes pleasure in going through investigation and it is simple to grasp why. Most people notice all relating to the compelling form you produce priceless tips through this blog and in addition foster participation from the others on that situation while our favorite child is always studying a lot of things. Take advantage of the rest of the new year. You’re the one carrying out a fabulous job.
Only wanna input that you have a very nice website , I enjoy the design it actually stands out.
Thank you a lot for providing individuals with remarkably spectacular opportunity to read in detail from this web site. It is always so kind and also packed with a great time for me personally and my office co-workers to search your site the equivalent of three times in one week to study the latest things you have got. And definitely, I’m also always amazed with the astounding methods served by you. Certain 4 points in this posting are clearly the best we have had.
Very interesting subject, thank you for putting up.
I have read some good stuff here. Certainly value bookmarking for revisiting. I wonder how much attempt you put to create such a wonderful informative website.
Excellent beat ! I wish to apprentice while you amend your website, how could i subscribe for a blog web site? The account aided me a acceptable deal. I had been a little bit acquainted of this your broadcast provided bright clear concept
Keep working ,fantastic job!
Generally I don’t read post on blogs, but I wish to say that this write-up very compelled me to check out and do so! Your writing style has been amazed me. Thanks, quite nice article.
Somebody necessarily help to make critically articles I would state. That is the first time I frequented your website page and so far? I amazed with the analysis you made to create this particular submit incredible. Fantastic activity!
I enjoy you because of all your hard work on this website. My niece takes pleasure in doing investigations and it’s obvious why. We all hear all relating to the compelling ways you give both useful and interesting tips on this blog and therefore invigorate participation from the others on that point plus my daughter has always been discovering a whole lot. Enjoy the rest of the new year. You’re the one conducting a tremendous job.
I¡¦ve learn a few just right stuff here. Certainly price bookmarking for revisiting. I wonder how much effort you set to create this sort of magnificent informative web site.
I¡¦ll right away grab your rss feed as I can not find your email subscription link or newsletter service. Do you have any? Please let me recognise in order that I may just subscribe. Thanks.
I have been surfing on-line more than three hours these days, yet I never discovered any attention-grabbing article like yours. It is pretty price sufficient for me. In my view, if all website owners and bloggers made good content material as you probably did, the net will likely be a lot more useful than ever before.
I do not even know how I ended up here, but I thought this post was great. I do not know who you are but definitely you’re going to a famous blogger if you aren’t already 😉 Cheers!
It is really a nice and helpful piece of info. I am satisfied that you shared this helpful information with us. Please stay us up to date like this. Thank you for sharing.
I will immediately snatch your rss as I can’t to find your e-mail subscription hyperlink or newsletter service. Do you’ve any? Kindly permit me recognise in order that I may subscribe. Thanks.
Awesome write-up. I am a regular visitor of your web site and appreciate you taking the time to maintain the nice site. I will be a frequent visitor for a really long time.
Good – I should definitely pronounce, impressed with your web site. I had no trouble navigating through all the tabs as well as related info ended up being truly easy to do to access. I recently found what I hoped for before you know it at all. Quite unusual. Is likely to appreciate it for those who add forums or anything, site theme . a tones way for your customer to communicate. Nice task.
I have learn some just right stuff here. Certainly worth bookmarking for revisiting. I wonder how a lot effort you set to create this type of excellent informative site.
I’ll right away take hold of your rss as I can’t find your email subscription hyperlink or e-newsletter service. Do you’ve any? Kindly permit me know so that I may subscribe. Thanks.
I have read a few excellent stuff here. Certainly value bookmarking for revisiting. I wonder how much effort you place to make this kind of magnificent informative website.
I gotta bookmark this website it seems extremely helpful invaluable
I would like to voice my passion for your kind-heartedness giving support to women who should have assistance with this one concept. Your personal dedication to getting the message all over appeared to be really practical and has all the time encouraged employees much like me to reach their dreams. Your own useful recommendations means a great deal a person like me and extremely more to my peers. Thanks a ton; from all of us.
Undeniably believe that which you stated. Your favorite reason appeared to be on the internet the easiest thing to be aware of. I say to you, I certainly get annoyed while people think about worries that they plainly don’t know about. You managed to hit the nail upon the top and defined out the whole thing without having side-effects , people could take a signal. Will likely be back to get more. Thanks
I love your blog.. very nice colors & theme. Did you make this website yourself or did you hire someone to do it for you? Plz reply as I’m looking to create my own blog and would like to find out where u got this from. thanks a lot
Some genuinely choice articles on this internet site , bookmarked .
I used to be recommended this web site by way of my cousin. I am not certain whether this put up is written by means of him as nobody else realize such targeted approximately my problem. You’re amazing! Thank you!
Hello, i think that i saw you visited my weblog thus i came to “return the favor”.I’m trying to find things to enhance my web site!I suppose its ok to use a few of your ideas!!
Of course, what a splendid blog and revealing posts, I surely will bookmark your website.All the Best!
Well I sincerely liked studying it. This article provided by you is very helpful for good planning.
Awesome post. I’m a normal visitor of your site and appreciate you taking the time to maintain the excellent site. I’ll be a regular visitor for a long time.
I got what you mean , thankyou for putting up.Woh I am happy to find this website through google. “Food is the most primitive form of comfort.” by Sheila Graham.
Heya i am for the first time here. I found this board and I find It truly useful & it helped me out much. I hope to give something back and aid others like you helped me.
Good post made here. One thing I’d like to say is the fact most professional areas consider the Bachelors Degree just as the entry level requirement for an online degree. Even though Associate Certification are a great way to get started, completing a person’s Bachelors opens up many entrances to various employment opportunities, there are numerous internet Bachelor Diploma Programs available via institutions like The University of Phoenix, Intercontinental University Online and Kaplan. Another issue is that many brick and mortar institutions present Online editions of their diplomas but normally for a extensively higher payment than the corporations that specialize in online higher education degree programs.
I like this web site very much, Its a very nice office to read and incur info . “The love of nature is consolation against failure.” by Berthe Morisot.
I have observed that of all varieties of insurance, health care insurance is the most marked by controversy because of the issue between the insurance policy company’s need to remain adrift and the consumer’s need to have insurance policies. Insurance companies’ income on well being plans are incredibly low, consequently some companies struggle to generate income. Thanks for the concepts you share through this web site.
You made some decent points there. I looked on the web for the problem and located most people will go together with with your website.
I used to be suggested this website by my cousin. I’m now not sure whether this submit is written by him as nobody else realize such certain approximately my trouble. You are amazing! Thanks!
Very well written story. It will be valuable to anybody who utilizes it, including myself. Keep doing what you are doing – for sure i will check out more posts.
Hi, i think that i saw you visited my blog thus i came to “return the favorâ€.I am attempting to find things to enhance my site!I suppose its ok to use some of your ideas!!
Thanks for giving your ideas on this blog. Likewise, a fantasy regarding the banking companies intentions if talking about foreclosures is that the lender will not take my repayments. There is a certain quantity of time the bank can take payments from time to time. If you are also deep inside hole, they are going to commonly demand that you pay the particular payment entirely. However, i am not saying that they will have any sort of payments at all. Should you and the bank can seem to work a little something out, the particular foreclosure approach may end. However, in the event you continue to miss payments underneath the new system, the foreclosed process can pick up where it was left off.
Hi, I think your blog might be having browser compatibility issues. When I look at your website in Firefox, it looks fine but when opening in Internet Explorer, it has some overlapping. I just wanted to give you a quick heads up! Other then that, fantastic blog!
You made some nice points there. I looked on the internet for the subject matter and found most people will agree with your blog.
Thank you for another fantastic blog. Where else might one get that sort of knowledge written in such a perfect way? I actually have a presentation that i’m presently acting on, and i are yearning for such info instead.
Hiya, I’m really glad I have found this information. Nowadays bloggers publish only about gossip and web stuff and this is really irritating. A good site with exciting content, this is what I need. Thank you for making this web site, and I will be visiting again. Do you do newsletters by email?
Hey there. I discovered your web site by means of Google whilst searching for a related topic, your website came up. It seems to be good. I have bookmarked it in my google bookmarks to come back then.
Hey there. I discovered your site by way of Google at the same time as searching for a comparable matter, your site came up. It seems to be good. I have bookmarked it in my google bookmarks to visit then.
Hiya, I’m really glad I have found this info. Today bloggers publish only about gossip and net stuff and this is actually irritating. A good web site with interesting content, this is what I need. Thank you for making this web-site, and I will be visiting again. Do you do newsletters by email?
Appreciating the persistence you put into your blog and detailed information you provide.
Awesome post. I am a regular visitor of your website and appreciate you taking the time to maintain the excellent site. I will be a regular visitor for a really long time.
Hi there. I found your site via Google at the same time as looking for a comparable subject, your website got here up. It appears to be great. I have bookmarked it in my google bookmarks to come back then.
Hiya, I’m really glad I have found this info. Today bloggers publish only about gossip and internet stuff and this is really annoying. A good blog with exciting content, that’s what I need. Thank you for making this web site, and I’ll be visiting again. Do you do newsletters by email?
Awesome write-up. I am a normal visitor of your site and appreciate you taking the time to maintain the nice site. I’ll be a regular visitor for a really long time.
Hiya, I am really glad I have found this information. Nowadays bloggers publish only about gossip and net stuff and this is actually annoying. A good blog with exciting content, that’s what I need. Thank you for making this website, and I’ll be visiting again. Do you do newsletters by email?
Hi there. I discovered your web site by way of Google whilst looking for a related subject, your website came up. It seems to be great. I’ve bookmarked it in my google bookmarks to visit then.
Hi there. I discovered your website via Google whilst looking for a similar subject, your web site got here up. It appears to be great. I’ve bookmarked it in my google bookmarks to come back then.
Hiya, I am really glad I have found this information. Today bloggers publish only about gossip and net stuff and this is actually annoying. A good blog with interesting content, this is what I need. Thank you for making this web-site, and I’ll be visiting again. Do you do newsletters by email?
Hey there. I discovered your web site by means of Google while searching for a related topic, your site came up. It appears to be good. I’ve bookmarked it in my google bookmarks to visit then.
Awesome write-up. I’m a normal visitor of your site and appreciate you taking the time to maintain the excellent site. I’ll be a regular visitor for a really long time.
Awesome post. I am a normal visitor of your website and appreciate you taking the time to maintain the nice site. I will be a regular visitor for a long time.
Awesome post. I’m a normal visitor of your web site and appreciate you taking the time to maintain the nice site. I will be a frequent visitor for a long time.
Awesome post. I’m a regular visitor of your site and appreciate you taking the time to maintain the nice site. I will be a regular visitor for a long time.
Awesome post. I’m a normal visitor of your website and appreciate you taking the time to maintain the nice site. I’ll be a regular visitor for a long time.
Hi there. I found your blog via Google even as looking for a similar matter, your website got here up. It seems to be great. I have bookmarked it in my google bookmarks to visit then.
Awesome write-up. I am a normal visitor of your web site and appreciate you taking the time to maintain the nice site. I will be a frequent visitor for a really long time.
Hey there. I found your blog by way of Google whilst looking for a similar subject, your web site got here up. It looks great. I’ve bookmarked it in my google bookmarks to come back then.
Awesome write-up. I’m a normal visitor of your web site and appreciate you taking the time to maintain the nice site. I’ll be a frequent visitor for a really long time.
Hiya, I’m really glad I have found this info. Nowadays bloggers publish only about gossip and net stuff and this is actually annoying. A good web site with interesting content, that is what I need. Thanks for making this web site, and I will be visiting again. Do you do newsletters by email?
Awesome post. I am a regular visitor of your website and appreciate you taking the time to maintain the excellent site. I’ll be a frequent visitor for a long time.
Hiya, I’m really glad I’ve found this information. Today bloggers publish only about gossip and web stuff and this is actually annoying. A good blog with exciting content, that is what I need. Thanks for making this website, and I’ll be visiting again. Do you do newsletters by email?
Hiya, I’m really glad I’ve found this info. Nowadays bloggers publish just about gossip and internet stuff and this is really irritating. A good site with interesting content, that is what I need. Thank you for making this website, and I will be visiting again. Do you do newsletters by email?
Hiya, I’m really glad I have found this information. Nowadays bloggers publish just about gossip and internet stuff and this is actually irritating. A good blog with exciting content, this is what I need. Thank you for making this website, and I’ll be visiting again. Do you do newsletters by email?
You are a very smart person!
Magnificent goods from you, man. I have understand your stuff previous to and you are just too magnificent. I really like what you have acquired here, certainly like what you’re saying and the way in which you say it. You make it enjoyable and you still care for to keep it smart. I can not wait to read much more from you. This is really a wonderful site.
Hiya, I’m really glad I’ve found this info. Nowadays bloggers publish just about gossip and web stuff and this is actually annoying. A good site with exciting content, that’s what I need. Thanks for making this web-site, and I will be visiting again. Do you do newsletters by email?
When was this posted?
I just wanted to make a small note to say thanks to you for those unique advice you are giving on this website. My particularly long internet investigation has now been recognized with reasonable knowledge to talk about with my neighbours. I would say that many of us site visitors are quite blessed to live in a remarkable place with so many lovely individuals with beneficial guidelines. I feel truly grateful to have come across your web page and look forward to plenty of more exciting times reading here. Thanks a lot again for everything.
Hi, Neat post. There is a problem together with your website in web explorer, might test this¡K IE still is the marketplace leader and a big part of folks will leave out your magnificent writing due to this problem.
Hiya, I am really glad I’ve found this info. Nowadays bloggers publish only about gossip and net stuff and this is actually annoying. A good site with exciting content, this is what I need. Thank you for making this website, and I’ll be visiting again. Do you do newsletters by email?
Hey there. I found your website via Google whilst looking for a similar matter, your website came up. It seems good. I have bookmarked it in my google bookmarks to visit then.
Hi there. I discovered your site via Google while searching for a comparable subject, your web site got here up. It looks good. I’ve bookmarked it in my google bookmarks to visit then.
Excellent post, thank you a lot for sharing. Do you have an RSS feed I can subscribe to?
Awesome write-up. I’m a normal visitor of your website and appreciate you taking the time to maintain the nice site. I will be a regular visitor for a really long time.
Awesome write-up. I am a regular visitor of your site and appreciate you taking the time to maintain the excellent site. I will be a regular visitor for a really long time.
Hey there. I discovered your website by way of Google while searching for a comparable matter, your web site came up. It looks great. I have bookmarked it in my google bookmarks to visit then.
Awesome post. I am a regular visitor of your web site and appreciate you taking the time to maintain the nice site. I will be a regular visitor for a really long time.
Thank you a lot for sharing this with all folks you really understand what you are talking about! Bookmarked. Kindly also seek advice from my web site =). We may have a link exchange contract among us!
You really make it seem so easy with your presentation but I find this topic to be actually something which I think I would never understand. It seems too complex and extremely broad for me. I’m looking forward for your next post, I’ll try to get the hang of it!
What i do not understood is if truth be told how you’re now not really a lot more smartly-appreciated than you may be right now. You are so intelligent. You already know therefore significantly in terms of this subject, made me individually believe it from so many numerous angles. Its like women and men are not fascinated until it is one thing to accomplish with Girl gaga! Your personal stuffs outstanding. All the time deal with it up!
Awesome post. I am a normal visitor of your blog and appreciate you taking the time to maintain the nice site. I’ll be a regular visitor for a really long time.
Awesome post. I am a normal visitor of your web site and appreciate you taking the time to maintain the nice site. I will be a frequent visitor for a long time.
Hiya, I’m really glad I’ve found this information. Today bloggers publish just about gossip and internet stuff and this is actually frustrating. A good web site with exciting content, this is what I need. Thanks for making this website, and I’ll be visiting again. Do you do newsletters by email?
Hey there. I found your website by way of Google even as searching for a related matter, your website got here up. It seems good. I have bookmarked it in my google bookmarks to come back then.
Hello there. I found your web site by the use of Google at the same time as searching for a similar topic, your site came up. It seems great. I have bookmarked it in my google bookmarks to visit then.
Awesome post. I am a regular visitor of your blog and appreciate you taking the time to maintain the nice site. I’ll be a frequent visitor for a long time.
Hiya, I’m really glad I’ve found this information. Today bloggers publish just about gossip and net stuff and this is actually frustrating. A good blog with exciting content, this is what I need. Thanks for making this web-site, and I will be visiting again. Do you do newsletters by email?
Hello there. I discovered your blog by way of Google even as searching for a related subject, your website got here up. It seems to be good. I have bookmarked it in my google bookmarks to visit then.
Hiya, I am really glad I’ve found this info. Nowadays bloggers publish only about gossip and web stuff and this is actually irritating. A good web site with exciting content, that’s what I need. Thank you for making this site, and I will be visiting again. Do you do newsletters by email?
Hello there. I found your website by way of Google whilst looking for a similar topic, your web site came up. It seems good. I have bookmarked it in my google bookmarks to come back then.
Hi there. I found your website by way of Google while looking for a related matter, your website got here up. It seems great. I have bookmarked it in my google bookmarks to visit then.
Hi, Neat post. There is a problem with your website in internet explorer, would check this… IE still is the market leader and a large portion of people will miss your excellent writing because of this problem.
Hey there. I discovered your site by means of Google whilst looking for a comparable matter, your site got here up. It looks good. I’ve bookmarked it in my google bookmarks to visit then.
Hiya, I am really glad I have found this information. Nowadays bloggers publish just about gossip and web stuff and this is really annoying. A good blog with exciting content, this is what I need. Thank you for making this web site, and I’ll be visiting again. Do you do newsletters by email?
Awesome post. I am a normal visitor of your blog and appreciate you taking the time to maintain the nice site. I’ll be a frequent visitor for a long time.
Hey there. I discovered your web site by the use of Google even as searching for a similar topic, your site got here up. It seems good. I have bookmarked it in my google bookmarks to come back then.
Hello there. I discovered your web site by means of Google even as searching for a similar topic, your site came up. It seems good. I’ve bookmarked it in my google bookmarks to come back then.
Awesome post. I’m a normal visitor of your website and appreciate you taking the time to maintain the excellent site. I’ll be a frequent visitor for a long time.
Hiya, I’m really glad I have found this info. Today bloggers publish just about gossip and net stuff and this is actually irritating. A good blog with interesting content, this is what I need. Thanks for making this site, and I’ll be visiting again. Do you do newsletters by email?
I loved as much as you’ll receive carried out right here. The sketch is attractive, your authored subject matter stylish. nonetheless, you command get got an impatience over that you wish be delivering the following. unwell unquestionably come more formerly again since exactly the same nearly a lot often inside case you shield this hike.
Awesome post. I am a regular visitor of your blog and appreciate you taking the time to maintain the excellent site. I’ll be a frequent visitor for a really long time.
Hi there. I discovered your site by way of Google even as searching for a comparable topic, your web site came up. It looks great. I have bookmarked it in my google bookmarks to come back then.
Awesome post. I am a regular visitor of your site and appreciate you taking the time to maintain the nice site. I’ll be a regular visitor for a really long time.
Awesome post. I am a regular visitor of your site and appreciate you taking the time to maintain the nice site. I’ll be a regular visitor for a really long time.
Hiya, I’m really glad I have found this information. Nowadays bloggers publish only about gossip and internet stuff and this is really irritating. A good blog with exciting content, this is what I need. Thanks for making this website, and I will be visiting again. Do you do newsletters by email?
I wish to get across my appreciation for your kind-heartedness for persons that must have guidance on the matter. Your real dedication to passing the solution all around ended up being exceedingly productive and have made guys and women like me to attain their targets. This interesting instruction denotes a great deal to me and much more to my colleagues. Thank you; from all of us.
Awesome write-up. I am a regular visitor of your web site and appreciate you taking the time to maintain the excellent site. I’ll be a frequent visitor for a long time.
Hiya, I am really glad I’ve found this info. Nowadays bloggers publish just about gossip and web stuff and this is actually irritating. A good web site with exciting content, that’s what I need. Thank you for making this web site, and I’ll be visiting again. Do you do newsletters by email?
Hiya, I’m really glad I’ve found this information. Nowadays bloggers publish only about gossip and internet stuff and this is actually annoying. A good site with exciting content, that’s what I need. Thank you for making this site, and I’ll be visiting again. Do you do newsletters by email?
Awesome post. I’m a normal visitor of your web site and appreciate you taking the time to maintain the nice site. I will be a regular visitor for a really long time.
Hiya, I am really glad I have found this information. Nowadays bloggers publish just about gossip and web stuff and this is really irritating. A good blog with exciting content, this is what I need. Thanks for making this website, and I will be visiting again. Do you do newsletters by email?
Thanks a lot for sharing this with all of us you really realize what you’re speaking approximately! Bookmarked. Please also discuss with my site =). We could have a link exchange agreement among us!
Hi there. I discovered your blog by means of Google while searching for a similar matter, your web site got here up. It seems great. I have bookmarked it in my google bookmarks to visit then.
Hiya, I am really glad I have found this information. Nowadays bloggers publish just about gossip and internet stuff and this is actually irritating. A good website with interesting content, that is what I need. Thank you for making this web site, and I will be visiting again. Do you do newsletters by email?
Hi there, You’ve done a great job. I’ll definitely digg it and personally suggest to my friends. I’m sure they will be benefited from this site.
Thanks for some other informative site. Where else may I get that kind of info written in such an ideal approach? I’ve a venture that I’m simply now running on, and I’ve been on the look out for such information.
Hey there. I discovered your web site by the use of Google even as looking for a comparable subject, your site got here up. It seems good. I’ve bookmarked it in my google bookmarks to visit then.
Thank you for the sensible critique. Me and my neighbor were just preparing to do some research about this. We got a grab a book from our local library but I think I learned more clear from this post. I’m very glad to see such great information being shared freely out there.
Hiya, I’m really glad I’ve found this information. Today bloggers publish just about gossip and net stuff and this is really annoying. A good blog with interesting content, that is what I need. Thank you for making this website, and I’ll be visiting again. Do you do newsletters by email?
Hello there. I discovered your website by the use of Google whilst searching for a related subject, your website came up. It seems great. I have bookmarked it in my google bookmarks to visit then.
Awesome post. I am a normal visitor of your web site and appreciate you taking the time to maintain the excellent site. I’ll be a regular visitor for a long time.
Hiya, I am really glad I have found this information. Today bloggers publish only about gossip and web stuff and this is really annoying. A good site with interesting content, that’s what I need. Thanks for making this website, and I’ll be visiting again. Do you do newsletters by email?
Awesome write-up. I am a regular visitor of your web site and appreciate you taking the time to maintain the nice site. I will be a frequent visitor for a really long time.
Hi there. I found your web site by way of Google even as looking for a comparable topic, your website came up. It appears good. I have bookmarked it in my google bookmarks to visit then.
Hiya, I am really glad I have found this info. Today bloggers publish just about gossip and internet stuff and this is actually annoying. A good site with exciting content, that is what I need. Thank you for making this site, and I will be visiting again. Do you do newsletters by email?
Hiya, I am really glad I’ve found this information. Nowadays bloggers publish only about gossip and net stuff and this is really irritating. A good web site with exciting content, that is what I need. Thank you for making this website, and I’ll be visiting again. Do you do newsletters by email?
Hiya, I’m really glad I have found this info. Today bloggers publish just about gossip and net stuff and this is really frustrating. A good website with exciting content, that is what I need. Thanks for making this web-site, and I will be visiting again. Do you do newsletters by email?
Hey there. I discovered your blog by means of Google while looking for a similar subject, your web site came up. It looks good. I have bookmarked it in my google bookmarks to visit then.
An fascinating discussion will probably be worth comment. I do believe that you ought to write on this topic, it might certainly be a taboo subject but normally folks are there are not enough to talk on such topics. An additional. Cheers
Thanks so much for providing individuals with an extraordinarily spectacular opportunity to read articles and blog posts from this blog. It is usually very pleasurable and also packed with a good time for me and my office mates to search your website on the least 3 times weekly to learn the new secrets you will have. And indeed, I am certainly impressed for the good things you serve. Certain two facts in this article are undeniably the best we have all ever had.
I was recommended this blog by my cousin. I’m not sure whether this post is written by him as no one else know such detailed about my difficulty. You are incredible! Thanks!
It¡¦s really a nice and helpful piece of info. I am happy that you simply shared this helpful info with us. Please stay us up to date like this. Thank you for sharing.
The young boys ended up stimulated to read through them and now have unquestionably been having fun with these things.
It’s reallyactuallyin facttrulygenuinely very complexdifficultcomplicated in this busyfull of activityactive life to listen news on TVTelevision, sothustherefore I onlysimplyjust use internetwebworld wide webthe web for that purposereason, and takegetobtain the latestnewestmost recentmost up-to-datehottest newsinformation.
Great post. I was checking constantly this blog and I am impressed! Very useful information specifically the last part 🙂 I care for such info much. I was looking for this certain info for a long time. Thank you and good luck.
It as best to participate in a contest for among the best blogs on the web. I all suggest this website!
very handful of websites that transpire to become detailed beneath, from our point of view are undoubtedly very well worth checking out
I like this post, enjoyed this one thank you for putting up. “When you make a world tolerable for yourself, you make a world tolerable for others.” by Anais Nin.
I’m not that much of a onlineinternet reader to be honest but your blogssites really nice, keep it up! I’ll go ahead and bookmark your sitewebsite to come back laterdown the roadin the futurelater on. CheersAll the bestMany thanks
(Your good knowledge and kindness in playing with all the pieces were very useful. I don’t know what I would have done if I had not encountered such a step like this.
I found so many interesting stuff in your blog especially its discussion. From the tons of comments on your articles, I guess I am not the only one having all the enjoyment here! keep up the good work..
Thank you for such a well written article. It’s full of insightful information and entertaining descriptions. Your point of view is the best among many.
It’s an awesomeremarkableamazing articlepostpiece of writingparagraph fordesigned forin favor ofin support of all the internetwebonline userspeopleviewersvisitors; they will takegetobtain benefitadvantage from it I am sure.
Very handy article, this is unquestionably very valuable for a website. Thanks. Thumb up for this informative article.
Thanks for one marvelous posting! I liked reading it ; you are a great author.I will make certain that you bookmark your blog and might return someday. I want to encourage that you continue your great posts, have a nice weekend!
I must voice my passion for your kindness providing support to those individuals that should have advice on this important issue.
Present with no answers to the issues you have sorted out through this manual is a critical instance, in addition to the kind which could have badly influenced my whole career if I had not discovered your website.
I was excited to find this web site. I need to to thank you for ones time due to this wonderful read!! I definitely savored every part of it and I have you saved as a favorite to see new things on your web site.
I have been reading out a few of your articles and i must say pretty good stuff. I will definitely bookmark your site.
Write more, thats all I have to say. Literally, it seems as though you relied on the video to make your point. You clearlydefinitelyobviously know what youre talking about, why wastethrow away your intelligence on just posting videos to your blogsiteweblog when you could be giving us something enlighteninginformative to read?
Hello there I am so thrilled I found your website, I really found you by mistake, although I was browsing on Yahoo for something different, Anyhow I’m here now and would like to say thanks a lot for a tremendous post and a all round exciting site (I adore the theme/design), I don’t have the time to go through it all at the moment but I have saved it and also added on your RSS feeds, so when I have time I’ll be back to see more, please do keep up the wonderful job.